Climbing to the Top of the Test Pyramid with Playwright
Playwright, a cross-browser, cross-language, and cross-platform web testing and automation framework, can help you climb to the top of the test pyramid. Automate your E2E testing with ease and eliminate flaky tests using Playwright's powerful features and web-first assertions.
1 views • 42 slides
❤[READ]❤ Deep Space Craft: An Overview of Interplanetary Flight (Springer Praxis
\"COPY LINK HERE ; https:\/\/getpdf.readbooks.link\/3540895094\n\n[PDF] DOWNLOAD Deep Space Craft: An Overview of Interplanetary Flight (Springer Praxis Books) | Deep Space Craft: An Overview of Interplanetary Flight (Springer Praxis Books)\n\"\n
0 views • 6 slides
Deep Reinforcement Learning for Mobile App Prediction
This research focuses on a system, known as ATPP, based on deep marked temporal point processes, designed for predicting mobile app usage patterns. By leveraging deep reinforcement learning frameworks and context-aware modules, the system aims to predict the next app a user will open, along with its
0 views • 24 slides
Deep Hedging and Heat Rate Options: Enhancing Financial Markets
Explore the innovative concept of deep hedging and heat rate options introduced by Mark Higgins, focusing on improved hedging strategies through deep learning and optimization techniques. Discover the shift from traditional risk-neutral pricing to a more dynamic approach that utilizes neural network
0 views • 16 slides
Advancing Deep Space Exploration Capabilities: NextSTEP Modular ECLSS Effort
The Next Space Technologies for Exploration Partnerships (NextSTEP) program, initiated in 2015, focused on enhancing deep space habitation capabilities through a public-private partnership. The Modular ECLSS Effort aimed to develop adaptable ECLSS systems for various exploration missions. It involve
0 views • 14 slides
Deep Institute: Your Path to DSSSB Triumph in Delhi
Deep Institute prepares you for success in the DSSSB exams in the busy city of Delhi. Deep Institute is the best coaching institute in Delhi that provides a path to success according to the requirements of each student. With the help of our experienced faculty, personalized coaching, and complete st
1 views • 2 slides
USING GPUS IN DEEP LEARNING FRAMEWORKS
Delve into the world of deep learning with a focus on utilizing GPUs for enhanced performance. Explore topics like neural networks, TensorFlow, PyTorch, and distributed training. Learn how deep learning algorithms process data, optimize weights and biases, and predict outcomes through training loops
4 views • 98 slides
Block-grained Scaling of Deep Neural Networks for Mobile Vision
This presentation explores the challenges of optimizing Deep Neural Networks (DNN) for mobile vision systems due to their large size and high energy consumption. The LegoDNN framework introduces a block-grained scaling approach to reduce memory access energy consumption by compressing DNNs. The agen
8 views • 39 slides
Understanding Deep Ocean Circulation and Salinity Patterns
Explore the intricate relationship between ocean salinity, vertical structure, and deep-water currents in this informative collection of images and explanations. Discover how salt inputs and outputs influence ocean salinity levels, and learn about the factors that contribute to the vertical variatio
12 views • 21 slides
Adventure Awaits- Find Your Deep Creek Rental for All-Season Fun
Unleash your inner child at Deep Creek Lake! Beyond the serenity of nature and outdoor thrills, Deep Creek Lake offers a haven for family fun. Deep Creek Lake rentals with spacious living areas and game rooms provide the perfect space for creating lasting memories. Splash together at the lake's sand
2 views • 4 slides
Equalisation Measure for Deep-Seabed Mining in the Commonwealth Area
Deep-seabed mining in the Commonwealth Area is a topic of discussion, focusing on implementing equalisation measures to ensure fair competition and avoid competitive advantages or disadvantages. The effective tax rate and financial models are considered to achieve a balanced approach. Challenges suc
1 views • 18 slides
Wars of the Roses (1445-1461): Source Analysis on the Downfall of Henry VI
This content delves into the Wars of the Roses period (1445-1461) in England, focusing on the outbreak of conflicts, political turmoil, and the downfall of Henry VI. It includes an inquiry topic, sample paper question, and a detailed analysis of a historical source (Source A) by Jack Cade regarding
0 views • 16 slides
Introduction to Predicate Logic in Mathematics
Predicate logic is a powerful tool used in mathematics to express complex relationships and assertions that cannot be adequately represented by propositional logic. It allows for the quantification of statements over a range of elements using predicates and quantifiers like universal and existential
1 views • 13 slides
How to Check Status in SAM.gov
SAM.gov is a crucial site for checking the status of registrations and validations. Once logged in, users can visit the workspace to monitor their status daily, apply, or renew. The process involves validating entities, obtaining a Unique Entity ID, entering core data and assertions, completing Reps
0 views • 8 slides
