Seat Belts
How seat belts work in a crash and the importance of wearing them to protect yourself during a collision.
0 views • 14 slides
Line Segment Intersection
Geometric intersections play a crucial role in computational geometry for tasks such as solid modeling, collision detection in robotics, and overlaying subdivisions in geographic information systems. The problem of line segment intersection involves finding all intersection points between a set of c
0 views • 17 slides
Autonomous Conjunction Assessment Methodology Among Satellites
Methodology for Collision Avoidance (CA) among constellations of autonomously-controlled satellites is crucial for protecting assets in space. From straightforward protection against dead satellites to active coordination for maneuverable payloads, the range of primary-secondary CA possibilities is
1 views • 12 slides
Understanding 2D Collision Detection in Game Development
Explore the intricacies of 2D collision detection in game development through methods like distance checks, bounding shapes, and optimizing collision tests. Dive into concepts like sprite speed assumptions, square-square collisions, and rectangle testing complexities. Learn about useful Rectangle me
5 views • 29 slides
Chemical Kinetics: Understanding Reaction Rates and Factors
Chemical kinetics is a branch of physical chemistry that explores the velocity and factors influencing chemical reactions. It studies how reactants transform into products, considering conditions like temperature, pressure, and reactant concentrations. Factors affecting reaction rates include the na
7 views • 24 slides
Automotive Sensing Systems & Radar Technology Overview
Explore the world of automotive sensing systems and radar technology including radar speed guns. Learn about the sensors used in cars for various applications such as radar cruise control, collision detection, and more. Discover the characteristics of these sensors and how they can be augmented or r
0 views • 7 slides
Quick & Reliable Towing Near Me Gastonia NC
In the world of automobiles, unforeseen circumstances can arise at any moment. Whether it's a flat tire, engine trouble, or an unfortunate collision, finding yourself stranded on the side of the road can be a stressful experience.
2 views • 5 slides
Safety and Responsibility: Transitioning to Secondary School
As students transition to secondary school, they are granted more freedom which comes with added responsibility. This period brings significant changes, including traveling to school independently, using public transport, walking, or cycling. However, there are risks involved, with statistics showin
0 views • 28 slides
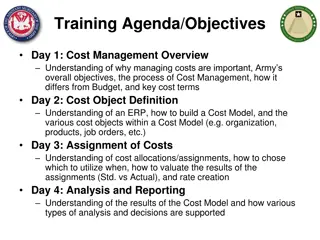
Comprehensive Cost Management Training Objectives
This detailed training agenda outlines a comprehensive program focusing on cost management, including an overview of cost management importance, cost object definition, cost assignment, analysis, and reporting. It covers topics such as understanding cost models, cost allocations, various types of an
2 views • 41 slides
Understanding Sediment Provenance in Geology
Sediment provenance in geology involves reconstructing the origin of sediments through compositional analyses to determine erosion history and geographical origins. It helps characterize the journey of sediments from source to sink, providing insights into tectonic and paleoclimatic histories. Prove
1 views • 11 slides
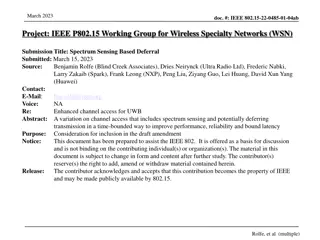
Spectrum Sensing for Enhanced Channel Access in Wireless Networks
This document presents a proposal for Spectrum Sensing Based Deferral (SSBD) to improve channel access in wireless networks. SSBD incorporates spectrum sensing with transmission deferral in a time-bound manner to enhance performance, reliability, and latency control. The proposed solution safeguards
1 views • 11 slides
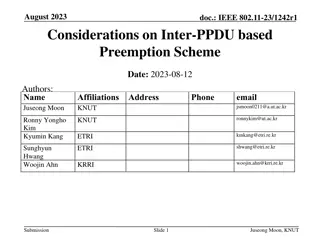
Considerations on Inter-PPDU Based Preemption Scheme in IEEE 802.11-23
In this document, considerations are presented for a preemption scheme in IEEE 802.11-23, focusing on issues such as coordination, ACK transmission timing, and channel access fairness. The proposed inter-PPDU based preemption scheme aims to improve the transmission of low latency traffics within the
1 views • 12 slides
Advanced Emergency Braking System (AEBS) Definition and Activation Guidelines
The provided content outlines the definition and activation requirements of the Advanced Emergency Braking System (AEBS). It covers the phases involved, including Collision Warning and Emergency Braking, as well as the speed limitations for activation. The system aims to automatically detect potenti
0 views • 12 slides
Study on Collective Flow and Participant Eccentricity in High-energy Heavy-ion Collisions
Explore the research on collective behavior, eccentricity, and flow of final state particles in high-energy heavy-ion collisions. Learn about the measurement of Fourier coefficients, azimuthal angles, and spatial anisotropy, as well as the analysis of system size dependence and radial flow in variou
