Adaptive Tree-based Convergecast Protocol
Adaptive tree-based protocol for managing overlay networks in heterogeneous networks. It proposes improvements to the existing Tree-Based Convergecast Routing (TBCR) protocol by considering additional parameters such as RTT, power consumption, link stability, and link mobility to optimize routing de
32 views • 12 slides
Longest Common Subsequences in Bioinformatics
DNA Sequence Alignment is a crucial task in bioinformatics, where dynamic programming helps in finding the best alignment between DNA strings efficiently. The Longest Common Subsequence (LCS) problem aims to discover the longest shared subsequence between two strings, offering applications in DNA si
1 views • 21 slides
Near-Optimal Quantum Algorithms for String Problems
This paper discusses near-optimal quantum algorithms for various string problems like exact pattern matching, longest common substring, lexicographically minimal string rotation, longest palindromic substring, and more. It explores quantum black-box models, query complexities, and previous sublinear
0 views • 22 slides
OSI Model and TCP/IP Protocol Suite
Explore the concept of layering in data communication, comparing the OSI model and TCP/IP protocol suite. Learn about protocol layers, protocol hierarchies, and the functionality of each layer in these models. Discover the interrelationships between layers and the evolution from OSI to TCP/IP.
6 views • 57 slides
Polymer Degradation Processes in Chemistry
Polymer degradation involves a reduction in molecular weight due to various factors like heating, mechanical stresses, radiation, oxygen, and moisture. Two main types of degradation include chain end degradation and random degradation, each affecting the polymer structure differently. Chain end degr
2 views • 12 slides
London Homeless Coalition (LHC) Death Communication Protocol
In 2014, the Memorial Committee of the London Homeless Coalition (LHC) established the Death Communication Protocol to acknowledge, share, and address the loss of individuals experiencing homelessness. The protocol aims to inform partnering organizations of confirmed or unconfirmed deaths, support g
2 views • 12 slides
Mobile Computing and TCP/IP Protocol Suite
Mobile computing is crucial for continuous internet connectivity regardless of physical location. The TCP/IP protocol suite, consisting of Transmission Control Protocol (TCP) and Internet Protocol (IP), forms the backbone of internet infrastructure. IP addressing and mobility challenges are addresse
2 views • 51 slides
Cybersecurity and Supply Chain Risk Management Best Practices
Supply chain attacks pose a significant threat to software developers and suppliers by targeting source codes and build processes to distribute malware. This article discusses the importance of supply chain risk management, the various attack vectors involved, the industries at risk, and the repercu
1 views • 23 slides
OSI Model and TCP/IP Protocol Suite in Computer Networking
This chapter explores the OSI model and TCP/IP protocol suite, delving into protocol layers, addressing mechanisms, and network components. It highlights the interface between layers, functions of each layer in the OSI model, and compares TCP/IP protocol suite layers with OSI model layers. The discu
0 views • 30 slides
MAAP Protocol Overview in IEEE 1722: Address Acquisition and Message Format
The MAAP (Multicast Address Acquisition Protocol) is defined in IEEE 1722 for time-sensitive applications in bridged local area networks. It involves acquiring multicast addresses through claiming, probing, and defending messages. MAAP enables dynamic allocation of addresses and defending against co
1 views • 8 slides
Free Radical Polymerization Kinetics
This lecture covers the kinetics of free radical polymerization, including initiation, propagation, termination, and kinetic chain length concepts. It explains the calculation of kinetic chain length and chain-transfer reactions. Key points include the rate equations for initiation, propagation, and
0 views • 11 slides
Longest Increasing Subsequence Problem and Solution
The Longest Increasing Subsequence problem involves finding a subsequence in a given sequence that is strictly increasing and of maximum length. The solution utilizes Dynamic Programming by maintaining arrays to store indices and track the longest increasing subsequence. By iterating over the list,
1 views • 32 slides
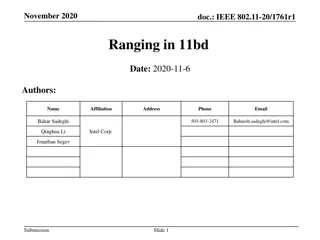
IEEE 802.11-20/1761r1 Ranging Protocol for 11bd
This document outlines the ranging protocol proposed for IEEE 802.11-20/1761r1, focusing on RTT-based ranging leveraging multi-channel operation. By integrating the 11az ranging protocol, it enables flexible and low-overhead application in 11bd for improved accuracy in ITS bands. The protocol includ
1 views • 13 slides
Rutgers Business School Supply Chain Management Curriculum Overview
