Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
Driving Effectiveness with Direct Mail: Key Insights
Direct mail continues to be a powerful marketing tool, offering personalized, targeted, and impactful campaigns in today's digital world. WARC's research highlights the effectiveness of including direct mail in marketing strategies, driving revenue growth, brand building, and overall campaign succes
1 views • 15 slides
Comprehensive Review on Medical Separations and Direct Threat Assessments for Health Staff
This resource provides an extensive overview of medical separations and direct threat assessments relevant to Job Corps health and wellness staff and subcontractors. It covers topics such as the process of medical separations, reinstatement rights, disability accommodation, and when medical separati
1 views • 60 slides
MONEYVAL,the next six months.The view from the Isle of Man Experience from assessments.
Detailed insights on upcoming MONEYVAL assessments, experiences from the Isle of Man, timelines for 2023-2024, and advice for preparing for assessments. The content covers events, timelines, nationwide strategies, risk assessments, and publications related to money laundering and terrorist financing
1 views • 16 slides
Quick and Easy access to Cash with Direct Lender's Short Term Loans UK
Short Term Loans Direct Lenders | Short Term Loans UK Direct Lender | Short Term Loans UK\nOn the other hand, short term loans UK direct lender are available to you in a convenient way. The lender does not conduct a credit check. It is intended that these funds accept applications with any kind of c
1 views • 1 slides
Understanding Direct and Reported Speech in English
Explore the differences between direct and reported speech, learn how to convert direct speech into reported speech, and understand when to use each form in writing. Direct speech uses the speaker's actual words in quotes, while reported speech conveys the gist of what was said without using exact w
2 views • 20 slides
Mastering Direct and Indirect Speech: A Comprehensive Guide
Explore the world of direct and indirect speech with this in-depth lesson on narration. Learn how to speak using both methods, transform sentences from direct to indirect, and discover the nuances of backshift of tenses and adverbs. Gain a better understanding of how grammatical changes occur betwee
2 views • 31 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
1 views • 51 slides
Understanding Direct and Indirect Speech in English
Direct speech involves reporting exact words spoken, while indirect speech conveys the same message using different words. Learn about the rules for changing pronouns and key aspects of both direct and indirect speech. Master the art of transforming sentences from direct to indirect speech with ease
2 views • 15 slides
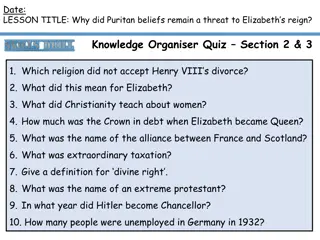
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
Risk Management Strategies in Organizational Security
Exploring risk management in organizational security, this study guide delves into resiliency, automation strategies, policies, and procedures to reduce risk. It covers threat assessments, computing risk assessments, qualitative vs. quantitative risk measurements, and actions based on risk assessmen
1 views • 19 slides
Understanding AML Risk Assessments and Due Diligence Regulations
Anti-money laundering (AML) risk assessments and due diligence regulations are crucial for preventing money laundering and terrorist financing. This content discusses the importance of risk assessments, client due diligence, and regulatory compliance in the AML landscape. It emphasizes the need for
0 views • 13 slides
Understanding Direct and Indirect Objects in Grammar
Direct and indirect objects are essential components of sentences, helping clarify the action and recipients involved. Direct objects receive the action directly, answering the questions "Whom?" or "What?" Indirect objects indicate to whom or for whom the action is done, always appearing between the
0 views • 12 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Direct Routing with Teams: Opportunity or Threat?
Microsoft's shift in cloud architecture for voice services opens up new possibilities for enterprises and carriers with Teams Direct Routing. This allows seamless integration of PSTN services directly to the cloud, offering flexibility in maintaining existing contracts while transitioning to Teams a
0 views • 10 slides
Utah State Board of Education Testing Ethics Policy Presentation
This presentation by the Utah State Board of Education outlines the organization of the Standard Test Administration and Testing Ethics Policy. It covers the purpose of testing, assessments, mandated assessments, state assessments, federal assessments, and required district assessments. The focus is
0 views • 26 slides
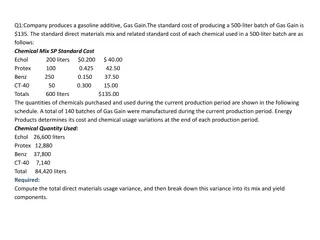
Costing and Variance Analysis in Manufacturing Processes
The content discusses various scenarios related to costing and variance analysis in manufacturing processes. It addresses topics such as direct materials usage variance, direct labor mix and yield variances, total direct labor efficiency variance, and standard costing system variances. The examples
0 views • 8 slides
Understanding Direct Objects and Direct Object Pronouns
Direct objects receive the direct action of the verb, and when they are people or domesticated animals, the personal "a" is used. Direct object pronouns replace the object to avoid repetition. Learn more about the personal "a", its usage, and how to identify direct objects in sentences.
