Types Cyber Attacks: Cyber Security Training Workshop
Join our Cyber Security Training Workshop to learn about different types of cyber attacks such as social engineering attacks, DDoS attacks, malware attacks, MitM attacks, APTs, and password attacks. Enhance your knowledge and skills in cyber security.
15 views • 45 slides
Adversarial Machine Learning
Evasion attacks on black-box machine learning models, including query-based attacks, transfer-based attacks, and zero queries attacks. Explore various attack methods and their effectiveness against different defenses.
21 views • 60 slides
Pest control in Kolkata
Are you looking for professional pest control services in Kolkata? Socspl.com is here to provide the most reliable and efficient pest control services in Kolkata. We have extensive knowledge and experience in handling all kinds of pest infestations such as termite control, cockroach control, ant con
1 views • 8 slides
Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
1 views • 46 slides
Understanding Malicious Attacks, Threats, and Vulnerabilities in IT Security
Malicious attacks, threats, and vulnerabilities in IT systems pose significant risks and damages. This chapter explores the types of attacks, tools used, security breaches, and measures to protect against cyber threats. Learn how security professionals safeguard organizations from malicious attacks
0 views • 24 slides
Role of AI in Threat Detection and Zero-day Attacks
Cybercrime has been on the rise, especially with the surge in zero-day attacks targeting various industries. State-sponsored actors, like Chinese groups, dominate zero-day exploits, challenging traditional detection methods. Incorporating AI, machine learning, and deep learning is vital in enhancing
0 views • 9 slides
Principles of Cyber Security
Threat actors prioritize targeting networks to exploit vulnerabilities, leading to various attacks such as interception, DNS attacks, and MITM attacks. MITM attacks involve eavesdropping on communications or impersonating parties, with techniques like session replay to steal credentials. Implementin
0 views • 7 slides
Understanding Network Security Fundamentals and Common Web Application Attacks
Learn about the basics of network security, including common web application attacks such as Cross-Site Scripting (XSS), SQL Injection, and Session Hijacking. Explore important concepts like cookies, markup languages, and ways to enhance security to protect against cyber threats.
0 views • 11 slides
Managing Covid-19 Cyber and Data Protection Risks
Exploring the risks and challenges related to cyber attacks and data protection amidst the Covid-19 pandemic. The agenda covers an overview of cyber-attacks, recent developments, protections against cyber attacks, data protection concerns during lockdown, compliance steps, and employee rights issues
1 views • 35 slides
Mitigation of DMA-based Rowhammer Attacks on ARM
Practical strategies are presented in "GuardION: Practical Mitigation of DMA-based Rowhammer Attacks on ARM" to defend against Rowhammer attacks on ARM architecture. The paper discusses Rowhammer defenses, RAMPAGE attacks on Android OS, and introduces GuardION as a lightweight mitigation approach. I
0 views • 48 slides
Cybersecurity Challenges: Attacks on Web Applications and Cost of Security Breaches
In the realm of cybersecurity, attacks on web applications pose a significant threat with 78% of attacks targeting applications. The consequences of these attacks are immense, with projected costs reaching $6 trillion annually by 2021. Notable breaches in recent years highlight the urgency for robus
8 views • 23 slides
Understanding Marketing Control and Its Importance in Business
Marketing control is a crucial process for firms to evaluate the impact of their marketing strategies and initiatives, making necessary adjustments for better outcomes. It involves various aspects such as annual plan control, profitability control, efficiency control, and strategic control. The proc
0 views • 20 slides
Understanding Network Security: Hijacking, Denial of Service, and IDS
This content delves into the concepts of spying and hijacking in network security, covering topics such as eavesdropping on packets, injecting packets into streams, denial of service attacks, and defense mechanisms like firewalls and IDS. It explores low-level attacks and defenses, including ARP cac
1 views • 81 slides
Understanding Control Plans in Process Management
A Control Plan is vital in controlling risks identified in the FMEA process, focusing on process and product characteristics, customer requirements, and establishing reaction plans for out-of-control conditions. It serves as a central document for communicating control methods and includes key infor
1 views • 20 slides
Understanding Denial-of-Service Attacks and Defense Strategies
