Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding Cellular Pathology: Response to Stress and Disease Predisposition
Explore the hallmarks of cellular pathology, including factors influencing disease predisposition such as genetics, environmental factors, and lifestyle. Delve into the cellular response to stress, adaptive and pathological reactions, and key stressors disrupting cellular homeostasis. Uncover how ce
0 views • 51 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Understanding Motor Proteins and Cytoskeletal Dynamics in Cell Biology
Motor proteins, such as myosin, kinesin, and dynein, utilize chemical energy to move along cellular tracks, influencing processes like muscle contraction, organelle movements, and cellular migration. With the ability to translocate using ATP hydrolysis, these proteins play crucial roles in various c
5 views • 14 slides
Understanding Cellular Respiration and Metabolism in Living Organisms
Cellular respiration is a vital process in all living cells, producing energy through chemical reactions. Metabolism, consisting of anabolism and catabolism, maintains growth and function. ATP plays a central role as energy currency in cells. Through stages like glycolysis and the Krebs cycle, cellu
0 views • 16 slides
Understanding Cellular Respiration and Oxygen Delivery
Cellular respiration, a vital process for organ survival, involves mitochondria performing cellular respiration by utilizing glucose and oxygen. Glucose is derived from diet or body breakdown, while oxygen enters through the respiratory system, facilitated by red blood cells in the circulatory syste
0 views • 8 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Neo.Go Mobile Application Integration Settings
This guide provides detailed instructions for integrating the Neo.Go mobile application with Neo security system panels using Ethernet or Cellular communication. It covers programming steps, data plan considerations, and settings for both Cellular and Ethernet communications. Ensure a proper data pl
0 views • 26 slides
Understanding Wireless Wide Area Networks (WWAN) and Cellular Network Principles
Wireless Wide Area Networks (WWAN) utilize cellular network technology like GSM to facilitate seamless communication for mobile users by creating cells in a geographic service area. Cellular networks are structured with backbone networks, base stations, and mobile stations, allowing for growth and c
2 views • 17 slides
Overview of Cellular Respiration Pathways and ATP Generation
Cellular respiration involves key processes like the Tricarboxylic Acid Cycle (TCA), Electron Transport Chain, and ATP generation pathways. The TCA cycle utilizes Acetyl-CoA to produce energy-rich molecules, while the Electron Transport Chain facilitates ATP synthesis through oxidative phosphorylati
0 views • 18 slides
Explore Cellular Respiration Through POGIL Activities
Dive into the world of cellular respiration through POGIL activities that cover topics such as glycolysis, Krebs Cycle, Electron Transport System, and more. Discover critical thinking questions and application problems related to cellular respiration processes and their real-world implications.
0 views • 6 slides
Cellular Fractionation: Techniques and Applications
Cellular fractionation is a crucial process for separating cellular components to study intracellular structures and proteins. It involves homogenization, centrifugation, and purification steps to isolate organelles based on their properties like density and shape. This method provides valuable insi
6 views • 11 slides
Cellular Network Security Threats and Solutions
This article delves into the security aspects of cellular networks, focusing on threats such as charging fraud, unauthorized use, handset cloning, voice interception, location tracking, and network service disruptions. It also explores the security architecture involving Home Location Register (HLR)
0 views • 28 slides
Understanding Cellular Injury and Its Manifestations
Cellular injury can occur due to various factors like physical trauma, chemicals, radiation, and biologic agents. This process can lead to reversible or irreversible damage in cells, affecting their normal functions and possibly leading to cell death. Manifestations of cellular injury include cellul
0 views • 9 slides
Introduction to Histology and Cell Structure
Histology is the microscopic study of normal tissues utilizing light and electron microscopes. This field explores the composition and function of cells, focusing on the nucleus, cytoplasm, organelles, and inclusions. Thin tissue sections stained with Haematoxylin and Eosin reveal distinct cellular
0 views • 23 slides
Exploring Cellular Structures in Quizbowl Biology
Biology in quizbowl competitions often focuses on understanding cellular structures, from organs to organelles. Players encounter questions about various organelles like mitochondria, ribosomes, chloroplasts, and the Golgi body. Ribosomes, though not classified as organelles, play a critical role in
0 views • 27 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Understanding Enzymes: The Catalysts of Cellular Reactions
Enzymes play a vital role in controlling cellular reactions by speeding up processes without being consumed themselves. They are biological catalysts made of proteins, with each enzyme having a specific shape for its designated molecule. This summary highlights the importance of enzymes in cellular
0 views • 47 slides
Highlights from the 3rd International Workshop on Cellular and Molecular Biology
Explore images from the 3rd International Workshop on Cellular and Molecular Biology showcasing various aspects of the event and the participation of experts in the field. Dive into the world of cellular and molecular biology through these visual representations.