Explore Rutgers Business School's innovative Supply Chain Management Curriculum designed for high schools. The curriculum focuses on Project-Based Learning (PBL) and integrates essential elements such as significant content, 21st-century skills, in-depth inquiry, and more. The program is based on th
0 views • 15 slides
EIGRP: A Comprehensive Overview
Enhanced Interior Gateway Routing Protocol (EIGRP) is a dynamic routing protocol providing various advantages to network administrators. It is a classless routing protocol supporting VLSM and is considered an Interior Gateway Protocol (IGP). EIGRP uses advanced distance vector routing and is known f
1 views • 5 slides
SFTP Server Functionality with ACS 5.x by Mohammad Azharuddin AAA Team
SFTP (SSH File Transfer Protocol) is a secure network protocol for file access, transfer, and management over reliable data streams. It enhances security by extending the SSH protocol and can be implemented using a reliable 8-bit byte stream protocol. SFTP commands are sent as 4 ASCII letters follow
4 views • 23 slides
Introduction to Supply Chain Management
Explore the key components of supply chains, the importance of supply chain management technology, and strategies to overcome challenges. Learn about supply chain visibility, the structure of supply chains, and the three segments - upstream, internal, and downstream. Discover how organizations acces
1 views • 29 slides
Enhanced Family Court Police Disclosure Protocol for 2024
The 2024 Family Court Police Disclosure Protocol addresses key issues identified in the 2013 protocol, emphasizing timely and proportionate requests for material. Changes include a new checklist for the judiciary, guidance notes, and revised processes for litigants in person. The protocol provides c
1 views • 19 slides
Enhancing Supply Chain Insights Through Holistic Data Synthesis
Synthesizing economic data for comprehensive supply chain analysis, this talk by Krista Chan, Kevin Li, and Christian Moscardi from the U.S. Census Bureau discusses the goals, challenges, supply chain interests, data sources, and desired functionalities to present a holistic view of product supply c
0 views • 16 slides
Essential Elements of Clinical Trial Protocols
Understanding the key components of a clinical trial research protocol is essential for conducting successful studies. This includes identifying session objectives, discussing trial protocol contents, exploring observational study elements, and learning about reporting guidelines. Study objectives f
2 views • 25 slides
Analysis of Longest Instrumental Rainfall Series in Indian Regions
This study by Yamini Kulkarni analyzes the longest instrumental rainfall series in Indian regions from 1848 to 2006. It includes the development of rainfall series for different zones using a network of rain gauge stations and statistical methods to understand fluctuations in precipitation over a 15
0 views • 9 slides
Utilizing Technology for Efficient Health Supply Chain Management in Pakistan During COVID-19
The USAID Global Health Supply Chain Program has supported Pakistan in leveraging its logistics management information system (LMIS) to efficiently plan and deliver critical COVID-19 supplies. Through coordination with government entities and use of various LMIS interfaces, Pakistan has enhanced dat
1 views • 12 slides
The Value Chain and Supply Chain Dynamics
The value chain involves adding value through a series of activities from producer to consumer, focusing on meeting consumer demands and gaining a competitive advantage. On the other hand, the supply chain focuses on efficient and cost-effective product distribution to meet consumer needs. The prima
0 views • 10 slides
Enhancing Supply Chain Security and IT Governance: An Overview
This presentation delves into the critical aspects of supply chain security and IT governance, highlighting the synchronization of IT decisions across supply chains, global supply chain concerns, the cost implications of supply chain security lapses, and the need for more research and strategic alig
0 views • 28 slides
Supply Chain Management: Key Concepts and Processes
Supply chain management (SCM) involves the centralized management of goods and services flow, covering processes from raw materials to final products. By efficiently managing the supply chain, companies can reduce costs and improve product delivery. This seminar presentation explores the definition,
0 views • 24 slides
Proof of Stake in Blockchain Technology
This lecture delves into the concept of Proof of Stake (PoS) as an energy-efficient alternative to Proof of Work (PoW) in blockchain protocols. It explores how PoS allows meaningful participation based on the stake individuals hold, replacing the need for energy-intensive mining. The lecture discuss
0 views • 28 slides
Enhancing Supply Chain Efficiency with Quality Systems
Explore the best practices and methodologies for improving supply chain operations such as planning, sourcing, making, delivering, and returning. Discover key initiatives like E-procurement, bar coding, supplier quality assurance, and green supply chain to elevate functional excellence. Align supply