1 views • 29 slides
Production in Collisions at 8-16 TeV: Analysis Overview
Detailed analysis overview of the production in collisions at 8-16 TeV incorporating contributions from Pavel Larionov (ITSsa), Paula Matuoka (TPC), Silvia Pisano (TPC), and Marco Toppi (TOF). The analysis involves the comparison of spectra data to previous datasets, emphasizing the importance of un
0 views • 50 slides
Legal Scenario Analysis: Liability in a Complex Situation
Tito, Mia, Omar, and Kashawn are involved in a series of incidents post a party, leading to varying degrees of injuries. Tito's red light violation causes a collision with a bicyclist, resulting in a subsequent car accident that leaves Mia severely injured. Omar suffers an allergic reaction to treat
0 views • 19 slides
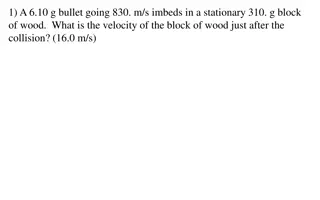
Physics Collision Problems Explained
Explore various collision scenarios involving bullets, blocks, cars, and people in this physics problem set. Calculate velocities, masses, and recoils to understand the dynamics of collisions and their effects on different objects involved.
0 views • 15 slides
Analysis of Automotive Paint Smears Using Charpy Impact Tester
The study focuses on developing a procedure utilizing a Charpy impact tester to generate and analyze automotive paint smears, particularly in crime scene investigations. These paint smears are complex mixtures of various paint layers, making analysis challenging. The impact-induced smearing process
0 views • 22 slides
Insights into LHC Experimental Physics: Lecture Highlights and Challenges
Delve into the world of experimental physics at LHC with lectures by Jon Butterworth at University College London in September 2016. Topics covered include accelerators, detectors, principles, and digressions, along with discussions on triggers, multi-level trigger systems, and collision selection m
0 views • 26 slides
Understanding Convex Hulls in Computational Geometry
Convex hulls play a vital role in computational geometry, enabling shape approximation, collision avoidance in robotics, and finding smallest enclosing boxes for point sets. The convex hull problem involves computing the smallest convex polygon containing a set of points, with extreme points determi
0 views • 119 slides
Understanding the Dynamics of Collision: Bug vs. Windshield
Explore the intriguing physics behind a bug hitting a windshield, delving into concepts like Newton's third law, momentum conservation, and the differences in force, time of impact, and change in velocity. Discover why a bug goes splat while a windshield remains intact in a collision scenario, with
0 views • 19 slides
Drone Collision Avoidance Simulator for Autonomous Maneuvering
Our project focuses on developing a drone collision avoidance simulator using NEAT and Deep Reinforcement Learning techniques. We aim to create a model that can maneuver obstacles in a 2D environment, enhancing performance and survivability. Previous attempts utilizing non-machine learning solutions
0 views • 28 slides
Conservation of Momentum in Collisions: University of Ottawa Physics Lab
Study the conservation of linear momentum and energy in elastic and inelastic collisions in one dimension at the University of Ottawa's physics lab. Analyze the motion of gliders on an air track, observe changes in velocity, momentum, and energy, and compare position-time and velocity vs. time graph
0 views • 15 slides
Advanced Techniques in Collider Physics for Enhanced Luminosity
Explore cutting-edge research on beam-beam effects, crab waist colliders, and luminosity optimization in collider physics. Discover how innovative strategies like crab waist technology and bunch crabbing mitigation are revolutionizing particle collision studies. Dive into the complexities of achievi
0 views • 10 slides
Introduction to Static Analysis in C.K. Chen's Presentation
Explore the fundamentals of static analysis in C.K. Chen's presentation, covering topics such as common tools in Linux, disassembly, reverse assembly, and tips for static analysis. Discover how static analysis can be used to analyze malware without execution and learn about the information that can
0 views • 54 slides
Understanding the Relationship between Decisional Second-Preimage Resistance and Preimage Resistance in Cryptographic Hash Functions
This work delves into the subtle question of when Decisional Second-Preimage Resistance (SPR) implies Preimage Resistance (PRE) in hash functions. It presents a tool for enabling tight security proofs for hash-based signatures by exploring the success probability of adversaries against collision res
0 views • 25 slides
Foundations of Cryptography: Digital Signatures and Collision-Resistant Hash Functions
Foundations of Cryptography explores the construction of digital signature schemes and collision-resistant hash function families using one-way functions and safe primes. The content delves into the concept of collision-resistant hash functions and their construction from the discrete logarithm prob
