Reporting Pilot Financial Remedies
Established practices of confidentiality in family financial remedy (FR) cases are being challenged by recent judicial opinions, suggesting a shift towards greater transparency. Exceptions to the general rule of non-reporting are identified, highlighting evolving attitudes towards media reporting an
0 views • 20 slides
Freedom of Speech-Topics 3.5 – 3.6
Delve into the realm of freedom of speech and anonymity through a series of thought-provoking questions on topics like the First Amendment, anonymity, online privacy, and net neutrality. Discover insights on how these concepts intersect with legal rights, law enforcement, and individual expression i
0 views • 26 slides
What Makes Banksy's Paintings So Popular
Banksy's paintings resonate due to their edgy, thought-provoking messages and innovative street art techniques. His anonymity creates a sense of mystery, and his works often appear in unexpected places, capturing public attention. The fusion of art and activism in Banksy's work drives its enduring p
0 views • 5 slides
What Makes Banksy's Paintings So Popular
Banksy's paintings resonate due to their edgy, thought-provoking messages and innovative street art techniques. His anonymity creates a sense of mystery, and his works often appear in unexpected places, capturing public attention. The fusion of art and activism in Banksy's work drives its enduring p
1 views • 5 slides
Self-Care, Resilience, and Preventing Burnout: Essential Tips for Well-Being
This session focuses on the crucial aspects of self-care, resilience, and preventing burnout, emphasizing the importance of psychological personal protective equipment. Experts share valuable insights and actionable tips to help individuals maintain mental well-being amidst challenges. Engage in ful
0 views • 10 slides
Darknet Drug Trafficking Trends and Impacts in 2020
Darknet drug trafficking over the years has shown both upward and downward trends influenced by market shutdowns, exit scams, and the COVID-19 pandemic. Despite challenges, anonymity and cryptocurrency use drive transactions, with cannabis being a popular choice. The evolving landscape maintains ste
0 views • 13 slides
Compact Ring Signatures from LWE - CRYPTO 2021 Research
Research presented at CRYPTO 2021 introduces a compact ring signature scheme using components instantiated from LWE. The scheme allows each signer to sign on behalf of a ring of users, offering properties of unforgeability, anonymity, and compactness. The work explores the possibility of building co
0 views • 25 slides
Exploring a Poignant Holocaust Poem: A 6893 by Anna Sotto
Discover the powerful poem "A 6893" by Anna Sotto, reflecting on the heartbreaking experiences of a Jewish person during the Holocaust. Through the poignant verses, the poem delves into the stripping away of identity and humanity faced by many victims. The questions raised about the anonymity of wri
1 views • 12 slides
Understanding Ethics in Research: Principles and Major Issues
Ethics in research is crucial for ensuring the well-being of participants and upholding moral principles. Key aspects include beneficence, respect for autonomy, informed consent, and freedom from harm. Major ethical issues involve informed consent, beneficence, respect for anonymity and confidential
5 views • 18 slides
Strategic Tourism Demand Forecasting Methods
The chapter delves into qualitative and quantitative approaches for tourism demand forecasting, including the Delphi method and executive opinion juries. It explores advanced forecasting methods and the application of big data analytics in the tourism industry. The focus is on generating expert opin
1 views • 39 slides
Ethical Considerations in Reporting Violence Against Women: Interviewing Victims and Ensuring Consent
It is crucial for journalists reporting on violence against women to interview victims and survivors ethically and respectfully, ensuring informed consent is obtained before sharing their stories. This involves being sensitive to trauma, prioritizing the well-being of the interviewees, and assessing
3 views • 11 slides
Understanding Bitcoin and Cryptocurrency: A Comprehensive Overview
Delve into the world of Bitcoin and cryptocurrency with this comprehensive guide by Ethan Herdrich, an Experiential Learning Specialist. Learn about Bitcoin as a token and protocol, the concept of blockchain, mining, origins in the deep web, anonymity, other cryptocurrencies, and the volatile nature
0 views • 15 slides
Overview of ATM Committee at BUSM
Boston University School of Medicine (BUSM) is committed to providing a supportive learning environment free from mistreatment. The ATM Committee at BUSM focuses on investigating reports of student mistreatment and ensuring prompt, respectful responses. The committee's charge includes identifying an
0 views • 12 slides
Student Experience of Learning and Teaching (SELT) at University of Adelaide