2022 Financial Audit Manual Update Overview
This content provides details on the 2022 Financial Audit Manual update, focusing on significant changes to GAO/CIGIE FAM Volumes 1 and 2. It covers key amendments, revised examples of engagement letters, and communication requirements for auditors. The update also highlights changes in AU-C standar
1 views • 19 slides
Analysis of John Donne's Poem "The Sunne Rising
John Donne's poem "The Sunne Rising" humorously portrays a lover chiding the sun for interrupting his time with his beloved. The speaker asserts that love transcends time and space, elevating his relationship to a cosmic importance. Through hyperbolic assertions, Donne explores the intense subjectiv
2 views • 8 slides
Runtime Checking of Expressive Heap Assertions
Motivated by the unreliability of large software systems due to concurrency bugs and limitations of static analysis, the goal is to enable runtime analysis of deep semantic properties with low overhead. This involves checking expressive heap assertions at runtime with minimal impact on performance,
0 views • 15 slides
European Deep Space Surveillance and Tracking Collaboration
EU Space Surveillance and Tracking program involves five European nations collaborating to assess and reduce risks to European spacecraft, provide early warnings for re-entries and space debris, and prevent space debris proliferation. Available deep space sensors, such as optical telescopes, are uti
1 views • 8 slides
Understanding Predicate Calculus: Symbols, Terms, and Variables
Predicate calculus extends propositional calculus by introducing symbols like truth values, constants, variables, and functions. It allows for precise manipulation of components within assertions, enabling the creation of general statements about classes of entities. Learn how predicates define rela
1 views • 14 slides
Facts and Myths About Food and Health
In this content, various assertions about food, fruits, health, and exercise are made. It covers topics such as the growth of tomatoes, the colors of corn, the nature of avocados, the process of making raisins, the anatomy of strawberries, the color of okra, exercise requirements, junk food percepti
0 views • 10 slides
Handling Errors and Failures in Software Design and Implementation
Exploring the concepts of dealing with errors and failures in software development, focusing on assertions and exceptions. Discusses the importance of preventing complete failures, giving information about problems, and preventing harm when things go wrong. Emphasizes the significance of structuring
0 views • 37 slides
EGI Installation Check-in Updates and Support Activities
The EGI foundation, funded by the European Commission, has implemented various updates in their Installation Check-in process. These updates include adding support for AES-GCM encrypted attribute assertions, enabling expiration policies, improving user notifications, and deploying a new Federation R
0 views • 15 slides
Automated Static Verification of Higher-order Functional Programs
Explore the automated static verification of higher-order functional programs, focusing on Haskell code. Learn about denotational semantics, program assertions, and tools like GHC for verification. Discover the emphasis on simplicity and structural properties for easy proofs. Consider utilizing exis
0 views • 22 slides
Introduction to Code Reasoning in CSE331 Lecture
In this lecture, we delve into the fundamentals of code reasoning, focusing on forward and backward reasoning techniques in straight-line and if-statement code. The session includes reviewing the practice of identifying the strongest assertions and understanding the dual purposes of proving code cor
0 views • 24 slides
Handling Privilege and Discovery Issues in Corporate Litigation
Exploring privilege assertions and discovery rules in Illinois law for corporate litigation cases, emphasizing the burden of proof on privilege assertion, strong disfavor of privileges, and exceptions in certain circumstances. Understanding the importance of disclosure in legal proceedings and the n
0 views • 51 slides
Introduction to Keras for Deep Learning
Introduction to the world of deep learning with Keras, a popular deep learning library developed by François Chollet. Learn about Keras, Theano, TensorFlow, and how to train neural networks for tasks like handwriting digit recognition using the MNIST dataset. Explore different activation functions,
0 views • 17 slides
Assertion Collection in DICOM Working Group 07 Radiotherapy
The Assertion Collection IOD addresses the need to collect assertions outside DICOM Instances, providing contextual and identification information. It aims to collect assertions for DICOM Instances during clinical procedures, providing meta information about assertions and allowing for self-containe
0 views • 9 slides
Advanced Program Optimization Techniques for Efficient Verification and Goal-Directed Search
Explore advanced program optimization techniques targeting program verification and goal-directed search, including deep assertions, inlining-based verifiers, and lazy inlining algorithms. Learn about optimizations that preserve semantics and improve execution/verification time.
