Data Augmentation Techniques for Deep Learning-Based Medical Image Analyses
Various data augmentation techniques for improving deep learning-based medical image analyses. It covers topics such as overfitting, data labeling, and the use of generative adversarial networks (GANs).
2 views • 14 slides
Adversarial Machine Learning in Cybersecurity: Challenges and Defenses
Adversarial Machine Learning (AML) plays a crucial role in cybersecurity as security analysts combat continually evolving attack strategies by malicious adversaries. ML models are increasingly utilized to address the complexity of cyber threats, yet they are susceptible to adversarial attacks. Inves
4 views • 46 slides
CS 404/504 Special Topics
Adversarial machine learning techniques in text and audio data involve generating manipulated samples to mislead models. Text attacks often involve word replacements or additions to alter the meaning while maintaining human readability. Various strategies are used to create adversarial text examples
1 views • 57 slides
Adversarial Machine Learning in Cybersecurity
Adversarial Machine Learning (AML) is a critical aspect of cybersecurity, addressing the complexity of evolving cyber threats. Security analysts and adversaries engage in a perpetual battle, with adversaries constantly innovating to evade defenses. Machine Learning models offer promise in combating
1 views • 43 slides
Adversarial Attacks in Machine Learning
Adversarial attacks in machine learning aim to investigate the robustness and fault tolerance of models, introduced by Aleksander Madry in ICML 2018. This defensive topic contrasts with offensive adversarial examples, which seek to misclassify ML models. Techniques like Deep-Fool are recognized for
1 views • 29 slides
Adversarial Machine Learning Attacks
Adversarial Machine Learning (AML) involves attacks on machine learning models by manipulating input data to deceive the model into making incorrect predictions. This includes creating adversarial examples, understanding attack algorithms, distance metrics, and optimization problems like L-BFGS. Var
0 views • 88 slides
Adversarial Threats in Machine Learning
This document explores the world of adversarial threats in machine learning, covering topics such as attack nomenclature, dimensions in adversarial learning, influence dimension, causative and exploratory approaches in attacks, and more. It delves into how adversaries manipulate data or models to co
0 views • 10 slides
Limitations of Deep Learning in Adversarial Settings
Deep learning, particularly deep neural networks (DNNs), has revolutionized machine learning with its high accuracy rates. However, in adversarial settings, adversaries can manipulate DNNs by crafting adversarial samples to force misclassification. Such attacks pose risks in various applications, in
0 views • 38 slides
Adversarial Risk Analysis for Urban Security
Adversarial Risk Analysis for Urban Security is a framework aimed at managing risks from the actions of intelligent adversaries in urban security scenarios. The framework employs a Defend-Attack-Defend model where two intelligent players, a Defender and an Attacker, engage in sequential moves, with
2 views • 26 slides
Secure Multiparty Computation: Enhancing Privacy in Data Sharing
Secure multiparty computation (SMC) enables parties with private inputs to compute joint functions without revealing individual data, ensuring privacy and correctness. This involves computations on encrypted data using techniques like homomorphic encryption for scenarios like e-voting. SMC serves as
2 views • 27 slides
Adversarial Learning in ML: Combatting Internet Abuse & Spam
Explore the realm of adversarial learning in ML through combating internet abuse and spam. Delve into the motivations of abusers, closed-loop approaches, risks of training on test data, and tactics used by spammers. Understand the challenges and strategies involved in filtering out malicious content
1 views • 13 slides
Distillation as a Defense Against Adversarial Perturbations in Deep Neural Networks
Deep Learning has shown great performance in various machine learning tasks, especially classification. However, adversarial samples can manipulate neural networks into misclassifying inputs, posing serious risks such as autonomous vehicle accidents. Distillation, a training technique, is proposed a
3 views • 31 slides
Robustness to Adversarial Examples in Machine Learning
Explore the vulnerability of machine learning models to adversarial examples, including speculative explanations and the importance of linear behavior. Learn about fast gradient sign methods, adversarial training of deep networks, and overcoming vulnerabilities. Discover how linear perturbations imp
0 views • 37 slides
Adversarial Attacks on Post-hoc Explanation Methods in Machine Learning
The study explores adversarial attacks on post-hoc explanation methods like LIME and SHAP in machine learning, highlighting the challenges in interpreting and trusting complex ML models. It introduces a framework to mask discriminatory biases in black box classifiers, demonstrating the limitations o
3 views • 18 slides
