FST Research
Approach, sustain, and breach the knowledge frontier through the Researcher Development Framework. Explore different research clusters and embrace passion, creativity, and picking a research area. Stay informed with continuous literature flow and meta-analyses.
0 views • 21 slides
Protecting Accounts & Devices: Stay Secure Online
Secure accounts & devices, manage breaches, prevent attacks, recover lost data. What to do in case of security breach and steps to safeguard personal information and devices.
1 views • 18 slides
The Church's Response to Poverty in Contemporary Times
Explore the multifaceted approach the Church should take towards poverty, focusing on unity, honor for all members, understanding causes, and aligning with God's calling. Embrace the vocation of the Church to repair breach, restore streets, and rebuild ruins, guided by faith and prayer for common go
0 views • 11 slides
A CLINICAL NEGLIGENCE OVERVIEW
Clinical negligence claims require claimants to establish duty of care, breach of duty, causation, and more. Healthcare workers owe patients a duty of care to avoid physical injuries. The law on advice has evolved with cases like Montgomery, emphasizing the importance of informed consent. Recent leg
1 views • 19 slides
Security Breach: Detecting and Exploiting SQL Injection in Contact Groups
Suspect a potential SQL injection in the macros used in Contact groups? Learn how to identify and exploit it through blind SQL injection techniques. Follow step-by-step instructions to execute a payload that alters user data and gain unauthorized access. Stay vigilant and proactively safeguard your
3 views • 27 slides
Privacy Breach Management Guide by Health PEI
Understanding, Preventing, and Managing Privacy Breaches in Healthcare: Learn about what constitutes a privacy breach, how to prevent breaches, steps to determine and manage breaches effectively, including containment, investigation, and notification processes.
0 views • 10 slides
Amended Convention on Physical Protection of Nuclear Material Tabling in Parliament
The Amended Convention on Physical Protection of Nuclear Material (CPPNM) is being tabled for acceptance and ratification in Parliament on 05 September 2023. The purpose is to enhance physical protection measures for nuclear material, especially in the face of increased security concerns post the 9/
3 views • 18 slides
Intrigue and Rebellion in Mrichchhakatika
The play "Mrichchhakatika" unfolds a tale of love, betrayal, and societal norms through its main plot involving Charudatta and Vasantasena, as well as a subplot featuring Madanika and Sharvilaka. Acts III and IV depict the making of a breach as characters navigate themes of freedom, theft, and defia
0 views • 7 slides
Cyber Data Breach Review_ A Comprehensive Insight with LDM Global in the USA
In today's digital landscape, cyber data breaches pose significant threats to organizations of all sizes. A cyber data breach can result in severe financial losses, reputational damage, and legal ramifications. To navigate these challenges effectively, companies turn to expert services like those pr
1 views • 13 slides
Proposed Amendments for Hazardous Material Release Reporting Regulations
Amendments to the hazardous material release reporting regulations include consolidating definitions, adding new definitions, changing the administering agency, updating citations, and altering notification timeframes. The amendments aim to enhance emergency response and improve reporting procedures
1 views • 18 slides
Data Breach Exercise: Responding to a School District Breach
This tabletop exercise simulates a data breach within a school district, putting participants in critical decision-making roles to react and respond effectively. Recommendations include anticipating roles needed, preparing for the unexpected, and considering communication strategies. The background
1 views • 31 slides
2,400 Patients Potentially Exposed to Infectious Diseases at Providence, Legacy
Legacy Health announced it is sending letters to 221 patients at providence who might have been affected by this breach.
0 views • 2 slides
Understanding Sub-Letting in Rental Properties
Assured tenancies come with a statutory prohibition on sub-letting under the Housing Act 1988. If a tenant sub-lets, they breach their contract with the landlord, potentially leading to possession orders. The sub-tenants have a legal status, but the contractual relationship for paying rent lies with
0 views • 18 slides
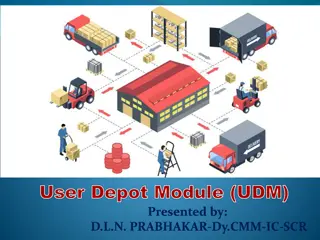
Understanding User Depot Module (UDM) in Material Management
Genesis UDM was developed by CRIS to computerize material management at consignees' end, integrating with iMMS and IREPS. UDM revolutionizes the supply chain of materials management through digitalization, optimizing asset maintenance, expenditure control, and promoting a shift to digital working en
0 views • 19 slides
Postsecondary Data Breach Exercise: Prepare for the Unexpected!
