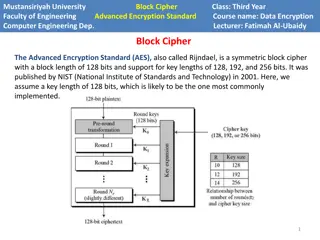
AES Encryption in Computer Engineering
Advanced Encryption Standard (AES) is a powerful symmetric block cipher used in computer engineering for data encryption. Developed by NIST, AES supports key lengths of 128, 192, and 256 bits. The algorithm operates on a state array and consists of encryption phases like initial round, main rounds,
3 views • 8 slides
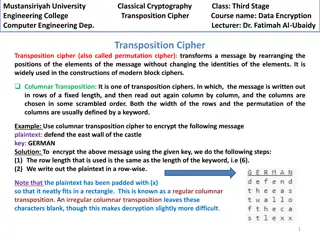
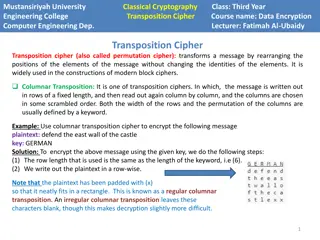
Columnar Transposition Cipher: Data Encryption Techniques at Mustansiriyah University Engineering College
Transposition ciphers, particularly the columnar transposition technique, are explored in the course "Data Encryption" at Mustansiriyah University Engineering College. The cipher involves rearranging message elements without changing their identities, making it crucial in modern block cipher designs
0 views • 4 slides
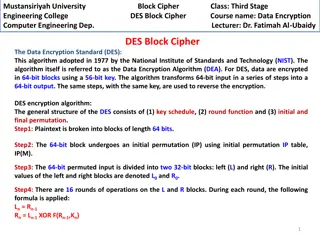
DES Block Cipher in Computer Engineering at Mustansiriyah University
Data Encryption Standard (DES) is a widely used algorithm for encrypting data in 64-bit blocks with a 56-bit key. This course at Mustansiriyah University covers the key components of DES, including the key schedule, round function, and initial/final permutation. Students learn about the encryption p
1 views • 8 slides
Evolution of Cryptography: From Ancient Techniques to Modern Security Mechanisms
Explore the evolution of cryptography from ancient techniques like the Caesar Cipher to modern security mechanisms like SSL, SSH, and IPSec. Learn how cryptography plays a crucial role in ensuring confidentiality, integrity, authentication, non-repudiation, and availability in network security. Disc
1 views • 62 slides
ADFGVX Cipher: Encryption and Decryption Techniques
Discover the ADFGVX cipher, a historical encryption method used to secure messages during World War I. Learn about Fritz Nebel and Gino Painvin, who played significant roles in its development. Explore the Polybius Square invented by Polybius in the 2nd century BC for converting letters to numbers.
