Solving Sensitive Healthcare Challenges
Address the background, magnitude, proposed solution, potential impact, existing market solutions, implementation challenges, and expertise needed to solve sensitive healthcare issues effectively.
1 views • 14 slides
Data Guardianship_ Securing Sensitive Documents
The modern day digital world deals with data breaches and cyber threats, that\u2019s why the importance of secure document management in Los Angeles, cannot be overstated. Whether you\u2019re a small business owner, a healthcare professional, or an individual handling personal information, ensuring
9 views • 6 slides
Data Guardianship_ Securing Sensitive Documents
The modern day digital world deals with data breaches and cyber threats, that\u2019s why the importance of secure document management in Los Angeles, cannot be overstated. Whether you\u2019re a small business owner, a healthcare professional, or an individual handling personal information, ensuring
0 views • 6 slides
Safeguarding Canada's Research: Policy on Sensitive Technology Research and Affiliations of Concern (STRAC)
Canada's new Policy on Sensitive Technology Research and Affiliations of Concern (STRAC) aims to protect the country's research ecosystem from foreign entities posing security risks. The policy restricts funding for projects involving sensitive technology research if affiliated with military or stat
1 views • 10 slides
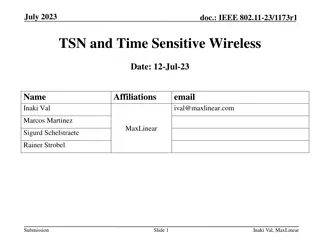
TSN and Time Sensitive Wireless
This document explores the relationship between IEEE 802.11 and Time Sensitive Networking (TSN), defining TSN in the context of 802.11 and highlighting the importance of TSN for improving packet delivery, reducing latency, and enhancing network reliability. Various features like Multi-AP, preemption
6 views • 18 slides
Mistakes to Avoid When Parenting as a Sensitive Father_
Are you a sensitive father raising a strong-willed child? While it's natural to make mistakes along the way, being aware of common pitfalls can help you navigate parenthood more effectively. Below, we are going to outline some common mistakes to steer clear of when parenting as a sensitive father, d
7 views • 6 slides
How BI Software Tools Secure Sensitive Business Information
Protecting sensitive business information is more important than ever. BI software tools play a crucial role in securing data through advanced security features such as data encryption, user access controls, real-time monitoring, audit trails, and data anonymization. These tools not only safeguard f
1 views • 6 slides
Understanding VA Privacy Issues and Sensitive Information
Explore the complex landscape of VA privacy issues, including data relationships, sensitive personal information (SPI), personally identifiable information (PII), individually identifiable information (III), and individually identifiable health information (IIHI). Learn about the roles and responsib
0 views • 29 slides
Understanding Bystander Intervention in Sensitive Situations
Learn about the role of a bystander in sensitive situations, including types of bystanders and how to intervene effectively. Explore scenarios and factors affecting intervention and non-intervention, emphasizing the importance of noticing, interpreting, feeling responsible, and possessing necessary
1 views • 20 slides
Understanding Trauma-Sensitive Care for Students During COVID-19
In this presentation by Monique Johnson, LCSW, the importance of trauma-sensitive and responsive care for students during COVID-19 is emphasized. It discusses the impact of trauma, different types of trauma youth may experience, stress reactions, and protective factors. Participants are guided to co
0 views • 17 slides
Understanding Privacy in Information Security Training
Privacy awareness training is crucial, covering topics such as the definition of privacy, importance of privacy protection, Personally Identifiable Information (PII), and Sensitive PII. Discover why privacy is vital to maintaining public trust, preventing identity theft, and complying with laws. Lea
0 views • 55 slides
Improving Low-Latency Buffer Status Reporting in IEEE 802.11
Proposal for enhancing the Buffer Status Report (BSR) mechanism in IEEE 802.11 to include timing constraints for transmitting latency-sensitive traffic. Suggestions involve adding TSPEC-based signaling and efficient mechanisms for Enhanced Traffic APs to ascertain low-latency traffic status. The cur
0 views • 12 slides
Understanding Vulnerable Situations of Migrants at International Borders
This training course focuses on migrants in vulnerable situations at international borders, discussing why special consideration is needed for their human rights protection. It covers the concept of vulnerable situations, reasons for focusing on such migrants, and the specific protection they requir
0 views • 15 slides
Understanding Electrostatic Sensitive Devices (ESDS)
Electrostatic Sensitive Devices (ESDS) are susceptible to damage caused by electrostatic discharge (ESD). This results from the transfer of electrostatic charge induced by high electrical fields. ESD can alter the characteristics of semiconductor devices, leading to malfunctions or failures in elect