This tabletop exercise simulates a data breach scenario within a complex organization, engaging participants to make critical decisions and respond effectively. Teams will work together to uncover the extent of the breach and devise a response plan. Consider various roles needed in your organization
0 views • 31 slides
Understanding the Domino's Data Breach Incident and Its Implications
The recent data breach at Domino's India has raised concerns over consumer data protection. With personal information of millions compromised, the need for a uniform Data Protection Law is emphasized. Users are advised to take precautions, while the accountability of companies under existing regulat
0 views • 9 slides
Contempt in the Family Jurisdiction with Respect to Breach of Orders
The concept of contempt in the family jurisdiction regarding the breach of court orders other than those for financial relief is crucial for upholding the due administration of justice. Courts have the authority to punish for contempt to safeguard their processes and ensure compliance with their ord
0 views • 17 slides
Understanding Material Cost Variances in Commerce
Material cost variances play a crucial role in analyzing the differences between actual and standard costs of direct materials used in production. From material cost variances to material price, usage, and mix variances, each aspect sheds light on different aspects of cost control and efficiency in
0 views • 12 slides
Essential Steps for Personal Data Breach Management
Detect, identify, and respond effectively to personal data breaches by containing the breach, assessing risks, notifying relevant authorities and affected individuals, and implementing measures to prevent future occurrences. Debunk common myths surrounding breach reporting and focus on mitigating ne
0 views • 5 slides
Material Control in Cost Accounting
Material control in cost accounting involves maintaining a systematic control over the purchasing, storing, and utilization of materials to minimize costs while ensuring uninterrupted production. It encompasses aspects such as accounting and operational controls, aiming to balance the efficient use
0 views • 9 slides
Strategies for Developing a National Nuclear Forensics Library
Nuclear forensics involves comparing data from unknown sources with known material characteristics to determine their origin. Establishing a national nuclear forensics library is crucial for identifying nuclear materials and promoting international cooperation in investigations. Key elements include
0 views • 18 slides
Understanding Breach of Confidence and Privacy Rights in English Law
English law does not provide a specific right to privacy, but breach of confidence laws offer protection against unauthorized disclosure of private information. While there is no overarching invasion of privacy tort, legal controls exist to balance freedom of expression with respect for individual p
0 views • 18 slides
Understanding Professional Duties in Accountancy
This informative content discusses various aspects of professional duties in accountancy, such as negligence, breach of duty of care, causation, asset valuation, and ethics. It covers topics like duty of care, foreseeability test, breach of duty standards, causation principles, and the accountants'
1 views • 10 slides
Understanding Rescission and Its Legal Implications
Rescission is a legal remedy where a court cancels a contract and orders exchanged items to be returned. It can be invoked in cases of material breach, impracticability, frustration, mistake, or misrepresentation. This article explores the concept of rescission, its criteria under common law and UCC
0 views • 4 slides
Can You Afford a Data Breach? Understanding the Risks and Consequences
Explore the potential dangers and implications of a data breach through insightful presentations and visuals by Laura Middleton and James Hayward. Learn about the value of personal data, human errors, and organizational measures to mitigate risks. Stay informed and subscribe to the e-newsletter for
0 views • 10 slides
Effective Method to Protect Web Servers Against Breach Attacks
Abdusamatov Somon presents an effective method called HTB to protect web servers against breach attacks, focusing on secure computation and mitigation. The research addresses side-channel attacks based on compression and the CRIME BREACH issue, providing insights into implementing the breach attack
1 views • 13 slides
Exploring Material Science and Engineering Fundamentals
Delve into the world of material science and engineering to understand the core concepts, including the definition of materials, the role of material scientists, and the different types of materials such as metals, ceramics, polymers, and composites. Explore the length scales in material science, fr
0 views • 28 slides
Privacy Breach Response and Reporting under the Health Information Act