1 views • 28 slides
China-Africa Supply Chain Cooperation: Challenges and Opportunities
China-Africa Supply Chain Cooperation presents both challenges and opportunities for development. The growth of China-Africa supply chain is crucial, considering Africa's participation in the global supply chain mainly focused on providing primary products. The strategic importance of this relations
0 views • 19 slides
Danyang Bridge: The World's Longest Bridge
The Danyang Bridge, captured and researched by Kaylee in 2nd grade, is an impressive engineering marvel in China. Stretching 102 miles (114 km), it surpasses all other bridges in length and is a key part of the Beijing high-speed railway. Built in 2011, its spans reach 102 feet, distinguishing it as
0 views • 6 slides
Sync HotStuff: Practical Synchronous State Machine Replication
Sync HotStuff is a practical synchronous protocol that tolerates Byzantine replicas and handles weaker synchrony models. It overcomes issues of requiring a large number of rounds and lock-step execution. The protocol ensures safety by committing blocks and guarantees liveness by continuing to commit
0 views • 15 slides
Queen Elizabeth II: The Longest-Reigning British Monarch
Elizabeth Alexandra Mary Windsor, born in 1926, became Queen Elizabeth II in 1952 after her father's death. She married Philip, Duke of Edinburgh, in 1947 and has four children. Queen Elizabeth II is the longest-lived and longest-reigning British monarch, achieving several historical milestones duri
0 views • 6 slides
Hybrid Consensus: Incorporating BFT into Longest-Chain Protocols
Today's lecture discussed the integration of BFT into longest-chain protocols, introducing new hybrid consensus models and finality gadgets. By combining HotStuff with PoW, the system aims to achieve fast transaction confirmation while maintaining decentralization and fairness in the committee elect
0 views • 21 slides
Enhancing Nepal's Agricultural Supply Chain for Sustainable Growth
Nepal's agricultural imports, dominated by staples, edible oil, vegetables, fruits, and more, indicate the need to strengthen the agricultural supply chain. Analyzing trade indicators reveals a trade deficit and the importance of optimizing supply chain management. The country's fragmented ASC manag
0 views • 12 slides
Dynamic Programming for Longest Palindromic Subsequence Algorithm
This content covers the topic of dynamic programming for finding the longest palindromic subsequence in a given string. It provides information on how to approach the problem, define the recurrence relation, establish base cases, and determine the order of solving subproblems. The discussion include
0 views • 19 slides
Protocol Deviations in Clinical Trials
Protocol deviations are expected occurrences in clinical trials that may arise from site or participant actions. It is crucial for research teams to identify, report, and learn from these deviations to ensure the integrity and safety of the study. Mechanisms for identifying and reporting deviations,
0 views • 16 slides
OSI Model and TCP/IP Protocol Suite in Computer Networking
This content delves into the OSI model and TCP/IP protocol suite, highlighting the protocol layers, addressing mechanisms, and communication scenarios. It explores the functions of each layer, the interface between layers, and compares the TCP/IP layers with the OSI model. Through examples and illus
0 views • 46 slides
Router Design and Longest Prefix Matching in Computer Networks
Explore concepts like control plane processors, route lookup, and IP block reallocation in computer networking. Learn about the basics of forwarding tables, scheduling, and buffer management crucial for network operations. Dive into routing algorithms and data plane processing for efficient packet d
0 views • 39 slides
Seeking a General-Purpose CCSDS Link Layer Protocol: Next-Generation Data Link Protocol (NGDLP)
This document discusses the proposed Universal Frame Format for a next-generation data link protocol, focusing on major questions about transfer frames, Protocol Link Transmission Unit (PLTU), and Universal Transfer Frame Structure. It explores topics such as frame formats, telemetry transfer frames
0 views • 24 slides
NT Awake Proning Protocol for Non-Intubated Patients
This protocol outlines the benefits and procedure for prone positioning in non-intubated patients experiencing mild to moderate hypoxemia. It highlights patient eligibility criteria, equipment required, and considerations for nursing care. The protocol emphasizes improving oxygenation by promoting a
0 views • 11 slides
Proof of Work and Mining in Blockchain
Exploring the concepts of Proof of Work, Mining, Longest Chain Rule, Double Spend Attack, and the implementation of an Oracle in the context of Bitcoin. The content covers how time slots are organized, node selection, ownership and transfer of coins, integrity maintenance, resistance to attacks, and
0 views • 13 slides