0 views • 10 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
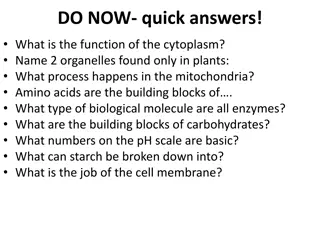
Cellular Processes and Functions Explained
The cytoplasm is essential for cell function, housing organelles like chloroplasts and vacuoles unique to plants. Mitochondria facilitate cellular respiration, while amino acids form proteins. Enzymes are proteins, and carbohydrates consist of simple sugars. Basic pH numbers range from 8 to 14. Star
0 views • 24 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Exploring Cellular Biology: From Cells to DNA
Delve into the intricacies of cellular biology by comparing prokaryotic and eukaryotic cells, investigating cellular processes, understanding viral structures and reproduction, exploring the cell cycle stages, examining specialized cells, and recognizing the crucial roles of DNA and RNA in cell diff
0 views • 42 slides
Understanding Cellular Respiration: Energy Production in Organisms
Organisms can be classified into autotrophs that use sunlight for photosynthesis and heterotrophs that rely on consuming food. Regardless of food source, all organisms obtain energy through cellular respiration, a process that converts stored chemical energy into ATP. This energy currency is essenti
0 views • 21 slides
Energy-Efficient Handover Triggering for Cellular Networks
Mobile devices play a crucial role in today's world, with a surge in mobile subscriptions and applications. However, energy consumption, particularly battery life, remains a challenge. The study focuses on Application-Based Handover Triggering (AHT) as a solution to optimize energy usage in cellular
0 views • 24 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Introduction to Animal Physiology and Cellular Biology Overview
This comprehensive course delves into the fundamental aspects of animal physiology and cellular biology. Topics covered include the characteristics of living organisms, cellular organelles, the cell cycle, division, growth, and death. Additionally, the course introduces the various animal phyla, fro
0 views • 43 slides
Understanding the Types of Endosperm in Angiosperms
Endosperm is the nutritive tissue formed in angiosperms through triple fusion, serving to nourish the embryo. There are three main types of endosperm: Nuclear, Cellular, and Helobial, each characterized by distinct modes of development. Nuclear endosperm features repeated division of the primary nuc
0 views • 16 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Alternative Cellular Avalanche Model for Solar Flares
Exploring an alternative cellular avalanche model based on the maximum release of energy during solar flares, this research delves into optimizing models to study the quasi-static evolution of coronal magnetic fields. Through a series of image objects and studies, the study presents various cellular
0 views • 16 slides
Understanding Cellular Traffic Accounting and TCP Retransmissions
Delve into the complexities of cellular traffic accounting, focusing on the impact of TCP retransmissions on network data billing. Explore the challenges faced by cellular providers in accurately charging subscribers for data usage amidst increasing traffic volumes. Consider the implications of TCP
0 views • 31 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Cellular Network Positioning Techniques for Location Estimation
Utilizing cellular signal strength information for positioning devices within a network, this study explores network-side positioning methods such as fingerprinting in cellular networks. The research delves into the process of estimating device locations by analyzing received signal strengths from n
0 views • 29 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides