Algorithm Analysis
Algorithm analysis involves evaluating the efficiency of algorithms through measures such as time and memory complexity. This analysis helps in comparing different algorithms, understanding how time scales with input size, and predicting performance as input size approaches infinity. Scaling analysi
1 views • 30 slides
Understanding Neural Networks: Models and Approaches in AI
Neural networks play a crucial role in AI with rule-based and machine learning approaches. Rule-based learning involves feeding data and rules to the model for predictions, while machine learning allows the machine to design algorithms based on input data and answers. Common AI models include Regres
9 views • 17 slides
Are Server Rentals Essential for Implementing Clustering?
Discover why renting servers is important for clustering with VRS Technologies LLC's helpful PDF. Learn how to make your IT setup better. For Server Rental Dubai solutions, Contact us at 0555182748.
13 views • 2 slides
Understanding Booth's Algorithm for Binary Integer Division
Learn about Booth's Algorithm and how it facilitates binary integer division. Discover key points to remember when using the algorithm, steps to initiate the process, and a detailed example to illustrate the multiplication of two operands using Booth's Algorithm.
0 views • 42 slides
Understanding Clustering Algorithms: K-means and Hierarchical Clustering
Explore the concepts of clustering and retrieval in machine learning, focusing on K-means and Hierarchical Clustering algorithms. Learn how clustering assigns labels to data points based on similarities, facilitates data organization without labels, and enables trend discovery and predictions throug
0 views • 48 slides
Understanding Stable Matchings and the Gale-Shapley Algorithm
The concept of stable matchings is explored, along with the Gale-Shapley algorithm for finding them efficiently. Key ideas and steps of the algorithm are explained, supported by visuals. The process, examples, and observations related to the algorithm's effectiveness are discussed, highlighting the
1 views • 29 slides
Ricart and Agrawala's Algorithm for Mutual Exclusion
The Ricart-Agrawala Algorithm is a distributed system algorithm for achieving mutual exclusion without the need for release messages, developed by Glenn Ricart and Ashok Agrawala. The algorithm involves processes sending timestamped requests to enter a critical section, with careful handling of repl
1 views • 16 slides
Understanding Algorithm Efficiency Analysis
In this chapter, Dr. Maram Bani Younes delves into the analysis of algorithm efficiency, focusing on aspects such as order of growth, best case scenarios, and empirical analysis of time efficiency. The dimensions of generality, simplicity, time efficiency, and space efficiency are explored, with a d
1 views • 28 slides
Understanding Lamport Algorithm for Mutual Exclusion
Lamport Algorithm, presented by Prafulla Santosh Patil, is a permission-based algorithm utilizing timestamps to order critical section requests and resolve conflicts. It employs three types of messages: REQUEST, REPLY, and RELEASE, where each site manages a queue to store requests. By ensuring commu
0 views • 15 slides
Digital Differential Analyzer (DDA) Algorithm in Computer Graphics
In computer graphics, the Digital Differential Analyzer (DDA) Algorithm is utilized as the basic line drawing algorithm. This method involves interpolation of variables between two endpoints to rasterize lines, triangles, and polygons efficiently. The algorithm requires inputting coordinates of two
0 views • 9 slides
Text Analytics and Machine Learning System Overview
The course covers a range of topics including clustering, text summarization, named entity recognition, sentiment analysis, and recommender systems. The system architecture involves Kibana logs, user recommendations, storage, preprocessing, and various modules for processing text data. The clusterin
0 views • 54 slides
Grey Wolf Optimizer: A Nature-Inspired Optimization Algorithm
The Grey Wolf Optimizer algorithm is based on the social hierarchy of grey wolves in the wild. Inspired by the pack behavior of grey wolves, this algorithm utilizes alpha, beta, and delta solutions to guide the optimization process. The hunting phases of tracking, pursuing, and attacking prey mimic
3 views • 16 slides
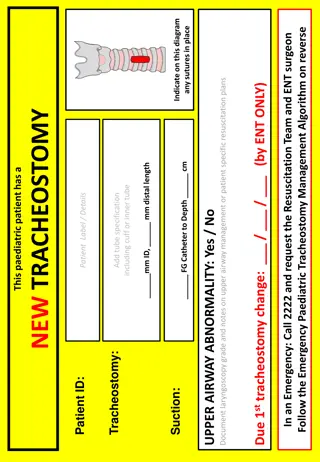
Emergency Paediatric Tracheostomy Management Algorithm
Emergency Paediatric Tracheostomy Management Algorithm provides a structured approach for managing pediatric patients requiring tracheostomy in emergency situations. The algorithm outlines steps for assessing airway patency, performing suction, and changing the tracheostomy tube if necessary. It emp
0 views • 4 slides
DNA Data Archival: Solving Read Consensus Using OneJoin Algorithm
DNA data storage presents challenges in archiving digital information efficiently due to the nature of biological media. This article delves into the complexities of DNA data storage, emphasizing the importance of robust archival solutions. The OneJoin algorithm offers a scalable and cross-architect
