Understanding IDS/IPS: Enhancing Security with SecurityGen's Advanced Solutions
In the realm of cybersecurity, Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) play pivotal roles in safeguarding networks against evolving threats. SecurityGen's IDS IPS solutions are designed to monitor network traffic, detect suspicious activities, and prevent potential i
4 views • 1 slides
Comprehensive IT & Security Solutions for Home and Business Needs
ONE STEP SOLUTION offers a range of IT services including computer sales & services, security solutions, CCTV surveillance systems, networking, fire alarm systems, and more. PROLOGIC SOLUTIONS provides reliable IT and security solutions for industrial and residential requirements, specializing in CC
0 views • 15 slides
Explore the Top 5 Trends in Alarm Systems with Shellharbour Security Systems
Explore the latest trends in alarm systems with Shellharbour Security Systems. Learn about advancements such as smart home integration, wireless technology, AI-powered monitoring, and more. Stay informed to enhance your home or business security with cutting-edge solutions. Visit: \/\/shellharbourse
7 views • 8 slides
Machine Learning Techniques for Intrusion Detection Systems
An Intrusion Detection System (IDS) is crucial for defending computer systems against attacks, with machine learning playing a key role in anomaly and misuse detection approaches. The 1998/1999 DARPA Intrusion Set and Anomaly Detection Systems are explored, alongside popular machine learning classif
0 views • 36 slides
Deception Game on Decoy Systems and Honeypots
Deception Game on Decoy Systems and Honeypots explores the use of deception technologies in computer security, focusing on decoy systems like honeypots. It delves into how attackers are lured into fake objects and the monitoring of their behavior to mitigate intrusion. The concept of fake honeypots,
4 views • 25 slides
Understanding Snort: An Open-Source Network Intrusion Detection System
Snort is an open-source Network Intrusion Detection System (NIDS) developed by Cisco, capable of analyzing network packets to identify suspicious activities. It can function as a packet sniffer, packet logger, or a full-fledged intrusion prevention system. By monitoring and matching network activity
0 views • 23 slides
Semantics-Aware Intrusion Detection for Industrial Control Systems by Mer Yksel
Mer Yksel, a PhD candidate at Eindhoven University of Technology, specializes in intrusion detection and data analytics with a focus on industrial control systems. His research covers targeted attacks, threat modeling, protection of ICS networks, and innovative anomaly-based approaches for cybersecu
0 views • 31 slides
One of the Best Smoke Alarm Inspections in Albany Creek
Hopkinson Electrical serves the Best Smoke Alarm Inspections in Albany Creek. Their commitment to quality, punctuality, and customer satisfaction sets them apart, They owe their success in operating a small business to repeat work, which speaks volum
0 views • 6 slides
Fire Safety Measures for CEU Facilities
Learn the essential steps for fire safety at Central European University (CEU), including how to raise the alarm, evacuate the building safely, and use fire alarm equipment. Follow the guidelines provided to ensure your safety in the event of a fire emergency.
0 views • 26 slides
Yale Intrusion Alarm System Overview
Yale, a global leader in security solutions, offers the Yale Intrusion Alarm system designed to secure homes and personal belongings. This system features the HSA-6403-PS and HSA-6404-GSM panels with various security elements like sensors, sirens, keypad, and more. Users can easily program and test
0 views • 24 slides
Success Traits of Ostariophysans: Weberian Apparatus and Alarm Response
Freshwater habitats are dominated by ostariophysans, thanks to their unique traits: the Weberian apparatus, a series of bones connecting the gas bladder with the inner ear, and the alarm response, involving the production of an alarm substance and a coordinated escape reaction. These characteristics
0 views • 9 slides
Comprehensive Overview of Distributed Intrusion Detection System (DIDS)
Explore the Distributed Intrusion Detection System (DIDS) introduced by Mohammad Hossein Salehi and Kiumars Talaee. Learn about the significance, working, and different types of IDS within DIDS like HIDS, NIDS, and agent-based IDS. Understand the division, information sources, and roles of client-ba
0 views • 25 slides
A Hybrid Intrusion Detection System Approach for IEEE 802.11 Wireless Networks
This research project explores the development of a hybrid intrusion detection system for IEEE 802.11 wireless networks. The study includes research objectives, background information, experimental results, evaluation, and comparison of existing systems, HWIDS design, conclusions, future work, and r
0 views • 73 slides
Effective Strategies for Virtualizing Intrusion Detection Systems
Explore the benefits of virtualizing intrusion detection systems through microservices, addressing the limitations of traditional monolithic IDS setups. Learn how this approach improves scalability, efficiency, and customization for enhanced security measures in network environments.
