How to Resolve QuickBooks Banking Error 9999?
How to Resolve QuickBooks Banking Error 9999?\nStuck with QuickBooks Banking Error 9999? Don't fret! This frustrating error disrupts bank connection in QBO. Fear not! Our guide equips you with solutions. Try waiting, checking credentials, or adjusting firewalls. If those fail, reconnect your bank ac
0 views • 4 slides
Protect Your Digital Identity: Cyber Hygiene Best Practices
Cyber hygiene involves following best practices to safeguard personal data in the digital realm. With the increasing value of personal data and evolving technology, individuals must take proactive steps such as using reputable antivirus software, network firewalls, updating software regularly, using
0 views • 25 slides
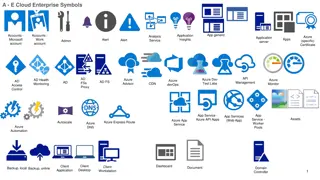
Symbolic Representation of Azure Cloud Enterprise Services
The images depict a variety of symbols representing different Azure cloud enterprise services, including application insights, analysis, monitoring, security, storage, virtual networks, and more. Each symbol represents a specific aspect or component of Azure services, such as VPN gateways, firewalls
0 views • 6 slides
Benefits and Structure of VoIP for Business
VoIP offers various benefits for businesses, including cost savings, increased productivity, and feature-rich communication. It allows seamless voice networks, mobility, and integration of data applications with phones. The traditional phone system is likely to be replaced by VoIP. The VoIP structur
0 views • 42 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Overview of .NG Registry Operations by NIRA
Nigerian Internet Registration Association (NIRA) manages Nigeria's country code top-level domain (.ng). NIRA was established in 2005 after the delegation of .ng to Nigeria. The .ng Registry design includes a 3R model, public WHOIS server, EPP interface, and security measures like redundant site net
5 views • 10 slides
Understanding Network Security: Hijacking, Denial of Service, and IDS
This content delves into the concepts of spying and hijacking in network security, covering topics such as eavesdropping on packets, injecting packets into streams, denial of service attacks, and defense mechanisms like firewalls and IDS. It explores low-level attacks and defenses, including ARP cac
1 views • 81 slides
Password Cracking Techniques and Remote Desktop Access Setup
Explore various password cracking methods such as offline and online techniques using tools like Hydra, alongside setting up remote desktop access on Windows VMs to gain remote control over services. Learn about preparing Windows VMs, disabling firewalls, and enabling remote desktop assistance for e
0 views • 12 slides
Active Response Mechanism for IaaS Cloud Security
Stepping-stone attacks in IaaS clouds pose a new threat where attackers compromise vulnerable VMs to launch attacks against external hosts. This research explores the necessity of self-protection mechanisms for IaaS providers, emphasizing active response to detect and stop outgoing attacks at edge f
0 views • 24 slides
Understanding Enterprise Network Security and Firewalls
Exploring key aspects of enterprise network security, this presentation delves into topics such as perimeter control, host-based security, intrusion detection, and various types of firewalls. It highlights filtering rulesets, requirements for outbound traffic, and the importance of dynamic packet fi
0 views • 19 slides
Understanding Malware: Types, Symptoms, and Countermeasures
Malware is malicious software that can alter computer settings, behavior, files, services, ports, and speed. Sources of malware include insufficient security, honeypot websites, free downloads, torrents, pop-ups, emails, and infected media. Symptoms of malware include unusual computer behavior, slow
0 views • 9 slides
Essential Tips to Prevent Cyber Attacks - Protect Your Data Safely
Learn how to protect your digital assets with these effective tips for preventing cyber attacks. Discover strategies like changing passwords regularly, updating operating systems and applications, using endpoint protection software, being cautious with RDP access, utilizing firewalls and IPS, and em
0 views • 10 slides
Understanding Network Security Vulnerabilities and Attacks
Explore the world of network security vulnerabilities and attacks, including Denial-of-Service (DoS) and Distributed-Denial-of-Service (D-DoS), security flaws in the TCP/IP protocol suite, ICMP attacks, routing attacks, and TCP attacks. Learn about common security vulnerabilities such as address spo
0 views • 36 slides
Ethics in Cybersecurity: Evolution, Challenges, and Solutions
Explore the evolution of cybersecurity, from the days of firewalls to modern cybersecurity threats like viruses and ransomware. Understand the importance of ethics in cybersecurity, as it plays a vital role in building strong defense mechanisms to secure personal and enterprise data effectively.
0 views • 18 slides
New Generation Network Security System Evolution and Implementation
The presentation outlines the evolution of network security systems, focusing on the transition from traditional firewalls to next-generation systems like intrusion detection systems. It highlights the limitations of current systems in detecting internal threats and the need for advanced solutions t
0 views • 9 slides