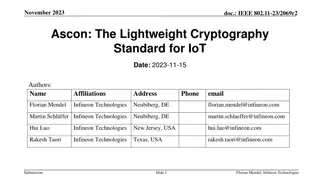
Ascon: The Lightweight Cryptography Standard for IoT
The November 2023 document IEEE 802.11-23/2069r2 discusses the importance of secure data storage and communication in IoT devices due to the increasing number of connected devices and potential security threats. It introduces Ascon as a lightweight cryptography standard selected by NIST for protecti
0 views • 26 slides
Lightweight Cryptography Standard for IoT - November 2023 IEEE Presentation
IEEE 802.11-23/2069r1 presents Ascon as a lightweight cryptography standard for IoT devices. With the increasing number of connected devices, protecting data on IoT devices becomes crucial. NIST selects Ascon to safeguard small devices, offering authenticated encryption and hashing efficiently. Asco
3 views • 26 slides
Sustainable Seo Services Seattle Long-Term Strategies for Consistent Growth
We are a Seattle-based SEO agency passionate about empowering local businesses to achieve long-term success through sustainable SEO practices. We don't just focus on short-term gains; we develop data-driven strategies that deliver consistent growth and organic traffic over time.
2 views • 15 slides
Sustainable Seo Services Seattle Long-Term Strategies for Consistent Growth
We are a Seattle-based SEO agency passionate about empowering local businesses to achieve long-term success through sustainable SEO practices. We don't just focus on short-term gains; we develop data-driven strategies that deliver consistent growth and organic traffic over time.
4 views • 15 slides
Understanding SHA-256 Algorithm and History
SHA-256 is a secure hashing algorithm that produces 256-bit hash values and is more secure than MD5, SHA-0, and SHA-1 due to fewer collisions. Created in 2001 by the NSA, it is widely used in various applications like cryptocurrency, SSL certificates, and blockchain. This summary provides insights i
0 views • 17 slides
Understanding Patient Health Record Linkage Methods
Explore the methods and processes involved in linking patient health records to ensure data accuracy and integrity. Learn about objectives, data de-duplication, encryption, data normalization, and linkage variables. Discover CU Record Linkage (CURL) data flow and key quality measures. Dive into data
2 views • 21 slides
Understanding Motion Under Constant Acceleration
Constant acceleration refers to motion where the speed increases by the same amount each second. It is exemplified in scenarios like free fall due to gravity, where objects experience a consistent acceleration of approximately 10 meters per second squared. This type of motion plays a significant rol
0 views • 11 slides
Secure Keyed Hashing on Programmable Switches
Explore the implementation challenges and opportunities for improved security, privacy, performance, and reliability in data plane applications using (Half)SipHash and CRC32 hashing techniques. Discover the vulnerabilities associated with CRC32 and the need for secure hashing solutions like SipID. L
0 views • 17 slides
Overview of Cryptography Techniques and Algorithms
Exploring the diverse realm of cryptography, this chapter delves into both nonmathematical and mathematical encryption methods. It covers substitution and transposition ciphers, steganography, hybrid systems, hashing, symmetric algorithms like DES and AES, as well as asymmetric algorithms utilizing
7 views • 21 slides
Sorbitan Monostearate: A Vital Element for Producing Stable and Consistent Food
Sorbitan Monostearate is a vital element in producing stable and consistent food products. As a key emulsifier, Sorbitan Monostearate ensures that oil and water blend seamlessly, preventing separation and maintaining uniformity. This ingredient plays
0 views • 4 slides
The Power of Consistent Prayer: Lessons from Colossians 1:9-14
Discover the powerful message behind Paul's prayer for the church in Colossae in Colossians 1:9-14. Explore the importance of consistent prayer, seeking God's will, producing obedience and fruitfulness, and embracing thankfulness for redemption and forgiveness. Learn valuable lessons for today on pr
0 views • 7 slides
Exploring Caching Techniques in Web Systems
Dive into the world of web caching with concepts like consistent hashing, Bloom filters, and shared caches for enhanced performance and efficiency. Discover the challenges faced in managing large-scale caches and learn about innovative solutions and ideas in the field of web systems.
