Cryptocurrencies and Blockchain Technologies
Join the CS251 course at Stanford University to learn about cryptocurrencies and blockchain technologies. Access course videos on Canvas, participate in discussions on Edstem, and complete homework on Gradescope. Explore the first project on Merkle trees available on the course website.
4 views • 46 slides
Efficient Key Recovery Attack on SIDH
Efficient key recovery attack on Supersingular Isogeny Diffie-Hellman (SIDH) protocol. It explores the vulnerability of the protocol and proposes a concrete solution. The attack leverages auxiliary points to solve the isogeny problem and reveals instances of the common secret key.
6 views • 22 slides
Batching Techniques for Accumulators: Applications to IOPs and Blockchains
This presentation discusses batching techniques for accumulators in the context of IOPs and blockchains. It covers challenges with UTXO sets, Merkle trees, and RSA accumulators, proposing solutions and improvements. The content explores problems with Merkle trees, benefits of RSA accumulators, and e
1 views • 27 slides
Blockchain Computer of Ethereum
Explore the intricate workings of Ethereum's blockchain computer, from the order-execute structure to persistent state storage mechanisms. Learn about account information, smart contracts, Merkle Patricia Trie, and the role of OPCODEs in Ethereum Virtual Machine. Delve into the creation of contract
0 views • 50 slides
Introduction to Public Key Cryptography
Public key cryptography, exemplified by algorithms like Diffie-Hellman and RSA, revolutionizes secure communication by allowing users to encrypt messages with public keys known to all and decrypt them with private keys known only to the intended recipient. This advanced encryption method ensures sec
1 views • 44 slides
Diffie-Hellman Problems in Cryptography
Exploring Diffie-Hellman assumptions and problems including Computational Diffie-Hellman (CDH) and Decisional Diffie-Hellman (DDH). Discusses the difficulty of solving the DDH problem compared to CDH and discrete logarithm assumptions. Covers examples and implications of these cryptographic challeng
4 views • 6 slides
Diffie-Hellman Key Exchange Algorithm
The Diffie-Hellman key exchange algorithm, a pioneering public-key cryptography method introduced by Diffie and Hellman in 1976, enables secure key exchange between two users to facilitate subsequent message encryption. The algorithm relies on the complexity of computing discrete logarithms and invo
2 views • 24 slides
Public-Key Cryptography and Its Applications
Public-Key Cryptography revolutionized secure communication by introducing the concept of using separate keys for encryption and decryption. Initially explored by researchers like Diffie, Hellman, and Merkle in the 70s, it addressed key distribution challenges faced by symmetric cryptography. This m
0 views • 34 slides
Dynamo: Amazon's Highly Available Key-value Store Summary
Dynamo is a distributed storage system designed by Amazon to provide scale, simplicity, key-value storage, and high availability. It aims to meet Service Level Agreements (SLAs) by offering simple query models, ACID properties, and efficient latency handling. The system sacrifices strong consistency
0 views • 19 slides
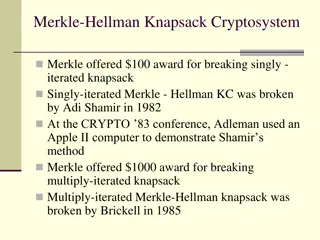
Overview of Knapsack Cryptosystems and Related Problems
The Merkle-Hellman knapsack cryptosystem is a cryptographic system that was initially proposed by Merkle, and later iterated versions were both broken by Shamir and Brickell in the early 1980s and 1985, respectively. This system is related to the classical knapsack problem, subset-sum problem, and e
0 views • 18 slides
Overview of Public-Key Cryptography and Knapsack Problem in Cryptology
This lecture delves into the realm of public-key cryptography, including the Knapsack one-way function and the Merkle-Hellman Crypto System. It explores historical perspectives, the concepts of OWFs, Elliptic Curve Cryptography, and introduces new algebra using additive groups over Elliptic Curves.
1 views • 16 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
2 views • 12 slides
Communication Lower Bounds of Key-Agreement Protocols
Key-agreement protocols play a vital role in secure communication between parties. This document explores lower bounds of key-agreement protocols through density increment arguments, idealization of symmetric primitives, Merkle puzzles, and the impact of communication bits between Alice and Bob. Var
1 views • 10 slides
Challenges in Key Exchange Protocols
Key exchange protocols play a crucial role in ensuring secure communication. This content explores the challenges faced in designing robust key exchange mechanisms, from vulnerabilities in existing protocols like Diffie-Hellman to the complexity of implementing authentication. Despite decades of res
2 views • 51 slides
Quantum Computing and Its Impact on Cryptography
Quantum computing utilizes the principles of quantum mechanics to process information exponentially faster than classical computers. This advancement poses a significant threat to current cryptographic systems, especially those reliant on factors like RSA and Diffie-Hellman key exchange. If large-sc
1 views • 25 slides
Key Exchange and Public-Key Cryptography Overview
Explore the challenges of key management, the use of trusted third parties in generating shared keys, the limitations of toy protocols in secure key exchange, and the evolution of public-key cryptography techniques like Merkle Puzzles, Diffie-Hellman, and RSA. Learn how to achieve secure key exchang
1 views • 36 slides
Exploration of Cryptography and Secure Communication Methods
Delve into the concepts of cryptography, data hiding, and secure communication methods such as Diffie-Hellman key exchange. Discover how Bob safely sends a ring to Alice, the use of Caesar cipher method, and the importance of mathematical principles in ensuring secure communication protocols. Learn
1 views • 22 slides
Cryptographic Protocols and Key Exchange
This content delves into the world of cryptographic protocols, discussing the importance of security measures such as symmetric cryptography, hash functions, and public-key cryptography. It explores the field's various studies, goals, Diffie-Hellman key exchange, and the significance of key size in
1 views • 28 slides
Overview of Public Key Encryption Schemes by Dan Boneh
This content provides insights into public key encryption schemes such as Diffie-Hellman and ElGamal, as presented by cryptography expert Dan Boneh. Topics covered include key exchange, secure email, encryption applications, constructions, and a review of the Diffie-Hellman protocol. The material de
0 views • 41 slides
Comprehensive Overview of Encryption Techniques and Algorithms
Explore the world of encryption with insights into symmetric and public key encryption, certificate authorities, secure sockets layer, substitution ciphers, block ciphers, AES, and public key cryptography. Delve into the intricacies of encryption keys and algorithms, including the AES process, Diffi
0 views • 31 slides
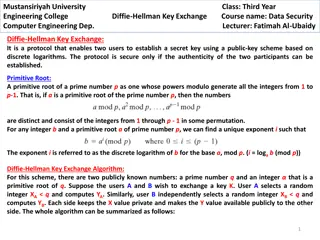
Diffie-Hellman Key Exchange Protocol in Data Security
Protocol enabling secure key establishment between users using public-key scheme based on discrete logarithms. Learn about primitive roots, algorithm steps, a key exchange example, and a scenario with an attacker. Explore how Diffie-Hellman ensures secure communication in computer engineering.
0 views • 6 slides
Decisional Diffie-Hellman Problem on Elliptic Curves
In this study, the decisional Diffie-Hellman problem is explored in the context of class group actions on elliptic curves. The formalization and applications of the problem are discussed along with potential solutions and implications. The research delves into distinguishing distributions and the th
0 views • 21 slides
Hash-Based Signatures
This content discusses the security requirements of hash-based signatures, particularly focusing on XMSS (eXtended Merkle Signature Scheme). It highlights the minimal security requirements of digital signature schemes and the key aspects of XMSS security, such as resistance to chosen message attacks
0 views • 6 slides
Public Key Cryptography and Modern Cryptology
Delve into the world of cryptology with a focus on public key cryptography, as pioneered by Whitfield Diffie, Martin Hellman, and James Ellis. Explore the revolutionary concept of using public and private keys for secure communication without the need for a prior key exchange. Uncover the insights a
0 views • 38 slides
Introduction to Cryptology
Public-key cryptography revolutionized secure communication by eliminating the need for exchanging secret keys, as seen through the breakthroughs of Shannon and Diffie-Hellman. This lecture outlines the significance, principles, and challenges within this cryptographic system, paving the way for mod
0 views • 19 slides
Cryptography in Bitcoin and Blockchain
The early concepts of cryptographic hash functions, digital signatures, and innovations like Merkle Trees laid the foundation for blockchain technology. Explore the journey from David Chaum's DigiCash to Satoshi Nakamoto's Bitcoin whitepaper and the Genesis Block, leading to the evolution beyond Bit
0 views • 33 slides
Understanding BLE Security in EECS 582 Spring 2015 Course
Explore various aspects of Bluetooth Low Energy (BLE) security in the EECS 582 course from Spring 2015, covering topics such as attacks, improvements, authentication, privacy, and more. Dive into the layers of BLE technology and learn about link layer connections, encryption methods, and the initiat
0 views • 16 slides
Secure In-Band Wireless Pairing: Innovative Solutions for MITM Attacks
Explore the evolution of secure wireless pairing techniques without the need for passwords through the Tamper-Evident Pairing (TEP) protocol. Learn about protecting against MITM attacks and the advancements in in-band pairing security. Discover how Trusting un-tampered wireless messages and detectin
0 views • 40 slides
Solving Data Availability and Security Issues in Blockchain Systems
Explore how erasure coding and Merkle trees can enhance data availability and security in blockchain systems. Learn about data availability attacks, Merkle tree proofs, and efficient mechanisms for verifying data integrity without downloading all messages.
0 views • 26 slides
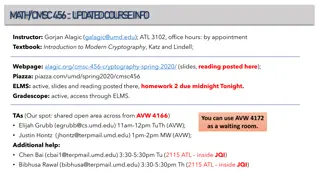
Cryptography Course Information and Merkle-Damgard Transform Overview
Explore details for CMSC 456 Cryptography course by Gorjan Alagic, covering Merkle-Damgard transform, random oracle models, and collision-resistant hashing. Learn about hash functions and their applications in building secure cryptographic protocols.
0 views • 39 slides
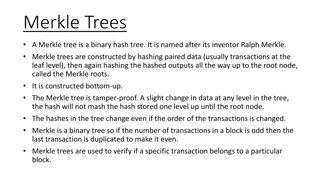
Understanding Decentralized Blockchain Concepts
Explore the core concepts of decentralized blockchain technology, including Proof of Work, Nakamoto Consensus, Merkle Trees, and Distributed Consensus. Learn about decentralized identity, ownership, transfer, variable difficulty mining, and the security analysis of blockchain systems.
0 views • 21 slides
Understanding Merkle Trees, Distributed Consensus, and Blockchain Applications
Dive into the world of Merkle Trees, Distributed Consensus, and Blockchain Applications. Learn how Merkle Trees ensure data integrity, how consensus is achieved in a decentralized system, and the life of blockchain applications. Explore the concepts of public and private blockchains in this informat
0 views • 11 slides
Secure Signatures for IoT: Hash-Based Schemes and OTS Overview
Dive into long-term secure signatures for the IoT, exploring hash-based signature schemes, Lamport-Diffie OTS, one-time signatures, chain-based OTS, Merkle's signature scheme, and more. Discover fast signing algorithms, small keys, and sequential signature verification methods.
0 views • 13 slides
Applications of Hash Functions in Cryptography and Beyond
Explore the ubiquitous nature of hash functions and their applications in collision-resistance, fingerprinting, outsourced storage, random oracles, and more. Learn how Merkle trees can efficiently solve the outsourcing problem. Delve into the Random Oracle (RO) model's implications for collision res
0 views • 22 slides
Understanding Cryptography and Hash Functions in Data Security
Explore the concepts of cryptography, random oracle model, hash functions, Merkle trees, fingerprinting, and outsourced storage for secure data protection. Learn how to leverage these techniques to safeguard information in an untrusted environment.
0 views • 32 slides
Update on Hash-based Signatures and Trapdoor Identification
Explore the latest advancements in hash-based signatures and trapdoor identification schemes, including post-quantum security measures and intractability assumptions. Dive into topics such as Merkle's hash-based signatures and Winternitz-OTS, understanding the functions and generations behind these
0 views • 40 slides
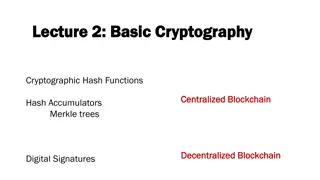
Understanding Cryptographic Hash Functions and Blockchain Technology
Delve into the realm of cryptographic hash functions, blockchain technology, digital signatures, and more. Explore the concepts of centralization versus decentralization, hash accumulators, Merkle trees, and the significance of hash pointers in data structures like blockchain.
0 views • 18 slides
Mitigating Multi-Target Attacks in Hash-Based Signatures
Explore advanced techniques for enhancing security in hash-based signature schemes to address multi-target attacks and ensure post-quantum security. Delve into trapdoor identification schemes, Merkle's hash-based signatures, and minimizing security assumptions.
0 views • 25 slides
Understanding Asymmetric Encryption: Diffie-Hellman Key Exchange Explained
Explore the world of asymmetric encryption through the captivating concept of the Diffie-Hellman key exchange protocol. Delve into the intricacies of public-key cryptography, secret key agreement, and the mathematical foundations that make this encryption method secure and reliable.
0 views • 29 slides
Practical Challenges and Innovations in Hash-based Signature Schemes
Explore the latest advancements in hash-based signature schemes, focusing on practical challenges, security requirements, and innovative approaches such as Merkle trees and XMSS. Industry experts invite valuable insights for handling state efficiently. Stay informed about post-quantum security and r
0 views • 21 slides