Types Cyber Attacks: Cyber Security Training Workshop
Join our Cyber Security Training Workshop to learn about different types of cyber attacks such as social engineering attacks, DDoS attacks, malware attacks, MitM attacks, APTs, and password attacks. Enhance your knowledge and skills in cyber security.
15 views • 45 slides
Adversarial Machine Learning
Evasion attacks on black-box machine learning models, including query-based attacks, transfer-based attacks, and zero queries attacks. Explore various attack methods and their effectiveness against different defenses.
21 views • 60 slides
Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
2 views • 46 slides
Understanding Malicious Attacks, Threats, and Vulnerabilities in IT Security
Malicious attacks, threats, and vulnerabilities in IT systems pose significant risks and damages. This chapter explores the types of attacks, tools used, security breaches, and measures to protect against cyber threats. Learn how security professionals safeguard organizations from malicious attacks
0 views • 24 slides
Principles of Cyber Security
Threat actors prioritize targeting networks to exploit vulnerabilities, leading to various attacks such as interception, DNS attacks, and MITM attacks. MITM attacks involve eavesdropping on communications or impersonating parties, with techniques like session replay to steal credentials. Implementin
0 views • 7 slides
Managing Covid-19 Cyber and Data Protection Risks
Exploring the risks and challenges related to cyber attacks and data protection amidst the Covid-19 pandemic. The agenda covers an overview of cyber-attacks, recent developments, protections against cyber attacks, data protection concerns during lockdown, compliance steps, and employee rights issues
1 views • 35 slides
Mitigation of DMA-based Rowhammer Attacks on ARM
Practical strategies are presented in "GuardION: Practical Mitigation of DMA-based Rowhammer Attacks on ARM" to defend against Rowhammer attacks on ARM architecture. The paper discusses Rowhammer defenses, RAMPAGE attacks on Android OS, and introduces GuardION as a lightweight mitigation approach. I
0 views • 48 slides
Cybersecurity Challenges: Attacks on Web Applications and Cost of Security Breaches
In the realm of cybersecurity, attacks on web applications pose a significant threat with 78% of attacks targeting applications. The consequences of these attacks are immense, with projected costs reaching $6 trillion annually by 2021. Notable breaches in recent years highlight the urgency for robus
8 views • 23 slides
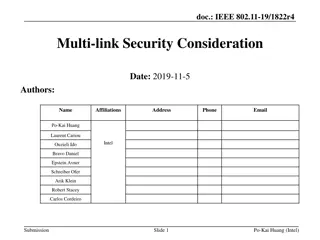
IEEE 802.11-19/1822r4 Multi-link Security Consideration
This document discusses the security considerations related to multi-link frameworks in IEEE 802.11-19/1822r4. It covers topics such as the use of different keys for different links, key generation methods, and potential replay attacks across links. The focus is on enhancing security in multi-link s
0 views • 16 slides
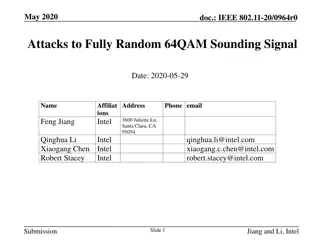
Attacks on Fully Random 64QAM Sounding Signal in IEEE 802.11-20/0964r0
Presentation by Intel demonstrates vulnerabilities in fully random QPSK and 64QAM sounding signals in IEEE 802.11-20/0964r0. Proposed attack methods, including Viterbi equalizer attacks, and solutions such as Secure LTF mechanism and windowed FFT are discussed to enhance security in ranging. The pre
0 views • 31 slides
Understanding Denial-of-Service Attacks and Defense Strategies
Denial-of-Service attacks pose a serious threat where attackers flood networks with traffic, leading to system crashes and slowdowns. Explore the impact, expected results, and various categories of DoS attacks such as bandwidth attacks, protocol exceptions, and logic attacks. Learn how to defend aga
0 views • 61 slides
Understanding Network Denial of Service (DoS) Attacks
Network Denial of Service (DoS) attacks aim to disrupt services by overwhelming them with traffic. These attacks can occur at various layers of the network stack and exploit weaknesses to achieve their goal. Amplification attacks, such as the Smurf attack and DNS Amplification attack, can significan
2 views • 52 slides
Preventing Active Timing Attacks in Low-Latency Anonymous Communication
This research addresses the vulnerabilities of onion routing to timing attacks and proposes solutions to prevent active timing attacks, focusing on low-latency anonymous communication systems. Various problems related to timing attacks in onion routing are analyzed, including the role of adversaries
0 views • 52 slides
Understanding Adversarial Machine Learning Attacks
