Budget Execution Challenges in Somalia's Social Sectors
Addressing malnutrition in Somalia is hindered by low budget execution rates in the health and education sectors. Only a small portion of Official Development Assistance (ODA) is channeled through government systems, impacting service delivery and development financing. Donor-supported budgets for h
0 views • 32 slides
PUMM: Preventing Use-After-Free Using Execution Unit Partitioning
Memory-unsafe languages like C and C++ are prone to Use-After-Free (UAF) vulnerabilities. PUMM introduces execution unit partitioning to efficiently tackle this issue. By segregating and managing execution units, PUMM aims to prevent UAF exploits and enhance software security.
0 views • 31 slides
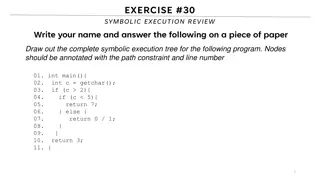
Symbolic Execution Tree for a Program
Generate the complete symbolic execution tree for a given program by annotating nodes with path constraints and line numbers, aiding in understanding program execution flow.
0 views • 26 slides
Evolution of IBM System/360 Architecture and Instruction Set Architectures
The IBM System/360 (S/360) mainframe computer system family, introduced in 1964, revolutionized computing by offering forward and backward compatibility, a unified instruction set architecture (ISA), and a balance between scientific and business efficiency. The critical elements of this architecture
0 views • 18 slides
MIPS CPU Design Using Verilog and Instruction Set Architecture Overview
Explore the world of MIPS CPU design using Verilog with a deep dive into Instruction Set Architecture (ISA), SPIM instruction formats, addressing modes, and more. Learn about the key components such as Program Counter (PC), Instruction Memory (IM), Register Files (RF), Arithmetic Logic Unit (ALU), D
1 views • 29 slides
Understanding Machine Instruction Sets in Computing
This material discusses the characteristics and functions of machine instruction sets in the context of computing technology. It covers essential elements of machine instructions, types of operands, and the operation of the processor. Topics include operation codes, operand references, and instructi
0 views • 57 slides
Understanding the Neglected Provisions of Order XXI CPC, 1908
Explore the overlooked aspects of Order XXI CPC, 1908, focusing on the definitions, types of decrees, modes of execution, procedures for executing decrees, reasons for neglect, impact, recommendations, and conclusion. Learn about neglected provisions like summary execution, execution against legal r
0 views • 14 slides
Understanding Addressing Modes in Computer System Architecture
Addressing modes determine how the operand in an instruction is specified, impacting the interpretation and execution. Implied, stack, immediate, direct, indirect, register direct, register indirect, relative, indexed, base register, auto-increment, and auto-decrement are various addressing modes ex
0 views • 4 slides
Understanding Software Testing: Test Cases, Selection, and Execution
Software testing plays a crucial role in identifying and resolving issues within software products. Test cases, selection, and execution are fundamental aspects of the testing process. Test cases define conditions for testing software functionality, with a focus on repeatability and data specificity
2 views • 36 slides
MIPS Single-cycle Datapath Analysis for Instruction SW
Examine the operation of the single-cycle datapath for a specific MIPS instruction "SW.R4,-100(R16)". This analysis covers the instruction word value, register numbers, control signals, and the logic diagram implementation. Dive into details like instruction word encoding, register file operations,
0 views • 55 slides
In-Depth Look at Pentium Processor Features
Explore the advanced features of the Pentium processor, including separate instruction and data caches, dual integer pipelines, superscalar execution, support for multitasking, and more. Learn about its 32-bit architecture, power management capabilities, internal error detection features, and the ef
0 views • 24 slides
Maximizing Literacy Achievement: Effective Instruction Planning Strategies
Timothy Shanahan from the University of Illinois at Chicago discusses key considerations for planning effective literacy instruction, including scheduling, amount of instruction, content to be taught, and the timing of instruction. Shanahan emphasizes the importance of providing ample literacy instr
1 views • 19 slides
Comprehensive Overview of Georgia's School Improvement Systems
Richard Woods, Georgia's School Superintendent, leads the initiative to enhance Georgia's education system through the Systems of Continuous Improvement. The Instructional Awareness Walk (IAW) program offers support to schools in establishing effective instruction and a conducive learning environmen