0 views • 34 slides
Exploring Time-Sensitive Networking Horizons and Possibilities for Low Latency Solutions
Delve into the world of time-sensitive networking (TSN) as it offers bounded low-latency solutions for various applications. Discover TSN components, tools, and protocols such as frame replication, path control, per-stream filtering, time synchronization, and more. Gain insights from Jnos Farkas's p
2 views • 23 slides
Payment Request and Reimbursement Resources for Business Expenses
Explore a range of resources related to payment requests, reimbursements, invoices, and sensitive inventory for managing business expenses. Access training materials, forms, and guidelines on requesting reimbursements for UMBC associates, including information on purchasing sensitive equipment. Lear
0 views • 23 slides
Data Protection Incidents and Fines: Lessons Learned
Learn from real-life data protection scenarios that led to fines and breaches, such as improper data handling with USB devices, confidential files ending up in public recycling, misdirected emails of sensitive data, and unsecured mobile devices leading to theft. Understand the consequences and best
0 views • 9 slides
Safety-Sensitive Functions and Decision Making in DOT/FTA Drug and Alcohol Program Conference
Explore key topics discussed by Lori DeCoste, Michael Redington, and Felicity Shanahan at the US DOT Volpe Center FTA Drug and Alcohol Program National Conference. Learn about safety-sensitive functions, random pool testing, supervision requirements, post-accident decision making scenarios, and more
0 views • 28 slides
Ignite: Innovative Nutrition-Sensitive Agriculture Tool
Welcome to the Food Systems Nutrition-Sensitive Intervention Selection Design Tool, part of the IGNITE initiative. This tool aims to provide technical innovation in nutrition, integrating sensitivity and gender perspectives into agriculture practices. With support from experts, this tool assists in
2 views • 179 slides
Hide Content from Bots in Shopify
Implement effective content hide content from Bots in Shopify strategies on your store from accessing sensitive information. To protect sensitive data and improve site security, make use of cutting-edge bot identification and blocking strategies. Ass
1 views • 6 slides
Cost-Sensitive Loss Functions in Machine Learning
Explore the concept of cost-sensitive loss functions in machine learning, a vital aspect often overlooked by standard loss functions. Understand how underestimates and overestimates can have varying costs, impacting decision-making processes. Learn about the importance of adjusting loss functions to
3 views • 18 slides
NBCS Multi-Project Program Development Process
The Nebraska Board of Public Roads Classifications & Standards (NBCS) has adopted a process for developing a Multi-Project Program or Strategy. This involves options such as relaxation of standards, changing standards through rulemaking, and now the inclusion of a Multi-Project Program option. The p
3 views • 35 slides
Enhancing Channel Access for Latency-Sensitive Traffic in January 2022
In the documentation IEEE 802.11-21/0894r1, the focus is on improving channel access for latency-sensitive traffic through concepts like Restricted TWT (Target Wake Time). The proposal suggests methods to protect TWT Service Periods from non-TWT scheduled STAs, ensuring prioritized transmission of l
0 views • 11 slides
Detecting Sensitive Data Disclosure via Text Analysis
This article discusses techniques for detecting sensitive data disclosure, including taint analysis and bi-directional text correlation analysis. It covers existing detection methods, challenges with generic APIs, and solutions using text correlation analysis to determine data sensitiveness. Example
0 views • 34 slides
Understanding Alabama Data Breach Notification Act for County Governments
Alabama's Data Breach Notification Act requires all county governments and related entities to comply with specific security measures to protect sensitive information of residents. The law mandates prompt investigation and notification in case of a breach, defining what constitutes a breach and sens
1 views • 36 slides
Effective Trauma-Sensitive Strategies in Schools by Suzanne Savall
Suzanne Savall, an experienced elementary teacher and principal from Washington State, shares insights on implementing trauma-sensitive strategies in schools. She emphasizes building resilience, creating a safe caregiving system, and understanding the impact of trauma on the developing brain. The sc
0 views • 11 slides
Virginia Department for Aging and Rehabilitative Services Cyber Security Policies
The Virginia Department for Aging and Rehabilitative Services (DARS) mandates cyber security awareness training for individuals with access to sensitive systems, requiring completion upon access grant and annual refreshers. Compliance with Virginia Information Technology Agency policies is essential
0 views • 17 slides
