Rational Expectations and the Efficient Market Hypothesis
The importance of expectations in various sectors and markets of the economy, including asset demand, risk and term structure of interest rates, asymmetric information and financial structure, financial innovation, bank management, money supply process, Federal Reserve, foreign exchange market, dema
7 views • 51 slides
Public key encryption, Digital signature and authentication
Understand the concept of public key encryption, asymmetric encryption, and the widely used RSA algorithm. Explore how public key cryptography revolutionized the field of encryption and its applications in confidentiality, authentication, and key distribution.
6 views • 12 slides
Security Threats and Public-Key Cryptosystems
Explore the world of security threats, passive and active attacks, and the importance of asymmetric encryption through the terminology related to asymmetric encryption, public-key cryptosystems, and public-key cryptography. Learn about the key components of public-key encryption schemes and the proc
2 views • 46 slides
Key Management and Distribution Techniques in Cryptography
In the realm of cryptography, effective key management and distribution are crucial for secure data exchange. This involves methods such as symmetric key distribution using symmetric or asymmetric encryption, as well as the distribution of public keys. The process typically includes establishing uni
3 views • 27 slides
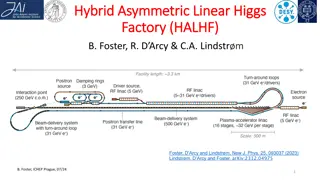
Innovative Hybrid Asymmetric Linear Higgs Factory (HALHF) Proposal
Cutting-edge proposal for the HALHF facility aiming to revolutionize particle acceleration technology by utilizing a hybrid asymmetric approach for electron-positron colliders. The design focuses on cost-efficiency and performance optimization, showcasing potential for significant advancements in hi
0 views • 18 slides
Overview of Cryptography Techniques and Algorithms
Exploring the diverse realm of cryptography, this chapter delves into both nonmathematical and mathematical encryption methods. It covers substitution and transposition ciphers, steganography, hybrid systems, hashing, symmetric algorithms like DES and AES, as well as asymmetric algorithms utilizing
7 views • 21 slides
Software Engineering Design Principles and Concepts
The chapter discusses the essential principles and concepts in software design, highlighting the four key design models - data design, architectural design, interface design, and component-level design. It emphasizes the importance of traceability to the analysis model, minimizing the gap between so
2 views • 36 slides
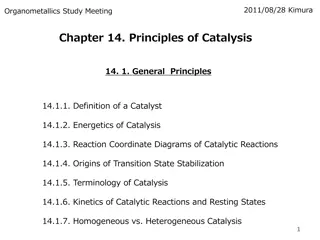
Fundamentals of Asymmetric Catalysis: Energetics and Principles
Exploring the principles and energetics of asymmetric catalysis, this study delves into the importance, classes of transformations, stereoselectivity, and transmission of asymmetry. It discusses reaction coordination diagrams, transition state stabilization, and the terminology of catalysis. The Cur
3 views • 20 slides
Overview of Basic Security Properties and Cryptography Fundamentals
This content provides an introduction to basic security properties such as confidentiality, authenticity, integrity, availability, non-repudiation, and access control. It also covers the fundamentals of cryptography, including symmetric and asymmetric encryption, public-key cryptography, and the imp
3 views • 41 slides
Cryptography Concepts and Encryption Methods Overview
Exploring elementary cryptography concepts such as encryption, cryptanalysis, symmetric and asymmetric encryption algorithms like DES, AES, and RSA. Delve into key exchange protocols, digital signatures, cryptographic hash functions, and the process of encryption and decryption in a cryptosystem.
0 views • 23 slides
Key Distribution and Management in Cryptography
This presentation discusses key distribution and management in cryptography, covering symmetric and asymmetric key cryptography, methods for sharing symmetric and public keys, as well as key distribution techniques such as manual delivery, initial key distributions, and the use of trusted third part
0 views • 30 slides
The Physics of Supernovae and Neutron Stars
Explore the fascinating world of supernovae and neutron stars through historical postulations, Nobel Prize-worthy discoveries, multi-dimensional simulations, and paradigm shifts in understanding asymmetric supernovae. Dive into the complexities of core-collapse mechanisms, jet formations, and the po
1 views • 35 slides
Design Inspiration and Elements in Costume and Fashion Design
Dive into the world of costume and fashion design through a visual journey of finding design inspiration, understanding the design process, emphasizing originality, and exploring different sources of creativity. Discover how technology, art, food, history, architecture, and nature can spark innovati
0 views • 45 slides
Dynamic Core Boosting for Heterogeneous Computing
Exploring the challenges of workload heterogeneity in parallel programming, focusing on the impact of asymmetric hardware on performance and synchronization. Insights on modeling workload imbalance and boosting critical paths for efficient computation in heterogeneous multicores.
