CYBERSECURITY AWARENESS MONTH 2023
Join us for Cybersecurity Awareness Month 2023 to learn how to stay safe online. Discover the importance of cybersecurity, find easy ways to protect yourself, and get involved in raising awareness.
6 views • 23 slides
Cybersecurity and Supply Chain Risk Management: Best Practices for Procurement
The best practices for managing cybersecurity and supply chain risks in procurement. This book covers topics such as supply chain attacks, evaluating cybersecurity risks, vendor risk assessment, and implementing effective procurement strategies.
7 views • 23 slides
REWIRE Cybersecurity Skills Alliance
REWIRE Cybersecurity Skills Blueprint and the Skills Intelligence behind it, as well as the key aspects of cybersecurity skills and the proposed categories for future development.
2 views • 21 slides
Instrument human capital cybersecurity mkb bedrijven
This concise instrument helps small and medium-sized businesses in the Netherlands enhance their cybersecurity by leveraging human capital. It provides practical tips and guidance on organizing cybersecurity within the company, focusing on employees (internally) and professionals/suppliers/advisors
1 views • 59 slides
Cybersecurity Industry Call for Innovation (CyberCall)
Submit your innovative project proposal for the CSA Cybersecurity Industry Call for Innovation. Enhance cybersecurity in a rapidly evolving industry.
0 views • 19 slides
Safeguarding Tampa's Business Landscape_ The Crucial Role of Managed Cybersecurity Services
Explore the significance of managed cybersecurity services for Tampa's businesses through our detailed PDF guide. It highlights how investing in sophisticated cybersecurity measures can be a game-changer, offering peace of mind by protecting against data loss, financial fraud, and reputation damage.
1 views • 6 slides
Empowering NNSA Cyber Professionals Through Enterprise Tools and Data Analytics
NNSA's Office of the Chief Information Officer is enhancing their cybersecurity capabilities by leveraging Enterprise Cybersecurity Data Integration architecture and strategic partnerships. This initiative focuses on expanding data sources, enabling correlation, and using resilient engineering for e
0 views • 10 slides
Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
1 views • 46 slides
Challenges in Cybersecurity Implementation: A Philippine Perspective
A presentation discussing the challenges in cybersecurity implementation specifically in the context of the Philippines. It covers the PPT framework (People, Process, Technology), classes of security measures based on the Philippines Data Privacy Act, roles and responsibilities, best practices for I
1 views • 18 slides
C2M2 Version 2.1 Cybersecurity Model Overview
The Cybersecurity Capability Maturity Model (C2M2) Version 2.1 provides a comprehensive framework for evaluating and improving cybersecurity capabilities within an organization. It outlines best practices and maturity levels across various domains to enhance cyber resilience and risk management, ser
4 views • 10 slides
Cybersecurity Risk Management in K-12 Education: Challenges and Strategies
Facing a surge in cyberattacks, K-12 schools struggle with limited funds, expertise, and staff for cybersecurity. This leads to vulnerabilities that make them prime targets for hackers. Lack of dedicated cybersecurity resources and training exacerbates the risks, highlighting the urgent need for com
1 views • 47 slides
Which and How of Cybersecurity Frameworks
Navigate the complex landscape of cybersecurity frameworks with expert guidance on identifying the perfect fit for your organization. Explore various frameworks such as IRAP, SOC2, ISO 27001, and learn the advantages of selecting the right one. Understand the importance of compliance, certification,
3 views • 41 slides
Why Partnering with a CISO Recruiter is Essential for Cybersecurity Success
\"Why Partnering with a CISO Recruiter is Essential for Cybersecurity Success\" explores the crucial role of specialized recruiters in finding top-tier cybersecurity leaders. Discover how a CISO recruiter enhances your organization\u2019s security posture by leveraging expertise, extensive networks,
0 views • 9 slides
Industrial Cybersecurity Market Worth $49.53 Billion by 2030
Industrial Cybersecurity Market, Cybersecurity, Network Security, Cloud Security, Cloud computing, Endpoint Security, Threat Management, Industrial Cybersecurity\n
1 views • 4 slides
Empowering Women in Cyber: CyberFirst Girls Competition
Embrace the future of technology and cybersecurity by joining the CyberFirst Girls Competition. Inspire the next generation of women to pursue careers in tech and make a difference in the world of cybersecurity. Explore opportunities, register, and support diversity in the cyber sector. #CyberFirst
