Impact of Fact-Checking on Credibility Among Older Adults
Analyzing the impact of fact-checking on news credibility among older adults reveals that age is a key factor in information credibility. Older adults tend to give more credibility to various kinds of information, leading to potential challenges in discerning between true facts and false news. Fact-
5 views • 31 slides
Exploring 'Checking Out Me History' - A Poem Analysis Quiz
Unravel the layers of "Checking Out Me History" through a 10-question quiz delving into themes of identity, historical figures, and the narrator's sentiments towards education and heritage. Discover the hidden messages and insights within this powerful poem.
0 views • 12 slides
Text Type Focus: Interviews
Interviews in English Language and Literature aim to entertain readers, fulfill their curiosity, and provide new insights on various topics. They typically follow a question-answer format and may present a mix of reported and direct speech. Interviews can cover a single topic or multiple subjects, w
1 views • 10 slides
Exploration of Gender and Sexuality in Tsitsi Dangarembga's "Nervous Conditions
Tsitsi Dangarembga's novel "Nervous Conditions" introduces a powerful narrative that focuses on the lives of young African girls and women in Zimbabwe during the postcolonial era. The novel challenges traditional gender roles and explores themes of sexuality, identity, and societal expectations. Thr
0 views • 11 slides
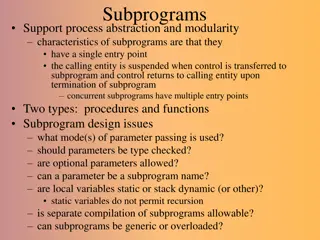
Overview of Subprograms in Software Development
Subprograms in software development provide a means for abstraction and modularity, with characteristics like single entry points, suspension of calling entities, and return of control upon termination. They encompass procedures and functions, raising design considerations such as parameter passing
4 views • 25 slides
Quality Improvement Cycle: Plan, Do, Check, Act (PDCA)
The Quality Improvement Cycle follows the PDCA framework, involving planning, implementing, checking, and acting to continuously enhance processes. It begins with defining customer requirements, implementing processes effectively, checking for issues, and taking action to resolve any problems. The c
1 views • 6 slides
Strategies for Difficult Conversations Workshop Overview
This workshop focuses on enhancing feedback skills and providing effective strategies for handling difficult situations and conversations in obstetrics and gynecology. It addresses the key premise that undermining behavior can be avoided through careful feedback, conflict management, and appropriate
0 views • 41 slides
Runtime Checking of Expressive Heap Assertions
Motivated by the unreliability of large software systems due to concurrency bugs and limitations of static analysis, the goal is to enable runtime analysis of deep semantic properties with low overhead. This involves checking expressive heap assertions at runtime with minimal impact on performance,
0 views • 15 slides
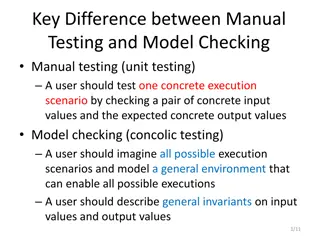
Difference Between Manual Testing and Model Checking
Manual testing focuses on testing specific scenarios with concrete inputs and outputs, while model checking involves imagining all possible scenarios to create a general environment for testing. In manual testing, users test specific execution scenarios, whereas in model checking, users envision and
2 views • 4 slides
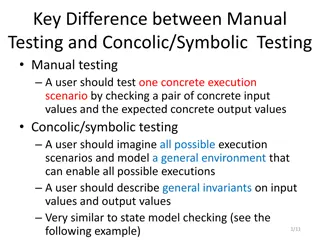
Difference Between Manual Testing and Concolic/Symbolic Testing in Software Development
Manual testing involves checking concrete input and output values for specific execution scenarios, while concolic/symbolic testing requires imagining all possible scenarios and modeling a general environment. General invariants on input and output values are described, similar to state model checki
0 views • 4 slides
Exploring 'The Story of an Hour' Setting in Kate Chopin's Work
In Kate Chopin's "The Story of an Hour," the setting plays a crucial role in depicting Mrs. Mallard's emotional journey upon hearing of her husband's death. The detailed description of the environment reflects her internal turmoil and eventual realization of newfound freedom and self-assertion.
0 views • 42 slides
Event Log Alignment for Conformance Checking
Approach based on ILP for aligning event logs and process models, ensuring multi-perspective conformance checking. Examples illustrate trace executions with and without problems, utilizing Petri Nets with data. Alignments between log and process traces are analyzed, showing the existence of multiple
0 views • 21 slides
Understanding SAML for Secure Single Sign-On
SAML (Security Assertion Markup Language) is an XML-based framework facilitating authentication and authorization data exchange between an identity provider (IdP) and a service provider (SP). It enables single sign-on (SSO) for many organizations and mobile web applications, offering secure authenti
0 views • 56 slides
The Evolution of U.S. Government: From Declaration of Independence to Constitution
The journey from the Declaration of Independence in 1776 to the Constitutional Convention in 1787 marked a crucial phase in American history. Beginning with the assertion of unalienable rights to the creation of a more effective and legitimate government through the Great Compromise, this period sha
0 views • 17 slides
Foundations of American Governance: From Our Political Beginnings to Independence
Explore the evolution of political systems in America, from the establishment of ordered and limited government to the assertion of individual rights through key historical documents such as the Magna Carta, Petition of Rights, and English Bill of Rights. Discover the formation of representative gov
0 views • 21 slides
Understanding Rhetorical Précis Writing
A rhetorical précis is a structured four-sentence paragraph that addresses the rhetorical situation of a discourse, capturing essential elements such as the author's name, title, publication date, major assertion, purpose, and audience relationship. The first sentence introduces the author and thes
0 views • 10 slides
Contrast and Development in "Men Should Weep" Act Three
Act Three of "Men Should Weep" by Ena Lamont Stewart portrays a contrast in atmosphere from the start of the act, characterized by a cheerier and more positive ambiance. It delves into complex family dynamics, plot strands, and character developments that culminate in a climactic resolution, offerin
0 views • 39 slides
Context-Aware Identification of Check-worthy Claims in Political Discussions
This work explores the intersection of man and machine in countering malicious communication in social networks, focusing on fact-checking in political discussions. The research investigates the need for technology to verify the accuracy of public figures' statements, considering the thriving field
0 views • 21 slides
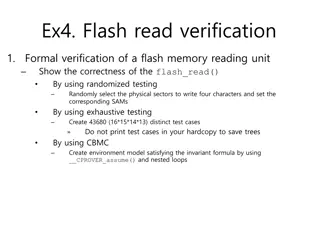
Formal Verification of Flash Memory Reading Unit
Perform formal verification of a flash memory reading unit by demonstrating correctness using randomized testing and exhaustive testing. Randomly select physical sectors to write characters and set corresponding Security Assertion Markup (SAM) structures. Create a total of 43,680 distinct test cases
0 views • 5 slides
Exploring Architecture and Challenges of Proof Assistants
Explore the architecture of proof assistants, discussing the use of tactics, formal proofs, and the difficulty in utilizing these tools. Discover the contribution of a new architecture for proof assistants, addressing extensibility and error checking, with a focus on soundness guarantees. Delve into
0 views • 41 slides
Handling Privilege and Discovery Issues in Corporate Litigation
Exploring privilege assertions and discovery rules in Illinois law for corporate litigation cases, emphasizing the burden of proof on privilege assertion, strong disfavor of privileges, and exceptions in certain circumstances. Understanding the importance of disclosure in legal proceedings and the n
0 views • 51 slides
Bounded Satisfiability Checking for Early Legal Compliance Verification
Early verification of legal compliance is crucial to avoid consequences such as violating regulations like GDPR. Through bounded satisfiability checking using Metric First-order Temporal Logic (MFOTL), this research focuses on system design verification for regulatory compliance. The study addresses
0 views • 29 slides
Assertion Collection in DICOM Working Group 07 Radiotherapy
The Assertion Collection IOD addresses the need to collect assertions outside DICOM Instances, providing contextual and identification information. It aims to collect assertions for DICOM Instances during clinical procedures, providing meta information about assertions and allowing for self-containe
0 views • 9 slides
Essential Guide to Opening and Managing a Checking Account
Learn the importance of opening a checking account, the process of choosing a bank, criteria to consider, and the steps to open an account. Understand the different services offered by banks and the key factors to keep in mind when selecting a financial institution. Discover the benefits and require
0 views • 39 slides
Understanding the Dynamics of Aggression and Assertion in Competitive Environments
Aggression is intentional behavior aimed at harming others, while assertion is forceful yet non-harmful conduct within the spirit of competition. Factors like antecedents, perceived unfairness, and pressure to win can trigger aggression in sports. Recognizing the differences between hostile and chan
0 views • 10 slides
Differential Assertion Checking and Relative Correctness in Software Verification