The Student Experience of Learning and Teaching (SELT) at the University of Adelaide is an online survey that allows students to provide valuable feedback on their learning experience. This feedback is instrumental in continuous improvement of courses and teaching methods. The survey is confidential
0 views • 8 slides
Privacy Considerations in Data Management for Data Science Lecture
This lecture covers topics on privacy in data management for data science, focusing on differential privacy, examples of sanitization methods, strawman definition, blending into a crowd concept, and clustering-based definitions for data privacy. It discusses safe data sanitization, distribution reve
0 views • 23 slides
Enhancing Crowd Anonymity with Dummy Jondos
Explore the concept of using dummy jondos to increase anonymity in crowds and mitigate common attacks like eavesdropping and collusion. Learn how the introduction of dummy jondos can impact crowd size and resistance against potential threats, along with considerations for implementation and ensuring
2 views • 30 slides
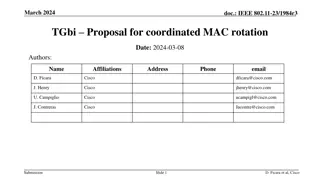
Proposal for IEEE 802.11-23/1984r1 TGbi Coordinated MAC Rotation
The document discusses a proposal for IEEE 802.11-23/1984r1 TGbi focusing on coordinated MAC rotation, EDP epochs, anonymity sets, and group epochs. It introduces concepts like individual and mass rotations, anonymity set size, and hiding in the crowd examples. The coordination for group epochs and
1 views • 10 slides
Student Safeguarding Engagement Session Facilitator Slides
This slide deck example is designed to facilitate student engagement sessions on safeguarding in schools, covering key areas like consent, confidentiality, and anonymity. The slides include activities created by the International Taskforce on Child Protection, Student Voice Committee, to gather stud
2 views • 28 slides
Trust-Based Anonymous Communication Models and Routing Algorithms
This research paper discusses trust-based anonymous communication models and routing algorithms in the context of onion routing, emphasizing the importance of trust in mitigating security risks from adversaries with resources. The paper presents a model of trust and proposes trust-based routing algo
0 views • 65 slides
MIYHS Teacher Training: Importance of Confidentiality and Consent
Maine Integrated Youth Health Survey (MIYHS) teacher training emphasizes the significance of maintaining student confidentiality and obtaining parental consent. Teachers play a crucial role in ensuring student anonymity during survey administration. Understanding the importance of consent and confid
0 views • 14 slides
Peer Evaluation Strategies in SALIS Language Module
Explore the peer evaluation methods used in the School of Applied Language & Intercultural Studies (SALIS) for the FR376 French module. The approach includes criteria such as linguistic quality, interaction management, and drawing lessons for future productions. Rubrics on Loop Forum aid in assessin
0 views • 21 slides
Cybercrime Prosecution Challenges and Strategies in Switzerland
Understanding the jurisdiction and challenges of prosecuting cybercriminals in Switzerland, including issues related to legislation, evidence gathering, perpetrator anonymity, mutual legal assistance, and international cooperation. The role of public and private partnerships in combating cybercrime
0 views • 9 slides
Understanding Independent Foster Care in Northern Ireland
Exploring the Independent Foster Care Sector in Northern Ireland through the perspectives of Independent Foster Carers, Agencies, and key professionals. The research aims to address gaps in knowledge, amplify voices within the sector, and promote evidence-informed practices. Methodologies include qu
0 views • 7 slides
PIR-Tor: Scalable Anonymous Communication Using Private Information Retrieval
Anonymous communication via PIR-Tor allows users to communicate while keeping their identities secret from third parties. This research discusses the background of Tor, performance issues in its architecture, current solutions, design goals for improvement, and key observations for enhancing relay s
0 views • 16 slides
Understanding the Tor Network: An In-Depth Overview
The Tor Network, developed in the mid-1990s, is a volunteer-based network that prioritizes privacy and security for Internet users through encryption and random pathways. By utilizing Onion Routing, Tor preserves anonymity but has limitations such as lack of application-level security and plugin usa
0 views • 13 slides
Official People Matter Survey 2022 Wellbeing Check & Updates
Dive into the official People Matter Survey 2022, discover the importance of your feedback, new updates following sector-wide consultation in 2021, how privacy and anonymity are safeguarded, data collection statement, and more. Your input matters, so make your voice heard in this comprehensive surve
0 views • 8 slides
Understanding Data Security and Privacy: An Overview of k-Anonymity, l-Diversity, t-Closeness, and Reconstruction Attacks
Delve into the realm of data security and privacy, exploring concepts such as k-Anonymity, l-Diversity, t-Closeness, and Reconstruction Attacks. Learn about the importance of privacy concerns, privacy-preserving data sharing, real threats of linking attacks, and specific instances like the GIC Incid
