Consumer Protection Act 2019
The Consumer Protection Act 2019 and its aim to protect consumers' rights. Explore a comparative study of the 1986 and 2019 acts, the establishment of a Central Consumer Protection Authority, simplified dispute resolution mechanisms, and the liability of businesses for defective products or services
9 views • 18 slides
Protection Analysis using the PAF
In this session, participants will learn how to utilize the Protection Analysis Framework (PAF) and its tools to conduct effective protection analysis. The session covers an overview of PAF, understanding its pillars, and analyzing data to comprehend essential protection concepts. Key points include
5 views • 48 slides
The Digital Personal Data Protection Act 2023
The Digital Personal Data Protection Act of 2023 aims to regulate the processing of digital personal data while balancing individuals' right to data protection and lawful data processing. It covers various aspects such as obligations of data fiduciaries, rights of data principals, and the establishm
3 views • 28 slides
Governance and Managerial Leadership of Formal Social Protection in Africa: Insights from Cameroon's National Social Insurance Fund (CNPS)
This presentation delves into the governance and managerial leadership of formal social protection in Africa, focusing on Cameroon's CNPS system. It discusses the institutional evolution of social protection, the challenges faced by bureaucratic and political stakeholders, and the roles of various s
0 views • 8 slides
Advancements in Chemical Mechanisms for Air Quality Management
Daniel Jacob and team have been enhancing chemical mechanisms in the GEOS-Chem model to support US air quality management. Ongoing work includes developing new mechanisms for aromatic VOCs, tropospheric halogens, mercury redox, adaptive mechanism reduction, machine learning applications, and unifica
0 views • 19 slides
Securing BIOS: Flash Protection Mechanisms and Best Practices
Explore advanced x86 BIOS security mechanisms like Global Flash Protection, Global BIOS Write Protection, and SMM-derived Write Protection to prevent unauthorized writing to the BIOS. Discover how BIOS vendors can enhance security configurations to thwart attackers effectively.
2 views • 38 slides
Comprehensive Training on Protection from Sexual Exploitation and Abuse
This training program covers the history, key concepts, zero tolerance principles, roles and responsibilities, risk factors, consequences, community-based complaints mechanisms, human resources, protection of whistleblowers, and mandatory reporting related to protection from sexual exploitation and
1 views • 38 slides
Understanding Plasmid Partitioning Mechanisms in Bacteria
The stable maintenance of low-copy-number plasmids in bacteria relies on partition mechanisms that ensure proper positioning during cell division. Different from high-copy-number plasmids, which rely on random diffusion, low-copy-number plasmids require regulated partitioning mechanisms to prevent d
0 views • 14 slides
Eye Protection Training for Workplace Safety
Understand the importance of proper eye protection at work, including identifying at-risk job functions, selecting the right PPE, and knowing responsibilities for employees and employers. Training covers when PPE is necessary, how to use, maintain, and dispose of it properly, and the need for retrai
2 views • 28 slides
Financial Consumer Protection Initiatives in Eastern and Southern Africa
Institute of Eastern and Southern Africa emphasizes the importance of financial literacy and consumer protection post the global financial crisis. Financial consumer protection ensures fair treatment, transparency, and effective recourse mechanisms for clients. It complements financial literacy and
3 views • 17 slides
Understanding the General Data Protection Regulation (GDPR) and Data Protection Bill
The General Data Protection Regulation (GDPR) is a set of rules aimed at safeguarding individuals' personal data and privacy rights, with key changes from the previous Data Protection Act 1998. The GDPR introduces transparency, consent requirements, enhanced individual rights, breach notifications,
3 views • 40 slides
Understanding Shuttle Picking Mechanisms in Weaving
Shuttle picking mechanisms play a crucial role in propelling the weft carrying element to maintain the required trajectory and velocity in fabric weaving. Two common mechanisms are cone over-pick and cone under-pick, each offering unique adjustments for strength and timing. The cone over-pick involv
0 views • 14 slides
Understanding Protection Mainstreaming in Humanitarian Aid
Protection Mainstreaming in humanitarian aid involves incorporating protection principles to ensure meaningful access, safety, and dignity for affected populations. Key elements include prioritizing safety and dignity, ensuring meaningful access without barriers, and establishing accountability mech
0 views • 36 slides
Understanding Operating System Protection Principles
Explore the goals, principles, and implementation of protection in computer systems, including access matrix, domain structure, and capability-based systems. Learn how protection domains and access control are used to specify resource access, and delve into the concept of least privilege and dynamic
