Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
Enhancing Professional Learning Through Active Listening Framework
Explore a comprehensive professional learning resource focusing on inclusion, wellbeing, and equalities for Scotland's educators and learners. The resource includes slides on active listening, interconnectivity, and guidance on how to utilize the material effectively. Dive into the National Model fo
11 views • 24 slides
Forever Fit: A Holistic Approach to Active Aging
Embracing an insight-led strategy, Forever Fit focuses on supporting older adults to lead active lifestyles. Collaborating with Everyone Active, their community health and wellbeing programs aim to address health disparities and promote physical activity. By harnessing community insights and fosteri
4 views • 5 slides
Understanding Active and Passive Voice Usage
Learn about the differences between active and passive voice in English grammar, how to convert sentences from active to passive voice, and examples of active and passive voice usage in different tenses. Understand which verbs can be used in passive voice constructions and practice changing sentence
9 views • 7 slides
Houston Active Living Plan Overview
The Houston Active Living Plan is a comprehensive initiative focused on improving the health and quality of life for Houston residents by promoting active lifestyles, access to healthy foods, and tobacco-free environments. The plan addresses key health concerns such as obesity, high blood pressure,
0 views • 14 slides
Understanding Active Transport: Energy-Driven Cellular Processes
Active transport is a vital process in cells that require energy in the form of ATP to move materials across the plasma membrane against their concentration gradient. This process involves pumps, endocytosis, and exocytosis. The sodium-potassium pump in nerve cells is a classic example of active tra
0 views • 9 slides
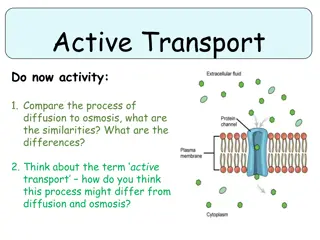
Understanding Passive and Active Transport in Cells
Explore the processes of diffusion, osmosis, and active transport in cells. Understand the similarities and differences between them, and learn why active transport is crucial for living organisms. Watch a video on active transport and answer related questions to deepen your knowledge. Enhance your
1 views • 12 slides
Active Norfolk Strategy 2021-26 Consultation Overview
Active Norfolk, hosted by Norfolk County Council, is a strategic lead for sport and physical activity, aiming to create a future in Norfolk where being physically active is the norm. Their mission includes tackling inequalities and promoting physical and mental well-being. The strategy focuses on ke
0 views • 11 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
1 views • 51 slides
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Understanding Passive and Active Voice in English Language
Learn about the passive and active voice in English grammar, focusing on describing processes and actions where the doer is unknown or unimportant. Explore examples, differences between active and passive voice, and how to convert sentences from active to passive voice. Practice activities to enhanc
1 views • 12 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
Effective Strategies for Active Supervision in Education
Explore the concept of active supervision as a low-intensity strategy to support instruction in educational settings. Understand the distinct elements, benefits, challenges, and the effectiveness of active supervision in preventing problem behavior and promoting positive learning environments. Suppo
0 views • 20 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Fun Physical Activities for Active Schools Champions
Engage as an Active Schools Champion by promoting physical activity through exciting games like Roll-n-Run, Disc Slam, Twirl-a-Whirl, Spin Fit, and Flying Saucer. These activities encourage movement, coordination, and teamwork, making fitness fun for students. Embrace the role of an Active Schools C
0 views • 6 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Active Schools Games: Fun Fitness and Sports Challenges Await!
