Revisiting the Spymasters: The Double Agent Problem
Delve into the intriguing world of spymaster tactics with a focus on the double agent problem and the feasibility of secure multiparty computation protocols. Explore motivations, related works, and groundbreaking results in this complex domain.
3 views • 20 slides
Computability: Exploring Theoretical Limits of Computation
Delve into computability theory, focusing on what is computable and the limits of computation. Explore concepts like Rice's Theorem, the Halting Problem, and classes of expressiveness in computability theory, such as combinational logic, finite-state machines, pushdown automata, and Turing machines.
5 views • 43 slides
Overview of Distributed Systems: Characteristics, Classification, Computation, Communication, and Fault Models
Characterizing Distributed Systems: Multiple autonomous computers with CPUs, memory, storage, and I/O paths, interconnected geographically, shared state, global invariants. Classifying Distributed Systems: Based on synchrony, communication medium, fault models like crash and Byzantine failures. Comp
9 views • 126 slides
Computation of Machine Hour Rate: Understanding MHR and Overhead Rates
Computation of Machine Hour Rate (MHR) involves determining the overhead cost of running a machine for one hour. The process includes dividing overheads into fixed and variable categories, calculating fixed overhead hourly rates, computing variable overhead rates, and summing up both for the final M
4 views • 18 slides
Enhanced Security in Multiparty Computation
Explore the improved black-box constructions of composable secure computation, focusing on definitions, objectives, and the formalization basics of multiparty computation (MPC). Learn about the motivating security aspects in MPC and the real/ideal paradigm. Discover how MPC security involves compari
1 views • 68 slides
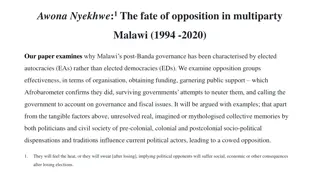
The Fate of Opposition in Multiparty Malawi: 1994-2020
This paper explores why Malawi's governance post-Banda has been dominated by elected autocracies rather than democracies. It delves into the effectiveness of opposition groups in terms of organization, funding, public support, and resilience against government attempts to suppress them. The influenc
0 views • 6 slides
CNF-FSS and Its Applications: PKC 2022 March 08
Explore the Background, Applications, and Summary of CNF-FSS, focusing on Function Secret Sharing, Distributed Point Function, CNF Key-Sharing, and more. Learn about the efficiency of multiparty sharing and 1-out-of-3 CNF-FSS constructions for certain classes of functions. Discover how CNF Key-Shari
1 views • 33 slides
Understanding Numerical Methods and Errors in Computation
Delve into the world of numerical methods through the guidance of Dr. M. Mohamed Surputheen. Explore topics such as solving algebraic and transcendental equations, simultaneous linear algebraic equations, interpolation, numerical integration, and solving ordinary differential equations. Learn about
0 views • 130 slides
Trust Income Computation and Application Guidelines
Learn about income computation of trusts using ITR-5 vs. ITR-7, types of institutions, components of income, application of income, and important guidelines including amendments by FA2022 for charitable and religious trusts.