0 views • 14 slides
Transposition Cipher Techniques in Modern Block Ciphers
Transposition ciphers, specifically columnar and double columnar transpositions, are explored in the context of data encryption and computer engineering at Mustansiriyah University Engineering College. These techniques involve rearranging message elements without changing their identities, providing
1 views • 4 slides
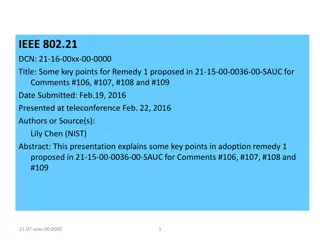
Optimizing MIH SA Establishment for Single Radio Handover
This presentation discusses the optimization of MIH (Media Independent Handover) Security Association (SA) establishment for single radio handover. It covers the key points and methods proposed for enhancing the communication between Mobile Node (MN) and Top Point of Service (TPoS) using cipher suit
4 views • 6 slides
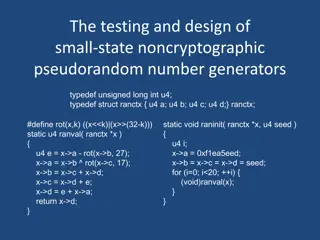
Small-State Noncryptographic Pseudorandom Number Generators
Explore the design and testing of small-state noncryptographic pseudorandom number generators, including definitions, rules of thumb, chisquare tests, existing and new generators, and more. Learn about block cipher encryption, hash functions, pseudorandom number generation, reversible mixing, and re
0 views • 46 slides
Block Ciphers in Cryptography
Explore the principles of block ciphers in modern cryptography, focusing on the Data Encryption Standard (DES) and its design principles. Learn about block cipher encryption, Feistel block cipher structure, n-bit block ciphers, ideal block ciphers, key length considerations, and challenges with idea
1 views • 44 slides
Encryption Techniques: From Transposition Ciphers to Rail Fence Ciphers
Explore the world of encryption techniques, diving into transposition ciphers and rail fence ciphers. Learn about encryption, decryption, plaintext, ciphertext, keys, and the art of secret writing. Discover how transposition ciphers reorder letters without changing their values and how rail fence ci
0 views • 26 slides
Encryption: Keys, Algorithms, and Applications
Encryption plays a crucial role in securing data transmission and storage. It involves using keys and algorithms to convert plaintext information into a cipher that can only be deciphered with the correct key. This article explores different encryption methods, such as private and public key encrypt
2 views • 62 slides
Key Principles in Cryptography: Kerckhoff's and Key Space
Understanding fundamental principles in cryptography, including Kerckhoff's principle, key space requirements, and the importance of secure private-key encryption. Exploring the Shift Cipher's security, key space size considerations, and the need for heuristic constructions for proving scheme securi
1 views • 51 slides
Overview of Modern Cryptography and Data Encryption Standard (DES)
Exploring modern cryptography including symmetric key block ciphers, public key ciphers, stream ciphers, and post-quantum ciphers. Focus on Data Encryption Standard (DES), Simplified DES, Feistel cipher, key schedule, expansion function, S-Box, DES encryption, and decryption processes.
1 views • 37 slides
Cryptography Basics and Toolbox
Cryptography serves the goals of managing who can view data, ensuring data integrity, and verifying the origin of data. It involves dramatis personae like Alice, Bob, Eve, and Oscar. The toolbox includes hash functions, symmetric encryption, and asymmetric encryption. Hash functions play a crucial r
1 views • 32 slides
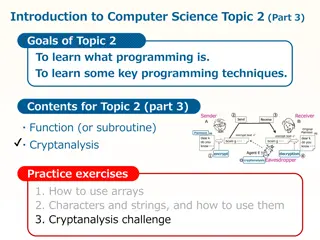
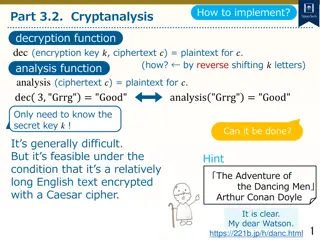
Cryptanalysis: Key Concepts and Techniques
Cryptanalysis is a fundamental aspect of cryptography that involves decoding encrypted communications and messages. This topic delves into the basic cryptographic tools, such as the Caesar cipher, and explores how encryption and decryption functions work. By understanding cryptanalysis, you can anal
0 views • 12 slides
Cryptanalysis and Decryption Techniques for Caesar Cipher
Learn how to decrypt Caesar cipher text using cryptanalysis techniques by analyzing letter frequencies and determining the secret key through character analysis. Explore methods to count character frequencies and find the most common letter to decipher encrypted messages.
