Stand Out in Search: The Art of Rich Snippet Optimization
\nRich snippets are enhanced search results that provide additional information beyond traditional titles and meta descriptions. Achieved through structured data markup, such as JSON-LD or Microdata, rich snippets offer a more detailed preview of webpage content in search engine results. Examples in
1 views • 8 slides
Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
2 views • 46 slides
CS 404/504 Special Topics
Adversarial machine learning techniques in text and audio data involve generating manipulated samples to mislead models. Text attacks often involve word replacements or additions to alter the meaning while maintaining human readability. Various strategies are used to create adversarial text examples
1 views • 57 slides
Brief Introduction Of Search Engine Optimization
Search Engine Optimization (SEO) is the practice of enhancing the visibility and ranking of a website or web page in the organic (non-paid) search engine results. The higher a website ranks on a search engine results page (SERP), the more likely it is to attract visitors. SEO involves a combination
2 views • 16 slides
The Importance of a Thorough Chief Financial Officer Executive Search
\"The Importance of a Thorough Chief Financial Officer Executive Search\" highlights the critical role of a meticulous search process in identifying the right CFO. This blog explores the significance of finding a candidate with the right skills, experience, and cultural fit to drive financial perfor
0 views • 9 slides
Exploring Adversarial Machine Learning in Cybersecurity
Adversarial Machine Learning (AML) is a critical aspect of cybersecurity, addressing the complexity of evolving cyber threats. Security analysts and adversaries engage in a perpetual battle, with adversaries constantly innovating to evade defenses. Machine Learning models offer promise in combating
0 views • 43 slides
Understanding Search Procedures and Warrants in Legal Context
Search procedures play a crucial role in law enforcement, allowing authorities to explore, probe, and seek out hidden or suspected items. This comprehensive outline covers the meaning of search, locations where searches are conducted, objects searched for, legal definitions of search of a place, sea
0 views • 11 slides
Executive Search Specialists In London
Starfish Search is a chief executive officer search specialist executive search recruitment firm in London We offer board recruitment services, top executive search. \/\/starfishsearch.com
0 views • 13 slides
Understanding Adversarial Attacks in Machine Learning
Adversarial attacks in machine learning aim to investigate the robustness and fault tolerance of models, introduced by Aleksander Madry in ICML 2018. This defensive topic contrasts with offensive adversarial examples, which seek to misclassify ML models. Techniques like Deep-Fool are recognized for
0 views • 29 slides
Understanding Adversarial Machine Learning Attacks
Adversarial Machine Learning (AML) involves attacks on machine learning models by manipulating input data to deceive the model into making incorrect predictions. This includes creating adversarial examples, understanding attack algorithms, distance metrics, and optimization problems like L-BFGS. Var
0 views • 88 slides
Understanding Adversarial Threats in Machine Learning
This document explores the world of adversarial threats in machine learning, covering topics such as attack nomenclature, dimensions in adversarial learning, influence dimension, causative and exploratory approaches in attacks, and more. It delves into how adversaries manipulate data or models to co
0 views • 10 slides
Limitations of Deep Learning in Adversarial Settings
Deep learning, particularly deep neural networks (DNNs), has revolutionized machine learning with its high accuracy rates. However, in adversarial settings, adversaries can manipulate DNNs by crafting adversarial samples to force misclassification. Such attacks pose risks in various applications, in
0 views • 38 slides
Adversarial Risk Analysis for Urban Security
Adversarial Risk Analysis for Urban Security is a framework aimed at managing risks from the actions of intelligent adversaries in urban security scenarios. The framework employs a Defend-Attack-Defend model where two intelligent players, a Defender and an Attacker, engage in sequential moves, with
1 views • 26 slides
Covert Visual Search and Effective Oculomotor Range Constraints
The study delves into whether covert visual search is biologically limited by the Effective Oculomotor Range (EOMR), exploring neuropsychological evidence, eye movement studies, and participant measurements. It investigates the impact on visual search tasks, including color, orientation, and conjunc
1 views • 15 slides
Adversarial Learning in ML: Combatting Internet Abuse & Spam
