Comprehensive Guide to Programming in IDL with Pointers and Extensions
Explore the world of programming in IDL with a focus on dynamic variables, heap and pointers, scientific data formats, GUI development, and IDL extensions. Learn about working with pointers, handling dynamic memory, dealing with external software, and examples of code implementation. Discover how to
1 views • 28 slides
Dynamic Memory Allocation in Computer Systems: An Overview
Dynamic memory allocation in computer systems involves the acquisition of virtual memory at runtime for data structures whose size is only known at runtime. This process is managed by dynamic memory allocators, such as malloc, to handle memory invisible to user code, application kernels, and virtual
0 views • 70 slides
Understanding Garbage Collection in Java Programming
Garbage collection in Java automates the process of managing memory allocation and deallocation, ensuring efficient memory usage and preventing memory leaks and out-of-memory errors. By automatically identifying and removing unused objects from the heap memory, the garbage collector frees up memory
14 views • 22 slides
Shortest Paths Algorithms and Applications Overview
This material covers various aspects of shortest path algorithms, focusing on Dijkstra's algorithm with binary heap and its time complexity. It delves into the history of shortest path algorithms, highlighting key authors and their contributions. Additionally, it explores different applications of s
4 views • 27 slides
Enhancing Compost Quality for Organic Farming: Phosphorous-Enriched Compost Preparation
Composting is a natural process crucial for organic farming. Enriched compost improves nutrient supply to crops. Learn how to prepare phosphorous-enriched compost using organic wastes, bio-inoculants, and rock phosphate. Follow a method involving layering organic materials, cow dung, and rock phosph
3 views • 8 slides
Understanding Memory Management in Computer Systems
Explore Carnegie Mellon University's concepts on heap management and memory allocation strategies as detailed in "Computer Systems: A Programmer's Perspective." Dive into topics such as extending the heap, free blocks, and common problems with throughput and memory utilization.
0 views • 21 slides
Understanding Memory Management Concepts at Carnegie Mellon University
Explore advanced topics in memory management as taught at Carnegie Mellon University, including dynamic memory allocation, heap structure visualization, and common programming challenges related to memory utilization and throughput. The content covers practical insights and solutions for optimizing
0 views • 21 slides
Understanding Memory Allocation in C Programming
This content provides insights into memory allocation in C programming. It covers concepts like malloc, calloc, free, and realloc, illustrating how memory can be dynamically allocated and deallocated. The code snippets demonstrate how to work with arrays and pointers, along with explanations on stac
0 views • 44 slides
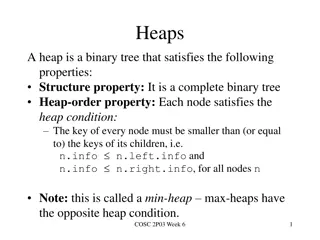
Understanding Heaps in Binary Trees
Heaps are binary trees that adhere to specific properties, such as being complete and satisfying the heap-order property. This involves nodes having keys smaller than or equal to their children. Key operations like removeMin and insert can be performed on heaps efficiently. Array implementations all
0 views • 10 slides
Runtime Checking of Expressive Heap Assertions
Motivated by the unreliability of large software systems due to concurrency bugs and limitations of static analysis, the goal is to enable runtime analysis of deep semantic properties with low overhead. This involves checking expressive heap assertions at runtime with minimal impact on performance,
0 views • 15 slides
Understanding Control Hijacking Attacks in Software Systems
Control hijacking attacks, such as buffer overflows and format string vulnerabilities, allow attackers to take over a target machine by manipulating application control flow. Knowledge of C functions, system calls, CPU, and OS used is crucial for executing these attacks successfully. This summary pr
1 views • 55 slides
Understanding Control Hijacking Attacks and Defenses
Control hijacking attacks pose a significant threat by allowing malicious actors to manipulate data and control flow within a system. This article explores common attack methods like stack smashing and heap spraying, along with defenses such as fixing bugs, implementing platform defenses, and markin
1 views • 36 slides
Buffer Overflows in CSE351 Autumn 2017
Explore buffer overflows in CSE351 Autumn 2017, covering topics like memory layout, stack, heap, and defenses against buffer overflows. Learn about important concepts such as input buffers, code injection, and memory allocation examples, with insights into x86-64 Linux memory layout.
