BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
7 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
10 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
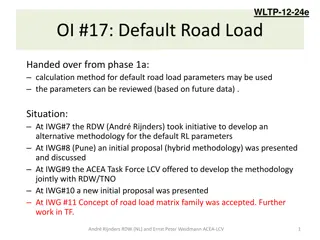
- Development of Alternative Methodology for Default Road Load Parameters in Vehicle Testing
- The initiative to develop an alternative methodology for default road load parameters in vehicle testing was led by RDW and ACEA. The process involved multiple meetings, discussions, and proposals, resulting in the acceptance of the concept of a road load matrix family. Various x-factors were adop
2 views • 22 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
2 views • 17 slides
Understanding Hammett Parameters in Organic Chemistry
The Hammett Parameters analysis, particularly the Hammett Plot, is a valuable tool in studying the electronic effects of substituents on aromatic systems. This linear free-energy relationship approach aids in optimizing reaction conditions and probing reaction mechanisms. Applications of Hammett Par
0 views • 8 slides
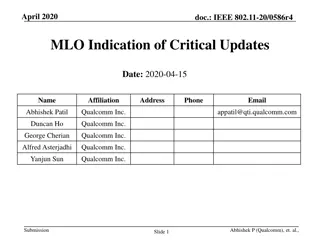
IEEE 802.11-20/0586r4 MLO Indication of Critical Updates
The document discusses the need for a mechanism in the MLO framework to enable non-AP MLDs to receive updates to operational parameters without monitoring all links. It proposes that each AP of an MLD should provide an indication of updates to another AP's operational parameters. It also outlines ho
0 views • 17 slides
Understanding Flip-Flop Timing Parameters in Digital Systems
In digital systems, flip-flop timing parameters are crucial for proper operation. Synchronous inputs must remain stable before and after the clock edge to ensure correct storage of values. Clock frequency, setup time, hold time, and propagation delay play key roles in signal integrity. By considerin
0 views • 9 slides
Building Engineering Systems Overview
Explore the standards, requirements, and parameters for building engineering systems, focusing on indoor microclimate conditions, energy efficiency, and optimal parameters for different seasons. Learn about European and Lithuanian standards, as well as specific parameters for school classrooms. Refe
0 views • 8 slides
PDSCH Demodulation Parameters & Requirements Discussion
This document covers the discussion on PDSCH demodulation parameters and requirements for UE demodulation and CSI reporting in FR2 DL 256QAM, specifically focusing on static channel mode, TDL-D channel mode, and TDL-A channel mode. The document also explores rank options, channel bandwidth, PRB allo
0 views • 9 slides
Automatic Optimization of Basis Set Parameters for Enhanced Quality
Learn how to automatically optimize the parameters that define the quality of the basis set with the Simplex code, as detailed by Alberto García Javier Junquera. This process involves compiling the Simplex code, preparing the necessary input files, creating a directory for running the optimization
0 views • 11 slides
User-Centric Parameters for Call Handling in Cellular Mobile Voice Service
The ITU Regional Standardization Forum for Africa held in Kampala, Uganda in June 2014 introduced ITU-T Recommendation E.807, focusing on the definitions and measurement methods of user-centric parameters for call handling in cellular mobile voice service. The recommendation outlines five key parame
1 views • 15 slides
Optimizing SG Filter Parameters for Power Calibration in Experimental Setup
In this investigation, the aim is to find the optimal SG filter parameters to minimize uncertainty in power calibration while avoiding overfitting. Analyzing power calibration measurements and applying SG filter techniques, the process involves comparing different parameters to enhance filter perfor
0 views • 21 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Understanding Functions in Modular Programming
Functions in modular programming allow for hierarchical decomposition of problems into smaller tasks, with interfaces defining input parameters and output. Each function operates independently, following a specific structure for headers, parameters, and return statements. Proper function prototyping
0 views • 27 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
1 views • 41 slides
Understanding Biomarkers and Maturity Parameters in Petroleum Exploration
Biomarkers and maturity parameters play crucial roles in characterizing source materials and assessing the thermal maturity of organic matter in petroleum exploration. Specific biomarkers and non-biomarker maturity parameters are utilized to determine the relative maturity of source rocks and oils.