0 views • 44 slides
Anonymization Techniques in Data Privacy
Anonymizing data is crucial to safeguard privacy, prevent data breaches, and enable sharing for various use cases, such as statistics, data science, and data release. Techniques like K-anonymity aim to protect individual identities by grouping data into subsets with shared characteristics. However,
0 views • 24 slides
Ensuring Privacy in Microdata Publishing
This research explores various privacy protection techniques for publishing microdata, focusing on k-anonymity, l-diversity, t-closeness, and EMD models. It discusses the challenges and limitations of each method, highlighting the need for robust privacy guarantees in the handling of sensitive infor
0 views • 20 slides
Traffic Analysis for Measuring Tor from Within
Study by Rob Jansen and team explores traffic analysis techniques to measure Tor from within the network, focusing on website and onion service fingerprinting. The research examines the limitations of entry positions and advantages of middle relays in fingerprinting attacks on Tor. By considering ad
0 views • 25 slides
Dealing with Student Conflict and Incivility in Online Classrooms
Classroom incivility encompasses disruptive behaviors that hinder a conducive learning environment. It affects both students and instructors, leading to stress and discontent. Various uncivil behaviors include dominating discussions, challenging instructors, disputes between students, and demeaning
0 views • 19 slides
Exploring Intertextuality in Medieval Manuscripts
Delve into the concept of intertextuality in medieval manuscripts, focusing on the Châtelaine de Vergy. Discover how manuscript culture and mouvance shape textual mobility and authorship perceptions. Uncover key points on manuscript variations and the dynamic nature of medieval works. Critically ex
0 views • 16 slides
Reevaluating Captain Charles Johnson's A General History of the Robberies and Murders of the Notorious Pyrates
Delve into the ambiguous credibility and authorship of Captain Charles Johnson's historical accounts of infamous pirates like Anne Bonny and Mary Read. Explore themes of gender identity, anonymity, and the complexities surrounding Johnson's mysterious identity in this intriguing analysis.
0 views • 5 slides
Targeted Deanonymization via the Cache Side Channel: Attacks and Defenses
This presentation by Abdusamatov Somon explores targeted deanonymization through cache side-channel attacks, focusing on leaky resource attacks and cache-based side-channel attacks. It discusses the motivation behind these attacks, methods employed, potential defenses, and the evaluation of such att
0 views • 16 slides
IEEE 802.11-23/1984r3 TGbi Proposal for Coordinated MAC Rotation
The document discusses a proposal for coordinated MAC rotation within the IEEE 802.11-23/1984r3 framework. It delves into concepts like Epochs and Coordination, Anonymity Set Size, and Hiding in the Crowd examples. The focus is on enhancing privacy and security through group and individual rotations
0 views • 11 slides
Understanding the People Matter Survey in Victorian Public Sector
The People Matter Survey conducted by the Victorian Public Sector Commission aims to gather independent employee opinions from public sector organizations. It helps in understanding employee engagement, career development, diversity, inclusion, and overall workplace experience. The survey results ar
0 views • 13 slides
UAMS 2020 Employee Engagement Survey Overview and Feedback
In the UAMS 2020 Employee Engagement Survey, eligible employees will participate to help improve engagement. The survey, conducted in February 2020, aims to measure employee alignment within the organization. Past survey results led to positive changes such as increased salaries, more appreciation e
1 views • 7 slides
Understanding the Law School Exam Process
Explore the detailed process of law school exams, including scheduling, anonymity, timed proctored exams, resources, and key dates for the Fall 2020 Final Exam Period. Learn about the requirements for taking exams, accommodations, and the importance of following guidelines set by the Office of Stude
0 views • 34 slides
Non-Interactive Anonymous Router with Quasi-Linear Computation
Explore the concept of a Non-Interactive Anonymous Router with Quasi-Linear Computation, Receiver Insider Protection (RIP), Sender Insider Protection (SIP), and Multi-Client Functional Encryption. The comparison of anonymity notions in NIAR and the motivation behind the non-interactive anonymous shu
0 views • 29 slides
Understanding the Importance of Anonymous Communication in Digital World
Explore the concept of information hiding, including digital watermarking, steganography, covert channels, and anonymous communication. Learn how anonymity can benefit journalists, whistleblowers, activists, executives, and more, while also providing privacy for everyday individuals. Discover the ch
0 views • 56 slides