Adversarial Machine Learning (AML) involves attacks on machine learning models by manipulating input data to deceive the model into making incorrect predictions. This includes creating adversarial examples, understanding attack algorithms, distance metrics, and optimization problems like L-BFGS. Var
0 views • 88 slides
Understanding Control Hijacking Attacks in Software Systems
Control hijacking attacks, such as buffer overflows and format string vulnerabilities, allow attackers to take over a target machine by manipulating application control flow. Knowledge of C functions, system calls, CPU, and OS used is crucial for executing these attacks successfully. This summary pr
1 views • 55 slides
Understanding Control Hijacking Attacks and Defenses
Control hijacking attacks pose a significant threat by allowing malicious actors to manipulate data and control flow within a system. This article explores common attack methods like stack smashing and heap spraying, along with defenses such as fixing bugs, implementing platform defenses, and markin
1 views • 36 slides
Understanding BGP and DNS Worms in Network Security
Border Gateway Protocol (BGP) is crucial for network communication, allowing autonomous systems to exchange routing information. BGP works by announcing network ownership and directing traffic efficiently. However, BGP Blackhole attacks pose a threat, where malicious entities reroute traffic to disr
0 views • 37 slides
Strategies to Protect School Systems from Cyber Attacks
Schools are increasingly becoming targets of cyber attacks, making cybersecurity measures crucial. The article discusses the importance of responding to cyber attacks, creating incident response plans, and being vigilant against interception attacks. It outlines the steps to detect, document, and mi
0 views • 21 slides
Understanding Heap Overflow Attacks
A heap is a collection of variable-size memory chunks managed by the program. Heap overflow attacks occur when malicious actors corrupt heap memory, potentially allowing them to overwrite data and execute arbitrary code. This poses a significant security risk. The process involves manipulating heap
2 views • 19 slides
Active Response Mechanism for IaaS Cloud Security
Stepping-stone attacks in IaaS clouds pose a new threat where attackers compromise vulnerable VMs to launch attacks against external hosts. This research explores the necessity of self-protection mechanisms for IaaS providers, emphasizing active response to detect and stop outgoing attacks at edge f
0 views • 24 slides
Understanding Data Security and Privacy: An Overview of k-Anonymity, l-Diversity, t-Closeness, and Reconstruction Attacks
Delve into the realm of data security and privacy, exploring concepts such as k-Anonymity, l-Diversity, t-Closeness, and Reconstruction Attacks. Learn about the importance of privacy concerns, privacy-preserving data sharing, real threats of linking attacks, and specific instances like the GIC Incid
0 views • 44 slides
Cache-Based Attack and Defense on ARM Platform - Doctoral Dissertation Thesis Defense
Recent research efforts have focused on securing ARM platforms due to their prevalence in the market. The study delves into cache-based security threats and defenses on ARM architecture, emphasizing the risks posed by side-channel attacks on the Last-Level Cache. It discusses the effectiveness of si
0 views • 44 slides
Security Issues in Parallel and Distributed Computing - Side Channel Attacks and Defenses
Explore various security threats in parallel and distributed computing, focusing on side channel attacks and defenses. Learn about microarchitecture, cache hierarchy, popular attacks, defense mechanisms, and more. Discover how hardware vulnerabilities can lead to the compromise of sensitive data and
1 views • 30 slides
Understanding Spectre and Meltdown Security Vulnerabilities
Spectre and Meltdown are two critical security vulnerabilities that exploit microarchitectural features to gain unauthorized access to memory. These vulnerabilities enable attackers to read memory that should be inaccessible, targeting branch prediction and exception handling mechanisms. Side channe
0 views • 19 slides
Automated Signature Extraction for High Volume Attacks in Cybersecurity
This research delves into automated signature extraction for high-volume attacks in cybersecurity, specifically focusing on defending against Distributed Denial of Service (DDoS) attacks. The study discusses the challenges posed by sophisticated attackers using botnets and zero-day attacks, emphasiz
0 views • 37 slides
Combined Cyber and Physical Attacks on Maritime Transportation System
Attacks on the maritime transportation system involve a combination of cyber and physical methods, posing significant threats to global commerce. Cyber vulnerabilities, such as hacking security cameras or spreading fake news, can lead to physical intrusions and disruptions. More sophisticated attack
