BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
Shielding Your Organization: Chief Security Officer Recruitment Insights
\"Shielding Your Organization: Chief Security Officer Recruitment Insights\" offers invaluable guidance for businesses seeking to fortify their security posture by recruiting the right Chief Security Officer (CSO). This comprehensive resource delves into the intricacies of chief security officer rec
0 views • 7 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
0 views • 1 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
1 views • 1 slides
Understanding Linux User Capabilities and Namespace Management
Linux user namespaces and capabilities play a critical role in managing system security and permissions. Users and groups are assigned unique IDs, and processes are associated with the user's ID. The kernel enforces permission checks based on user IDs and group IDs, allowing root access to bypass ce
0 views • 14 slides
Understanding AARCH64 Linux Kernel Memory Management
Explore the confidential and proprietary details of AARCH64 Linux kernel memory mapping, virtual memory layout, variable configurations, DDR memory layout, and memory allocation techniques. Get insights into the allocation of physically contiguous memory using Continuous Memory Allocator (CMA) integ
0 views • 18 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Understanding Generalized Discriminant Analysis (GDA) in Pattern Recognition
Generalized Discriminant Analysis (GDA) is a nonlinear form of Linear Discriminant Analysis (LDA) that utilizes kernel methods to find discriminatory features for optimal class separability. LDA aims to maximize the between-class covariance matrix while minimizing the within-class covariance matrix.
2 views • 17 slides
Optimizing User-Space Network Services with F-Stack and FreeBSD TCP/IP Stack
F-Stack, a user-space network service using DPDK and FreeBSD TCP/IP stack, addresses challenges in handling service traffic like CDN and live streaming. By leveraging 25GbE, 40GbE, and 100GbE NICs, coupled with multi-core CPUs and kernel bypass techniques, F-Stack overcomes bottlenecks between user
1 views • 17 slides
Understanding Kernel Tricks in Machine Learning
Kernel tricks in machine learning involve transforming inputs into higher-dimensional spaces to make linear models work for nonlinear data. Kernels can be applied to various algorithms like SVM, ridge regression, and more, allowing for better model performance with complex datasets.
0 views • 15 slides
Fundamentals of Operating Systems Explained
Explore the core concepts of operating systems, including kernel-userspace interactions, system calls, context switching, and virtual memory management. Delve into x86 assembly for system calls, hardware interrupts, and the flow of control during system call invocations. Gain insights into key compo
7 views • 19 slides
Improving the Reliability of Commodity Operating Systems
This research paper discusses the challenges and solutions in enhancing the reliability of commodity operating systems by addressing system failures caused by kernel extensions. The Nooks approach isolates extensions within protection domains, allowing them to reside in the kernel address space with
0 views • 40 slides
Raspberry Pi 2 Boot Process Overview
Raspberry Pi 2's boot process involves a series of stages initiated by the GPU, loading essential firmware and enabling hardware components gradually, leading to the activation of the CPU and the kernel's entry point. The system transitions through various low-level processes before reaching a stabl
0 views • 9 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Multi-phase System Call Filtering for Container Security Enhancement
This tutorial discusses the importance of multi-phase system call filtering for reducing the attack surface of containers. It covers the benefits of containerization, OS virtualization, and the differences between OS and hardware virtualization. The tutorial emphasizes the need to reduce the kernel
0 views • 32 slides
Understanding User Mode, Kernel Mode, Interrupts, and System Calls in Computer Architecture
In modern computers following Von Newman Architecture, programs and data are stored in RAM. The CPU, RAM, ROM, and devices communicate via address and data buses. The system operates in both kernel and user modes, where kernel mode allows full system control, while user mode restricts access for sec
0 views • 29 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Tracing Network Packets in Linux Kernel with eBPF
This presentation discusses the challenges of troubleshooting modern networking systems and proposes a solution using eBPF technology to trace the path of network packets in the Linux kernel. The goal is to develop a tool that provides detailed information about how network packets are processed in
0 views • 16 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Analyzing Multimodality in Density Distributions Using JMP Scripting
Explore variability sources hidden in density distributions through JMP scripting. The analysis focuses on identifying and filtering distribution modes in semiconductor fab electrical measurements using kernel estimation and empirical rules. Antonio D'Angelo and Felice Russo from Lfoundry S.r.l. Ita
0 views • 6 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Understanding Remote Procedure Call (RPC) in Different Kernel Environments
Communication through Remote Procedure Call (RPC) plays a crucial role in facilitating seamless interaction between server and client processes, whether on the same machine or across different kernels. This technology streamlines local and cross-domain communication, optimizing performance while ens
0 views • 9 slides
Overview of the Pintos Instructional Operating System Kernel Project
Description of the Pintos Operating System Kernel project, including its use in educational settings at institutions such as Stanford University and Virginia Tech. The project aims to provide students with a hands-on experience in OS design, focusing on the internal workings of the kernel. Pintos fe
0 views • 33 slides
Understanding Pipes in Process Communication
Pipes in process communication allow for high-throughput data transfer between parent and child processes. The kernel creates a communication stream through file descriptors, enabling one process to send data to another. Processes can use pipes for efficient inter-process communication, with the ker
1 views • 15 slides
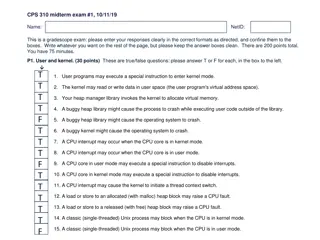
Understanding User and Kernel Modes in Operating Systems
The content provided discusses various aspects of user and kernel modes in operating systems through a set of true/false questions related to user programs, CPU interrupts, heap management, and process behavior in different modes. It touches on the role of the kernel in managing virtual memory, hand
0 views • 10 slides
Hyper-Parameter Tuning for Graph Kernels via Multiple Kernel Learning
This research focuses on hyper-parameter tuning for graph kernels using Multiple Kernel Learning, emphasizing the importance of kernel methods in learning on structured data like graphs. It explores techniques applicable to various domains and discusses different graph kernels and their sub-structur
0 views • 20 slides
Overview of UNIX and Linux Operating Systems
The UNIX brand encompasses a range of powerful multitasking, multiuser operating systems used by various organizations to develop IT technologies. UNIX internals consist of kernel space and user space, with programs accessing system services rather than hardware directly. The Unix filesystem is a ke
0 views • 36 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Understanding Context Switching and User-Kernel Interaction in Operating Systems
Context switching in operating systems involves a seamless transition between user-level threads without the kernel's awareness. User-level code manages register state and stack pointers, while user-kernel mode switching requires changing processor privilege levels and agreement on information excha
0 views • 25 slides