0 views • 17 slides
Comprehensive Introduction to Technical Training Instruction Set
Delve into the basics of technical training instruction sets covering 181 different instructions. Explore key concepts such as coil/bit output, analog/process control, program looping, timer/counter functions, and more. Understand the operational characteristics of different instruction categories,
0 views • 19 slides
Variations in Computer Architectures: RISC, CISC, and ISA Explained
Delve into the realm of computer architectures with a detailed exploration of Reduced Instruction Set Computing (RISC), Complex Instruction Set Computing (CISC), and Instruction Set Architecture (ISA) variations explained by Prof. Kavita Bala and Prof. Hakim Weatherspoon at Cornell University. Explo
0 views • 55 slides
Ensuring Security in Persistent Key-Value Stores using Shielded Execution
This content discusses the challenges and solutions for securing LSM-based Key-Value stores in untrusted computing environments using Shielded Execution. It addresses the need for confidentiality, integrity, and freshness of data in persistent storage systems. The research explores Trusted Execution
0 views • 32 slides
Modes of Execution of Decree in Civil Law
The lecture discusses the various modes of execution of decree in civil law, such as execution against a person through arrest and detention, and execution against property. It explains the procedures involved in arrest and detention, including the conditions for release, restrictions on arrest, and
0 views • 9 slides
Understanding Java Memory Management
Explore how memory is managed in Java programs, including memory allocation for code, objects, and execution stack. Learn about memory areas like the execution stack and heap, and understand the concept of activation records in method execution.
0 views • 27 slides
Exploring Instruction Level Parallel Architectures in Embedded Computer Architecture
Delve into the intricacies of Instruction Level Parallel Architectures, including topics such as Out-Of-Order execution, Hardware speculation, Branch prediction, and more. Understand the concept of Speculation in Hardware-based execution and the role of Reorder Buffer in managing instruction results
0 views • 51 slides
Evolution of Execution Methods in Modern Society
Explore the historical and modern methods of execution, from hanging to lethal injection, and the transition towards more civilized approaches. Learn about the contributions of prominent figures like Elbridge Gerry in advocating for humane execution methods. Delve into the commercial rivalry between
0 views • 13 slides
Secure and Efficient Multi-Variant Execution in Distributed Settings
This paper discusses dMVX, a system for secure multi-variant execution in distributed settings to mitigate memory errors and protect against attacks. Using leader and follower variants, diversified program variants run in lockstep to ensure security. The system monitors and replicates I/O results, e
0 views • 35 slides
Certified Professional in Online Instruction: Promoting Quality and Credibility in Distance Education
International Certification Board of Online Instruction (ICBOI) offers the Certified Professional in Online Instruction (CPOI) program to assess knowledge and skills in technology and pedagogy. This certification aims to enhance the quality and effectiveness of online instruction, helping schools ga
0 views • 9 slides
Embedded Computer Architecture - Instruction Level Parallel Architectures Overview
This material provides an in-depth look into Instruction Level Parallel (ILP) architectures, covering topics such as hazards, out-of-order execution, branch prediction, and multiple issue architectures. It compares Single-Issue RISC with Superscalar and VLIW architectures, discussing their differenc
0 views • 49 slides
Hardware-Assisted Task Scheduler for OS Intensive Applications
A hardware-assisted task scheduler called SchedTask is proposed to address the issue of instruction cache pollution in OS intensive applications. By utilizing SuperFunction characterization and a specialized scheduler, the system aims to optimize task execution on different cores for improved perfor
0 views • 28 slides
Understanding Y86-64 Instruction Set Architecture
Explore the Y86-64 instruction set architecture in computer architecture, focusing on processor state, memory, instruction encoding, and operation. Learn about the different instruction formats, registers, condition codes, and how instructions access and modify program state.