Presto: Edge-based Load Balancing for Fast Datacenter Networks
Datacenter networks face challenges with network congestion affecting both throughput-sensitive elephants and latency-sensitive mice traffic. This paper discusses the problem, existing traffic load balancing schemes, and proposes an edge-based solution called Presto to address network congestion pro
0 views • 76 slides
Understanding Locality Sensitive Hashing (LSH) for Nearest Neighbor Queries
Locality Sensitive Hashing (LSH) is a technique used to efficiently find nearest neighbors in high-dimensional spaces. By grouping similar points into the same hash bucket, LSH enables fast search for nearest neighbors, overcoming the curse of dimensionality. Variants include k-nearest neighbors and
0 views • 41 slides
Coldwater Conservation Techniques for Monitoring Water Quality in Trout Habitats
Learn about the Trout Unlimited Coldwater Conservation Corps' process for assessing water quality in trout habitats, including sampling techniques, taxonomic sequencing, and categorizing pollution tolerance levels of aquatic macroinvertebrates. Discover pollution-sensitive, somewhat sensitive, and p
0 views • 40 slides
Gentle Cleanser for Maintaining Healthy and Refreshed Sensitive Skin
Atomy Aidam offers a gentle cleanser that maintains the health and freshness of sensitive skin, leaving you with a revitalizing feeling. The Oriental Herb Complex, developed with natural herbs like chamomile and rosemary, enhances skin immunity and provides a natural aroma that keeps your private ar
0 views • 4 slides
Intervention Strategies for Sensitive Situations in Group Settings
Learn about practical intervention techniques in sensitive scenarios within group dynamics. Explore the importance of creating a safe space, setting ground rules, and recognizing when to intervene. Discover how to address challenging behaviors and promote respectful communication within a group envi
0 views • 9 slides
Rapid Gender Analysis in Humanitarian Response Cycle
Rapid Gender Analysis (RGA) is a systematic process aimed at collecting and analyzing sex and age disaggregated data to understand gender dynamics in emergency situations. The process involves finding, collecting, analyzing, writing, and sharing data to inform practical recommendations for humanitar
0 views • 17 slides
Effective Communication Techniques for Avoiding Unsafe Situations
Recognize communication danger signs, prevent escalation, and communicate effectively in tense situations. Understand the basics of dynamic communication, sender-receiver dynamics, and instances where tensions arise. Prioritize safety by de-escalating agitated individuals, considering risk factors f
0 views • 31 slides
Guidelines for Preliminary Identification and Referral Mechanisms for Migrants in Vulnerable Situations
Regional guidelines emphasize the importance of providing protection to migrants in vulnerable situations while respecting their human rights. Technical support from IOM and UNHCR is crucial in identifying and referring vulnerable migrant populations. National workshops have been conducted to enhanc
0 views • 22 slides
Understanding Trauma-Sensitive Discipline Policies in Schools
Explore the concept of trauma-sensitive discipline policies in schools within the framework of VTSS TFI 1.6. Gain insights into changes in the Model Code of Conduct, identify vulnerable decision points, and incorporate trauma-sensitive approaches to respond to challenging behaviors. Embrace proactiv
0 views • 34 slides
Understanding the Risks of Sensitive Sectors in Free Trade Agreements
Explore the intricacies of sensitive sectors in Free Trade Agreements (FTAs) through an in-depth analysis of the potential dangers and benefits. Delve into the complexities of preferential tariff cuts, trade creation versus diversion, rules of origin, and the exemption of sensitive sectors. Learn ho
0 views • 27 slides
Understanding Action Situations and Outcomes in Interaction
Action Situations (AS) are instances of interacting agents producing outcomes, whether aggregate or emergent, with lasting effects. These situations can be social or ecological, involving various behaviors such as trade, decision making, conflict, and more. The outcomes of ASs have causal effects on
0 views • 5 slides
The Water Sensitive City Theory: Climate Change Adaptation Approach
The Water Sensitive City Theory explores how cities can evolve into integrated, adaptive, and climate-resilient water systems. It emphasizes restoring natural water balance, providing ecosystem services, and fostering water-sensitive communities. This approach is crucial for climate change adaptatio
0 views • 16 slides
Managing Sensitive Data in Cloud Infrastructures: Best Practices and Considerations
Explore the orchestration of cloud infrastructures for handling sensitive data, including the importance of context, legal considerations, and utilizing self-assessment tools like CAIQ. Learn about QDR's current infrastructure at Syracuse University and the challenges of storing sensitive data in th
0 views • 10 slides