Case Studies on Successful Revenue Technology Implementations in Cargo Services (1)
In the fast-paced world of cargo services, optimizing pricing strategies remains a pivotal challenge for businesses aiming to boost profitability and maintain competitive advantage. Revenue technology, specifically tools that enable dynamic and cargo pricing, has revolutionized how companies approac
2 views • 5 slides
AARCH64 Linux Kernel Memory Management
Explore the confidential and proprietary details of AARCH64 Linux kernel memory mapping, virtual memory layout, variable configurations, DDR memory layout, and memory allocation techniques. Get insights into the allocation of physically contiguous memory using Continuous Memory Allocator (CMA) integ
0 views • 18 slides
OVS with P4 Code Walk Overview
OVS with P4 Code Walk by Namrata Limaye integrates P4, P4runtime, Openconfig, and more to enhance control plane elements. The design and future implementations focus on P4-DPDK, Tofino backend support, and enhanced kernel control plane functionalities. The project also offers detailed container setu
0 views • 6 slides
STM32WB BLE SW Application Sequencer Architecture Overview
The STM32WB BLE SW Application Sequencer is a specialized framework that optimizes while loop bare-metal implementations to avoid race conditions, especially in low power modes. It is not intended to compete with standard operating systems but rather with bare-metal implementations. The sequencer al
3 views • 14 slides
Generalized Discriminant Analysis (GDA) in Pattern Recognition
Generalized Discriminant Analysis (GDA) is a nonlinear form of Linear Discriminant Analysis (LDA) that utilizes kernel methods to find discriminatory features for optimal class separability. LDA aims to maximize the between-class covariance matrix while minimizing the within-class covariance matrix.
2 views • 17 slides
Optimizing User-Space Network Services with F-Stack and FreeBSD TCP/IP Stack
F-Stack, a user-space network service using DPDK and FreeBSD TCP/IP stack, addresses challenges in handling service traffic like CDN and live streaming. By leveraging 25GbE, 40GbE, and 100GbE NICs, coupled with multi-core CPUs and kernel bypass techniques, F-Stack overcomes bottlenecks between user
2 views • 17 slides
Kernel Tricks in Machine Learning
Kernel tricks in machine learning involve transforming inputs into higher-dimensional spaces to make linear models work for nonlinear data. Kernels can be applied to various algorithms like SVM, ridge regression, and more, allowing for better model performance with complex datasets.
1 views • 15 slides
Fundamentals of Operating Systems Explained
Explore the core concepts of operating systems, including kernel-userspace interactions, system calls, context switching, and virtual memory management. Delve into x86 assembly for system calls, hardware interrupts, and the flow of control during system call invocations. Gain insights into key compo
8 views • 19 slides
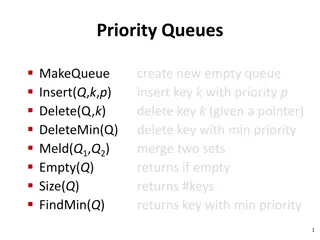
Priority Queues and Heap Data Structures
Priority queues play a key role in computer science algorithms by managing data based on priority levels. The use of heap data structures enhances the efficiency of priority queue operations. This tutorial covers the basics of priority queues, their applications, different implementations such as li
0 views • 30 slides
Priority Queues in Java: Implementation and Use Cases
Explore the concept of priority queues in Java, covering implementations using unsorted and sorted linked lists, as well as heaps. Learn about the differences between a queue and a priority queue through reading quizzes and discover various priority queue implementation options. Dive into priority q
1 views • 42 slides
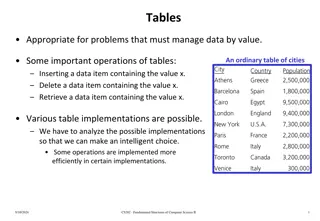
Implementations and Operations of Tables for Managing Data
An analysis of different table implementations for managing data by value, discussing operations like insertion, deletion, and retrieval. The post explores various linear and nonlinear implementations such as sorted arrays, linked lists, and binary search trees, highlighting the importance of select
0 views • 54 slides
Priority Queues: Operations and Implementations
Priority queues are data structures that allow efficient insertion, deletion, and retrieval of elements based on their priority. This information-rich content covers various aspects of priority queues, including ideal times, binomial queues, Dijkstra's algorithm for single-source shortest paths, and
0 views • 11 slides
Improving the Reliability of Commodity Operating Systems
This research paper discusses the challenges and solutions in enhancing the reliability of commodity operating systems by addressing system failures caused by kernel extensions. The Nooks approach isolates extensions within protection domains, allowing them to reside in the kernel address space with
0 views • 40 slides
Raspberry Pi 2 Boot Process Overview