0 views • 17 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Autonomous Detection of Vehicular Wheel Alignment Parameters
This research focuses on the autonomous detection of vehicular wheel alignment parameters conducted by Aaron Ameerali, Nadine Sangster, and Gerard Ragbir at the University of Trinidad & Tobago. The study addresses the importance of wheel alignment for proper road contact and maintenance, discussing
0 views • 19 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Understanding Water Quality Parameters and Characteristics
Water quality encompasses physical, chemical, and biological characteristics that determine its suitability for various uses. Physical parameters like turbidity, taste, odor, color, and temperature affect sensory perception. Chemical parameters such as pH, acidity, alkalinity, and hardness relate to
0 views • 26 slides
Analysis of Bunch Lengthening in CEPC for Different Design Parameters
This study explores bunch lengthening in the Circular Electron Positron Collider (CEPC) for various design parameters, analyzing a 54 km design scheme, a 61 km design scheme, and a 100 km design scheme. The analysis includes the theoretical framework used, equations for bunch lengthening, and conclu
1 views • 15 slides
Magnetic Field Calculation and Parameters for Injection/Extraction Kicker CR
This document provides detailed information on the injection/extraction kicker CR used by Aleksey Kasaev at the BINP-FAIR-GSI workshop in 2014. It includes main parameters of the kicker, magnetic field calculations, ferrite parameters, magnetic field distribution, and time cycles of operation. Addit
0 views • 11 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
1 views • 68 slides
Optimizing Continuous Quantum Control with Variable Parameters
The research delves into solving quantum optimal control problems with versatile system parameters through robust and analytical approaches. It explores optimizing figures of merit in quantum systems with varying Hamiltonian and pulse parameters, showcasing solutions for single-qubit and two-qubit s
0 views • 18 slides
Understanding the Importance of Calibration in Hydrological Modeling
Hydrological models require calibration to adjust parameters for better representation of real-world processes, as they are conceptual and parameters are not physically measurable. Calibration involves manual trial and error or automatic optimization algorithms to improve model accuracy. Objective f
0 views • 12 slides
Understanding Parameters, Statistics, and Statistical Estimation in Statistics
In statistics, we differentiate between parameters and statistics, where parameters describe populations and statistics describe samples. Statistical estimation involves drawing conclusions about populations based on sample data. The Law of Large Numbers explains the relationship between sample stat
1 views • 12 slides
CEPC Main Ring Double Ring Scheme Lattice Design
Lattice design and parameters for the double ring scheme of the Circular Electron Positron Collider (CEPC) main ring discussed at the CEPC AP meeting in January 2016. The outline covers the CEPC parameters for C=100km, including the lattice design and geometry for different regions. Details on energ
0 views • 14 slides
Channel Generation Process for IEEE 802.11aj (45GHz) Based on Channel Measurement
This presentation by Haiming Wang and team from SEU/CWPAN discusses the process of channel realization and generation in the 45 GHz bandwidth. It covers the generation of the channel impulse response, modeling of parameters, statistical measurements, and future work related to the 802.11ad standard.
0 views • 27 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
1 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
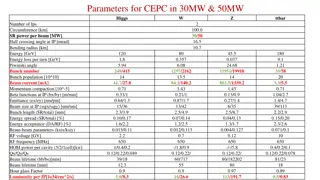
Parameters and Results for CEPC in 30MW & 50MW
Parameters and results for the Circular Electron Positron Collider (CEPC) operating at 30MW and 50MW including information on the Higgs, W, Z, and ttbar processes. The data covers various aspects such as the number of IPs, circumference, power per beam, bending radius, energy, beam properties, beam-
0 views • 7 slides
New Assumptions for Achieving Chosen Ciphertext Security in Cryptography
This research work focuses on presenting new assumptions for achieving chosen ciphertext security in public key encryption. The study aims to clarify the necessary and sufficient assumptions to realize general cryptographic primitives, particularly focusing on CCA secure PKE and KEM. The ultimate go
0 views • 27 slides
Understanding Transport Layer Parameters and Examples
This content delves into the important parameters associated with the transport layer, such as the number of lanes per converter device, the number of converters per device, and the number of octets per frame. It provides examples of how these parameters are configured in different scenarios, showca
0 views • 8 slides