0 views • 33 slides
Understanding Memory Layout in Computer Systems at Carnegie Mellon
Explore the memory layout in computer systems through the lens of Carnegie Mellon University's advanced topics in machine-level programming. Learn about buffer overflow vulnerability protection, memory allocation examples, x86-64 Linux memory layout, and addressing schemes. Dive into practical examp
2 views • 47 slides
Understanding Heaps - A Comprehensive Overview
Heaps are hierarchical data structures that prioritize the most important elements for quick access. This article explores the concept of heaps, types of heaps (such as min and max heaps), abstract data type, practical uses over binary search trees, storing heaps in memory with arrays, manipulations
0 views • 17 slides
Understanding Priority Queues and Heaps in Data Structures
Priority queues prioritize item retrieval based on value, contrasting with traditional queues that follow a first-in-first-out approach. Priority queues efficiently manage items based on their importance, often utilized in scenarios like emergency rooms or air traffic control. Heaps, a form of binar
0 views • 20 slides
Comprehensive Overview of Binary Heaps, Heapsort, and Hashing
In this detailed review, you will gain a thorough understanding of binary heaps, including insertion and removal operations, heap utility functions, heapsort, and the efficient Horner's Rule for polynomial evaluation. The content also covers the representation of binary heaps, building initial heaps
0 views • 24 slides
Data Structures and Heaps in Computer Science - Lecture 10 Overview
Explore the concept of heaps and heapsort in data structures, focusing on the binary heap data structure as an array object that resembles a nearly complete binary tree. Learn about binary tree representations, heap properties, and vertex assignments in a linear array to enhance search efficiency. U
1 views • 33 slides
Soft Heap and Soft Sequence Heaps: Properties and Applications
Explore the properties and applications of Soft Heap and Soft Sequence Heaps, discussing how corruption handling and selection functions are optimized in these data structures. The concept of car-pooling and the simplification of heap operations are highlighted, along with references to relevant res
1 views • 10 slides
Overview of Soft Sequence Heaps in Algorithms
Soft sequence heaps are a specialized data structure designed to handle corruptions in heap operations efficiently. This technology, introduced at Aarhus University, simplifies heap manipulation, particularly in car-pooling and other applications, with a focus on minimizing corruptions during extrac
0 views • 10 slides
Understanding Heap Sort in Data Structures
Heap Sort, a sorting algorithm based on the concept of a heap data structure, is explained in detail. The properties of a heap, its implementation using a complete binary tree, and its application in priority queues are discussed. The process of building a heap, inserting elements, and sorting them
0 views • 7 slides
Understanding Heap Overflows: An Introduction to Exploit Development
Learn about heap overflows in exploit development, including heap structure, memory maps, exploiting vulnerabilities, and controlling writes in the heap. Understand the difference between stack and heap, viewing heap in gdb, targeted exploit techniques, and the challenges of controlling EIP in the h
0 views • 17 slides
Understanding Priority Queues and Heap Data Structures
Priority queues play a key role in computer science algorithms by managing data based on priority levels. The use of heap data structures enhances the efficiency of priority queue operations. This tutorial covers the basics of priority queues, their applications, different implementations such as li
0 views • 30 slides
Abstract Domains for Lists and Heap Structures: A Comprehensive Overview
Explore the concepts of quantified data automata on skinny trees, automatic shapes in static analysis, universally quantified properties on lists, heap configurations with skinny trees, and the extension of quantified data automata over lists. Dive into the abstract domain of automata to capture inf
1 views • 20 slides
Heapsort and Heaps: A Generic Algorithm for Sorting
This content discusses the concept of heapsort and heaps in the context of sorting algorithms. It covers a generic algorithm for sorting a sequence of numbers in non-decreasing order, detailing different implementations and time requirements for inserting and removing elements from a set. A clever c
0 views • 50 slides
Understanding Heap Data Structure Implementation
Explore the implementation of a heap data structure through a complete binary tree concept, array representation, adding elements, removing elements, and avoiding swaps. Learn the steps involved in adding, removing, and organizing elements within a heap for efficient data storage and retrieval.