Raspberry Pi 2's boot process involves a series of stages initiated by the GPU, loading essential firmware and enabling hardware components gradually, leading to the activation of the CPU and the kernel's entry point. The system transitions through various low-level processes before reaching a stabl
0 views • 9 slides
Priority Queues and Heaps in CSE 373 Lecture
Today's lecture in CSE 373 covers the Priority Queue Abstract Data Type (ADT), the properties of heaps, and their implementations. Key topics include the completeness property of heaps, different priority queue implementations such as the binary search tree for faster insert and find operations, and
0 views • 21 slides
Enhancing 3DIC Implementations with Mix-and-Match Die Stacking
This study by Kwangsoo Han, Andrew B. Kahng, and Jiajia Li delves into the improved performance of 3DIC implementations through the mix-and-match die stacking technique. By integrating slow and fast tiers, they aim to enhance parametric yield and optimize design-stage processes for a more efficient
0 views • 19 slides
Queues in Computer Science: Principles and Implementations
Explore the concept of queues in computer science, focusing on ordered collections of data following the FIFO principle. Learn about queue ADTs, implementations in Python, and delve into a simulation of a Printer Queue problem. Discover how to model printing tasks as random events and analyze the im
0 views • 15 slides
Multi-phase System Call Filtering for Container Security Enhancement
This tutorial discusses the importance of multi-phase system call filtering for reducing the attack surface of containers. It covers the benefits of containerization, OS virtualization, and the differences between OS and hardware virtualization. The tutorial emphasizes the need to reduce the kernel
0 views • 32 slides
User Mode, Kernel Mode, Interrupts, and System Calls in Computer Architecture
In modern computers following Von Newman Architecture, programs and data are stored in RAM. The CPU, RAM, ROM, and devices communicate via address and data buses. The system operates in both kernel and user modes, where kernel mode allows full system control, while user mode restricts access for sec
0 views • 29 slides
DNS Flag Day and EDNS: A Comprehensive Overview
DNS Flag Day marks a coordinated effort to remove workarounds in DNS implementations, impacting domains in various ccTLDs like .CL, .CZ, .SE, .NU, and .NZ. Enhanced DNS (EDNS) provides a mechanism for supporting new options, but issues arise from poor DNS implementations causing delays and hindering
0 views • 20 slides
ADT List Operations and Implementations
In this detailed content, you will learn about the specifications and operations involved in working with an ADT list. The structure, domain operations, and user instructions are clearly outlined for efficient implementation. The content also delves into the representation and implementation aspects
0 views • 30 slides
Efficient Snapshot Implementations in Distributed Systems
This content discusses various snapshot implementations in distributed systems, focusing on achieving faster and sub-linear snapshot complexity. It covers topics such as multi-writer registers, tree structures, polylogarithmic snapshots, and the challenges of ensuring consistency across processes. T
0 views • 16 slides
PacketGuardian: A Tool for Static Detection of Packet Injection Vulnerabilities
This research paper introduces PacketGuardian, an effective static analysis tool designed to evaluate the robustness of protocol implementations against packet injection attacks. This tool supports precise context, flow, field-sensitive taint analysis, implicit flow analysis, and employs a summary-b
0 views • 23 slides
Practical Implementations of Arithmetic Coding
Explore the practical implementations, advantages, and disadvantages of arithmetic coding in this informative guide. Learn about the basic algorithm, dynamic interval expansion, integer arithmetic coding, and methods to improve the speed of arithmetic coding. Dive deep into encoding algorithms, exam
0 views • 78 slides
Tracing Network Packets in Linux Kernel with eBPF
This presentation discusses the challenges of troubleshooting modern networking systems and proposes a solution using eBPF technology to trace the path of network packets in the Linux kernel. The goal is to develop a tool that provides detailed information about how network packets are processed in
0 views • 16 slides
AI-Based Compression and Understanding of Industrial Data (MPAI-CUI) - Company Performance Prediction Use Case
AI-based Compression and Understanding of Industrial Data (MPAI-CUI) is a standard developed by the MPEG standards group. This standard focuses on transforming data into a more suitable format for applications. The presentation will cover the introduction to MPAI, applications, a demo for anonymous
0 views • 25 slides