0 views • 36 slides
Understanding MIPS Instruction Sets and Binary Execution
This lecture covers the mapping of MIPS instructions to binary for execution, the use of pseudo-instructions to improve code readability, and the handling of large constants. It discusses levels of representation and interpretation, the concept of stored-program computers, addressing in memory, bina
0 views • 50 slides
Understanding Code Execution Graphs and Superblocks in Software Analysis
Explore the concepts of Static Execution Graphs, Dynamic Execution Graphs, Superblocks, hot-path detection, and memory arithmetic in software analysis. Learn about the grouping of blocks, violation tracking, control dependencies, and code behaviors across time through these graphical representations
0 views • 9 slides
Understanding Processes in Operating Systems - ECE344 Lecture 3 Summary
This lecture delves into the essential concepts of processes, threads, and synchronization in operating systems. Key topics covered include units of execution, representation of units of execution in the OS, process execution states, and state transitions. Users, programs, and the role of processes
0 views • 45 slides
InvisiSpec: Making Speculative Execution Invisible
InvisiSpec presents a novel defense mechanism to address speculative execution attacks in the cache hierarchy. By making speculative execution invisible to potential attackers, this holistic approach aims to mitigate the risks associated with exploiting side effects on incorrect paths, such as Spect
0 views • 18 slides
Multicycle Datapath and Execution Steps Overview
This content provides a detailed explanation of a multicycle datapath and the execution steps involved in processing instructions. It covers key elements such as instruction fetching, decoding, memory referencing, ALU operations, branch and jump instructions, as well as memory access for read and wr
0 views • 11 slides
Understanding Symbolic Execution and Directed Automated Random Testing
Symbolic Execution is a method used for analyzing programs to determine inputs causing each part to execute, vital in program testing. However, limitations arise in cases without code availability, hindering definitive path conditions. Directed Automated Random Testing (DART) overcomes this through
0 views • 20 slides
Secure Cloud Applications with Intel SGX - OSDI 2014 Presentation Summary
This presentation discusses the challenges of trusting cloud environments and proposes solutions utilizing Intel SGX technology. It explores the need for secure execution of applications on untrusted cloud platforms, presents existing solutions, and introduces the concept of Haven for private execut
0 views • 33 slides
Understanding Expanding Opcodes in Instruction Set Architectures
Exploring the concept of expanding opcodes in instruction set architectures, this lecture delves into how varying the number of operands affects instruction length and efficiency. By utilizing expanding opcodes, it is possible to accommodate different operand requirements and optimize instruction en
0 views • 27 slides
Rethinking Processes with Threads in Operating Systems
Processes in operating systems traditionally include various resources and execution states, leading to inefficiencies in communication and parallel program execution. By separating the concept of a process from its execution state, modern OSes like Mac, Windows, and Unix introduce threads as lightw
0 views • 29 slides
Parallel Processing in Computer Organization
Computers can be classified based on data and instruction streams, forming various types of structures. Parallel processing levels can be defined based on instruction and data stream categorization, proposed by Michael Flynn in 1972. The instruction cycle consists of steps needed for executing instr
0 views • 44 slides
Python Programming Essentials: Basics, Operators, Expressions, and Control Flow
This segment delves into the fundamentals of Python programming with a focus on essential concepts such as comments, numbers, strings, variables, arithmetic operators, logical operators, order of execution, expressions, and control flow statements like conditional execution and looping. Learn about
0 views • 12 slides
Understanding Operating System Concepts: Multiprogramming, Multiprocessing, Multitasking, and Multithreading
In the realm of operating systems, terms like multiprogramming, multiprocessing, multitasking, and multithreading can often be confusing due to their similar appearance but distinct meanings. These concepts play a crucial role in efficiently managing resources in a computing system, particularly in
0 views • 6 slides
Memory Allocation and Program Execution Overview
Understanding memory allocation is crucial for efficient program execution. This content delves into the importance of memory allocation, considerations for storing data during program execution, and the requirements for allocating memory efficiently. It also explores solutions for managing memory s
0 views • 35 slides
Arithmetic and Logic Instructions: ADD Instruction Overview
The ADD instruction is part of the Arithmetic and Logic Instructions First Group and is used to add a number from a source to a destination and store the result in the specified destination. The instruction affects flags like AF, CF, OF, SF, and ZF. It can operate with immediate numbers, registers,
0 views • 24 slides
Understanding CPU Virtualization and Execution Control in Operating Systems
Explore the concepts of CPU virtualization, direct execution, and control mechanisms in operating systems illustrated through a series of descriptive images. Learn about efficient CPU virtualization techniques, managing restricted operations, system calls, and a limited direct execution protocol for
0 views • 18 slides