Mitigating Multi-Target Attacks in Hash-Based Signatures
"Explore advanced techniques for enhancing security in hash-based signature schemes to address multi-target attacks and ensure post-quantum security. Delve into trapdoor identification schemes, Merkle's hash-based signatures, and minimizing security assumptions."
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
Mitigating Multi-Target-Attacks in Hash-based Signatures Andreas H lsing joint work with Joost Rijneveld, Fang Song
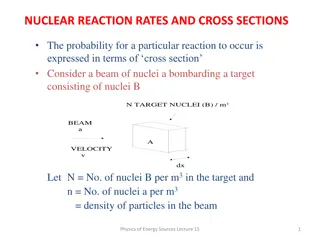
Trapdoor- / Identification Scheme-based (PQ-)Signatures Lattice, MQ, Coding Signature and/or key sizes = + + + 2 1 y x x x x x x 1 1 2 1 4 3 x = + + + + 2 3 1 y x x x x x 2 2 3 2 4 1 = ... y 3 Runtimes Secure parameters 12-4-2025 PAGE 5
Hash-based Signature Schemes [Mer89] Post quantum Only secure hash function Security well understood Fast 12-4-2025 PAGE 6
Basic Construction 12-4-2025 PAGE 8
Lamport-Diffie OTS [Lam79] Message M = b1, ,bm, OWF H = n bit * SK sk1,0 sk1,1 skm,0 skm,1 H H H H H H PK pk1,0 pk1,1 pkm,0 pkm,1 bm b1 b2 Mux Mux Mux Sig sk1,b1 skm,bm 12-4-2025 PAGE 9
Merkles Hash-based Signatures PK SIG = (i=2, , , , , ) H H H OTS H H H H H H H H H H H H OTS OTS OTS OTS OTS OTS OTS OTS SK 12-4-2025 PAGE 10
Minimizing security assumptions... [BHH+15,BDE+11,BDH11, DOTV08,H l13,HRB13]
XMSS Tree: Uses bitmasks H Leafs: Use binary tree with bitmasks H OTS: WOTS+ bi Message digest: Randomized hashing Collision-resilient -> signature size halved
Multi-Tree XMSS Uses multiple layers of trees -> Key generation (= Building first tree on each layer) (2h) (d*2h/d) -> Allows to reduce worst-case signing times (h/2) (h/2d)
...and dealing with the consequences
Multi-target attacks What is the bit security of a protocol using a n = 256 bit hash function that requires one-wayness? 256 bit? Not necessarily!
Multi-target attacks Consider ?? { ?: 0,1? 0,1?|? 0,1?} Assume protocol that uses ?? times Break invert ?on one out of ? different values. Attack complexity: (2? log ?) (generic attacks) Bit security: ? log? Similar problem applies for SPR, eTCR,....
Formalizing the issue One-wayness: for any classical q-query A Single-function, multi-target one-wayness
Solution? Use different elements from function family for each hash. - Makes problems independent - Each hash query can only be used for one target!
Multi-function, multi-target OW Seems trivial, right? What about the quantum case? Still trivial?
Technique for quantum bounds Define hard avg. case search problem: Reduce this to OW (SPR,....) of random function family
Implications Tight security for MSS that rely on multi-function properties (works for stateful & stateless). New function (key) for each call. New bitmask too for SPR. No solution for message digest, yet (see eTCR)
XMSS / XMSS XMSS / XMSS- -T Implementation T Implementation (same parameters) (same parameters) C Implementation, using OpenSSL [HRS16] Sign (ms) Signature (kB) Public Key (kB) Secret Key (kB) Bit Security classical/ quantum Comment XMSS 3.24 2.8 1.3 2.2 212 / 106 h = 20, d = 1, XMSS-T 9.48 2.8 0.064 2.2 190 / 95 h = 20, d = 1 XMSS 3.59 8.3 1.3 14.6 170 / 85 h = 60, d = 3 XMSS-T 10.54 8.3 0.064 14.6 190 / 95 h = 60, d = 3 Intel(R) Core(TM) i7 CPU @ 3.50GHz All using SHA2-256, w = 16 and k = 2
XMSS / XMSS XMSS / XMSS- -T Implementation T Implementation (same security) C Implementation, using OpenSSL [HRS16] Sign (ms) Signature (kB) Public Key (kB) Secret Key (kB) Bit Security classical/ quantum Comment XMSS 4.98 3.5 1.5 2.6 256/ 128 h = 20, d = 1, m = 276, n = 300 XMSS-T 10.14 2.9 0.064 2.2 256/ 128 h = 20, d = 1, m = 276, n = 256 XMSS 6.43 13.7 1.7 21.4 256/ 128 h = 60, d = 3, m = 316, n = 342 XMSS-T 12.82 8.8 0.064 14.6 256/ 128 h = 60, d = 3, m = 316, n = 256 Intel(R) Core(TM) i7 CPU @ 3.50GHz All using SHA2-256 or SHA2-512, w = 16 and k = 2
In paper XMSS-T ( == draft-irtf-cfrg-xmss-hash-based-signatures-02 ) Tight security reduction for XMSS-T Implementation of XMSS & XMSS-T
Thank you! Questions? For references & further literature see https://huelsing.wordpress.com/hash-based-signature-schemes/literature/ 12-4-2025 PAGE 29