0 views • 25 slides
Mastering Intrusion Detection with Snort: A Comprehensive Guide
Dive into the world of network security with Snort, the powerful intrusion detection system. Learn how to analyze network traffic in real time, create custom configuration files, and defend against zero-day attacks. Explore Snort's versatility, portability, and configurability, and discover advanced
0 views • 5 slides
Understanding IDS and IPS for Network Security
Enhance the security of your network with IDS (Intrusion Detection System) and IPS (Intrusion Prevention System) by monitoring traffic, inspecting data packets, and detecting malicious activities based on known signatures. Learn about different types like HIDS and NIDS, their functions, and tools us
0 views • 7 slides
Understanding Intrusion Detection Systems (IDS)
Intrusion Detection Systems (IDS) are software pieces that monitor computer systems to detect unauthorized intrusions and misuse, responding by logging activity, notifying authorities, and taking appropriate countermeasures. IDS help address security challenges, aiming to find and fix serious securi
0 views • 40 slides
Root Causes of Intrusion Detection False Negatives: Methodology and Case Study
This study, presented at IEEE MILCOM 2019 by Eric Ficke, Kristin M. Schweitzer, Raymond M. Bateman, and Shouhuai Xu, delves into the analysis of root causes of intrusion detection false negatives. The researchers explore methodologies and present a case study to illustrate their findings.
0 views • 24 slides
Understanding Intrusion Detection Systems (IDS) and Snort in Network Security
Intrusion Detection Systems (IDS) play a crucial role in network security by analyzing traffic patterns and detecting anomalous behavior to send alerts. This summary covers the basics of IDS, differences between IDS and IPS, types of IDS (host-based and network-based), and the capabilities of Snort,
0 views • 34 slides
Anomaly-Based Network Intrusion Detection in Cyber Security
An overview of the importance of network intrusion detection, its relevance to anomaly detection and data mining, the concept of anomaly-based network intrusion detection, and the economic impact of cybercrime. The content also touches on different types of computer attacks and references related to
0 views • 32 slides
Understanding Intrusion Detection and Prevention Systems
Learn about the components and implementation options of intrusion detection and prevention systems, as well as the goals and role of an IDPS in network defense. Discover the capabilities of IDPS, such as assessing network traffic, detecting unauthorized access, and responding to threats. Explore an
0 views • 57 slides
Comprehensive Guide to Hacking Techniques & Intrusion Detection
Dive into the world of hacking techniques, intrusion detection, and network protocols with expert Ali Al-Shemery. Learn about host discovery, port scanning, packet crafting, and more using tools like Nmap. Explore the importance of network protocols like TCP, UDP, ICMP, and ARP. Discover the art of
0 views • 50 slides
Introducing Connected Alarm Clock IoT Project
Explore the innovative Connected Alarm Clock IoT project developed by EFREI-M1-CLOCK students. This project combines traditional alarm clock features with IoT technology, allowing users to set unlimited alarms remotely. The system includes equipment such as RTC DS3231, Arduino UNO, Wi-Fi Rev2, and o
0 views • 7 slides
Deep Sea Electronics PLC - Alarm Status and Conditions Overview
Deep Sea Electronics PLC, located in North Yorkshire, England, specializes in electronic systems for the marine industry. The provided information details alarm status and conditions for their GENCOMM protocols, highlighting active alarms and alarm conditions. This comprehensive guide includes regis
0 views • 12 slides
Managing BEAST Alarm System: Enhancing Alarm Monitoring and Analysis
Explore how managing the BEAST alarm system with a detailed alarm history helps in better understanding event sequences, producing alarm statistics, identifying nuisance alarms, and finding patterns. The operations alarm dashboard provides visualization, trends, and statistics with advanced filterin
0 views • 5 slides
Setting Flow Alarm Maintenance Procedure
Learn how to enter maintenance mode, adjust low flow alarm points, and set trip points for a flow alarm system. Follow step-by-step instructions provided by RKI Instruments for calibrating and setting your flow alarm device. Ensure proper functioning by correctly adjusting values and following the o
0 views • 4 slides
Integrated Alarm System for ALMA Observatory Architecture - Development Overview
Detailed documentation from ALMA-CTA meetings showcasing the development stages and components of the Integrated Alarm System for the ALMA Observatory. Includes insights on alarm systems, computing elements, distributed units, and implementation strategies discussed in Garching meetings.