0 views • 47 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Secure Multiparty Computation for Department of Education Data Sharing
This report discusses the use of Secure Multiparty Computation (SMC) to enable sharing of sensitive Department of Education data across organizational boundaries. The application of SMC allows for joint computation while keeping individual data encrypted, ensuring privacy and security within the Nat
0 views • 15 slides
Advancements in Active Secure Multiparty Computation (MPC)
Delve into the realm of secure multiparty computation under 1-bit leakage, exploring the intersection of DP algorithms, MPC, and the utilization of leakage for enhanced performance. Discover the overhead implications of achieving active security, as well as the evolution of secure computation protoc
0 views • 43 slides
Enhancing Computation in Physics Education Using Cognitive Approaches
Utilizing evidence-based methods, this study explores incorporating computation in physics courses, focusing on instructional design, student knowledge states, and preparation for future learning. It discusses common conceptual difficulties in quantum mechanics and proposes cognitive theory-based st
0 views • 24 slides
Secure Multiparty Computation: Enhancing Privacy in Data Sharing
Secure multiparty computation (SMC) enables parties with private inputs to compute joint functions without revealing individual data, ensuring privacy and correctness. This involves computations on encrypted data using techniques like homomorphic encryption for scenarios like e-voting. SMC serves as
2 views • 27 slides
Evolution of the American Political Landscape: A Historical Overview
Explore the development of the multiparty political system in the United States through the origins of the Democratic and Republican parties, tracing back to historical figures like Thomas Jefferson, James Madison, and Abraham Lincoln. Dive into the ideological spectrum, party histories, presidentia
0 views • 32 slides
Understanding Sequence Alignment and Scoring Matrices
In this content, we dive into the fundamentals of sequence alignment, Opt score computation, reconstructing alignments, local alignments, affine gap costs, space-saving measures, and scoring matrices for DNA and protein sequences. We explore the Smith-Waterman algorithm (SW) for local sequence align
0 views • 26 slides
COMET: Code Offload by Migrating Execution - OSDI'12 Summary
The research paper discusses COMET, a system for transparently offloading computation from mobile devices to network resources to improve performance. It outlines the goals of COMET, its design, and evaluation, focusing on distributed shared memory and bridging computation disparity through offloadi
0 views • 31 slides
Exploring Challenges and Opportunities in Processing-in-Memory Architecture
PIM technology aims to enhance performance by moving computation closer to memory, improving bandwidth, latency, and energy efficiency. Despite initial setbacks, new strategies focus on cost-effectiveness, programming models, and overcoming implementation challenges. A new direction proposes intuiti
0 views • 43 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Enhancing Mobile-Cloud Computing with Autonomous Agents Framework
Autonomous Agents-based Mobile-Cloud Computing (MCC) refers to moving computing tasks to powerful centralized platforms in the cloud, offering advantages like extending battery life and dynamic resource provisioning. However, an inflexible split of computation between mobile and cloud platforms lead
0 views • 22 slides
Enhancing Multi-Party Computation Efficiency Through ORAM Techniques
Explore the realm of efficient random access in multi-party computation through the reevaluation of classic schemes and the introduction of new approaches. Discover the potential of ORAM in improving performance and reducing costs in various computational tasks, such as secure multi-party computatio
0 views • 22 slides
Enhancing I/O Performance on SMT Processors in Cloud Environments
Improving I/O performance and efficiency on Simultaneous Multi-Threading (SMT) processors in virtualized clouds is crucial for maximizing system throughput and resource utilization. The vSMT-IO approach focuses on efficiently scheduling I/O workloads on SMT CPUs by making them "dormant" on hardware
0 views • 31 slides
Advancements in Multi-Key Homomorphic Encryption Using TFHE
Revolutionary research has led to the development of Multi-Key Homomorphic Encryption (MKHE) from TFHE, enabling secure and efficient computations on encrypted data. This technology offers advantages such as dynamic operability, stronger security, and minimized interaction, making it an ideal soluti
0 views • 20 slides
Exploring Secure Computation in the Age of Information
Welcome to Secure Computation Lecture 1 by Arpita Patra. The course covers evaluation policies, projects, and references in the realm of secure computation. The content delves into the significance of information security across various sectors, emphasizing the importance of safeguarding sensitive d
0 views • 36 slides
Secure Two-Party Computation and Basic Secret-Sharing Concepts
In today's lecture of "Foundations of Cryptography," the focus is on secure two-party and multi-party computation, emphasizing semi-honest security where Alice and Bob must compute without revealing more than necessary. Concepts such as real-world vs. ideal-world scenarios, the existence of PPT simu