0 views • 21 slides
Understanding Scrypt: Maximally Memory-Hard Functions
Scrypt is a memory-hard function designed for password hashing and key derivation, aiming to thwart brute-force attacks by making evaluation moderately hard. It emphasizes the need for memory intensity over computation, hindering the advantages of special-purpose hardware, parallelism, and amortizat
0 views • 59 slides
Entity Resolution Problem in Customer Data Matching
The challenge of entity resolution, especially in the context of matching customer data between companies, is addressed in this content. The scenario involves accurately identifying which records correspond to the same individuals despite potential variations or errors in the data. Strategies such a
1 views • 56 slides
Comprehensive Overview of Binary Heaps, Heapsort, and Hashing
In this detailed review, you will gain a thorough understanding of binary heaps, including insertion and removal operations, heap utility functions, heapsort, and the efficient Horner's Rule for polynomial evaluation. The content also covers the representation of binary heaps, building initial heaps
0 views • 24 slides
CSE 373 - Hashing Concepts and Exam Preparation
Introduction to hashing in CSE 373, covering basic concepts, hash functions, collision resolution, and runtimes. Exam details for Friday's practice exam include topics on Stacks, Queues, BigO Notation, Heaps, Trees, Design Tradeoffs, and exam format with emphasis on theoretical understanding. Lectur
0 views • 38 slides
Quality Control in Manufacturing Operations
Quality Control (QC) is an essential aspect of manufacturing operations to ensure products meet required quality standards. It involves inspection, analysis, and action to maintain consistent quality levels. Key elements include defining QC, process control, roles of QC personnel, common mispercepti
0 views • 27 slides
Understanding Locality Sensitive Hashing (LSH) for Nearest Neighbor Queries
Locality Sensitive Hashing (LSH) is a technique used to efficiently find nearest neighbors in high-dimensional spaces. By grouping similar points into the same hash bucket, LSH enables fast search for nearest neighbors, overcoming the curse of dimensionality. Variants include k-nearest neighbors and
0 views • 41 slides
Implementing Consistent and Predictable Consequences in Behavior Management
Explore strategies such as reinforcement, punishment, proactive techniques like priming and pre-correction, and the use of consistent consequences to manage behaviors effectively in educational settings. Understand how to proactively encourage desired behaviors, address infractions, and pre-correct
0 views • 44 slides
Dynamo: Amazon's Highly Available Key-value Store Summary
Dynamo is a distributed storage system designed by Amazon to provide scale, simplicity, key-value storage, and high availability. It aims to meet Service Level Agreements (SLAs) by offering simple query models, ACID properties, and efficient latency handling. The system sacrifices strong consistency
0 views • 19 slides
Scaling Services and Key-Value Storage Techniques
This content delves into various aspects of scaling services, including partitioning, hashing, and key-value storage. It discusses vertical and horizontal scalability, the chaotic nature of horizontal scaling, techniques for partitioning data, and case studies like Amazon Dynamo. The importance of p
0 views • 48 slides
Understanding Consistent Hashing and Distributed Hash Table
Explore the concept of consistent hashing and distributed hash tables to efficiently store and retrieve web pages across multiple servers. Learn how hashing functions and algorithms can distribute data evenly, handle server additions smoothly, and minimize object relocations. Discover the benefits o
1 views • 36 slides
Overview of SwissBox Project at ETH Zurich
SwissBox project at ETH Zurich, led by G. Alonso, D. Kossmann, and T. Roscoe, focuses on building a high-performance system called SwissBox. It encompasses hardware components like CPUs, memory, FPGAs, and storage, aiming to create a versatile computing platform. The project explores shared i-disk a
0 views • 18 slides
Overlay Networks and Consistent Hashing in Distributed Systems
Understanding the concept of overlay networks and consistent hashing in distributed systems is crucial for scalability and efficient data storage. Overlay networks like P2P DHT via KBR offer a decentralized approach for managing data while consistent hashing provides a balanced and deterministic way
0 views • 36 slides
Adapting Linear Hashing for Flash Memory Constrained Embedded Devices
This research explores the adaptation of linear hashing for improved data handling on flash memory-constrained embedded devices. Motivated by the increasing data collection by IoT devices, the study focuses on implementing database structures like a linear hash table for efficient data processing. T
0 views • 67 slides
Understanding Hash Functions in Data Structures
Hash functions are crucial in storing data efficiently by converting a sized amount of data into a single integer. They are used to generate hash values, hash codes, or hash sums, which serve as indexes in arrays. The hash function should be quick to compute and distribute hash addresses uniformly t
