BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
Organizational Structure Overview of HSE and Security Functions
This detailed content provides an overview of the organizational structure of the HSE (Health, Safety, and Environment) and Security functions within the corporation. It includes charts and roles of key personnel such as the Head of HSE and Security, Corporate Health Advisor, Regional Security Manag
3 views • 4 slides
Livestock Marketing Functions and Classification
Livestock marketing involves various functions such as exchange, physical supply, facilitative functions like grading, transportation, storage, and more. These functions are classified into primary, secondary, and tertiary functions based on their roles. Assembling, processing, distribution, and equ
3 views • 23 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Domain and Range of Functions
Understanding functions involves exploring concepts such as domain, range, and algebraic inputs. This content covers topics like constructing functions, common functions like quadratic and trigonometric, and solving functions based on given domain and range. It also provides practice questions to te
1 views • 21 slides
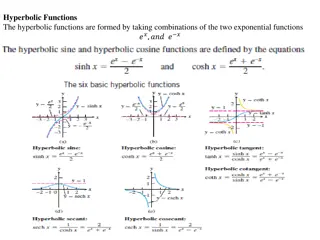
Understanding Hyperbolic Functions and Their Inverses
This content delves into the world of hyperbolic functions, discussing their formation from exponential functions, identities, derivatives, and inverse hyperbolic functions. The text explores crucial concepts such as hyperbolic trigonometric identities, derivatives of hyperbolic functions, and integ
0 views • 9 slides
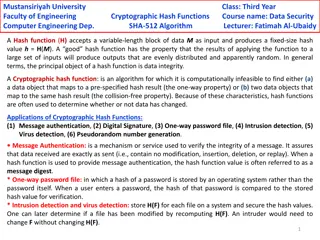
Cryptographic Hash Functions in Data Security: Mustansiriyah University Course Overview
Cryptographic hash functions play a crucial role in ensuring data integrity and security. This course at Mustansiriyah University's Faculty of Engineering covers the SHA-512 algorithm and its applications in various fields such as message authentication, digital signatures, and intrusion detection.
0 views • 6 slides
Understanding Functions in Python: Basics and Usage
In this lecture on functions in Python, the focus is on the basics of defining and using functions. The session covers the formal definition of functions, parameters, local and global scopes of variables, return values, and pass-by-value concept. It emphasizes the importance of proper indentation in
1 views • 28 slides
Understanding Functions: Tables, Graphs, and Formulas Based on Functions, Data, and Models
Explore the world of functions through tables, graphs, and formulas in this presentation based on the book "Functions, Data, and Models" by S.P. Gordon and F.S. Gordon. Learn how functions in the real world work, understand the relationship between variables, and see different representations of fun
0 views • 29 slides
Understanding SQL Functions for Database Queries
SQL functions are essential elements in performing actions and obtaining results in a database query. They come in two main types: scalar functions and aggregate functions. Scalar functions operate on single values, while aggregate functions operate on sets of data. Examples of SQL functions include
0 views • 14 slides
Understanding Basis Functions and Hemodynamic Response Functions in fMRI Analysis
This content discusses the use of basis functions, parametric modulation, and correlated regressors in the first-level analysis of fMRI data processing. It delves into the concept of temporal basis functions for modeling complex functions of interest, such as the canonical hemodynamic response funct
1 views • 26 slides
Understanding Functions in Coding with Minecraft
Functions in coding are self-contained sets of instructions that perform specific tasks within a computer program. They allow for code reuse and save time by writing instructions once as a function and calling it whenever needed. This content covers the purpose of functions, how they save time when
0 views • 30 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Understanding Composition of Functions in Mathematics
Learn how to perform operations with functions, find composite functions, and iterate functions using real numbers. Explore the composition of functions through examples and understand the domain of composite functions. Enhance your mathematical skills by mastering operations like addition, subtract
0 views • 10 slides
Understanding Functions in C Programming
Functions play a vital role in C programming by enabling the execution of specific tasks. They can be pre-defined or user-defined, offering flexibility and efficiency in code organization and execution. Pre-defined functions are already available in C libraries, while user-defined functions are cust
0 views • 46 slides
Understanding Composite and Inverse Functions
Learn about composite functions, inverse functions, and how to find their compositions and inverses through examples and step-by-step explanations. Explore the concept of forming composite functions, verifying inverse functions, and finding the inverse of a function using interchange and solving met
0 views • 15 slides
Introduction to Defining Functions in Python Programming
This chapter introduces the concept of defining functions in Python programming. It covers the importance of dividing programs into sets of cooperating functions, defining new functions in Python, understanding function calls and parameter passing, and reducing code duplication through the use of fu
0 views • 78 slides
Understanding Functions in Computer Science I for Majors Lecture 10
Expanding on the importance of functions in programming, this lecture delves into dividing code into smaller, specific pieces, defining functions in Python, understanding function calls and parameter passing, and using functions to enhance code modularity. Key topics covered include control structur
0 views • 62 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Advanced Security Concepts in SNARGs Using iO and Lossy Functions
Explore the latest research on Adaptive and Selective Soundness in Succinct Non-interactive Argument of Knowledge (SNARGs), presenting theorems and the inclusion of subexponentially secure techniques like indistinguishability obfuscation, one-way functions, and very lossy functions. Discover the pot
0 views • 20 slides
Understanding Housing Demand Theory in Urban Economics
Explore the nuances of housing demand theory in urban economics, covering topics such as alternative utility functions, exponential density functions, maximizing bid functions, and comparative statics. Delve into Stone-Geary and CES utility functions, their implications on demand functions, and the
0 views • 35 slides
Understanding Functions and Graphing in Mathematics
Functions and graphing play a crucial role in quantitative and qualitative reasoning. We explore the concept of points on a graph, coordinates, relations, functions, and ways to express functions. Utilizing visual aids and analogies, we delve into the importance of coordinates, the distinction betwe
0 views • 10 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
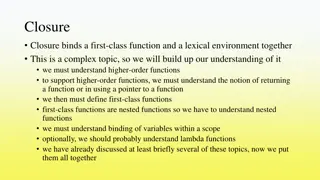
Understanding Closures, Lambda Functions, and Higher-Order Functions in Programming
In programming, closures bind functions and lexical environments, while lambda functions are nameless and used by higher-order functions. Higher-order functions operate by applying other functions, such as map and fold functions. Example implementations in LISP demonstrate how these concepts are uti
1 views • 16 slides
Introduction to Python Functions: Overview and Usage
In this module, we delve into Python functions, exploring common built-in functions and how to create custom functions. We learn the properties of functions, how to coordinate multiple functions, and concepts of modularization. Discover the essence of functions in Python programming through practica
0 views • 17 slides
Safeguarding National Security in EU Asylum Law: A Legal Analysis
The recast Qualification Directive allows Member States in the EU to restrict access to international protection on security grounds, including safeguarding national security. This article explores the limits imposed by national security concerns on accessing international protection in EU countries
0 views • 12 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Understanding Functions in C Programming
Functions play a crucial role in C programming, allowing for modularity and reusability of code. This content covers the basics of functions, creating custom functions, passing arguments, returning values, and the anatomy of a C function. Learn about defining functions, passing arguments effectively
0 views • 24 slides