0 views • 53 slides
Understanding the 2015 Smarter Balanced Interim Assessments
This informational piece delves into the details of the 2015 Smarter Balanced Interim Assessments, which are part of the broader assessment system designed to aid teaching and student learning. The assessments are optional yet highly recommended, offering valuable insights to teachers for monitoring
0 views • 50 slides
Student Direct Deposit Setup Instructions
Follow these step-by-step instructions to set up direct deposit for your student accounting account. Start by accessing the Account Inquiry link under My Account, then navigate to the Account Services tab to enroll in Direct Deposit. Enter your Bank ID/Routing and Account number, agree to the terms,
0 views • 6 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Understanding Direct Objects and Direct Object Pronouns in English and French
Explore the concepts of direct objects and direct object pronouns in English and French languages. Learn how direct objects are used in sentences, the role of direct object pronouns in avoiding repetition, and the differences in sentence structure when using object pronouns in French. Discover commo
0 views • 24 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
0 views • 42 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Pennsylvania School Threat Assessment Procedures and Guidance
Ongoing concerns about school safety led to legislation in 2019, requiring schools in Pennsylvania to establish threat assessment teams. This presentation provides an overview of the statute, threat levels, team responsibilities, procedures, and resources for school staff, parents, and guardians to
0 views • 25 slides
Conducting Threat Assessments Through the Atrocity Prevention Lens
This module from the GLOBAL CENTRE FOR THE RESPONSIBILITY TO PROTECT focuses on conducting threat assessments through an atrocity prevention lens. It covers risk identification, situational awareness in field settings, information collection methods, addressing vulnerabilities of women and children,
0 views • 20 slides
Bomb Threat Preparedness Guidelines for Shifa International Hospital
The Shifa International Hospital emphasizes the importance of maintaining a secure environment for employees, patients, and visitors in the event of a bomb threat. This presentation covers the types of bomb threats, steps to follow in case of a bomb threat, and provides guidance on handling telephon
0 views • 14 slides
High School Students Behavioral Threat Assessment Tabletop Exercise Analysis
Conduct a tabletop exercise analyzing the behavioral threat assessment of two high school students. Explore roles and responsibilities, exercise itinerary, goal, and purpose to enhance threat assessment team preparedness and response. Utilize simulated scenarios to simulate real-world events for opt
0 views • 23 slides
Examining Stereotype Threat in Engineering Education
Exploring the experiences of female engineering students facing stereotype threat, this critical theoretical framework study sheds light on the challenges that impact their academic journey. Through narrative inquiry methodology, the research focuses on white female students to understand how stereo
0 views • 37 slides
School Safety and Threat Assessment Program Overview
Fact-based Threat Assessment for Safe and Supportive School Programs involves identifying, inquiring, assessing, and managing potentially dangerous situations. It aims to distinguish between those making threats and those posing real risks, without profiling or labeling individuals. Understanding th
0 views • 20 slides
Exploring VCAA Online Language Assessments Webinar
Join the VCAA and ACER presentation for a closer look at the Language Assessments, focusing on listening and reading assessments in multiple-choice format. Learn how teachers can utilize these assessments to enhance language teaching, with a glimpse into assessment items and alignment with the Victo
0 views • 22 slides
Impact of Stereotypes on Perceived Facial Threat in Women Offenders
Facial expressions play a significant role in understanding emotions, but stereotypes can influence how people perceive facial affect. This study examines how reading tabloid articles about crimes committed by dark and light-skinned women offenders affects the perceived facial threat. Using a 2x2 fa
0 views • 9 slides