4 views • 21 slides
Importance of Consumer Protection in Economic Activities
Consumption is the cornerstone of economic activity, encompassing daily purchases and services. Over time, consumer protection rights have evolved to safeguard consumers. The transition from "Caveat Emptor" to "Caveat Venditor" reflects a paradigm shift in buyer-seller responsibilities. Internationa
1 views • 13 slides
Groundskeeping Safety and Personal Protective Equipment Training
This presentation covers essential information on groundskeeping safety and the proper use of personal protective equipment (PPE). Topics include head protection, eye/face protection, hearing protection, respiratory protection, hand protection, body protection, foot protection, as well as guidance o
0 views • 35 slides
Rethinking Conditionalities in Social Protection Programs
The images and descriptions provided delve into the concept of conditionalities within social protection programs, highlighting how they can mask poor service quality, create opportunities for coercion, and strip away the protection and safety nets meant to support individuals. The narrative advocat
0 views • 8 slides
Understanding Consumer Protection Remedies and Enforcement Mechanisms
Explore the key aspects of consumer protection remedies and enforcement mechanisms, including their purposes, types, effectiveness, and application against wrongdoers like fraudsters. Learn about injunctive relief, monetary remedies, compliance monitoring, and more to ensure consumer rights are safe
1 views • 18 slides
Understanding the Inversion of Mechanisms in Kinematics
Inversion of Mechanisms in Kinematics involves measuring absolute and relative motions in stationary and moving frames, respectively. By fixing different links in a kinematic chain, we can obtain various mechanisms. This process does not alter relative motions but may significantly change absolute m
0 views • 78 slides
Location Privacy Protection Strategies: A Comprehensive Overview
This study delves into optimal strategies to safeguard location privacy against localization attacks in the realm of location-based services. Discussing the shortcomings of anonymization and obfuscation as standalone defenses, it explores the challenges and pitfalls in designing effective protection
0 views • 26 slides
The Importance of Social Protection and the African Union in Africa
Social protection is recognized as a fundamental human right, and efforts within the African Union have been made to promote social protection programs to combat poverty in Africa. The growth of social protection initiatives since the Ouagadougou declaration of 2004 has led to increased awareness an
0 views • 12 slides
Safeguarding Focal Point Training: Enhancing Reporting and Response Mechanisms
This training module focuses on empowering Safeguarding Focal Points (SFPs) to understand and implement community-based feedback and response mechanisms, effectively handle safeguarding complaints, document barriers to reporting, address data protection issues, and ensure inclusive and confidential
0 views • 18 slides
Importance of Fall Protection Systems in Workplace Safety
Fall protection systems play a crucial role in preventing injuries and fatalities caused by falls at the workplace. Understanding the anatomy of a fall, statistics on fall-related incidents, and the various philosophies of fall protection can help companies plan and implement effective fall protecti
0 views • 50 slides
Empowering Consumer Protection and Redress in South Africa
The National Consumer Tribunal in South Africa plays a crucial role in enforcing consumer protection laws and ensuring redress for consumers. The presentation outlines the genesis of the current consumer protection framework in South Africa, highlighting the need for empowering mechanisms and struct
0 views • 20 slides
Understanding Authentication Mechanisms and Security Vulnerabilities
Authentication lies at the core of application security, serving as the primary defense against malicious attacks. This article explores various authentication technologies, including HTML forms-based authentication, multi-factor mechanisms, client SSL certificates, and more. It delves into common d
0 views • 70 slides
Overview of UNIX System Protection
UNIX System Protection focuses on ensuring security and access control mechanisms within the UNIX operating system. Developed in 1969 by Dennis Ritchie and Ken Thompson at AT&T Bell Labs, UNIX features design elements like a portable API, protection rings, kernel processes, and a trusted computing b
0 views • 12 slides
Ensuring Effective Whistleblower Protection and Supportive Environments
Establishing supportive environments and robust mechanisms for protecting whistleblowers is crucial to overcoming challenges such as fear of retaliation and legal liabilities. Key aspects include creating safe reporting channels, safeguarding confidentiality, and implementing transparent reactions t
0 views • 14 slides
Challenges and Solutions in Consumer Protection within Monopoly Environments