0 views • 11 slides
Cryptographic Center in Novosibirsk: Advancements in Cryptography and Research
The Cryptographic Center in Novosibirsk, established in 2011, focuses on advancing cryptography through research, education, and international collaborations. With a team of researchers and students, the center explores various aspects of cryptography, including cryptographic Boolean functions, ciph
0 views • 33 slides
Exploration of Cryptography and Secure Communication Methods
Delve into the concepts of cryptography, data hiding, and secure communication methods such as Diffie-Hellman key exchange. Discover how Bob safely sends a ring to Alice, the use of Caesar cipher method, and the importance of mathematical principles in ensuring secure communication protocols. Learn
1 views • 22 slides
Introduction to Cryptology in Algebra 2 Classroom
Engage students in a high school Algebra 2 class by exploring cryptology concepts such as coding, hexadecimal systems, substitution ciphers, and the Vigenere cipher. The lesson plan includes activities like solving puzzles, introducing binary systems, converting to hexadecimal, and writing messages
1 views • 16 slides
Fun Spy Challenges for Beavers - Crack the Codes!
Dive into exciting spy missions with a group of clever beavers! Decode secret messages using various encryption techniques such as switching codes, letter grouping, Pig Pen cipher, Morse code, and Caesar cipher. Test your spy skills as you unravel each challenge to reveal hidden messages. Unleash yo
0 views • 6 slides
Encryption and its Importance in Everyday Life
Encryption is a crucial process that transforms messages into secret codes, ensuring only intended recipients can decipher them. This review delves into the significance of encryption for online activities, cracking different cipher methods, and recognizing security flaws. Discover how computational
0 views • 9 slides
Fundamentals of Cryptography and Network Security
Explore the basics of cryptography, including classical encryption techniques, terminology definitions, types of encryption operations, cryptanalysis objectives and attacks, and the concept of cipher strength. Uncover the principles and methods behind encryption and decryption, key distinctions betw
0 views • 52 slides
Unlock the Challenges in Cipher Cove: A STEM Adventure
Explore Cipher Cove and tackle five cryptographic challenges involving different ciphers such as Caesar Shift, Pigpen, Transposition, Substitution, and Periodic Table. Put your problem-solving skills to the test by deciphering hidden clues and codes to progress through each challenge and ultimately
0 views • 6 slides
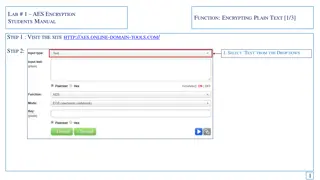
Guide to AES Encryption for Students - Encrypting and Decrypting Text
This manual provides a step-by-step guide on AES encryption for students. Learn how to encrypt plain text using a secure key, generate cipher text, and then decrypt it back to the original message. Follow the instructions on a specific website, enter your text, select encryption options, and save th
2 views • 6 slides
Loops and ASCII Values in Python
Learn about while loops, fencepost loops, and sentinel loops in Python programming. Explore how ASCII values are assigned to characters and how to manipulate them. Practice a Caesar cipher program to encrypt messages and discover common pitfalls in loop structures. Gain insights into the importance
3 views • 22 slides
Symmetric Encryption and Basic Terminology
This content covers symmetric encryption techniques, substitution and transposition methods, rotor machines, and basic cryptographic terminology such as plaintext, ciphertext, cipher, and key. It also discusses the requirements and assumptions for secure symmetric encryption, and the model of symmet
0 views • 49 slides
Muddiest Point: Questions on RSA, DDoS Attacks, and Block Cipher Algorithms
In this collection of images, various concepts related to RSA encryption, DDoS attacks, block cipher algorithms like DES and AES, TCP protocols, and real-life applications of cryptography are explored. The images cover topics such as the Mirai-infected devices used in a DDoS attack on Dyn, differenc
0 views • 14 slides
Cryptography: Modern Symmetric Ciphers
Explore the world of modern symmetric ciphers used in network security, from encryption basics to advanced techniques like Block vs. Stream Cipher and Autokeyed Vigenere Cipher. Understand the importance of encryption in providing protection for confidentiality, authentication, integrity, and non-re
0 views • 60 slides
Cryptanalysis and Rail Fence Cipher Decryption Methods
In this discussion, we explored cryptanalysis techniques and the decryption process of the rail fence cipher. By mapping text to random letter permutations, breaking ciphers through histograms, and analyzing letter frequency distributions, we delved into deciphering encrypted messages. The session h
0 views • 27 slides
Modes of Operation in Block Cipher: Understanding ECB, CBC, CFB, and OFB
A block cipher encrypts fixed-length blocks of text with a key, and NIST has defined five modes of operation to enhance cryptographic algorithms. Explore ECB, CBC, CFB, and OFB modes in detail to understand their unique characteristics and applications.