0 views • 200 slides
Enhancing MemC3: Compact and Concurrent MemCache for Improved Performance
MemC3 introduces a novel approach to compact and concurrent caching through dumber caching and smarter hashing techniques, addressing key issues faced by traditional memory caching systems. By implementing CLOCK-based LRU, approximate LRU, and utilizing Cuckoo Hashing, MemC3 achieves significant imp
0 views • 20 slides
Enhancing Key-Value Storage with MemC3 and Cuckoo Hashing
MemC3 is a specialized key-value store that combines CLOCK and Concurrent Cuckoo Hashing to improve performance and efficiency. Memcached, an established DRAM-based key-value store, is also discussed along with its LRU eviction strategy. The use of internal chaining hashtable and LRU caching in Memc
1 views • 23 slides
Creating Consistent and Interactive Presentations
Utilize a structured approach for creating interactive presentations with consistent layouts. Design title slides distinctively and incorporate menus efficiently. Enhance user navigation by linking transparent shapes to relevant slides and indicate slide positions within the menu. Optimize the Slide
0 views • 6 slides
Understanding Database Index Hashing Techniques
Hashing-based indexing in database systems is efficient for equality selections but not suitable for range searches. Both static and dynamic hashing methods exist, with static hashing involving fixed primary pages that are allocated sequentially. The process involves determining the bucket to which
0 views • 41 slides
Understanding Data Structures and Hashing in Java
Data structures play a crucial role in organizing, iterating, adding, deleting, and searching data efficiently. Hash tables, linked lists, trees, and more are explored in this overview, highlighting their strengths and trade-offs. Hashing, collision resolution strategies, and the importance of a wel
0 views • 19 slides
Dynamo and Bayou: High Availability and Weak Consistency in Modern Applications
Dynamo and Bayou databases offer high availability and weak consistency, making them suitable for modern applications with super high demands. Examples of suitable applications include flight ticket booking, Amazon shopping carts, and more. Availability is crucial for accommodating millions of custo
0 views • 38 slides
Amazon's Dynamo: Highly Available Key-Value Store Overview
Amazon Dynamo is a highly available key-value store emphasizing reliability and scalability. It uses a write-always approach and consistent hashing for workload distribution. System requirements include query model for reading and updating data items, ACID properties, and stringent latency requireme
0 views • 40 slides
Understanding Hashing: Efficient Data Storage and Retrieval
Hashing is a powerful technique for achieving constant time complexity in finding and inserting data. It allows for quick access without the need for ordered elements. Direct addressing, limited hash operations, and efficient storage methods are discussed in this content to optimize data retrieval s
0 views • 100 slides
Effective Strategies for Team Communication and Attendance Management in Sports
Effective communication, clear expectations, and consistent enforcement of team rules are vital for success in sports. This presentation discusses the importance of attendance expectations, communication strategies, trust-building, team handbook implementation, and enforcing rules for all athletes.
0 views • 14 slides
Understanding Sketching and Locality Sensitive Hashing in Data Mining
Explore the concepts of Jaccard Similarity and Cosine Similarity in data mining, along with their applications in recommendation systems and finding near-duplicates. Discover how Sketching and Locality Sensitive Hashing techniques help in efficiently identifying similar items and solving the Nearest
0 views • 63 slides
Dichotomy on Complexity of Consistent Query Answering
The research paper presents a dichotomy on the complexity of consistent query answering for atoms with simple keys. It discusses repairs for uncertain instances in a schema with key constraints, as well as the concept of consistent query answering. The document addresses the problem statement of cer
0 views • 26 slides
Understanding Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
0 views • 40 slides
Understanding Network Security Principles and Techniques
Explore the fundamental concepts of network security, including issues of confidentiality, integrity, and non-repudiability. Learn about the challenges of securing networks and the types of attacks that computer systems face. Dive into basic security techniques like hashing and symmetric key cryptog
0 views • 36 slides
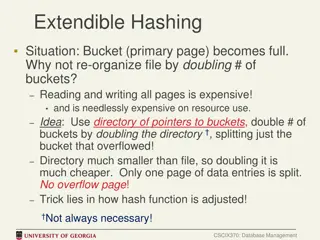
Efficient Bucket Management in Extendible Hashing
In cases where a bucket (primary page) becomes full in extendible hashing, re-organizing the file by doubling the number of buckets can be costly in terms of resource utilization. An alternative approach involves using a directory of pointers to buckets and doubling the directory instead of all buck
0 views • 9 slides