Understanding privacy breaches under the Health Information Act (HIA) is crucial for organizations dealing with health data. This document outlines what constitutes a breach, mandatory notification requirements, factors to consider in determining risk of harm, and potential offences and penalties fo
0 views • 21 slides
Understanding Alabama Data Breach Notification Act for County Governments
Alabama's Data Breach Notification Act requires all county governments and related entities to comply with specific security measures to protect sensitive information of residents. The law mandates prompt investigation and notification in case of a breach, defining what constitutes a breach and sens
1 views • 36 slides
Legal Case Study: Compensation for Breach of Promise
In this legal case study, we examine different scenarios involving breach of promise and the resulting compensation. The study covers promises kept, losses caused by breaches, and the corresponding awards for individuals involved. Various situations are analyzed, from promises kept without mitigatio
0 views • 6 slides
NHS Sussex Conflicts of Interest Breach Register Summary May 2024
NHS Sussex manages conflicts of interest breaches by recording and publishing them on their website. Breaches are documented with details of the nature of the breach and actions taken. In May 2024, no breaches were reported. Previous months had breaches due to late declarations of interest. Staff we
0 views • 5 slides
Data Breach Occurrence at Illinois Department of Transportation
A data breach at the Illinois Department of Transportation exposed social security numbers and employee identification numbers of all current and former employees. The breach was discovered on April 14, 2022, after being visible from April 6, 2022. The breached file was located on an internal IDOT w
0 views • 11 slides
Material Design: Combining Classic Design Principles with Technological Innovation
Material Design is a design language that combines traditional design principles with the possibilities offered by technology and science. It emphasizes visual language, classic design elements, and innovation to create delightful user experiences. The Material Metaphor, Imagery, Typography, Color,
0 views • 34 slides
Legal Dispute Between Walker & Co. and Harrison: Contract Breach Analysis
In the legal dispute between Walker & Co. and Harrison regarding a breached contract over a billboard, Harrison claimed that Walker failed to maintain the sign, justifying contract termination. However, Walker's actions to remedy the breach and the criteria for material breach were evaluated by the
0 views • 9 slides
Understanding the Role and Liabilities of Promoters in Company Formation
Promotion in the formation of a company involves the initial groundwork by a promoter, who assembles funds, property, and managerial expertise. Promoters have a fiduciary duty towards the company and original shareholders, necessitating full disclosure of all material facts. They can be held liable
0 views • 20 slides
Exploring Dynamic Mechanical Analysis (DMA) for Material Characterization
Dynamic Mechanical Analysis (DMA) is a valuable technique for studying viscoelastic behavior in materials, particularly polymers. By applying sinusoidal stress and measuring strain, DMA helps determine modulus and locate the glass transition temperature. The method involves varying temperature or st
0 views • 8 slides
Understanding Breach of Confidence and Privacy Rights in Legal Context
The legal landscape regarding breach of confidence and privacy rights, especially in the context of English law and the European Convention on Human Rights, is complex and ever-evolving. While English law traditionally does not recognize a right to privacy, recent developments and landmark cases hav
0 views • 18 slides
Cyber Data Breach Review_ Safeguarding Firms in the Digital Age
This blog explores the critical role of Cyber Data Breach Review in protecting legal firms from digital threats. It highlights how LDM Global's approach, grounded in their core values\u2014Team, Results, Accountability, and Quality\u2014helps firms n
1 views • 10 slides
State of Idaho Data Breach & Credit Monitoring Services Overview
This document outlines the State of Idaho's Division of Purchasing's procurement of data breach and credit monitoring services through NASPO ValuePoint. The purpose, scope of services, sourcing team details, evaluation criteria, and RFP process are detailed, emphasizing the benefits of having pre-es
0 views • 33 slides
Understanding Material Derivative in Fluid Mechanics
Fluid flows are described using Eulerian kinematics and material derivative concepts, highlighting the changes in scalar and vector fields. The acceleration and components of material acceleration are explored, along with visualizations of material acceleration. Trajectories and displacements of flu
0 views • 13 slides