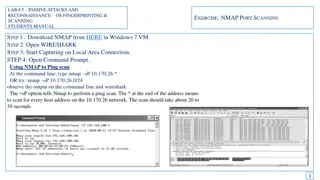
Passive Attacks and Reconnaissance using NMAP for Network Scanning
Learn how to use NMAP for passive attacks and reconnaissance through port scanning techniques like ping scan, TCP port scan, and stealth scan. Understand how to analyze the output in Wireshark to identify open ports and version numbers on target systems.
2 views • 7 slides
Network Traffic Analysis with Wireshark: Examples and Techniques
Explore the world of network traffic analysis using Wireshark through examples and practical techniques. Learn how tools like Nmap and Wireshark can be used for network scanning and detecting suspicious activities. Dive into real examples, including identifying attackers through HTTP web traffic ana
1 views • 10 slides
ethical hacker learning
Ethics hackers use a range of specialized tools to test and analyze systems. These include software for scanning networks, testing web applications, and sniffing out vulnerabilities. Some popular tools you might encounter include Nmap, Metasploit, an
1 views • 1 slides
Comprehensive Guide to Hacking Techniques & Intrusion Detection
Dive into the world of hacking techniques, intrusion detection, and network protocols with expert Ali Al-Shemery. Learn about host discovery, port scanning, packet crafting, and more using tools like Nmap. Explore the importance of network protocols like TCP, UDP, ICMP, and ARP. Discover the art of
0 views • 50 slides
Network Sniffing and Protocol Analysis Overview
Learn about network sniffing, a process of capturing and interpreting network traffic, its analogies like wiretapping, environmental considerations, and protocol analysis. Understand the risks, authorization requirements, and tools like Wireshark. Explore examples of Nmap Port Scans and monitoring w
0 views • 30 slides
Weak Keys Detection in Network Devices
TLS and SSH rely on RSA and DSA for security, but weaknesses in random number generation can lead to widespread weak keys among hosts on the Internet. This paper uncovers the prevalence of repeated keys and easily inferred private keys, emphasizing the importance of entropy pools in key generation.
0 views • 28 slides