0 views • 22 slides
Targeted Deanonymization via the Cache Side Channel: Attacks and Defenses
This presentation by Abdusamatov Somon explores targeted deanonymization through cache side-channel attacks, focusing on leaky resource attacks and cache-based side-channel attacks. It discusses the motivation behind these attacks, methods employed, potential defenses, and the evaluation of such att
0 views • 16 slides
Understanding Network Security Vulnerabilities and Attacks
Explore the world of network security vulnerabilities and attacks, including Denial-of-Service (DoS) and Distributed-Denial-of-Service (D-DoS), security flaws in the TCP/IP protocol suite, ICMP attacks, routing attacks, and TCP attacks. Learn about common security vulnerabilities such as address spo
0 views • 36 slides
Understanding TCP Sequence Numbers and Attacks
Explore the fundamental concepts of TCP sequence numbers and inference attacks, along with the design, implementation, and impact analysis of TCP attacks. Delve into the significance of TCP fields, the three-way handshake process, as well as sequence and acknowledgment numbers to gain a comprehensiv
0 views • 35 slides
Understanding Network Interference in CS590B/690B Lecture
Delve into the realm of network interference through the CS590B/690B lecture with Phillipa Gill at UMass Amherst. Explore topics such as Internet routing, timing attacks, BGP hijacks, Tor network functionality, relay selection, collusion scenarios, use of guards, web site fingerprinting attacks, tra
0 views • 11 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Transitioning to BGP Security: Incentives and Challenges
Explore the strategies and incentives for transitioning to BGP security in internet routing, including the use of S*BGP to attract traffic and mitigate interception attacks. Learn about RPKI as a key infrastructure and the need for additional security measures beyond RPKI. Discover how S*BGP can hel
0 views • 31 slides
Machine Learning for Cybersecurity Challenges: Addressing Adversarial Attacks and Interpretable Models
In the realm of cybersecurity, the perpetual battle between security analysts and adversaries intensifies with the increasing complexity of cyber attacks. Machine learning (ML) is increasingly utilized to combat these challenges, but vulnerable to adversarial attacks. Investigating defenses against
0 views • 41 slides
Understanding Homeland Security in the United States
Homeland security in the United States encompasses measures aimed at preventing terrorist attacks, reducing vulnerability to terrorism, and aiding in recovery from attacks. Key aspects include the Homeland Security Act of 2002 which established the Department of Homeland Security and the focus on ho
0 views • 13 slides
Understanding Universally Composable Security: A Tutorial by Ran Canetti
This tutorial by Ran Canetti explores the concept of Universally Composable Security (UC) framework, aiming to elucidate its rationale and extend composability analysis beyond cryptography. The event covers topics like background, detailed framework workings, capturing attacks, introducing projects,
0 views • 69 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding DDoS Attacks: Simulation, Analysis & Defense
Delve into the world of Distributed Denial of Service (DDoS) attacks with this comprehensive study covering the architecture, advantages, bot installation phases, attack methods, defenses, and simulation. Learn about the detrimental impact of DDoS attacks on servers, their multi-tiered structure, an
0 views • 20 slides
Understanding Cross-Site Scripting (XSS) Attacks
Learn about the dangers of Cross-Site Scripting (XSS) attacks, including Reflected and Persistent XSS types. This malicious practice allows attackers to inject harmful code into websites, potentially compromising user data and security measures. Discover how XSS attacks work, their impact on online
0 views • 38 slides
Overview of DoS and DDoS Attacks in Cybersecurity
This content provides an in-depth overview of Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks in cybersecurity. It covers the types of attacks, including volumetric, reflected, and stealthy, along with detailed explanations and examples. Additionally, it discusses how DoS at
0 views • 8 slides
Understanding Network-based Attacks in the Cloud: The Dark Menace
The presentation delves into the escalating threat landscape within cloud computing, highlighting the absence of comprehensive research. Key questions relate to the volume, nature, and actors behind cloud attacks, urging advancements in detection and compliance. The pioneering study characterizes di
0 views • 32 slides