0 views • 17 slides
Understanding Heap Sort and Binary Search Tree Concepts
Learn about Heap Sort for sorting elements in ascending or descending order, Priority Queue as a data structure supporting key operations, Binary Trees with recursive definitions, and exercises involving priority queue operations. Explore the concepts through visual aids and examples provided in the
0 views • 18 slides
Understanding Heap Overflow Attacks
A heap is a collection of variable-size memory chunks managed by the program. Heap overflow attacks occur when malicious actors corrupt heap memory, potentially allowing them to overwrite data and execute arbitrary code. This poses a significant security risk. The process involves manipulating heap
2 views • 19 slides
Implementing Heaps: Node Operations and Runtime Analysis
Understanding the implementation of heaps involves knowing various node operations like finding the minimum node, last node, next open space, children, and parent. The runtime analysis of heap operations such as peekMin, removeMin, and insert are crucial for optimizing performance. This recap covers
0 views • 9 slides
Understanding Priority Queues and Heaps in CSE 373 Lecture
Today's lecture in CSE 373 covers the Priority Queue Abstract Data Type (ADT), the properties of heaps, and their implementations. Key topics include the completeness property of heaps, different priority queue implementations such as the binary search tree for faster insert and find operations, and
0 views • 21 slides
A Comparative Analysis of Heap Specification Approaches
This presentation discusses various approaches to heap specification, including ownership systems, dynamic frames, permissions, and capabilities. It explores challenges related to invariants and frames, showcasing examples from RockBand and Object state specifications. The discussion covers tools li
0 views • 11 slides
Understanding Memory Management Tradeoffs in Web Browsers
Explore the tradeoffs between memory usage, CPU cost, and performance in web browsers. Learn about setting heap limits, Pareto optimality, and compositional heap limit rules to optimize memory usage efficiently.
1 views • 18 slides
Binary Trees and Heap Implementation in Java
Explore the concepts of binary trees, heap implementation, and traversal techniques in Java through engaging peer instruction materials by Cynthia Lee. Learn about heap uniqueness, in-place heapsort, and generic binary trees. Test your knowledge with reading quizzes and analyze heap outcomes based o
0 views • 27 slides
Overview of SB 850 Homeless Emergency Aid Program (HEAP)
SB 850 establishes the Homeless Emergency Aid Program (HEAP) to provide flexible block grant funds to address immediate homelessness challenges in California. The program moves the Homeless Coordinating and Financing Council (HCFC) to the BCSH Agency and designates the BCSH Secretary as the HCFC Cha
0 views • 33 slides
Dynamic Memory Management Overview
Understanding dynamic memory management is crucial in programming to efficiently allocate and deallocate memory during runtime. The memory is divided into the stack and the heap, each serving specific purposes in storing local and dynamic data. Dynamic memory allocators organize the heap for efficie
0 views • 31 slides
Understanding Memory Management in C Programming
The discussion covers various aspects of memory management in C programming, including common memory problems and examples. It delves into memory regions, stack and heap management, and static data. The examples illustrate concepts like static storage, heap allocation, and common pitfalls to avoid.
0 views • 24 slides
CSE 545 Heap Challenges Overview
In CSE 545, students can expect a series of challenges related to heap exploitation techniques. The assignments involve releasing new challenges with specific deadlines and combining the points earned from previous challenges. The grading system is structured to allocate percentages to each assignme
0 views • 32 slides
Understanding CPU and RAM Relationship in Memory Segments
A program's address space consists of four segments - code, static data, stack, and heap. Each segment plays a crucial role in memory allocation and management. The OS and C++ runtime handle the allocation and deallocation of memory in the heap segment. Garbage collectors in certain languages aid in
0 views • 22 slides
Understanding Heap Exploitation Techniques in CSE 545 Fall 2020
This collection of images covers various heap exploitation techniques discussed in CSE 545 Fall 2020, such as fastbin use-after-free vulnerabilities, tcache poisoning, double-free exploits, metadata manipulation, and more. The images depict scenarios involving tcache, fast bins, unsorted bins, and f
0 views • 72 slides
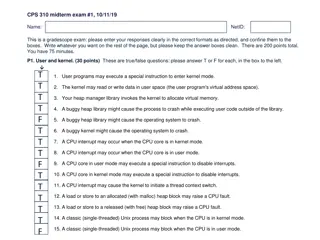
Understanding User and Kernel Modes in Operating Systems
The content provided discusses various aspects of user and kernel modes in operating systems through a set of true/false questions related to user programs, CPU interrupts, heap management, and process behavior in different modes. It touches on the role of the kernel in managing virtual memory, hand
0 views • 10 slides