0 views • 34 slides
Understanding Semantics of Datalog With Negation
Delve into the semantics of Datalog with negation, exploring the concepts of local stratification, stable models, well-founded models, and the importance of model selection in determining the meaning of Datalog programs. Discover the significance of ground atoms and the implications for declarative
0 views • 55 slides
Differential Assertion Checking and Relative Correctness in Software Verification
Differential assertion checking compares two similar programs to identify errors, while relative correctness ensures all assertions pass, highlighting failed assertions. The content discusses the challenges and benefits of these techniques in software verification, with examples of correct and buggy
0 views • 17 slides
Understanding SQL Constraints and Triggers in Database Systems
SQL (Structured Query Language) provides a high-level approach to database management by focusing on what needs to be done rather than how. Constraints and triggers play vital roles in ensuring data integrity and enforcing specific actions. Keys, foreign keys, value-based constraints, tuple-based co
0 views • 130 slides
Exploring Sports and Deep Tissue Massage Techniques
In this lesson plan, students will delve into the world of sports and deep tissue massage, learning about the theoretical aspects, hands-on techniques, and graded events involved. The content covers classroom rules, the introduction to sports and deep tissue massage, an overview of the segment class
0 views • 25 slides
Understanding the Language of Advertising Claims
The language of advertising claims, as explored by Jeffrey Schrank, delves into how ads make assertions about product superiority. It discusses misleading versus true claims, the prevalence of pseudo-information for parity products, and various types of claims like Weasel, Water is Wet, Unfinished,
0 views • 13 slides
Women's Role in the Neolithic Period and Challenges Faced
The passage discusses the significant role women played during the Neolithic period, where they enjoyed equality with men, invented agriculture, and contributed equally to the community. However, over time, the status of women declined as men began taking over agricultural work. The question further
0 views • 6 slides
UC Santa Barbara engineering
Explore the need for specification languages in quantum algorithms, correctness verification methods, programmer assertions, success probabilities, scalable compilation techniques, and language design ideas. Emphasizing the importance of tracking precision, error bounds, and optimizing quantum opera
0 views • 8 slides
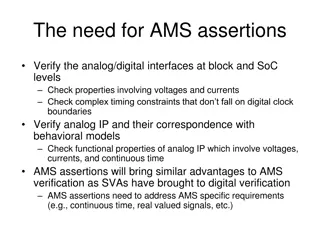
Advancing AMS Assertions for Analog/Digital Interface Verification
AMS assertions play a crucial role in verifying analog/digital interfaces, checking properties related to voltages, currents, and complex timing constraints. They bring advantages similar to SVAs in digital verification, addressing specific AMS requirements. Examples showcase comparisons of voltage/
0 views • 11 slides
Understanding Multi-Valued Logic in Three-Valued Systems
Explore the intricacies of multi-valued logic in three-valued systems, including Liberal and Draconian protocols. Learn how logical assertions and byte generation are influenced by the values of variables like a, b, u, and v.
0 views • 23 slides
Microsoft Research: Deep Learning, AI, and Information Processing Overview
Dive into the world of deep learning and artificial intelligence through Microsoft Research's exploration of new-generation models and methodologies for advancing AI. Topics covered include computational neuroscience, deep neural networks, vision and speech recognition, as well as the application of
0 views • 19 slides
Understanding Defensive Programming for Robust Code
Defensive programming, as explained by Nikolaus Embgen, is a proactive approach to writing code that focuses on error prevention, input validation, and robustness. It emphasizes not trusting external sources and assuming potential flaws in the code. By using techniques such as assertions, error hand
0 views • 23 slides
Enhancing Program Verification Through Optimization Strategies
Explore the realm of program transformations and optimizations targeted at improving program verification processes. Delve into inlining-based verifiers, deep assertions, and goal-directed search strategies to enhance program reliability and efficiency.
0 views • 34 slides

![❤[READ]❤ Deep Space Craft: An Overview of Interplanetary Flight (Springer Praxis](/thumb/21511/read-deep-space-craft-an-overview-of-interplanetary-flight-springer-praxis.jpg)