Join the exciting Active Schools Games featuring Starlight Steps to Fitness (Beginner), Starlight Steps to Fitness (Advanced), and Starlight Sports Challenges Game. Roll the dice, complete challenges, earn points, and race to the finish line in these engaging fitness and sports activities. Choose op
0 views • 8 slides
Understanding Active and Passive Voice in English Writing
Explore the forms and uses of active and passive voice in English writing with examples and explanations. Learn how to distinguish between active and passive voice, create passive sentences using appropriate tenses, and understand when to use each voice effectively in different situations. Enhance y
0 views • 15 slides
Active Response Mechanism for IaaS Cloud Security
Stepping-stone attacks in IaaS clouds pose a new threat where attackers compromise vulnerable VMs to launch attacks against external hosts. This research explores the necessity of self-protection mechanisms for IaaS providers, emphasizing active response to detect and stop outgoing attacks at edge f
0 views • 24 slides
Understanding Active vs Primary Status in Education System of British Columbia
In the education system of British Columbia, students classified as Active no Primary are those who are no longer active in their Primary School (School of Record) but are active in a Secondary School. This status affects reporting, tracking, and school record maintenance. Schools and Districts have
0 views • 8 slides
Enhancing Learning Through Active Engagement: Strategies and Insights
Explore the concept of active learning with Swati Ramani, Director of Faculty Development & Curriculum Management at the Southern California University of Health Sciences. Discover the practical applications of active learning, key learning outcomes, and strategies for effective implementation. Dive
1 views • 19 slides
Insights from Residents on Active Travel in Doncaster
This report highlights findings from a survey on active travel in Doncaster, covering respondent demographics, levels of active travel, influencing factors, preferred transport methods, perceptions, future plans, and key insights. Key findings include the age groups and employment status of responde
0 views • 35 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
Lessons Learned from Roanoke City Health Department's Active Shooter Incident
Roanoke City Health Department faced a threat of an active shooter in 2016. The incident prompted immediate response actions, including mobilizing an incident command team and enhancing security measures. Transitional responses involved state-level collaboration for investigation and operational sec
0 views • 10 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
1 views • 42 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Pennsylvania School Threat Assessment Procedures and Guidance
Ongoing concerns about school safety led to legislation in 2019, requiring schools in Pennsylvania to establish threat assessment teams. This presentation provides an overview of the statute, threat levels, team responsibilities, procedures, and resources for school staff, parents, and guardians to
0 views • 25 slides
Conducting Threat Assessments Through the Atrocity Prevention Lens
This module from the GLOBAL CENTRE FOR THE RESPONSIBILITY TO PROTECT focuses on conducting threat assessments through an atrocity prevention lens. It covers risk identification, situational awareness in field settings, information collection methods, addressing vulnerabilities of women and children,
0 views • 20 slides
Bomb Threat Preparedness Guidelines for Shifa International Hospital
The Shifa International Hospital emphasizes the importance of maintaining a secure environment for employees, patients, and visitors in the event of a bomb threat. This presentation covers the types of bomb threats, steps to follow in case of a bomb threat, and provides guidance on handling telephon
0 views • 14 slides
High School Students Behavioral Threat Assessment Tabletop Exercise Analysis
Conduct a tabletop exercise analyzing the behavioral threat assessment of two high school students. Explore roles and responsibilities, exercise itinerary, goal, and purpose to enhance threat assessment team preparedness and response. Utilize simulated scenarios to simulate real-world events for opt
0 views • 23 slides
Examining Stereotype Threat in Engineering Education
Exploring the experiences of female engineering students facing stereotype threat, this critical theoretical framework study sheds light on the challenges that impact their academic journey. Through narrative inquiry methodology, the research focuses on white female students to understand how stereo
0 views • 37 slides
Understanding Active/Active SQL Clusters for High Availability
Discover the importance of Active/Active SQL clusters for ensuring 24/7 availability of your database servers. Learn about the benefits, setup process, and the high availability solution it offers for the entire server instance. Follow a detailed step-by-step guide for setting up SQL Active/Active c
0 views • 18 slides
School Safety and Threat Assessment Program Overview
Fact-based Threat Assessment for Safe and Supportive School Programs involves identifying, inquiring, assessing, and managing potentially dangerous situations. It aims to distinguish between those making threats and those posing real risks, without profiling or labeling individuals. Understanding th
0 views • 20 slides
Impact of Stereotypes on Perceived Facial Threat in Women Offenders
Facial expressions play a significant role in understanding emotions, but stereotypes can influence how people perceive facial affect. This study examines how reading tabloid articles about crimes committed by dark and light-skinned women offenders affects the perceived facial threat. Using a 2x2 fa
0 views • 9 slides