Differential assertion checking compares two similar programs to identify errors, while relative correctness ensures all assertions pass, highlighting failed assertions. The content discusses the challenges and benefits of these techniques in software verification, with examples of correct and buggy
0 views • 17 slides
Divide & Conquer Approach to Model Checking
Addressing the state space explosion issue in model checking, this work by Canh Minh Do, Yati Phyo, and Kazuhiro Ogata introduces a divide & conquer approach focusing on until and until stable properties. The research extends techniques to handle these properties effectively, emphasizing mitigation
2 views • 17 slides
Understanding the Decision-Making Process of Checking Behaviors Among Doctors and Patients
Recent research by Ido Erev from Technion and University of Warwick, along with Alvin E. Roth and others, explores the coexistence of insufficient and over-checking behaviors among individuals, including doctors and patients. The study delves into the factors influencing checking decisions, highligh
0 views • 24 slides
National Advocacy Service for People with Disabilities: Empowering Choices and Inclusion
The National Advocacy Service (NAS) for People with Disabilities in Ireland, established in 2011, aims to empower individuals with disabilities, ensuring they have equal opportunities and choices in life. With a statutory function to provide advocacy, NAS focuses on principles such as empowerment, i
1 views • 26 slides
Analyzing Characters through AECR Method in Literature Studies
The lesson involves analyzing characters through dialogue and incidents, supported by evidence and commentary using the AECR method. Students discuss vocabulary, choose impactful words, and present arguments such as whether Mary Maloney in "Lamb to the Slaughter" is sympathetic. The Assertion, Evide
0 views • 13 slides
Inferential Statistics Solutions for Challenging Problems in Section B
The provided statistical problems in Section B involve calculating the expected number of shoppers spending specific durations at a furniture shop and reasons for not checking the weight of each packet when filling corn flakes. Solutions include determining the shoppers expected to spend more than 4
0 views • 25 slides
Input Elimination Transformations for Scalable Verification and Trace Reconstruction
This work introduces new input elimination techniques for scalable model checking in industrial applications, focusing on trace reconstruction. The transformations aim to make the netlist more tractable for solving, involving various algorithms such as retiming, phase abstraction, and bitwidth reduc
0 views • 27 slides
Succinct Representation of Concurrent Trace Sets in Program Synthesis
This work focuses on representing concurrent trace sets efficiently in program synthesis. It addresses the problem setting of concurrent programs with specifications and provides solutions for avoiding assertion violations, including adding locks, barriers, and wait-notifies. The synthesis loop ensu
0 views • 25 slides
Conflict Checking Process in Heraldry: Armory 104 Overview
Delve into the intricacies of conflict checking using the ordinary in heraldry with Armory 104. Explore prerequisites, review key concepts, understand where SCA-registered armory is located, and learn the process of identifying and analyzing charge groups to ensure uniqueness in designs. Avoid commo
0 views • 28 slides
Competitiveness and Epistemics in Interaction: A Linguistic Analysis
This linguistic analysis delves into the phenomena of imperative forms, assertion, disagreement, and the distribution of responsibilities in interactions. It explores the context of competitiveness and epistemics, emphasizing the participants' rights in describing and knowing information. The study
0 views • 13 slides
AECR Writing Strategy for Effective Responses
AECR (Assertion, Evidence, Commentary, Restate) Writing Strategy is explained with examples and prompts, guiding readers on how to structure and develop coherent responses. The strategy emphasizes creating a strong assertion, supporting it with evidence from the text, providing commentary to explain
0 views • 8 slides
Enhancing Confidence and Assertiveness in Employability Skills
Understanding the concepts of confidence and assertiveness is crucial in developing employability skills. Assertiveness involves standing up for oneself while respecting others. Tips for gaining confidence include visualization, self-affirmation, facing fears daily, and challenging your inner critic
0 views • 7 slides
Subtyping and Type Checking in Programming Language Design
In the realm of programming language design, subtyping and type checking play crucial roles. This content delves into how syntax-directed rule systems evolve when dealing with subtyping, presenting the challenges and the solutions through a recursive algorithm approach. The discussion includes the t
0 views • 40 slides
Orthogonal Vectors Conjecture and Sparse Graph Properties Workshop
Exploring the computational complexity of low-polynomial-time problems, this workshop delves into the Orthogonal Vectors Problem and its conjectures. It introduces concepts like the Sparse OV Problem, first-order graph properties, and model checking in graphs. Discussing the hardness of problems rel
2 views • 22 slides
Streamlining Technical Processing for Library Services
In the technical processing workflow of a library, utilizing tools like copy cataloging macros can significantly improve efficiency and accuracy. This involves checking for copy cataloging status, running fix routines, and updating catalog records. While these macros offer benefits such as saving ti
0 views • 17 slides