UiPath UiABA Exam Success Tips and Tricks
Start here---https:\/\/bit.ly\/3VdbNyq---Get complete detail on UiABA exam guide to crack Business Analyst. You can collect all information on UiABA tutorial, practice test, books, study material, exam questions, and syllabus. Firm your knowledge on Business Analyst and get ready to crack UiABA cert
1 views • 14 slides
UiPath UiABA Exam Success: Tips and Tricks
Start here---https:\/\/bit.ly\/3VdbNyq---Get complete detail on UiABA exam guide to crack Business Analyst. You can collect all information on UiABA tutorial, practice test, books, study material, exam questions, and syllabus. Firm your knowledge on Business Analyst and get ready to crack UiABA cert
2 views • 14 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Cisco 500-420 Certification: Proven Study Techniques & Resources
\nBegin Your Journey Here: \/\/bit.ly\/3vujoOj\n\nDiscover comprehensive insights on the 500-420 exam guide to excel in the Cisco AppDynamics Associate Performance Analyst certification. Gather all essential details including tutorials, practice tests, books, study materials, exam questions, and syl
2 views • 17 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
CERTIFIED BUSINESS MANAGEMENT ANALYST
Certified Business Management Analyst specializing in Manufacturing Operations, Retail Management, and Service Management Analysis. Services include cost savings analysis, make-or-buy decisions, production automation alternatives, and break-even analysis. Case studies provided for practical applicat
3 views • 67 slides
Ready to Ace the Databricks Data Analyst Associate Exam
Begin your journey here at \/\/bit.ly\/3WxlCI3 to access comprehensive details on the Data Analyst Associate exam guide, essential for cracking the Data Analyst certification. Gather insights on Data Analyst Associate tutorials, practice tests, recommended books, study materials, exam questions, and
2 views • 14 slides
The Ultimate Guide to Working with Data Analyst Recruiters
Our specialized data analyst recruiters connect you with top data talent, ensuring the perfect match for your business. With industry expertise and an extensive network, we streamline hiring to elevate your data capabilities and drive success.\n\n\n\n\n\n
0 views • 6 slides
Understanding Behavioural Styles: The Analyst (Technician)
Explore the concept of behavioural styles introduced by David Merrill and Roger Reid in the 1960s, focusing on the Analyst style. This style embodies traits such as organization, setting long-term goals, high standards, duty, analysis, directness, decision-making, task-oriented focus, risk-taking, a
0 views • 28 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding ArcGIS Network Analyst for Spatial Analysis
ArcGIS Network Analyst offers tools for complex routing problems using a unique network model. Learn about networks, elements, attributes, evaluators, and more to enhance spatial analysis capabilities with ArcGIS.
1 views • 11 slides
Certification and Training in Information Security
This content covers various aspects of certification and training in the field of information security, including organizational information security outlines, positions in information security personnel, and professional certifications from renowned organizations. It also provides insights into dif
0 views • 18 slides
a1 data analyst blog
Explore the costs related to Data Analyst Course Fee in India with this nitty-gritty direct. Get it what you'll anticipate to pay for beat programs in 2024, counting variables that impact course expenses. Find reasonable alternatives, compare divers
0 views • 4 slides
Pros and Cons of Certified Financial Analyst Certification
In the financial business, one of the most prominent certifications is the Certified Financial Analyst (CFA) designation.
2 views • 9 slides
Understanding Cyber Security and Risks
Cyber security, also known as IT security or computer security, is crucial for safeguarding information systems from theft, damage, and disruption. With the increasing connectivity of devices through the internet, the importance of cyber security cannot be overstated. Cyber risks encompass cyber cri
2 views • 24 slides
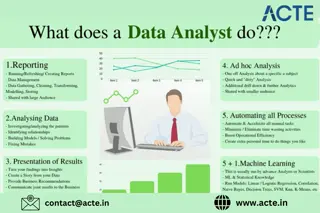
A Day in the Life of a Data Analyst: Unveiling the Role
In the data-driven world of today, data analysts play a pivotal role in transforming raw data into actionable insights. But what does a typical day look like for a data analyst? Here\u2019s a behind-the-scenes look at the diverse and dynamic activiti
1 views • 1 slides
What to Expect from Certified Financial Analyst Training
Certified Financial Analyst (CFA) certification is quite a tricky yet a lucrative path to financial, investment, and portfolio management competence.\n
2 views • 11 slides
Understanding Computer Security Principles and Practices
This excerpt delves into the fundamental concepts of computer security, highlighting key principles such as confidentiality, integrity, and availability. It also discusses the NIST's definition of computer security, key security concepts, levels of impact, and challenges faced in the realm of securi
3 views • 26 slides
Legal Framework on Information Security in the Ministry of Trade, Tourism, and Telecommunication
The legal framework on information security in the Ministry of Trade, Tourism, and Telecommunication, outlined by Nebojša Vasiljević, includes relevant EU legislation such as Regulation No. 460/2004 and Council decisions on network and information security. The EU legislation covers various aspect
0 views • 21 slides
Lucky Cement Limited FY 2020 Analyst Briefing Highlights
Lucky Cement Limited's FY 2020 Analyst Briefing highlights key figures, such as revenue growth, operating profit reduction, and sales quantity in the cement sector. Despite challenges like COVID-19, the company shows resilience with strategic investments and developments.
3 views • 13 slides
Understanding Security Threats and Countermeasures
Explore the diverse threats posed by attackers in the information security landscape, ranging from employee sabotage to hacking incidents. Learn about fundamental security terminology, types of security compromises, and countermeasure strategies to prevent, detect, and correct security breaches. Gai
0 views • 32 slides
Actuarial Science Major Information Session at SMU
The Actuarial Science Major Information Session at SMU is an opportunity for students interested in mathematics and careers in actuary, finance, insurance, and risk management. The program offers two tracks - Actuarial Analyst (AA) and Risk Analyst (RA) - structured after the education framework of
0 views • 6 slides
Analyst Study Guide and How to Crack Exam on Appian Certified Analyst?
Click Here--- \/\/bit.ly\/4d9Wnjt ---Get complete detail on Analyst exam guide to crack Appian Certified Analyst. You can collect all information on Analyst tutorial, practice test, books, study material, exam questions, and syllabus. Firm your knowl
0 views • 9 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Addressing Technology Overload in Middle School: A Policy Analyst Approach
Students at PS/MS 333 Goldie Maple Academy are struggling with excessive technology usage, prompting a Public Policy Analyst to step in and guide them through defining the issue, gathering evidence, identifying causes, evaluating existing policies, developing solutions, and selecting the best one. T
0 views • 8 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
APNIC Internet Resource Analyst Update
Anna Mulingbayan, Senior Internet Resource Analyst and Liaison Officer at APNIC, provides updates on IP address and ASN delegation in the Asia-Pacific region. The content covers IPv4 exhaustion, delegation policies, last /8 delegations, and key policies implemented in 2011. Additionally, it discusse
0 views • 18 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Presentation to Legislative Analyst's Office - Summary Slides
A series of slides containing valuable information presented to the Legislative Analyst's Office. The slides cover various aspects, such as data, analysis, and recommendations, aimed at informing and assisting the legislative process. The visuals and content focus on key points relevant to the offic
0 views • 23 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Exploring the Role of Group Analyst in Addressing Structural Oppression
Delve into the crucial role of group analysts in working with patients affected by institutional and structural oppression, particularly within the context of white supremacy and heteronormativity. Understand the intersectional positionality of the analyst and the distinction between structural oppr
1 views • 12 slides