Explore the realm of adversarial learning in ML through combating internet abuse and spam. Delve into the motivations of abusers, closed-loop approaches, risks of training on test data, and tactics used by spammers. Understand the challenges and strategies involved in filtering out malicious content
0 views • 13 slides
Understanding Informed and Uninformed Search Algorithms in Artificial Intelligence
Delve into the world of search algorithms in Artificial Intelligence with a focus on informed methods like Greedy Search and A* Search, alongside uninformed approaches such as Uniform Cost Search. Explore concepts like search problems, search trees, heuristic functions, and fringe strategies to comp
0 views • 69 slides
Distillation as a Defense Against Adversarial Perturbations in Deep Neural Networks
Deep Learning has shown great performance in various machine learning tasks, especially classification. However, adversarial samples can manipulate neural networks into misclassifying inputs, posing serious risks such as autonomous vehicle accidents. Distillation, a training technique, is proposed a
3 views • 31 slides
Understanding Robustness to Adversarial Examples in Machine Learning
Explore the vulnerability of machine learning models to adversarial examples, including speculative explanations and the importance of linear behavior. Learn about fast gradient sign methods, adversarial training of deep networks, and overcoming vulnerabilities. Discover how linear perturbations imp
0 views • 37 slides
Adversarial Attacks on Post-hoc Explanation Methods in Machine Learning
The study explores adversarial attacks on post-hoc explanation methods like LIME and SHAP in machine learning, highlighting the challenges in interpreting and trusting complex ML models. It introduces a framework to mask discriminatory biases in black box classifiers, demonstrating the limitations o
2 views • 18 slides
Innovative Features and Advancements in Patent Search Systems
Uncover the latest developments in the world of patent search systems through an enriching webinar presentation. Delve into the future developments, new features, search interfaces, and the importance of utilizing advanced search capabilities. Explore the significance of complex queries, stemming pr
1 views • 63 slides
The Battle Between Search Engines and Social Media
In the ongoing debate of Search Engines vs. Social Media, the focus is on visibility for businesses and products. While search engines excel in catering to our search habits and providing accurate results, social media offers peer recommendations, real-time responses to criticism, and immediate avai
0 views • 7 slides
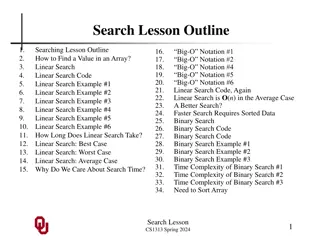
Understanding Linear Search: A Detailed Guide
Linear search is a fundamental algorithm for finding a value in an array. This guide covers the concept, code implementation, examples, time complexity analysis, and comparison with binary search. Explore how linear search works, its best and worst-case scenarios, and why search time matters in prog
0 views • 34 slides
Enhancing ITU-T Search Tools and MyWorkspace Features - November 2017
Explore the latest updates to ITU-T's search tools and MyWorkspace in November 2017. Discover improvements in global search engine capabilities, thematic search options, and personalized features for users. Enhance your search experience and access valuable resources efficiently through ITU-T's inno
0 views • 13 slides
Understanding Search Engines and Their Importance
Search engines, such as Google, play a crucial role in retrieving information from the web, providing access to a vast document collection, and helping users find what they need quickly and efficiently. They come in different types like robot-driven and meta search engines, each serving specific pur
1 views • 23 slides
Parallel Search Algorithm - Types and Approaches
Exploring parallel search algorithms in artificial intelligence, this study delves into various types like Sequential Depth First Search, Sequential Best First Search, and their parallel counterparts. The research outlines the process of searching for elements in initial and goal states, emphasizing
0 views • 24 slides
k-Ary Search on Modern Processors
The presentation discusses the importance of searching operations in computer science, focusing on different types of searches such as point queries, nearest-neighbor key queries, and range queries. It explores search algorithms including linear search, hash-based search, tree-based search, and sort
0 views • 18 slides
Understanding Game Playing and Adversarial Search at University of Berkeley
Delve into the realm of game playing and adversarial search at the University of Berkeley to understand the complexities of multi-agent environments. Explore the concepts of competitive MA environments, different kinds of games, and the strategic decision-making processes involved in two-player game
0 views • 81 slides
Solving Problems by Searching in Artificial Intelligence: Uninformed Search Strategies