0 views • 19 slides
Proposed Amendments to Burglar Alarm Ordinance
The Department of Administration & Regulatory Affairs presented a proposal to amend the Burglar Alarm Ordinance due to issues faced by permit holders post-Hurricane Harvey. The current ordinance does not address concerns such as permit transfers, refunds for false alarm fees, and refunds for permits
0 views • 5 slides
Innovative Sleep Monitoring Device for Improved Rest
EEG Alarm by Jackson Bautch, Alex Beck, Josh O'Brien, and Megan O'Donnell offers a solution to track sleep stages throughout the night using Electroencephalogram (EEG) technology. With fewer electrodes and a compact design, the device sends sleep data to the user's phone and sets off an alarm during
0 views • 7 slides
Fun with Neha and Her Alarm Clock: A Story of Morning Adventures
Join Neha as she navigates the morning routine with her pesky alarm clock and chirpy birds, facing challenges and learning to appreciate the start of a new day. Explore jumbled words, word puzzles, and word choices while engaging in activities related to a Sunday morning. Enhance language skills thr
0 views • 11 slides
Update on Vitrage Project at OpenStack Summit Vancouver
Vitrage is an OpenStack service for organizing and analyzing alarms and events, providing root cause analysis to deduce alarms and states based on system insights. Founded during the Mitaka release, it became an official OpenStack project in 2016 and has seen continuous development with features lik
0 views • 16 slides
Understanding Radon and Chemical Soil Gas Vapor Intrusion
This presentation at the 2019 International Radon Symposium in Denver, Colorado explores the association between radon, chemical soil gas, and vapor intrusion. It discusses the challenges in testing, analyzing differences, and the need for supplemental measurements like radon to validate models. The
0 views • 19 slides
Alternative Vapor Intrusion Screening Tools for Environmental Investigations
Estimation of subslab attenuation factors for vapor intrusion investigations is crucial in assessing indoor air quality. This study reviews EPA methods, emphasizing the importance of vapor attenuation in screening indoor air for contaminants. Various experts contributed insights, leading to the deve
0 views • 35 slides
Understanding Client-Side Attacks and Intrusion Detection
Explore client-side attacks, their methodology, and defense strategies in Ali Al-Shemery's comprehensive guide. Discover the evolving challenges of network security and the importance of staying ahead with effective intrusion detection techniques.
0 views • 65 slides
Understanding Intrusion Detection and Security Tools
Explore the world of intrusion detection, access control, and security tools through terminology, systems, classifications, and methods. Learn about intrusion detection systems (IDSs), their terminology, alert systems, classification methods like signature-based and statistical anomaly-based approac
0 views • 39 slides
Comprehensive Guide to Hacking Techniques and Intrusion Detection
This guide by Ali Al-Shemery provides insights into hacking techniques, intrusion detection, fingerprinting, external and internal footprinting, passive reconnaissance, WHOIS lookups, and various online tools for intelligence gathering during penetration tests. It covers identifying customer externa
0 views • 29 slides
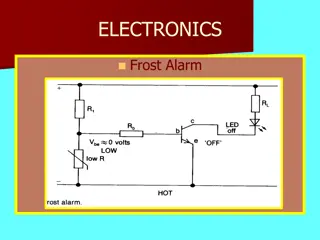
Exploring Electronic Alarm Circuits and Devices
Discover the workings of various electronic alarm circuits such as Frost Alarm, Fire Alarm, and Burglar Alarm. Learn how different sensors and components like thermistors, resistors, transistors, and capacitors are utilized to trigger alarms based on temperature changes, light conditions, and time d
0 views • 23 slides
Ensuring Compliance in Human Research Programs at Yale University
Yale University's Human Research Protection Program (HRPP) emphasizes the importance of preventing and addressing deviations in research practices. Led by experienced compliance managers, the HRPP RQA&C team at Yale focuses on conducting reviews, responding to research complaints, and developing eff
0 views • 32 slides
Tectonic Controls of the Sevier-Laramide Orogeny
The Sevier-Laramide orogeny was influenced by crustal thickening and gravitational extensional collapse. The tectonic model proposed suggests that conductive heating from subduction weakened the crust, leading to compression, uplift, and lateral growth. Deformation persisted from the Cretaceous to t
0 views • 8 slides
Analysis of Tropospheric Intrusion Evolution in START08 Field Campaign
The study presents the analysis of tropospheric intrusion evolution during the START08 Field Campaign using models such as WACCM and GFS. The primary goals include comparing model output with observations, verifying dynamical transport features, and studying the spatial and temporal evolution of mid
0 views • 26 slides