Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
2 views • 46 slides
Understanding Cybersecurity Threats and Facebook Security
In today's digital landscape, cybersecurity threats are ever-present, ranging from phishing to ransomware. This presentation by Paul Haithcock sheds light on protecting networks and data. It also emphasizes the importance of securing Facebook accounts amidst the prevalence of cybercriminal activitie
1 views • 15 slides
Comprehensive Digital Risk Assessment Guide for Businesses
Conducting a digital risk assessment is vital for securing your business against threats like viruses, malware, hackers, and human errors. This guide outlines key areas to focus on, such as identifying critical assets, assessing potential impacts of breaches, prioritizing threats, utilizing tools li
3 views • 4 slides
Industrial Cybersecurity Market Worth $49.53 Billion by 2030
Industrial Cybersecurity Market, Cybersecurity, Network Security, Cloud Security, Cloud computing, Endpoint Security, Threat Management, Industrial Cybersecurity\n
1 views • 4 slides
Enhance Your Protection with MDR Cyber Security Services in Dallas
Do you wish to improve your security in Dallas against cyber threats? This is exactly where MDR Cyber Security services from Blackswan Cybersecurity can come in handy. While more complex forms of cyber threats and data breaches are becoming more popular, corporations need to acquire modern security
4 views • 8 slides
How Do I Ensure That My Cybersecurity Solutions Are Up To Date With Emerging Threats
Don't let new threats catch you off guard! Learn how to keep your cybersecurity solutions up-to-date and defend your data effectively.
1 views • 5 slides
Cybersecurity Risks for Remote CISTAR Facilities Study
Study explores cybersecurity risks for proposed remote CISTAR facilities using Industrial Control Systems that may be susceptible to cyber, sabotage, and other threats. Recent data indicates an increase in targeted cyberattacks on the energy sector, emphasizing the importance of addressing vulnerabi
1 views • 25 slides
Exploring Adversarial Machine Learning in Cybersecurity
Adversarial Machine Learning (AML) is a critical aspect of cybersecurity, addressing the complexity of evolving cyber threats. Security analysts and adversaries engage in a perpetual battle, with adversaries constantly innovating to evade defenses. Machine Learning models offer promise in combating
0 views • 43 slides
Cybersecurity Career Path Overview
Discover the exciting world of cybersecurity with insights into different roles, resources for learning, career progression, and the importance of cybersecurity in today's digital landscape. Explore job roles like Cybersecurity Engineer, Incident Responder, Data Scientist, and more to build a succes
0 views • 11 slides
Cyber Threats and Security Controls Analysis for Urban Air Mobility Environments
The Urban Air Mobility (UAM) environment, with its service-oriented architecture, faces various cyber threats related to end-users, cyber-physical systems, cloud services, and on-premise computing. Threats include unauthorized interception of data, phishing attacks, and Denial of Service (DoS) incid
1 views • 9 slides
Comprehensive Airport Cybersecurity Quick Guide and Assessment Tool
This project by the National Safe Skies Alliance aims to provide airports with a comprehensive Cybersecurity Quick Guide and Assessment Tool. The guide helps airport managers understand and address cybersecurity issues while the assessment tool evaluates the maturity of their cybersecurity efforts.
0 views • 24 slides
Ensuring Business Security: Cybersecurity Webinar Insights
Explore cybersecurity insights from Ronnie Viera, a seasoned professional in IT and cybersecurity, covering topics such as common threats, cybersecurity basics, and the importance of protecting personal information. Gain valuable knowledge on cybersecurity measures for safeguarding your business aga
0 views • 18 slides
Cybersecurity 101 - Protecting yourself and Your Company from Internet Threats
Learn essential cybersecurity tips to safeguard yourself and your company from internet threats. Stay secure with our practical guide.\n
2 views • 6 slides
Workshop on Cybersecurity Professionalism & Ethics
Explore the core concepts of professionalism and ethics in cybersecurity through this interactive workshop funded by the National Centers of Academic Excellence in Cybersecurity grant. Topics include defining professionalism, key skills for building professionalism, and understanding ethics in the w
0 views • 16 slides
Understanding Cyber Threats and the Role of Defenders in Organizations
Explore the world of cyber threats, including phishing, malware, and data breaches, and understand the importance of being a defender in your organization. Learn about key security mechanics, evolving threats, and the essential role of human vigilance in cybersecurity.