In the field of Artificial Intelligence, solving problems through searching is essential. Uninformed search strategies, also known as blind search, involve exploring the search space without any additional information beyond what is provided in the problem definition. Techniques such as Breadth-Firs
1 views • 26 slides
Understanding Search Patterns for Music Materials in Libraries
Exploring how students search for music materials using a single search box, this study investigates if the nature of music materials influences search patterns compared to other subjects. It also evaluates the effectiveness of tools like federated search and discovery layers in facilitating searche
0 views • 25 slides
Heuristic Search Algorithms in Artificial Intelligence
In the realm of artificial intelligence, heuristic search algorithms play a pivotal role in efficiently navigating large search spaces to find optimal solutions. By leveraging heuristics, these algorithms can significantly reduce the exploration of the search space and guide agents towards the goal
0 views • 14 slides
Understanding Zero-Shot Adversarial Robustness for Large-Scale Models
Pretrained large-scale vision-language models like CLIP show strong generalization on unseen tasks but are vulnerable to imperceptible adversarial perturbations. This work delves into adapting these models for zero-shot transferability in adversarial robustness, even without specific training on unk
0 views • 18 slides
Understanding Depth-First Search in State Space Exploration
Depth-First Search (DFS) is a search strategy employed in state space exploration, where the search algorithm delves deep into a single branch of the search tree before backtracking to explore alternative paths. DFS is efficient for deep search spaces but can get lost in blind alleys if not implemen
0 views • 19 slides
Evaluating Adaptive Attacks on Adversarial Example Defenses
This content discusses the challenges in properly evaluating defenses against adversarial examples, highlighting the importance of adaptive evaluation methods. While consensus on strong evaluation standards is noted, many defenses are still found to be vulnerable. The work presents 13 case studies o
0 views • 9 slides
Understanding Adversarial Search in Artificial Intelligence
Adversarial search in AI involves making optimal decisions in games through concepts like minimax and pruning. It explores the strategic challenges of game-playing, from deterministic turn-taking to the complexities of multi-agent environments. The history of computer chess and the emergence of huma
0 views • 56 slides
Foundations of Artificial Intelligence: Adversarial Search and Game-Playing
Adversarial reasoning in games, particularly in the context of artificial intelligence, involves making optimal decisions in competitive environments. This module covers concepts such as minimax pruning, game theory, and the history of computer chess. It also explores the challenges in developing AI
0 views • 56 slides
Machine Learning for Cybersecurity Challenges: Addressing Adversarial Attacks and Interpretable Models
In the realm of cybersecurity, the perpetual battle between security analysts and adversaries intensifies with the increasing complexity of cyber attacks. Machine learning (ML) is increasingly utilized to combat these challenges, but vulnerable to adversarial attacks. Investigating defenses against
0 views • 41 slides
Exploring Adversarial Search and Minimax Algorithm in Games
Competitive games create conflict between agents, leading to adversarial search problems. The Minimax algorithm, used to optimize player decisions, plays a key role in analyzing strategies. Studying games offers insights into multiagent environments, economic models, and intellectual engagement. The
0 views • 17 slides
Overview of Informed Search Methods in Computer Science
Detailed exploration of informed search methods in computer science, covering key concepts such as heuristics, uninformed vs. informed search strategies, Best-First Search, Greedy Search, Beam Search, and A* Search. Learn about different algorithms and their applications to solve complex problems ef
0 views • 47 slides
Techniques in Beyond Classical Search and Local Search Algorithms
The chapter discusses search problems that consider the entire search space and lead to a sequence of actions towards a goal. Chapter 4 explores techniques, including Hill Climbing, Simulated Annealing, and Genetic Search, focusing solely on the goal state rather than the entire space. These methods
0 views • 51 slides
Efficient Image Compression Model to Defend Adversarial Examples
ComDefend presents an innovative approach in the field of computer vision with its efficient image compression model aimed at defending against adversarial examples. By employing an end-to-end image compression model, ComDefend extracts and downscales features to enhance the robustness of neural net
0 views • 16 slides