Denial-of-Service attacks pose a serious threat where attackers flood networks with traffic, leading to system crashes and slowdowns. Explore the impact, expected results, and various categories of DoS attacks such as bandwidth attacks, protocol exceptions, and logic attacks. Learn how to defend aga
0 views • 61 slides
Understanding Network Denial of Service (DoS) Attacks
Network Denial of Service (DoS) attacks aim to disrupt services by overwhelming them with traffic. These attacks can occur at various layers of the network stack and exploit weaknesses to achieve their goal. Amplification attacks, such as the Smurf attack and DNS Amplification attack, can significan
2 views • 52 slides
Preventing Active Timing Attacks in Low-Latency Anonymous Communication
This research addresses the vulnerabilities of onion routing to timing attacks and proposes solutions to prevent active timing attacks, focusing on low-latency anonymous communication systems. Various problems related to timing attacks in onion routing are analyzed, including the role of adversaries
0 views • 52 slides
Understanding Control Hijacking Attacks in Software Systems
Control hijacking attacks, such as buffer overflows and format string vulnerabilities, allow attackers to take over a target machine by manipulating application control flow. Knowledge of C functions, system calls, CPU, and OS used is crucial for executing these attacks successfully. This summary pr
1 views • 55 slides
Understanding Control Hijacking Attacks and Defenses
Control hijacking attacks pose a significant threat by allowing malicious actors to manipulate data and control flow within a system. This article explores common attack methods like stack smashing and heap spraying, along with defenses such as fixing bugs, implementing platform defenses, and markin
1 views • 36 slides
Strategies to Protect School Systems from Cyber Attacks
Schools are increasingly becoming targets of cyber attacks, making cybersecurity measures crucial. The article discusses the importance of responding to cyber attacks, creating incident response plans, and being vigilant against interception attacks. It outlines the steps to detect, document, and mi
0 views • 21 slides
Understanding Low-Intensity DoS Attacks on BGP Infrastructure
Low-intensity Denial of Service (DoS) attacks present a new challenge in cyber warfare, blending in with regular traffic to target communication channels like HTTP, SMTP, and DNS. These attacks require multiple participating hosts to flood the target with useless packets, gradually overloading serve
0 views • 25 slides
Automated Signature Extraction for High Volume Attacks in Cybersecurity
This research delves into automated signature extraction for high-volume attacks in cybersecurity, specifically focusing on defending against Distributed Denial of Service (DDoS) attacks. The study discusses the challenges posed by sophisticated attackers using botnets and zero-day attacks, emphasiz
0 views • 37 slides
Web Security Threats and Vulnerabilities: An Overview
Understanding the risks associated with web security, including issues like IP hijacking, cache poisoning, and transparent proxies. Explore how existing approaches fall short in protecting against malicious attacks and potential exploits, with observed vulnerabilities highlighting the importance of
0 views • 17 slides
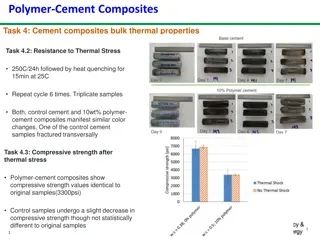
Study on the Thermal and Chemical Properties of Polymer-Cement Composites
The study investigates the resistance of polymer-cement composites to thermal stress and chemical attacks such as acidic and high CO2 environments. Results show similar color changes in control cement and polymer-cement composites after thermal stress, with the latter maintaining compressive strengt
0 views • 5 slides
Unit Testing Legacy Code: Hijacking Singletons for Testing
Enabling unit testing of legacy code requires making changes without altering existing calling code. Singleton pattern poses challenges for testing, but strategies such as hijacking can be employed for effective unit testing. David Benson shares insights on legacy code attributes and unit testing ap
0 views • 39 slides
Transparent and Efficient CFI Enforcement with Intel Processor Trace
This research discusses Control Flow Integrity (CFI) enforcement to combat control flow hijacking attacks. It explores methods for runtime CFI enforcement, including instrumented checking and transparent monitoring. The study delves into trace mechanisms, buffer management strategies, and when to tr
0 views • 32 slides
Targeted Deanonymization via the Cache Side Channel: Attacks and Defenses
This presentation by Abdusamatov Somon explores targeted deanonymization through cache side-channel attacks, focusing on leaky resource attacks and cache-based side-channel attacks. It discusses the motivation behind these attacks, methods employed, potential defenses, and the evaluation of such att
0 views • 16 slides
Understanding DLL Hijacking in Windows
