Defeating Vanish: Low-Cost Sybil Attacks Against Large DHTs
Explore the vulnerabilities of Vanish, a self-destructing data system, to low-cost Sybil attacks in large Distributed Hash Tables (DHTs). Learn about the potential risks, costs, countermeasures, and security implications associated with transient data storage in DHT networks.
Uploaded on Sep 02, 2024 | 1 Views
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
Click to edit Master title style Defeating Vanish with Low-Cost Sybil Attacks Against Large DHTs Scott Wolchok1 Owen S. Hofmann2 Nadia Heninger3 Edward W. Felten3 J. Alex Halderman1 Christopher J. Rossbach2Brent Waters2 Emmett Witchel2 1The University of Michigan2The University of Texas at Austin3 Princeton University
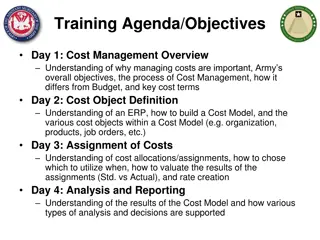
Click to edit Master title style Road Map 1. What is Vanish? 2. Attacking Vanish 3. Costs and performance 4. Countermeasures 5. What went wrong?
Click to edit Master title style Why Self-Destructing Data? Alice Bob Transient messages tend to persist Stored copies enable retroactive attacks Attacker subpoenas data months or years later
Click to edit Master title style Vanish Geambasu, Kohno, Levy, Levy USENIX Security 09 Alice Bob DHT Mallory
Click to edit Master title style Vanish and Vuze Vuze DHT Vanish uses the Vuze DHT (Distributed Hash Table) Over 1 million nodes, mostly BitTorrent Nodes delete values after 8 hours
Click to edit Master title style Vanish and Vuze Vuze DHT Shares placed at random locations in the DHT Replicated to 20 closest nodes
Click to edit Master title style Is Vanish Secure? Vanish 0.1 prototype released at publication Included user-friendly Firefox plugin Focused wide attention on its practical security
Click to edit Master title style Road Map 1. What is Vanish? 2. Attacking Vanish 3. Costs and performance 4. Countermeasures 5. What went wrong?
Click to edit Master title style DHT Crawling Threat Threat: attacker might continuously archive all data in the DHT Later, query archive to decrypt messages Don t need specific targets when recording
Click to edit Master title style Crawling with a Sybil Attack
Click to edit Master title style Making the Attack Practical Insight: have 8 hours to observe fragments Vuze replicates to 20 nearest nodes 1. Every 30 minutes 2. On join!
Click to edit Master title style Hopping Strategy Sybils hop to new IDs every 3 minutes 160x resource amplification over 8 hours Practical attack needs only ~2000 concurrent Sybils with hopping
Click to edit Master title style Making the Attack Practical Insight: Vuze client is a notorious resource hog Only 50 instances fit in 2 GB of RAM! Can we more efficiently support 2000 Sybils?
Click to edit Master title style Optimized Sybil Client C, lightweight, event-based implementation Listen-only (no Vuze routing table!) Thousands of Sybils in one process
Click to edit Master title style Road Map 1. What is Vanish? 2. Attacking Vanish 3. Costs and performance 4. Countermeasures 5. What went wrong?
Click to edit Master title style Attack Costs? Vanish paper estimate (for 25% recovery at k=45, n=50): 87,000 Sybils $860,000/year What does attacking Vanish really cost?