0 views • 13 slides
Overview of Data Encryption Standard (DES)
Data Encryption Standard (DES) is a symmetric-key block cipher created in 1973 by NIST. It uses a 64-bit plaintext to generate a 64-bit ciphertext and vice versa. The same 56-bit cipher key is employed for encryption and decryption, utilizing rounds with S-box and P-box steps, ensuring confusion and
0 views • 29 slides
History of Cryptography: Techniques, Evolution, and Impact
Delve into the fascinating world of cryptography through the ages, from ancient substitution ciphers to modern cipher devices. Explore the birth of cryptanalysis, polyalphabetic substitution, black chambers, and the development of innovative cipher devices post-WWI. Uncover the pivotal role cryptogr
0 views • 10 slides
Cryptography Evolution and Historical Cipher Systems
Explore the evolution of cryptography from Julius Caesar's Caesar Cipher to complex cryptographic systems used during the American Civil War. Understand the basics of symmetric key algorithms and the vulnerabilities of early ciphers. Dive into the significance of historical milestones in cryptograph
0 views • 58 slides
Cryptography Techniques: Caesar, Shift, and Affine Ciphers Explained
Explore classical cryptography methods including the Caesar cipher, shift cipher, and affine ciphers. Learn how these encryption techniques work and how to encrypt and decrypt messages using them.
0 views • 19 slides
Understanding Cryptography and Cipher Techniques
Dive into the world of cryptography with a focus on classic cipher techniques like the Caesar cipher and Vigenère cipher. Explore modern encryption algorithms such as AES and RSA, along with discussions on security concepts like cryptanalysis and cryptographic attacks. Discover how cryptography hel
0 views • 24 slides
Understanding the Shift Cipher Method for Cryptography
Dive into the world of cryptography with a focus on the Shift Cipher method, exploring encryption, decryption, the modulo operation, examples, and cryptanalysis techniques. Learn how to encrypt and decrypt messages using a shift in alphabets and understand the intricacies of breaking the cipher thro
0 views • 10 slides
RC4 Stream Cipher: Overview and Implementation at Mustansiriyah University
Explore the RC4 stream cipher, designed in 1987 by Ron Rivest, used in encryption protocols like WEP and WPA. Learn about the key initialization, permutation, and stream generation steps involved in RC4. Join the Data Encryption course at Mustansiriyah University to dive deeper into computer securit
0 views • 4 slides
Exploring Parallel Caesar Cipher Implementation in RISC-V
Discover the uniqueness of RISC-V architecture through a tutorial on writing and testing a parallel Caesar cipher implementation. Learn about RISC-V, Caesar cipher, sequential and parallel implementations, vector extensions, and more. Engage in discussions and Q&A to enhance your understanding.
0 views • 22 slides
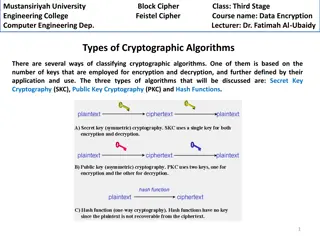
Understanding Cryptographic Algorithms Used in Data Encryption
Explore the classification of cryptographic algorithms based on key usage, including Secret Key Cryptography (SKC), Public Key Cryptography (PKC), and Hash Functions. Learn about Feistel Cipher, Block Cipher, and the structure of Feistel Cipher proposed by Feistel for creating block ciphers efficien
0 views • 6 slides
Hidden Markov Models for Vigenere Cryptanalysis - Techniques and Tests
Explore the application of Hidden Markov Models in Vigenere cryptanalysis through Classic Ciphers, Vigenere Cipher, and the Friedman Test for determining keyword length and ciphertext analysis.
0 views • 16 slides