0 views • 22 slides
Material Design: Combining Classic Design Principles with Technological Innovation
Material Design is a design language that combines traditional design principles with the possibilities offered by technology and science. It emphasizes visual language, classic design elements, and innovation to create delightful user experiences. The Material Metaphor, Imagery, Typography, Color,
0 views • 34 slides
Comprehensive Guide to System Design Components and Techniques
System design involves the detailed planning and identification of components in an information system, aiming to provide users with a general understanding of the new system. This process includes techniques like flowcharts, prototyping, and component design, covering aspects such as output design,
1 views • 24 slides
Bank Loan Markups and Adverse Selection: Market Concentration Analysis
This research presentation by Beyhaghi, Fracassi, and Weitzner explores the impact of market concentration on bank loan markups and adverse selection. It delves into how asymmetric information across lenders influences interest rates in local banking markets, shedding light on the relationship betwe
0 views • 44 slides
Strong Asymmetric PAKE Protocols
Explore the intricacies of strong asymmetric PAKE (Password-Authenticated Key Exchange) protocols, including their security notions, possible attacks, and implementations. Learn about the challenges in constructing such protocols, the significance of universally composable security, and the limitati
0 views • 15 slides
Basic Concepts in Software Design
Software design involves transforming customer requirements into a form suitable for implementation, with activities categorized into preliminary and detailed design stages. High-level design focuses on module identification and control relationships, while detailed design entails defining data stru
1 views • 24 slides
Asymmetric Information and Externalities in Microeconomics
Explore the concepts of adverse selection, market inefficiency, signaling, and moral hazard arising from asymmetric information in microeconomics. Delve into scenarios like the Market for Lemons and health insurance to grasp how information deficiencies impact economic outcomes. Additionally, analyz
0 views • 22 slides
Insights into Persuasion and Equilibrium in Multidimensional Cheap Talk
Explore the dynamics of multidimensional cheap talk, focusing on sender-receiver interactions, influential equilibrium, welfare rankings, and fragility to asymmetries. Lessons touch on bubbling equilibrium, influential equilibrium issues, welfare rankings preferences, and the impact of asymmetric pr
1 views • 20 slides
AERO: Mobile Routing & Addressing System for IP Internetworks
AERO, Asymmetric Extended Route Optimization, is a mobile routing and addressing system designed for IP internetworks like aviation, enterprise, and campus networks. It enables stable IPv6 prefixes for mobile devices, treating them as routers to connect to the Internet of Things. AERO offers feature
0 views • 26 slides
Cryptographic Algorithms and Hash Collisions Overview
Explore the world of cryptographic algorithms and hash collisions. Learn about various hashing algorithms like MD5, SHA-1, SHA-256, and more. Dive into the concepts of symmetric and asymmetric key algorithms and understand the risks associated with hash collisions. Discover the implications of post-
1 views • 58 slides
Proposed Changes to School Week: Asymmetric Week Implementation
Proposed changes to the school week involve introducing an Asymmetric Week structure, with 4.5 days per week. This adjustment aims to modernize and enhance the educational provision in schools, with potential benefits for student health, well-being, and curriculum flexibility. The proposal is based
0 views • 14 slides
Asymmetric Socialization and Resource Transfers in Welfare States
Exploring intergenerational resource transfers in the context of welfare states, this study examines three main channels: families, the government, and markets. It delves into different institutional arrangements governing asset-based reallocations, public transfers, and familial transfers. The leve
0 views • 12 slides
Fundamentals of Cryptography and Network Security
Explore the basics of cryptography, including classical encryption techniques, terminology definitions, types of encryption operations, cryptanalysis objectives and attacks, and the concept of cipher strength. Uncover the principles and methods behind encryption and decryption, key distinctions betw
1 views • 52 slides
Public-Key (Asymmetric) Ciphers
Principles and significance of public-key cryptography, including its motivation, trapdoor one-way functions, and the issues with symmetric-key ciphers. Learn about asymmetric ciphers, key distribution problems, and the use of prime numbers in encryption.