Click to edit Master title style Experiments 1. Insert key shares into the DHT 2. Run attack from 10 Amazon EC2 instances 3. Measure: DHT coverage = % key shares recovered Key coverage = % messages decrypted Attack cost = EC2 charges (Sep. 2009)
Click to edit Master title style Experimental Results Cost for >99% Vanish key recovery? Attack Concurrent Sybils Key Shares Recovered Annual Attack Cost* $23,500 Hopping 500 92% Hopping + Optimized Client 2000 99.5% $9,000
Click to edit Master title style DHT Coverage vs. Attack Size 100% 80% DHT Coverage 60% 40% Experiment 20% Model 0% 0 30k 60k 90k 120k 150k 180k 210k 240k 270k Effective Sybils Hopping plus Optimized Client
Click to edit Master title style Key Recovery vs. Attack Size 100% 99% @ 136k Sybils 80% Key Recovery Key-sharing parameters (k/n) 60% 40% 7/10 9/10 45/50 25% @ 70k Sybils 20% 0% 0 30k 60k 90k 120k 150k 180k 210k 240k 270k Effective Sybils Hopping plus Optimized Client
Click to edit Master title style Annual Cost vs. Key Recovery $14,000 99% @ $9000 $12,000 $10,000 Key-sharing parameters (k/n) Annual Attack Cost 90% @ $7000 $8,000 25% @ $5000 $6,000 7/10 $4,000 9/10 $2,000 45/50 $0 0% 20% 40% Key Recovery 60% 80% 100% Hopping plus Optimized Client
Click to edit Master title style Storage $1400/yr for all observed data $80/yr for potential key shares
Click to edit Master title style Road Map 1. What is Vanish? 2. Attacking Vanish 3. Costs and performance 4. Countermeasures 5. What went wrong?
Click to edit Master title style Increase Key Recovery Threshold? Required coverage increases in n and k/n Why not raise them? (99/100?) Reliability: some shares lost due to churn Performance: pushing shares is slow!
Click to edit Master title style Limit Replication? Attack exploits aggressive replication Less replication might make the attack harder, but how much? More in a few slides
Click to edit Master title style Sybil Defenses from the Literature? Client puzzles Limit ports/IP, IPs/subnet, etc. Social networking
Click to edit Master title style Detecting Attackers Find and target IPs with too many clients Use node enumerator, Peruze Can detect attack IPs hours after the attack Detected the Vanish demo
Click to edit Master title style Road Map 1. What is Vanish? 2. Attacking Vanish 3. Costs and performance 4. Countermeasures 5. What went wrong?
Click to edit Master title style Cost Estimation Issues Vanish paper extrapolated from 8000-node DHT Assumed Sybils must run continuously Assumed attacker uses inefficient Vuze client
Click to edit Master title style Cost Not Linear in Recovery 1.0 0.8 Key Recovery Fraction V D O P r e c o v e r 0.6 Key-sharing parameters (k/n) 0.4 7/10 9/10 0.2 45/50 0.0 0.0 0.2 0.4 0.6 0.8 1.0 P recovershare Coverage Fraction
Click to edit Master title style Response to Our Work Second report and prototype by Vanish team1 New defenses Use both Vuze DHT and OpenDHT Disable replicate-on-join in Vuze Use less aggressive threshold replication Will these defenses stop real attackers? 1 Geambasu, Falkner, Gardner, Kohno, Krishnamurthy, Levy. Experiences building security applications on DHTs . Technical report, UW-CSE-09-09-01.
Click to edit Master title style Conclusion Showed attacks that defeat Vanish 0.1 in practice for $9000/year Vanish team has proposed new defenses Future work: are new defenses effective? Our take: building Vanish with DHTs seems risky.
Click to edit Master title style Defeating Vanish with Low-Cost Sybil Attacks Against Large DHTs Scott Wolchok1 Owen S. Hofmann2 Nadia Heninger3 Edward W. Felten3 J. Alex Halderman1 Christopher J. Rossbach2 Brent Waters2 Emmett Witchel2 1 The University of Michigan 2 The University of Texas at Austin 3 Princeton University http://z.cs.utexas.edu/users/osa/unvanish/
Click to edit Master title style Vanish Attack Model Need to recover k of n fragments p = Pr{recover key fragment} Pr{recover VDO} = Pr{recover k or more fragments} Binomial distribution Pr{recover VDO} = n k n n i i (1 ) p p i k =
Click to edit Master title style Coverage Model m Sybils see c of N objects Balls-in-bins problem Expected fraction = 1 e-cm/N= 1 e-sm s = c/N is the (overlapping) fraction of the network observed by each Sybil
Click to edit Master title style Prior Work Enumerating DHT nodes Cruiser [Stutzbach 2006a,b] Blizzard [Steiner 2007a] Measuring DHT traffic Mistral [Steiner 2007b] Montra [Memon 2009]
Click to edit Master title style Hopping plus Optimized Client Concurrent Sybils Hours # VDO Fragments Fragments Found 2000 8 1650 1640 (99.4%) 1692 (99.5%) 1561 (91.8%) 2000 7.5 1700 500 8 1650