0 views • 27 slides
Linear Communication in Secure Multiparty Computation for Efficient and Fast Processing
The research focuses on achieving perfectly secure multiparty computation (MPC) with linear communication and constant expected time. It explores efficient approaches using a broadcast-hybrid model and P2P communication, aiming to balance speed and efficiency in MPC. The study highlights the importa
0 views • 23 slides
Secure Computation Challenges and Solutions in Data Mining
Exploring the intersection of secure computation and data mining, this content uncovers key challenges such as improving algorithms, converting programs for secure computation, and addressing parallelizability issues. It highlights the importance of cryptography in ensuring data privacy and presents
0 views • 30 slides
Covert Computation: Ensuring Undetectable Engagement
Covert computation aims to conceal the fact that computation is occurring and hide engagement in certain tasks like secure computation, authenticated key exchange, and more. By making messages indistinguishable and utilizing steganographic channels, it becomes possible to keep the activities covert
0 views • 16 slides
Enhancing Online Service Security through Symbolic Transaction Certification
The research discusses securing multiparty online services through the certification of symbolic transactions, addressing logic flaws and the importance of program verification. The Certification of Symbolic Transaction (CST) approach is presented as an effective way to verify system-wide properties
0 views • 22 slides
Overview of Turing Machines: Introduction, Tape, and Computation
Turing Machines are fundamental in the theory of computation, capable of recognizing all computable languages. They consist of a Finite State Machine combined with an infinite tape. The tape is initialized with input on the left end, and a TM's computation can either halt by entering special accept
0 views • 29 slides
Computation for Real Estate Sector in Bangalore Branch of ICAI
Practical overview of GST computation for real estate transactions in Bangalore, with details on old rates with ITC and new rate regime effective from April 1, 2019. The content discusses different transactions, conditions for new rates without ITC, and provides insights on the 80:20 computation met
0 views • 39 slides
Fides: A System for Verifiable Computation Using Smart Contracts
Fides presents a system for verifiable computation using smart contracts, focusing on blockchain basics, Ethereum, smart contracts, and outsourcing computation. It explores key components of blockchain, Ethereum's decentralized computing platform, properties of smart contracts, and the concept of ve
0 views • 25 slides
Insights into Secure Computation with Minimal Interaction
This paper revisits the concept of secure computation with minimal interaction, focusing on the challenges and possibilities of achieving secure multiparty computation in 2 rounds. Specifically exploring scenarios with 3 and 4 parties, the study delves into the reasons for choosing n=3, n=4, and t=1
0 views • 23 slides
Overview of Income Computation and Disclosure Standards (ICDS)
The Income-tax Act, 1961 introduced Income Computation and Disclosure Standards (ICDS) to be followed by certain assesses for computation of income. ICDS applies to taxpayers using the mercantile system of accounting from the Assessment Year 2016-17 onwards. Non-compliance with ICDS can lead to Best
0 views • 49 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Blackbox Verifiable Computation Scheme Overview
This summarized content discusses the concept of blackbox verifiable computation, focusing on the challenges faced by clients and servers, the role of helper oracles, positive results utilizing homomorphic encryption, and background information on Random Self Reducible (RSR) functions. The protocol
0 views • 20 slides
Parallel Computation for Matrix Multiplication
Matrix multiplication is a fundamental operation with diverse applications across scientific research. Parallel computation for matrix multiplication involves distributing the computational workload over multiple processors, improving efficiency. Different algorithms have been developed for multiply
0 views • 36 slides
Quantum Public-Key Encryption with Tamper-Resilient Public Keys
Explore the concept of Quantum Public-Key Encryption with Tamper-Resilient Public Keys from One-Way Functions. Learn about the essentials of Public-key Encryption (PKE), computational assumptions, and the implications of realizing PKE from OWFs in the quantum world. Delve into topics like statistica
0 views • 20 slides
Overview of Asynchronous MPC with Linear Communication and Optimal Resilience
Explore the concepts of Asynchronous Multiparty Computation (MPC) with Linear Communication and Optimal Resilience, discussing the model, motivation, and differences between synchronous and asynchronous protocols. The goal is to ensure correctness and privacy in a setting where parties may be corrup
0 views • 72 slides
Advanced Techniques in Multi-Party Computation
Explore cutting-edge methods in Multi-Party Computation (MPC), including leveraging Fully Homomorphic Encryption (FHE) for minimal round complexity, constructing MPC directly via FHE techniques, and simplifying multi-key FHE constructions for efficient decryption. Learn about key concepts such as di
0 views • 17 slides