0 views • 31 slides
Digital Logic Design with Alex Bronstein
In this course, delve into digital logic design concepts with Alex Bronstein. Explore the fundamentals of designing logic systems and learn the intricacies of a simple CPU design. Gain insights into the world of digital systems and their applications. The course covers a range of topics from hardwar
0 views • 32 slides
Hybrid Asymmetric Linear Higgs Factory (HALHF) - Innovation in Particle Acceleration
HALHF is a groundbreaking facility aiming to revolutionize particle acceleration by utilizing asymmetric energy concepts to enhance efficiency and reduce costs. With a focus on electron-positron collider development, this facility opens up new avenues in plasma acceleration technology. The design, l
0 views • 21 slides
Hybrid Asymmetric Linear Higgs Factory: Innovating Particle Acceleration
Implementing a groundbreaking concept, the HALHF facility aims to revolutionize particle collider technology by utilizing asymmetric energy machines for enhanced efficiency and cost-effectiveness. The facility's layout and cost estimates are detailed, showcasing its potential to transform plasma acc
0 views • 12 slides
Visual Design Studies: Exploring Design Principles and Projects
Visual Design students delve into the Four Frames and design principles, exploring a variety of design forms through physical and digital mediums. Projects span Jewelry, Fashion, Interior Design, Animation, Ceramics, Game Design, Film Set, and Prop Design. The course offers practical and theoretical
1 views • 4 slides
Understanding Analysis and Design in Object-Oriented Software Development
Analysis and design are crucial stages in the object-oriented software development lifecycle. Analysis involves understanding the current system and defining requirements for the new system, while design focuses on creating solutions that meet these requirements. This process is essential for develo
0 views • 25 slides
Advanced Organic Synthesis Methods: Oxidation Reactions Overview
Explore the intricacies of oxidation reactions in organic synthesis, focusing on Sharpless Asymmetric Epoxidation and related mechanisms. Learn about the Nobel Prize-winning work of K. Barry Sharpless and the application of titanium isopropoxide catalysts. Dive into the enantioselectivity concepts a
0 views • 14 slides
Understanding Adverse Selection and Lemons Problem in Economics
Learn about adverse selection and the lemons problem in economics, which refer to situations where information imbalances between buyers and sellers lead to market inefficiencies. Discover how asymmetric information can impact various markets, such as used cars, labor, and insurance, and explore str
0 views • 23 slides
Product and Process R&D Under Asymmetric Demands Research Insights
Explore the dynamics of product and process research and development (R&D) in response to asymmetric demands in various market competitions, using examples such as HD DVD vs. Blu-ray and Coke vs. Pepsi. Discover the implications of demand asymmetry on R&D investments, guided by the barbell model, hi
0 views • 63 slides
Uncovering Asymmetric Attention in Intertemporal Decision Making
Explore the research on how asymmetric attention to opportunity costs influences intertemporal decision-making, with insights on hidden zero effects, consumer choices, and the impact of various conditions and methods on decision outcomes.
0 views • 41 slides
Understanding Machine Design and Types: Introduction, Definition, and More
Explore the fundamentals of machine design, including its definition, purpose, and different types such as Adaptive Design, Development Design, and New Design. Learn about the design methods like Rational Design, Empirical Design, and Industrial Design. Enhance your knowledge on the concepts and pri
1 views • 11 slides
Exploring Design Strategies for Public Sector Professionals
Delve into the world of design in the public sector with Dr. Angela Fernandez-Orviz. Discover insights on factors influencing the adoption of design strategies in projects, including organizational culture, prior experiences, and policy considerations. Explore various design approaches such as servi
0 views • 42 slides
Traditional Ciphers III: Symmetric and Asymmetric Cryptographic Algorithms
Learn about symmetric and asymmetric cryptographic algorithms, including their differences, strengths, and weaknesses. Explore common algorithms like DES, 3DES, and AES, and understand the importance of key distribution in secure communication.
0 views • 8 slides
Understanding Asymmetric Encryption: Diffie-Hellman Key Exchange Explained
Explore the world of asymmetric encryption through the captivating concept of the Diffie-Hellman key exchange protocol. Delve into the intricacies of public-key cryptography, secret key agreement, and the mathematical foundations that make this encryption method secure and reliable.
0 views • 29 slides