0 views • 8 slides
Development of Satellite Passive Microwave Snowfall Detection Algorithm
This study focuses on the development of a satellite passive microwave snowfall detection algorithm, highlighting the challenges in accurately determining snowfall using satellite instruments. The algorithm uses data from AMSU/MHS, ATMS, and SSMIS sensors to generate snowfall rate estimates, overcom
0 views • 20 slides
Understanding Euclid's Algorithm: An Ancient Approach to Finding Greatest Common Divisors
Euclid's Algorithm, dating back 2500 years, offers a simpler method to find the greatest common divisor (gcd) of two non-negative integers compared to traditional factorization. By iteratively applying a rule based on the gcd of remainders, it efficiently computes gcd values. The basis of the algori
0 views • 15 slides
Efficient Parameter-free Clustering Using First Neighbor Relations
Clustering is a fundamental pre-Deep Learning Machine Learning method for grouping similar data points. This paper introduces an innovative parameter-free clustering algorithm that eliminates the need for human-assigned parameters, such as the target number of clusters (K). By leveraging first neigh
0 views • 22 slides
GPU Accelerated Algorithm for 3D Delaunay Triangulation
Thanh-Tung Cao, Todd Mingcen Gao, Tiow-Seng Tan, and Ashwin Nanjappa from the National University of Singapore's Bioinformatics Institute present a GPU-accelerated algorithm for 3D Delaunay triangulation. Their work explores the background, related works, algorithm implementation, and results of thi
0 views • 24 slides
Cuckoo Search: A Nature-Inspired Optimization Algorithm
Cuckoo Search (CS) algorithm, developed in 2009, mimics the brood parasitism of cuckoo species and utilizes Lévy flights for efficient optimization. This algorithm has shown promise in outperforming other traditional methods like PSO and genetic algorithms. The behavior of cuckoos in laying eggs an
0 views • 25 slides
Ford-Fulkerson Algorithm for Maximum Flow in Networks
The Ford-Fulkerson algorithm is used to find the maximum flow in a network by iteratively pushing flow along paths and updating residual capacities until no more augmenting paths are found. This algorithm is crucial for solving flow network problems, such as finding min-cuts and max-flow. By modelin
0 views • 26 slides
Understanding Transitivity and Clustering Coefficient in Social Networks
Transitivity in math relations signifies a chain of connectedness where the friend of a friend might likely be one's friend, particularly in social network analysis. The clustering coefficient measures the likelihood of interconnected nodes and their relationships in a network, highlighting the stru
0 views • 8 slides
3GPP Voting Rights Algorithm: Contiguous-3 Solution Evaluation
This evaluation delves into the advantages and disadvantages of the 3 Contiguous-3 solution within the 3GPP voting rights algorithm. It explores scenarios to test the algorithm's effectiveness in granting and revoking voting rights based on meeting attendance types. The evaluation includes diverse h
0 views • 10 slides
Introduction to Algorithm Analysis and Complexity in Computer Science
Algorithm analysis is crucial in determining the efficiency of programs by analyzing resource usage such as time and space. This involves comparing programs, understanding data structures, and evaluating algorithm performance. Efficiency is key as program execution time depends on various factors be
0 views • 66 slides
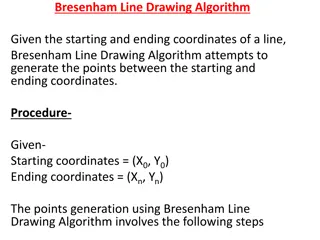
Bresenham Line Drawing Algorithm Explained with Examples
Bresenham Line Drawing Algorithm is a method used to generate points between starting and ending coordinates to draw lines efficiently. This algorithm involves calculating parameters, decision parameters, and iteratively finding points along the line. Two example problems are provided with step-by-s
0 views • 8 slides
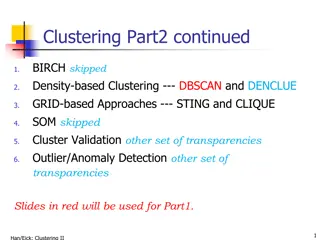
Density-Based Clustering Methods Overview
Density-based clustering methods focus on clustering based on density criteria to discover clusters of arbitrary shape while handling noise efficiently. Major features include the ability to work with one scan, require density estimation parameters, and handle clusters of any shape. Notable studies
0 views • 35 slides
Algorithm Strategies: Greedy Algorithms and the Coin-changing Problem
This topic delves into general algorithm strategies, focusing on the concept of greedy algorithms where locally optimal choices are made with the hope of finding a globally optimal solution. The discussion includes the nature of greedy algorithms, examples such as Dijkstra's algorithm and Prim's alg
0 views • 91 slides
Stable Matching Problem and Gale-Shapley Algorithm Overview
The content provides information on the stable matching problem and the Gale-Shapley algorithm. It covers the definition of stable matching, the workings of the Gale-Shapley algorithm, tips for algorithm implementation, and common questions related to the topic. The content also includes a summary o