0 views • 17 slides
Coastal Challenges: Threats and Uses Analysis
The Year 9 Geography homework booklet focuses on the topic of coasts, emphasizing grid references and mapping skills. Students are tasked with identifying grid references for shapes, drawing specific shapes on grids, and demonstrating understanding of 4 and 6 figure grid references. Additionally, in
0 views • 13 slides
Cybersecurity Workforce Management: Engage, Empower, Elevate
Explore the intricacies of Cybersecurity Workforce Management through engaging, empowering, and elevating your team. Discover the goals, challenges, and executive orders driving the cybersecurity workforce landscape, along with strategies to enhance workforce capabilities. Unveil the essence of pers
0 views • 27 slides
Understanding Security Threats and Vulnerabilities in Computer Systems
In computer security, threats exploit vulnerabilities to breach security and cause harm. Vulnerabilities arise from system weaknesses, attacker access, and capability. Threats include spoofing, data tampering, repudiation, information disclosure, denial of service, and elevation of privilege. Catego
0 views • 13 slides
Cybersecurity and Computer Science Education Projects at UH Maui College
UH Maui College, supported by NSF, conducts various cybersecurity and computer science education initiatives led by Debasish Bhattacharya. The projects aim to enhance cybersecurity education, curriculum development, and workforce training, catering to a diverse student population. The college has re
0 views • 16 slides
Shovel-Ready Projects Initiative for Cybersecurity Innovation in Canada
This proposal outlines the launch of the Shovel-Ready Projects Initiative aimed at advancing cybersecurity innovation and talent development in Canada. The program, led by the National Cybersecurity Centre (NCC), seeks to fund eligible projects that enhance cybersecurity capabilities through researc
0 views • 19 slides
Mobile Issues and Cyber Threats in Nigeria - Presentation by Dr. J.O. Atoyebi, NCC
Evolution of GSM in Nigeria, the impact of mobile phone deregulation, and the rise of cyber threats highlighted in a presentation by Dr. J.O. Atoyebi of the Nigerian Communications Commission. The report reveals Nigeria's position in global internet security threats and the challenges faced by the c
0 views • 7 slides
Enhancing Cybersecurity for Improved Insurability and Risk Management
In this resource, cybersecurity experts provide insights on improving cybersecurity insurability and minimizing rates. The content covers topics such as the cyber risk landscape, cyber insurance landscape, ransom payments, and ways to enhance cybersecurity measures. Key points include assessing info
1 views • 21 slides
Recognizing and Preventing Insider Threats in National Security
Insider threats pose a significant risk to national security and industry, involving individuals using authorized access to carry out harmful actions. This content covers the definition of insider threats, indicators, consequences, and ways to recognize and report suspicious behaviors. It emphasizes
0 views • 15 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Financial Management and Cybersecurity: Essential Tips for Treasurers
A comprehensive guide covering topics such as budget development, treasurer's role responsibilities, and cybersecurity basics for treasurers. Learn about financial sustainability, board commitments, and protecting against cybersecurity threats like ransomware and spoofing scams. These insights aim t
0 views • 13 slides
Understanding Cyber Threats in Today's Digital Landscape
Cyberspace is a vast realm encompassing the Internet, where we engage in various activities ranging from communication to entertainment. With the majority of children exposed to the online world, cybersecurity awareness is crucial to tackle the rising cyber threats. These threats include job frauds,
0 views • 33 slides
Machine Learning for Cybersecurity Challenges: Addressing Adversarial Attacks and Interpretable Models
In the realm of cybersecurity, the perpetual battle between security analysts and adversaries intensifies with the increasing complexity of cyber attacks. Machine learning (ML) is increasingly utilized to combat these challenges, but vulnerable to adversarial attacks. Investigating defenses against
0 views • 41 slides
Understanding Experiments and Threats to Validity
Explore the world of experimental research, internal and external validity, threats to validity, and the importance of proper study design in ensuring the credibility of research results. Learn about confounding variables, threats to internal validity such as environmental factors and group comparis
0 views • 15 slides
Ethics in Cybersecurity: Evolution, Challenges, and Solutions
Explore the evolution of cybersecurity, from the days of firewalls to modern cybersecurity threats like viruses and ransomware. Understand the importance of ethics in cybersecurity, as it plays a vital role in building strong defense mechanisms to secure personal and enterprise data effectively.