0 views • 17 slides
Cybersecurity Expert Shiva V. Parasram - Profile and Advice
Shiva V. Parasram is a renowned figure in cybersecurity, serving as a Director, Cybersecurity Instructor, Penetration Tester, and Forensic Investigator. He shares valuable insights, tools, and tips for handling security breaches and hacks effectively, along with essential advice for safeguarding you
0 views • 17 slides
Cybersecurity Risks for Remote CISTAR Facilities Study
Study explores cybersecurity risks for proposed remote CISTAR facilities using Industrial Control Systems that may be susceptible to cyber, sabotage, and other threats. Recent data indicates an increase in targeted cyberattacks on the energy sector, emphasizing the importance of addressing vulnerabi
1 views • 25 slides
Exploring Adversarial Machine Learning in Cybersecurity
Adversarial Machine Learning (AML) is a critical aspect of cybersecurity, addressing the complexity of evolving cyber threats. Security analysts and adversaries engage in a perpetual battle, with adversaries constantly innovating to evade defenses. Machine Learning models offer promise in combating
0 views • 43 slides
Cybersecurity Career Path Overview
Discover the exciting world of cybersecurity with insights into different roles, resources for learning, career progression, and the importance of cybersecurity in today's digital landscape. Explore job roles like Cybersecurity Engineer, Incident Responder, Data Scientist, and more to build a succes
0 views • 11 slides
Enhancing California's Election Cybersecurity Readiness
California has taken significant steps to bolster its election cybersecurity readiness, including rigorous source code reviews, red team testing, and open-ended penetration testing. The state has visited fusion centers, engaged local election officials, upgraded technology infrastructure, and establ
0 views • 6 slides
Cybersecurity Tabletop Exercise Overview
In this cybersecurity tabletop exercise, participants engage in scenario-based discussions and action planning to enhance readiness for cyber incidents. The exercise covers welcome and introductions, agenda review, administrative details, benefits, objectives, and more to improve response capabiliti
0 views • 40 slides
Comprehensive Airport Cybersecurity Quick Guide and Assessment Tool
This project by the National Safe Skies Alliance aims to provide airports with a comprehensive Cybersecurity Quick Guide and Assessment Tool. The guide helps airport managers understand and address cybersecurity issues while the assessment tool evaluates the maturity of their cybersecurity efforts.
0 views • 24 slides
Cybersecurity Entrepreneurship Workshop Highlights
The cybersecurity entrepreneurship workshop, held on September 27, 2019, featured sessions on privacy concerns in a 5G world, market definition and analysis, and a cyber tech competition. Topics included BYOD security, vulnerability management, market segmentation, and competitive landscape analysis
0 views • 4 slides
Ensuring Business Security: Cybersecurity Webinar Insights
Explore cybersecurity insights from Ronnie Viera, a seasoned professional in IT and cybersecurity, covering topics such as common threats, cybersecurity basics, and the importance of protecting personal information. Gain valuable knowledge on cybersecurity measures for safeguarding your business aga
0 views • 18 slides
Cybersecurity and Personal Finance: A Tale of Appily Ever After
Explore the engaging story of Ana's spending habits and in-app purchases, as she navigates through the world of digital finance and cybersecurity. Discover valuable lessons on responsible spending, making informed choices, and staying safe online while managing personal finances. With vivid visuals
0 views • 6 slides
Workshop on Cybersecurity Professionalism & Ethics
Explore the core concepts of professionalism and ethics in cybersecurity through this interactive workshop funded by the National Centers of Academic Excellence in Cybersecurity grant. Topics include defining professionalism, key skills for building professionalism, and understanding ethics in the w
0 views • 16 slides
Professionalism in Cybersecurity: Developing Essential Skills
Explore the importance of professionalism in cybersecurity, focusing on responsibility, integrity, and effective communication. Learn how to enhance your skills through practice and continual development, preparing for the competitive job market in cybersecurity. Discover the significance of conduct
0 views • 17 slides
Cybersecurity Workforce Management: Engage, Empower, Elevate
Explore the intricacies of Cybersecurity Workforce Management through engaging, empowering, and elevating your team. Discover the goals, challenges, and executive orders driving the cybersecurity workforce landscape, along with strategies to enhance workforce capabilities. Unveil the essence of pers
