Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
Cisco 300-220 Certification: All You Need to Know
Begin Your Journey Here--- https:\/\/bit.ly\/3PbovcW --- Access comprehensive details on the 300-220 exam guide to ace the Cisco Certified Specialist Threat Hunting and Defending certification. Gather all essential information on 300-220 tutorials, practice tests, books, study materials, exam questi
3 views • 17 slides
Role of AI in Threat Detection and Zero-day Attacks
Cybercrime has been on the rise, especially with the surge in zero-day attacks targeting various industries. State-sponsored actors, like Chinese groups, dominate zero-day exploits, challenging traditional detection methods. Incorporating AI, machine learning, and deep learning is vital in enhancing
0 views • 9 slides
Artificial Intelligence in Cyber Security: Enhancing Threat Detection and Response
Artificial Intelligence (AI) is revolutionizing cyber security by enhancing threat detection, response, and prevention capabilities. By leveraging machine learning algorithms, AI enables organizations to identify cyber threats, analyze behavioral patterns, automate incident response, adapt to evolvi
1 views • 33 slides
Strategic Planning Analysis for Starbucks Hong Kong
Conducting a strategic planning analysis for Starbucks in Hong Kong, focusing on Porter's Five Forces, PEST analysis, and market trends within the coffee and snacks store industry. Evaluate aspects such as threat of new entrants, supplier power, buyer power, rivalry, and threat of substitute product
0 views • 10 slides
Comprehensive Review on Medical Separations and Direct Threat Assessments for Health Staff
This resource provides an extensive overview of medical separations and direct threat assessments relevant to Job Corps health and wellness staff and subcontractors. It covers topics such as the process of medical separations, reinstatement rights, disability accommodation, and when medical separati
1 views • 60 slides
Software Development Life Cycle - Threat Modelling Initiation
Threat modelling should commence at the early stage of the software development life cycle to identify potential security risks and vulnerabilities effectively. It should ideally begin during the requirement analysis and continue throughout development, testing, and maintenance phases to ensure robu
3 views • 27 slides
Porter's Five Forces Analysis: Templates and Example
Explore Porter's Five Forces Analysis through templates and examples covering Threat of New Entry, Power of Buyers, Threat of Substitutes, Power of Suppliers, and Competitive Rivalry. Understand how to assess market forces impacting your business strategy and competition. Disclaimer included for ref
0 views • 4 slides
Understanding Microsoft Sentinel Fusion for Advanced Threat Detection
Threat intelligence plays a crucial role in Microsoft Sentinel solutions, enabling the detection of multi-stage attacks, ransomware activities, and emerging threats. Fusion technology combines Graph-powered Machine Learning and probabilistic kill chain analysis to detect anomalies and high-fidelity
2 views • 5 slides
Enhance Your Protection with MDR Cyber Security Services in Dallas
Do you wish to improve your security in Dallas against cyber threats? This is exactly where MDR Cyber Security services from Blackswan Cybersecurity can come in handy. While more complex forms of cyber threats and data breaches are becoming more popular, corporations need to acquire modern security
4 views • 8 slides
Understanding Measures of Prejudice in Research: Social Dominance Orientation, Stereotype Content Model, and More
Explore methods for measuring prejudice in research, including explicit and implicit attitude measures, Social Dominance Orientation (SDO) scale, and Symbolic (Modern) Racism Scale. Learn about the aims of research, selecting appropriate methods, and theoretical frameworks to apply.