ADTs: Lists, Stacks, and Queues - Implementation and Operations
Explore the world of Abstract Data Types (ADTs) - Lists, Stacks, and Queues, focusing on their operations like adding, removing, and accessing elements. Learn the differences between array and linked list implementations, along with insights on how to manipulate data structure implementations. Dive
0 views • 18 slides
Analyzing Multimodality in Density Distributions Using JMP Scripting
Explore variability sources hidden in density distributions through JMP scripting. The analysis focuses on identifying and filtering distribution modes in semiconductor fab electrical measurements using kernel estimation and empirical rules. Antonio D'Angelo and Felice Russo from Lfoundry S.r.l. Ita
0 views • 6 slides
Remote Procedure Call (RPC) in Different Kernel Environments
Communication through Remote Procedure Call (RPC) plays a crucial role in facilitating seamless interaction between server and client processes, whether on the same machine or across different kernels. This technology streamlines local and cross-domain communication, optimizing performance while ens
0 views • 9 slides
High Performance User-Level Sockets over Gigabit Ethernet
Presentation overview of the design challenges, performance enhancement techniques, and results related to implementing high-performance user-level sockets over Gigabit Ethernet networks. The background and motivation discuss the limitations of traditional kernel-based implementations and the need f
1 views • 34 slides
Overview of the Pintos Instructional Operating System Kernel Project
Description of the Pintos Operating System Kernel project, including its use in educational settings at institutions such as Stanford University and Virginia Tech. The project aims to provide students with a hands-on experience in OS design, focusing on the internal workings of the kernel. Pintos fe
0 views • 33 slides
Pipes in Process Communication
Pipes in process communication allow for high-throughput data transfer between parent and child processes. The kernel creates a communication stream through file descriptors, enabling one process to send data to another. Processes can use pipes for efficient inter-process communication, with the ker
1 views • 15 slides
Overview of HERDOS TES and SNiPER TES
HERDOS TES and SNiPER TES are discussed in detail, outlining their implementations and distinctive features. The discussion includes insights on TES requirements, concrete implementations, DataBuffer usage, HERD TES reliance on podio, and the migration plan to podio
0 views • 10 slides
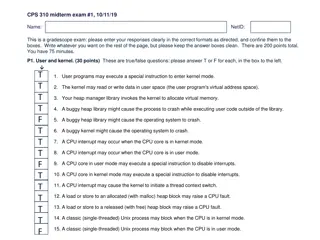
User and Kernel Modes in Operating Systems
The content provided discusses various aspects of user and kernel modes in operating systems through a set of true/false questions related to user programs, CPU interrupts, heap management, and process behavior in different modes. It touches on the role of the kernel in managing virtual memory, hand
0 views • 10 slides
Exploring Web Services at IRIS: Implementations and Coordination
Discover the world of web services at IRIS through a detailed exploration of implementations, international coordination efforts, and the team behind these endeavors. Learn about the definition of web services, practical examples, and the various data and processing services offered by IRIS to suppo
0 views • 24 slides
Noise*: A Verified Secure Channel Protocol Library
Explore Noise*, a library of high-performance secure channel protocol implementations that have been verified for correctness. The Noise protocol examples, such as IKpsk2, showcase key exchange patterns used in applications like WhatsApp and Wireguard VPN. Discover the importance of verified impleme
0 views • 18 slides
Hyper-Parameter Tuning for Graph Kernels via Multiple Kernel Learning
This research focuses on hyper-parameter tuning for graph kernels using Multiple Kernel Learning, emphasizing the importance of kernel methods in learning on structured data like graphs. It explores techniques applicable to various domains and discusses different graph kernels and their sub-structur
0 views • 20 slides
Overview of UNIX and Linux Operating Systems
The UNIX brand encompasses a range of powerful multitasking, multiuser operating systems used by various organizations to develop IT technologies. UNIX internals consist of kernel space and user space, with programs accessing system services rather than hardware directly. The Unix filesystem is a ke
2 views • 36 slides
Coverage-Directed Differential Testing of JVM Implementations
The paper discusses the importance of coverage-directed differential testing for Java Virtual Machine (JVM) implementations. It covers challenges in identifying JVM defects, solutions using test oracles, and examples of JVM behavior discrepancies. The study emphasizes the need for obtaining test cla
0 views • 45 slides
Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
1 views • 25 slides