0 views • 27 slides
Cybersecurity and Computer Science Education Projects at UH Maui College
UH Maui College, supported by NSF, conducts various cybersecurity and computer science education initiatives led by Debasish Bhattacharya. The projects aim to enhance cybersecurity education, curriculum development, and workforce training, catering to a diverse student population. The college has re
0 views • 16 slides
Shovel-Ready Projects Initiative for Cybersecurity Innovation in Canada
This proposal outlines the launch of the Shovel-Ready Projects Initiative aimed at advancing cybersecurity innovation and talent development in Canada. The program, led by the National Cybersecurity Centre (NCC), seeks to fund eligible projects that enhance cybersecurity capabilities through researc
0 views • 19 slides
Automated Signature Extraction for High Volume Attacks in Cybersecurity
This research delves into automated signature extraction for high-volume attacks in cybersecurity, specifically focusing on defending against Distributed Denial of Service (DDoS) attacks. The study discusses the challenges posed by sophisticated attackers using botnets and zero-day attacks, emphasiz
0 views • 37 slides
Enhancing Cybersecurity for Improved Insurability and Risk Management
In this resource, cybersecurity experts provide insights on improving cybersecurity insurability and minimizing rates. The content covers topics such as the cyber risk landscape, cyber insurance landscape, ransom payments, and ways to enhance cybersecurity measures. Key points include assessing info
1 views • 21 slides
Enhancing NASA's Cybersecurity for Mission Assurance
NASA's IV&V Program Safety and Mission Assurance Office prioritizes cybersecurity to protect mission assets. The evolving threat landscape necessitates a robust security posture, focusing on network security, software vulnerabilities, and secure development practices. Measures include leveraging sec
0 views • 15 slides
Ethics in Cybersecurity: Evolution, Challenges, and Solutions
Explore the evolution of cybersecurity, from the days of firewalls to modern cybersecurity threats like viruses and ransomware. Understand the importance of ethics in cybersecurity, as it plays a vital role in building strong defense mechanisms to secure personal and enterprise data effectively.
0 views • 18 slides
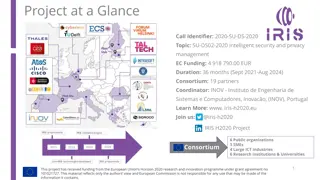
IRIS H2020 Project - Enhancing Cybersecurity for SMART CITIES
The IRIS H2020 project is dedicated to enhancing cybersecurity for SMART CITIES by developing a framework that supports European CERT and CSIRT networks in detecting, sharing, and responding to cybersecurity threats in IoT and AI-driven ICT systems. The project aims to minimize the impact of cyberse
0 views • 5 slides
Defense Industrial Base (DIB) Cybersecurity Training Overview
This training module focuses on the importance of cybersecurity in the Defense Industrial Base (DIB) sector, particularly highlighting the Cybersecurity Maturity Model Certification (CMMC) and its implications for organizations seeking certification. The content includes insights on incident reporti
0 views • 10 slides
Defense Industrial Base Sector Cybersecurity Training Overview
This training session focuses on educating Defense Industrial Base (DIB) suppliers about the requirements of the Cybersecurity Maturity Model Certification (CMMC). It covers topics such as the importance of cybersecurity, assessment processes, incident reporting, best practices, risk management, and
0 views • 22 slides
Cybersecurity Strategy in Japan - Roles of NISC and Basic Act Overview
The National Center of Incident Readiness and Strategy for Cybersecurity (NISC) plays a crucial role in Japan's cybersecurity landscape, integrating policies and handling cyber attacks 24/7. The Basic Act on Cybersecurity, enforced since January 2015, establishes a clear legislative framework and or
0 views • 12 slides
Understanding CYBEX - Cybersecurity Information Exchange Techniques
CYBEX introduces a new cybersecurity paradigm focusing on identifying weaknesses, minimizing vulnerabilities, and sharing attack heuristics within trusted communities. It emphasizes the importance of information exchange, policy, and identity assurance in combating cyber threats. The model aims to s
0 views • 14 slides
Interacting Safely in a Digital Setting: Cybersecurity Tips and Tricks
In our increasingly interconnected world, ensuring cybersecurity is crucial to safeguard sensitive information from potential threats. This module covers essential cybersecurity practices, such as using VPNs and antimalware, maintaining privacy online, and understanding netiquette. Learn how to enha
0 views • 15 slides