BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
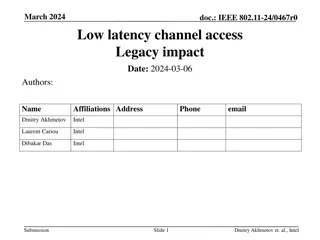
Enhancing Low Latency Channel Access in Legacy IEEE 802.11 Networks
This document discusses the impact of introducing a Low Latency (LL) channel access mechanism in legacy IEEE 802.11 networks. It addresses the use of High Priority EDCA (HiP EDCA) mechanisms, proposing solutions for improving tail latency in both isolated BSS and multi-BSS scenarios. Additionally, i
4 views • 10 slides
The Impact of No Code-Low Code on Startup Innovation
In the vibrant world of startups, innovation is the cornerstone of success. As these businesses aim to carve out their niches, they often face a common hurdle: the extensive resources required for traditional software development. However, the emergence of low code no code (LCNC) platforms is revolu
2 views • 12 slides
EBA Opinion on Legacy Instruments Monitoring Implementation Overview - Feb 2022 Meeting
The European Banking Authority (EBA) provided an opinion on legacy instruments monitoring at their Feb 2022 meeting. The presentation covers the monitoring in 2021, surveys, letters to competent authorities, and the overview of monitoring results. It discusses calls for input on the implementation o
0 views • 20 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Overview of EBA Opinion on Legacy Instruments Monitoring Implementation Results Feb 2022
In February 2022, the European Banking Authority (EBA) conducted monitoring on legacy instruments implementation. The presentation covers surveys, input from competent authorities, and outcomes. Efforts to address infection risks posed by legacy instruments were highlighted, with actions taken by in
1 views • 20 slides
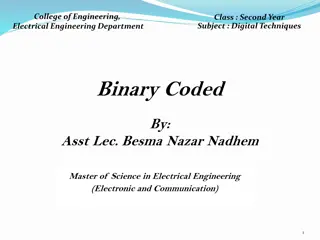
Understanding Binary Coded Decimal (BCD) and Excess-3 Code
Binary Coded Decimal (BCD) is a binary code used to represent decimal numbers, with the popular 8421 BCD code and its conversion process explained. Additionally, Excess-3 Code, another BCD code, is detailed with an example of finding its code for a given decimal number. Different BCD codes like 4221
0 views • 11 slides
Veterans Benefits Appeals and Legacy Appeals Process
Learn about the appeals process for denied VA benefits claims and the legacy appeals system for claims decided before February 19, 2019. Understand your rights to appeal decisions, examples of appealable decisions, actions that cannot be appealed, and the differences between Legacy Appeals and the A
3 views • 78 slides
Software Security Principles and Practices: Enhancing Program Code Security
Understanding and addressing critical web application security flaws like unvalidated input, cross-site scripting, buffer overflow, injection flaws, and improper error handling is crucial in enhancing the security of program code. The NIST report NISTIR 8151 provides valuable recommendations to redu
2 views • 44 slides
Insights into Legacy Accounting and Submissions
The legacy market is expected to grow significantly, with legacies becoming a crucial income source for UK charities. The emphasis on standardizing accounting methods for legacies is highlighted, aiming to enhance efficiency, accuracy, and forecasting. Key submissions propose uniformity in legacy ac
0 views • 22 slides
Legacy Giving Made Easy for Your Parish
Legacy giving is a crucial way to support nonprofits and churches through planned giving techniques, ensuring their sustainability for the future. Learn about the importance of legacy gifts and how they can shape the long-term success and impact of organizations. Discover why legacy giving is vital
0 views • 14 slides
Understanding the .NET Architecture Components
The .NET architecture comprises various key components such as the Common Language Specification, Code Manager, Managed Code, Unmanaged Code, and Native Code. These components play crucial roles in the development and execution of applications within the .NET framework. Managed code is executed by t
0 views • 21 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
STM32WB BLE Secure Connections Overview
This detailed content provides insights into the secure connections in STM32WB BLE devices, covering aspects such as BLE security methods, encryption techniques, pairing processes, key distribution, and security modes and levels. It emphasizes the use of Long Term Keys (LTK), Diffie-Hellman key exch
0 views • 12 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Unit Testing Legacy Code: Hijacking Singletons for Testing
Enabling unit testing of legacy code requires making changes without altering existing calling code. Singleton pattern poses challenges for testing, but strategies such as hijacking can be employed for effective unit testing. David Benson shares insights on legacy code attributes and unit testing ap
0 views • 39 slides
London 2012 Olympic Legacy Achievements
The legacy of the London 2012 Olympic and Paralympic Games has been remarkable, with significant achievements in sport participation, economic benefits, venue retention, and community engagement. Key highlights include a notable increase in people playing sports, substantial investments in grassroot
0 views • 20 slides
Legacy Transcripts Development Meeting Summary
Legacy Transcripts project aims to show progress in developing a web-based application to pull data from legacy systems into a single database for colleges transitioning to ctcLink. The iterative development process involves reviewing, testing, and deploying the application in smaller cycles until i
0 views • 10 slides
Multi-Label Code Smell Detection with Hybrid Model based on Deep Learning
Code smells indicate code quality problems and the need for refactoring. This paper introduces a hybrid model for multi-label code smell detection using deep learning, achieving better results on Java projects from Github. The model extracts multi-level code representation and applies deep learning
0 views • 10 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Importance of Security in Web Development
Our perception of security has evolved to acknowledge the presence of malicious actors and potential vulnerabilities in web applications. To write secure code, developers must assume the worst-case scenario and adopt a security mindset that trusts no one. Attackers have various goals, such as steali
0 views • 18 slides
Legacy of Leadership: Team Leaders and Cohorts 2018-2022
Explore the legacy of leadership through the team leaders and cohorts from 2018 to 2022. Witness the growth and impact of individuals like Cleve Clinton, Jill Jordan, Happy Franklin, and more as they lead and contribute to the legacy of leadership. Each cohort brings a unique blend of talent and exp
0 views • 4 slides
Faith and Legacy - A Journey of Conviction and Hope
The journey of faith and legacy intertwines with past roots and future confidence, revealing the righteousness of God through acts of faith. A young girl's emotional reaction to a touching scene, coupled with powerful messages of assurance and creation, highlight the significance of living by faith
0 views • 9 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Modern Strategies for Legacy Code Security
Explore advanced defenses against malware in legacy code, including techniques like NX bit implementation, randomizing layouts, and canaries. Learn about tools like Libsafe for dynamically intercepting risky function calls and enhancing security. Discover the effectiveness of methods like StackShiel
0 views • 25 slides
Legacy Fairness Enhancement in IEEE 802.11 Networks: Further Considerations
Investigating legacy fairness issues in IEEE 802.11 networks, this document explores methods to address throughput starvation of legacy stations due to enhanced Channel Clear Assessment (CCA) in High Efficiency (HE) stations. Two fairness methods, Legacy Frame Protection and PPDU Size Reduction, are
0 views • 9 slides
Current Issues in Secured Transactions Law in the United States: Licenses and Security Interests
This article discusses the current issues in secured transactions law in the United States, focusing on whether a debtor can grant a security interest in a statutory or contractual license, how syndicated financiers can perfect a security interest in a deposit account, and the collateral over which
0 views • 28 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Plumbing Code Appeals and Interpretations Overview
This document provides information on the agenda, upcoming professional development events, Building Code Appeal Board, Appeal Board decisions, Code Interpretation Committee, code interpretations, and final thoughts related to plumbing code appeals and interpretations. It covers the appeal process,
0 views • 8 slides