0 views • 31 slides
Foundations of Cryptography: Lecture 12 - Digital Signatures and Collision-Resistant Hash Functions
The lecture covers the construction of collision-resistant hash functions from discrete log, the security behind it, and the implications for digital signature schemes. It delves into the theoretical foundations of cryptography, showcasing the interplay between one-way functions, hash functions, and
0 views • 25 slides
Analysis of Preemption Methods in IEEE 802.11-23/2076r3 for Latency Reduction
Discussion on preemption methods in IEEE 802.11-23/2076r3 document focusing on latency reduction objectives. Topics include coordinated preemption, random channel access, comparison between methods, and the impact on STAs performance. The document addresses concerns such as collision probability, co
0 views • 8 slides
Industrial, Microbiological & Biochemical Analysis - Course Overview by Dr. Anant B. Kanagare
Dr. Anant B. Kanagare, an Assistant Professor at Deogiri College, Aurangabad, presents a comprehensive course on Industrial, Microbiological, and Biochemical Analysis (Course Code ACH502). The course covers topics such as Industrial Analysis, Microbiological Analysis, and Biochemical Analysis. Dr. K
0 views • 16 slides
Comprehensive Overview of CSE 373 Data Structures and Algorithms Course - Autumn 2018
This document provides detailed information about the CSE 373 Data Structures and Algorithms course in Autumn 2018, presented by Shrirang (Shri) Mare. It covers topics such as hashing, collision strategies, hash tables, design decisions, testing, and more. The content includes announcements, midterm
0 views • 25 slides
Privacy Address Requirements for Wireless Personal Area Networks
This document discusses the privacy address requirements for IEEE P802.15 Working Group's TG4ab standard for Wireless Personal Area Networks (WPANs). It covers the need for 48-bit addresses with collision resistance, the use of different privacy addresses for each frame, and the adequacy of 12-bit c
0 views • 8 slides
Benefits of Probabilistic Static Analysis for Improving Program Analysis
Probabilistic static analysis offers a novel approach to enhancing the accuracy and usefulness of program analysis results. By introducing probabilistic treatment in static analysis, uncertainties and imprecisions can be addressed, leading to more interpretable and actionable outcomes. This methodol
0 views • 11 slides
Understanding TCAS - Traffic Collision Avoidance System
A Traffic Collision Avoidance System (TCAS) is a vital aircraft collision avoidance technology that helps reduce mid-air collisions by monitoring the airspace around an aircraft. TCAS operates independently of ground-based equipment and advises pilots on potential conflicting aircraft. Mandated by t
0 views • 13 slides
Vehicle Safety Protocols: Handling Tire Blows, Brake Failure, and More
Learn essential actions for handling emergencies like tire blowouts, brake failure, stuck accelerator, and steering failure. Additionally, understand off-road recovery, minimizing damage due to potholes, and escaping from a sinking vehicle. Discover collision avoidance techniques and steps to take i
0 views • 9 slides
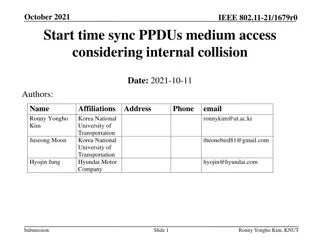
Understanding Start Time Sync Procedures in IEEE 802.11-21/1679r0
In the document authored by Ronny Yongho Kim et al., the focus is on start time sync PPDU medium access considering internal collision in IEEE 802.11-21/1679r0. It discusses the importance of defining a clear rule to resolve internal collision cases during medium access procedures. Specific attentio
0 views • 9 slides
Understanding Kinematics Challenges in High-Energy Physics Experiments
Delve into the complex world of kinematics in high-energy physics research, exploring challenges faced in collision simulations and event analysis. Discover how concepts like light-cone variables and covariant definitions play a crucial role in interpreting scattered electron data. Explore practical
0 views • 11 slides
Understanding Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
0 views • 40 slides
MitM Attack by Name Collision: Implications and Vulnerability Assessment
In this research study, the authors delve into the risks and vulnerabilities associated with Man-in-the-Middle (MitM) attacks exploiting name collision in the era of new generic Top-Level Domains (gTLDs). The study highlights how attackers can intercept web traffic by manipulating vulnerable domains
0 views • 25 slides
Proposed Guidance for Fixed Objects in Roadside Design
This presentation covers the development of design guidance aimed at mitigating collisions with roadside fixed objects, focusing on trees and utility poles. With a high number of traffic fatalities resulting from roadway departures involving such objects, the research objective is to provide enginee
0 views • 22 slides