Dynamic-Link Libraries (DLLs) are a mechanism in Windows for sharing code and data, making it easier to design and build applications. By loading DLLs either statically at compile time or dynamically at runtime, programs can enhance memory management and user experience. However, DLL hijacking, a co
0 views • 13 slides
Understanding Software Security Fundamentals
This review delves into essential concepts of software security, covering topics such as basic execution models, parameter areas, control flow hijacking, channeling vulnerabilities, buffer overflows, and format strings. It explores stack diagrams and analysis, elucidating critical mechanisms like co
0 views • 17 slides
Securing Domain Control with BGP Attacks and Digital Certificates
Exploring the vulnerabilities of domain control verification in the context of BGP attacks and the role of digital certificates in ensuring security. The process of domain control verification, issuance of digital certificates by Certificate Authorities (CAs), and the significance of Public Key Infr
0 views • 53 slides
Understanding Network Security Vulnerabilities and Attacks
Explore the world of network security vulnerabilities and attacks, including Denial-of-Service (DoS) and Distributed-Denial-of-Service (D-DoS), security flaws in the TCP/IP protocol suite, ICMP attacks, routing attacks, and TCP attacks. Learn about common security vulnerabilities such as address spo
0 views • 36 slides
Evolved Addressing and Forwarding in Information-Centric Networks
The content discusses Evolved Addressing and Forwarding in Information-Centric Networks, focusing on an accountable Internet protocol (AIP) that addresses vulnerabilities at the IP level, such as source spoofing, DoS attacks, and route hijacking. AIP utilizes a hierarchy of self-certifying addresses
0 views • 16 slides
Understanding Network Security Fundamentals in Computer Networks
Explore the importance of network security in Computer Networks, focusing on key aspects like confidentiality, integrity, authentication, and non-repudiation. Learn about common threats, such as eavesdropping, impersonation, hijacking, and denial of service attacks, and the role of cryptography in e
0 views • 28 slides
Understanding Control Hijacking Attacks in Computer Systems
Explore the concept of control hijacking attacks in computer systems, including buffer overflows, format string vulnerabilities, and use-after-free exploits. Learn about the attacker's goal, examples of attacks, and the importance of understanding C functions, the stack, and the heap. Delve into sys
0 views • 39 slides
Understanding Network Interference in CS590B/690B Lecture
Delve into the realm of network interference through the CS590B/690B lecture with Phillipa Gill at UMass Amherst. Explore topics such as Internet routing, timing attacks, BGP hijacks, Tor network functionality, relay selection, collusion scenarios, use of guards, web site fingerprinting attacks, tra
0 views • 11 slides
Comprehensive Guide on XSS Attacks and Defense Strategies
Explore the intricate details of Cross-Site Scripting attacks, the anatomy of XSS attacks, safe ways to represent dangerous characters in web pages, defense mechanisms based on data types and contexts, and the significance of encoding and output handling. Learn how attackers misuse XSS to hijack ses
0 views • 32 slides
Machine Learning for Cybersecurity Challenges: Addressing Adversarial Attacks and Interpretable Models
In the realm of cybersecurity, the perpetual battle between security analysts and adversaries intensifies with the increasing complexity of cyber attacks. Machine learning (ML) is increasingly utilized to combat these challenges, but vulnerable to adversarial attacks. Investigating defenses against
0 views • 41 slides
Authenticated Firmware Loaders: Verification and Potential Vulnerabilities
This research paper explores the verification of authenticated firmware loaders presented by Sujit Kumar Muduli, Pramod Subramanyan, and Sayak Ray. It delves into the secure boot process to prevent malicious firmware compromise. The study also discusses trusted firmware updates for remote device sec
0 views • 29 slides
Understanding DDoS Attacks: Simulation, Analysis & Defense
Delve into the world of Distributed Denial of Service (DDoS) attacks with this comprehensive study covering the architecture, advantages, bot installation phases, attack methods, defenses, and simulation. Learn about the detrimental impact of DDoS attacks on servers, their multi-tiered structure, an
0 views • 20 slides
Overview of DoS and DDoS Attacks in Cybersecurity
This content provides an in-depth overview of Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks in cybersecurity. It covers the types of attacks, including volumetric, reflected, and stealthy, along with detailed explanations and examples. Additionally, it discusses how DoS at
0 views • 8 slides