0 views • 12 slides
Addressing The Quantum Threat: The Quantum Resistant Ledger
The Quantum Resistant Ledger (QRL) is a visionary blockchain and digital asset security solution designed to counter the emerging threat of quantum computing. With quantum technology advancing and traditional blockchains at risk, QRL offers an industrial-grade, quantum computer-resistant cryptocurre
2 views • 9 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
1 views • 51 slides
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Transforming Your School into an Inclusive STEM Learning Center
Transforming a school into an inclusive STEM learning center involves creating a conducive environment for all students to excel in STEM disciplines. By implementing project-based learning, focusing on core STEM subjects, and addressing workforce development strategies, schools can empower diverse l
0 views • 29 slides
Dickens' Positive Portrayal of the Poor in Stave 3
In Stave 3 of the novella, Charles Dickens portrays the poor in a positive light, showcasing their hard work, jovial nature, and sense of community on Christmas Day. Through various quotations and scenes, Dickens challenges the stereotype of the poor being bad, emphasizing their resilience and human
1 views • 5 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
The Curse of Expectations in Education
The belief in the S-shape curve of educational benefits leads to the harmful practice of placing all educational hopes on one child, creating a perceived poverty trap. The combination of high ambition and low expectations in elitist school systems perpetuates inequality and stereotype threat, hinder
0 views • 13 slides
Understanding Sexual Violence: What You Need to Know
Sexual violence encompasses any non-consensual sexual act or behavior that targets a person's sexual function. It goes beyond unwanted penetration and can involve various forms of sexual contact, including physical violence targeting sexual organs. Gender-based violence differs in how it targets men
0 views • 18 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
0 views • 42 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Pennsylvania School Threat Assessment Procedures and Guidance
Ongoing concerns about school safety led to legislation in 2019, requiring schools in Pennsylvania to establish threat assessment teams. This presentation provides an overview of the statute, threat levels, team responsibilities, procedures, and resources for school staff, parents, and guardians to
0 views • 25 slides
Conducting Threat Assessments Through the Atrocity Prevention Lens
This module from the GLOBAL CENTRE FOR THE RESPONSIBILITY TO PROTECT focuses on conducting threat assessments through an atrocity prevention lens. It covers risk identification, situational awareness in field settings, information collection methods, addressing vulnerabilities of women and children,
0 views • 20 slides
Bomb Threat Preparedness Guidelines for Shifa International Hospital
The Shifa International Hospital emphasizes the importance of maintaining a secure environment for employees, patients, and visitors in the event of a bomb threat. This presentation covers the types of bomb threats, steps to follow in case of a bomb threat, and provides guidance on handling telephon
0 views • 14 slides
High School Students Behavioral Threat Assessment Tabletop Exercise Analysis
Conduct a tabletop exercise analyzing the behavioral threat assessment of two high school students. Explore roles and responsibilities, exercise itinerary, goal, and purpose to enhance threat assessment team preparedness and response. Utilize simulated scenarios to simulate real-world events for opt
0 views • 23 slides
Examining Stereotype Threat in Engineering Education
Exploring the experiences of female engineering students facing stereotype threat, this critical theoretical framework study sheds light on the challenges that impact their academic journey. Through narrative inquiry methodology, the research focuses on white female students to understand how stereo
0 views • 37 slides
Cognitive Model of Stereotype Change: Three Models Explored
The Cognitive Model of Stereotype Change, as researched by Hewstone & Johnston, delves into three key models for altering stereotypical beliefs: the bookkeeping model, the conversion model, and the subtyping model. These models suggest strategies such as adding or removing features to shift stereoty
0 views • 58 slides
Unpacking Biases and Tackling ISMs in Life
We all carry biases and opinions that influence our decisions. Learning to separate bias from stereotype is crucial for making informed choices. This course delves into identifying and addressing biases to combat ageism, sexism, racism, classism, and homophobia in society.
0 views • 10 slides
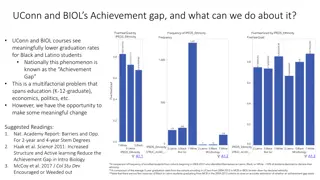
Addressing the Achievement Gap in UConn and BIOL Courses: Strategies for Inclusivity
UConn and BIOL courses show lower graduation rates for Black and Latino students, contributing to the nationwide Achievement Gap. The issue stems from various factors, including stereotype threat and a weed-out culture. Strategies such as increased structure, active learning, and creating a sense of
0 views • 6 slides
School Safety and Threat Assessment Program Overview
Fact-based Threat Assessment for Safe and Supportive School Programs involves identifying, inquiring, assessing, and managing potentially dangerous situations. It aims to distinguish between those making threats and those posing real risks, without profiling or labeling individuals. Understanding th
0 views • 20 slides
Impact of Stereotypes on Perceived Facial Threat in Women Offenders
Facial expressions play a significant role in understanding emotions, but stereotypes can influence how people perceive facial affect. This study examines how reading tabloid articles about crimes committed by dark and light-skinned women offenders affects the perceived facial threat. Using a 2x2 fa
0 views • 9 slides