Consumer protection in the context of monopoly environments presents unique challenges and requires specific actions. Professor Stephen Littlechild highlights the importance of competition as the most effective means of protecting consumers. In situations where there is a single supplier, such as in
0 views • 9 slides
Improving Consumer Protection in Ghana: Insights from the Sixth Annual African Dialogue Consumer Protection Conference
The Sixth Annual African Dialogue Consumer Protection Conference held in Lilongwe, Malawi in September 2014 shed light on the challenges faced by Ghana's consumer protection policies. Irene Aborchie-Nyahe, a legal consultant, highlighted the gaps in Ghana's legislative framework, lack of effective i
0 views • 14 slides
Overview of Human Rights Monitoring Mechanisms
Human rights conventions under the United Nations and regional systems have established monitoring mechanisms to ensure compliance. These mechanisms include treaty-based and non-treaty-based approaches, with treaty bodies overseeing the implementation of legally binding instruments. Reporting proced
0 views • 23 slides
Improved Truthful Mechanisms for Subadditive Combinatorial Auctions
This research paper discusses strategies to maximize welfare in combinatorial auctions. It explores mechanisms for handling strategic bidders with private valuations, aiming to design truthful and optimal welfare mechanisms while considering polytime constraints. The study presents advancements in a
0 views • 19 slides
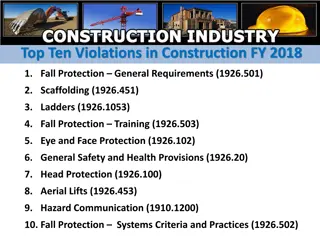
Top Ten Construction Violations FY 2018 Overview
The top ten violations in construction for fiscal year 2018 are related to fall protection, scaffolding, ladders, safety training, eye and face protection, general safety provisions, head protection, aerial lifts, hazard communication, and fall protection systems criteria and practices. The violatio
0 views • 11 slides
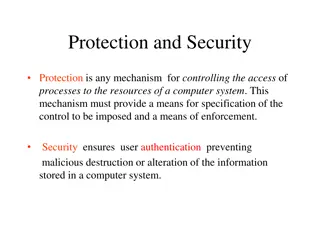
Understanding Computer System Protection and Security
Mechanisms like protection and security ensure controlled access to a computer system's resources and prevent malicious activities. Protection involves defining access control levels through models, policies, and mechanisms. Security focuses on user authentication to safeguard stored information. Di
0 views • 25 slides
Understanding Carnegie Mellon's Protection and Security Concepts
Carnegie Mellon University emphasizes the importance of protection and security in operating systems. Protection involves preventing unauthorized access by users, while security focuses on external threats and authenticating system users. The goals of protection include preventing access violations
0 views • 37 slides
Understanding Data Protection Regulations and Definitions
Learn about the roles of Data Protection Officers (DPOs), the Data Protection Act (DPA) of 2004, key elements of the act, definitions of personal data, examples of personal data categories, and sensitive personal data classifications. Explore how the DPO enforces privacy rights and safeguards person
0 views • 33 slides
Understanding Biomarkers and Toxicity Mechanisms: Overview of Mechanisms in Targeting Biological Macromolecules
This overview delves into different categorizations of mechanisms of action (MoA) based on target molecules, interaction types, and steric specificity. It explores non-specific and specific mechanisms, along with possible categorizations involving membrane toxicity, reactive toxicity, and species-sp
0 views • 8 slides
Understanding Coping Skills and Defense Mechanisms
Coping mechanisms and defense mechanisms are strategies individuals use to manage stress and emotions. Coping mechanisms help people adjust to difficult events while maintaining emotional well-being, whereas defense mechanisms operate at an unconscious level and can change internal psychological sta
0 views • 18 slides
Defense Mechanisms in Psychology: Understanding Repression, Displacement, Intellectualization, Rationalization
Defense mechanisms play a crucial role in how individuals cope with stress and anxiety. This text delves into key defense mechanisms such as repression, displacement, intellectualization, and rationalization. These mechanisms help individuals manage unacceptable thoughts, feelings, and impulses by r
0 views • 11 slides
Workshop on Data Protection: Mauritius Police Force Presentation
The workshop on data protection by Mrs. D. Madhub, Data Protection Commissioner, held on May 15, 2019, focused on the Data Protection Act, the Data Protection Office, definitions, functions, powers, and obligations related to data protection, covering areas such as processing of personal data and ri
0 views • 46 slides
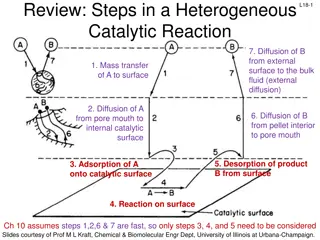
Understanding Steps in Heterogeneous Catalytic Reactions and Adsorption Mechanisms
This review discusses the steps involved in a heterogeneous catalytic reaction, focusing on diffusion, mass transfer, adsorption, and desorption processes. It details the site balance, surface reaction mechanisms, and desorption steps, providing insights into the complexities of catalytic processes.
0 views • 17 slides