0 views • 16 slides
Understanding Clustering Methods for Data Analysis
Clustering methods play a crucial role in data analysis by grouping data points based on similarities. The quality of clustering results depends on similarity measures, implementation, and the method's ability to uncover patterns. Distance functions, cluster quality evaluation, and different approac
0 views • 8 slides
Understanding Text Vectorization and Clustering in Machine Learning
Explore the process of representing text as numerical vectors using approaches like Bag of Words and Latent Semantic Analysis for quantifying text similarity. Dive into clustering methods like k-means clustering and stream clustering to group data points based on similarity patterns. Learn about app
0 views • 25 slides
Achieving Demographic Fairness in Clustering: Balancing Impact and Equality
This content discusses the importance of demographic fairness and balance in clustering algorithms, drawing inspiration from legal cases like Griggs vs. Duke Power Co. The focus is on mitigating disparate impact and ensuring proportional representation of protected groups in clustering processes. Th
0 views • 36 slides
Progress in Jet Clustering Algorithm Study with Durham Method
Application of Durham algorithm to event samples at Asian Physics & Software Meeting showed potential with slight improvement in significance. Future focus on paper writing and algorithm version upgrading.
0 views • 6 slides
Understanding Clustering Algorithms in Data Science
This content discusses clustering algorithms such as K-Means, K-Medoids, and Hierarchical Clustering. It explains the concepts, methods, and applications of partitioning and clustering objects in a dataset for data analysis. The text covers techniques like PAM (Partitioning Around Medoids) and AGNES
0 views • 74 slides
Understanding Major Terms, Cluster Labels, and Themes in IN-SPIRE Training
Major terms in IN-SPIRE are keywords used for clustering documents, while cluster labels in Galaxy view represent the most important terms associated with a point. Themes, calculated by clustering keywords, provide a higher-level description of data. PNNL techniques like RAKE and CAST help extract a
0 views • 4 slides
Understanding Deutsch's Algorithm in Quantum Computing
Deutsch's Algorithm is a fundamental quantum algorithm designed to solve the problem of determining if a given function is constant or balanced. This algorithm leverages quantum principles such as superposition and entanglement to provide a more efficient solution compared to classical methods. By e
0 views • 17 slides
Understanding Corporate Climate Assessment Using NLP Clustering
This work explores a novel approach in corporate climate assessment through applied NLP clustering, highlighting the relationship between climate risk and financial implications. The use of advanced techniques like BERT embedding for topic representation and clustering in corporate reports is discus
0 views • 33 slides
Algorithm for Determining Endpoints in Speech Recognition
This article discusses an algorithm proposed by L.R. Rabiner and M.R. Sambur in 1975 for determining endpoints in isolated utterances. The algorithm focuses on detecting word boundaries in speech through the recognition of silence, which can lead to reduced processing load and increased convenience,
0 views • 22 slides
Correlation Clustering: Near-Optimal LP Rounding and Approximation Algorithms
Explore correlation clustering, a powerful clustering method using qualitative similarities. Learn about LP rounding techniques, approximation algorithms, NP-hardness, and practical applications like document deduplication. Discover insights from leading researchers and tutorials on theory and pract
0 views • 27 slides
Exploring Avatar Path Clustering in Networked Virtual Environments
Explore the concept of Avatar Path Clustering in Networked Virtual Environments where users with similar behaviors lead to comparable avatar paths. This study aims to group similar paths and identify representative paths, essential in analyzing user interactions in virtual worlds. Discover related w
0 views • 31 slides
Time-space Tradeoffs and Optimizations in BKW Algorithm
Time-space tradeoffs and optimizations play a crucial role in the BKW algorithm, particularly in scenarios like learning parity with noise (LPN) and BKW algorithm iterations. The non-heuristic approach in addressing these tradeoffs is discussed in relation to the hardness of the LPN problem and the
0 views • 14 slides
Cluster Analysis: Grouping Elements into Clusters with Similarity Measures
Given a set of elements and a similarity measure, the algorithm aims to group elements into clusters where similar elements are grouped together. Each element is represented as a point in space, and the true number of clusters is unknown. The clustering algorithm is inspired by the behavior of ants
0 views • 15 slides