0 views • 18 slides
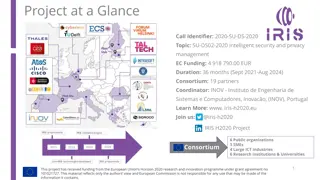
IRIS H2020 Project - Enhancing Cybersecurity for SMART CITIES
The IRIS H2020 project is dedicated to enhancing cybersecurity for SMART CITIES by developing a framework that supports European CERT and CSIRT networks in detecting, sharing, and responding to cybersecurity threats in IoT and AI-driven ICT systems. The project aims to minimize the impact of cyberse
0 views • 5 slides
Defense Industrial Base (DIB) Cybersecurity Training Overview
This training module focuses on the importance of cybersecurity in the Defense Industrial Base (DIB) sector, particularly highlighting the Cybersecurity Maturity Model Certification (CMMC) and its implications for organizations seeking certification. The content includes insights on incident reporti
0 views • 10 slides
Cybersecurity Strategy in Japan - Roles of NISC and Basic Act Overview
The National Center of Incident Readiness and Strategy for Cybersecurity (NISC) plays a crucial role in Japan's cybersecurity landscape, integrating policies and handling cyber attacks 24/7. The Basic Act on Cybersecurity, enforced since January 2015, establishes a clear legislative framework and or
0 views • 12 slides
Navigating Current and Emerging Cyber Threats: Leadership Insights
Delve into the realm of current and emerging cyber threats with a focus on leadership considerations. Understand the evolving landscape of cyber risks, the importance of cyber expertise in leadership planning, and the essential role of cybersecurity in today's digital world. Explore the various thre
0 views • 16 slides
Understanding Threats and Attacks in Information Systems
Threats and attacks pose risks to information systems through vulnerabilities that can be exploited, leading to data loss, system unavailability, and compromised security. Four primary classes of threats include unstructured threats from inexperienced individuals, structured threats from skilled hac
0 views • 21 slides
Comparison of Traditional and Cyber Threat Assessment Methodologies
In the digital age, understanding cyber threats alongside traditional threats is crucial. Cyber adversaries operate globally and are hard to identify, posing challenges for intelligence agencies. The ease of acquiring cyber skills and resources makes cyber threats dynamic and dangerous. Classical cy
0 views • 17 slides
Navigating CISO Executive Search Tips for Hiring Top Cybersecurity Talent
A world that is becoming ever more networked demands robust cybersecurity leadership. The threats that feature on the cyber radars of today's organizations are growing at a minute rate, and so the CISO plays a much-needed role. Still, it is never easy to find the right talent through a successful CI
0 views • 5 slides
Understanding CYBEX - Cybersecurity Information Exchange Techniques
CYBEX introduces a new cybersecurity paradigm focusing on identifying weaknesses, minimizing vulnerabilities, and sharing attack heuristics within trusted communities. It emphasizes the importance of information exchange, policy, and identity assurance in combating cyber threats. The model aims to s
0 views • 14 slides
Interacting Safely in a Digital Setting: Cybersecurity Tips and Tricks
In our increasingly interconnected world, ensuring cybersecurity is crucial to safeguard sensitive information from potential threats. This module covers essential cybersecurity practices, such as using VPNs and antimalware, maintaining privacy online, and understanding netiquette. Learn how to enha
0 views • 15 slides
Shadow: Scalable and Deterministic Network Experimentation in Cybersecurity
The presentation discusses the concept of deterministic experimentation in cybersecurity, emphasizing the importance of experimental control and scalability in large distributed systems like Tor. It introduces Shadow, a network simulator designed to achieve repeatable and realistic experiments for r
0 views • 15 slides
Framework Roadmap Overview - July 2018
The Framework Roadmap draft highlights key areas of development relevant to the Framework, including Confidence Mechanisms, Cyber Attack Lifecycle, Cybersecurity Workforce, Cyber Supply Chain Risk Management, Federal Agency Cybersecurity Alignment, Governance and Enterprise Risk Management, Identity
0 views • 7 slides