Game Playing and Adversarial Search at University of Berkeley
Delve into the realm of game playing and adversarial search at the University of Berkeley to understand the complexities of multi-agent environments. Explore the concepts of competitive MA environments, different kinds of games, and the strategic decision-making processes involved in two-player game
0 views • 81 slides
Understanding Zero-Shot Adversarial Robustness for Large-Scale Models
Pretrained large-scale vision-language models like CLIP show strong generalization on unseen tasks but are vulnerable to imperceptible adversarial perturbations. This work delves into adapting these models for zero-shot transferability in adversarial robustness, even without specific training on unk
1 views • 18 slides
Evaluating Adaptive Attacks on Adversarial Example Defenses
This content discusses the challenges in properly evaluating defenses against adversarial examples, highlighting the importance of adaptive evaluation methods. While consensus on strong evaluation standards is noted, many defenses are still found to be vulnerable. The work presents 13 case studies o
0 views • 9 slides
Adversarial Search in Artificial Intelligence
Adversarial search in AI involves making optimal decisions in games through concepts like minimax and pruning. It explores the strategic challenges of game-playing, from deterministic turn-taking to the complexities of multi-agent environments. The history of computer chess and the emergence of huma
0 views • 56 slides
Foundations of Artificial Intelligence: Adversarial Search and Game-Playing
Adversarial reasoning in games, particularly in the context of artificial intelligence, involves making optimal decisions in competitive environments. This module covers concepts such as minimax pruning, game theory, and the history of computer chess. It also explores the challenges in developing AI
0 views • 56 slides
Machine Learning for Cybersecurity Challenges: Addressing Adversarial Attacks and Interpretable Models
In the realm of cybersecurity, the perpetual battle between security analysts and adversaries intensifies with the increasing complexity of cyber attacks. Machine learning (ML) is increasingly utilized to combat these challenges, but vulnerable to adversarial attacks. Investigating defenses against
0 views • 41 slides
Adversarial Search and Minimax Algorithm in Games
Competitive games create conflict between agents, leading to adversarial search problems. The Minimax algorithm, used to optimize player decisions, plays a key role in analyzing strategies. Studying games offers insights into multiagent environments, economic models, and intellectual engagement. The
1 views • 17 slides
Efficient Image Compression Model to Defend Adversarial Examples
ComDefend presents an innovative approach in the field of computer vision with its efficient image compression model aimed at defending against adversarial examples. By employing an end-to-end image compression model, ComDefend extracts and downscales features to enhance the robustness of neural net
0 views • 16 slides
Defense Against Adversarial Images using Web-Scale Nearest-Neighbor Search
This study explores a method to defend against adversarial images by approximating their projection onto the image manifold through nearest-neighbor search. The approach involves finding the nearest neighbors in a web-scale image database to classify and mitigate the impact of adversarial perturbati
0 views • 15 slides
Intelligent Information Processing Lab – Seminar Insights
The Intelligent Information Processing Lab seminar delved into advanced techniques such as deep learning approaches, geometric transformations, color space transformations, and adversarial training. With a focus on plant image data augmentation, the lab showcased innovative methodologies such as GAN
0 views • 8 slides
Spectral Normalization for Generative Adversarial Networks
Spectral normalization is a technique used in Generative Adversarial Networks (GANs) to address issues like non-convergence, mode collapse, and gradient problems. By normalizing the spectral norm of weight matrices, SN helps stabilize training and improve quality. Explore the benefits and applicatio
0 views • 22 slides
Automatic Modulation Recognition Using Generative Adversarial Networks
In the realm of spectrum sensing, the demand for automatic modulation recognition (AMR) has intensified due to the scarcity of spectrum resources. This study delves into the utilization of Generative Adversarial Networks (GAN) to automate AMR, a departure from manual methods. By employing GAN's gene
0 views • 13 slides
Generative Adversarial Networks
In this informative content, explore the concepts of generative adversarial networks, synthetic data, hand shapes, 3D hand orientation, hand pose estimation applications, and labeling data for hand pose. Discover how synthetic data is used in training, the flexibility of hand shapes, the impact of 3
0 views • 60 slides
General Framework of GAN
fGAN is a framework that evaluates the difference between two distributions by utilizing f-divergence, with f being a convex function. This concept can be understood through examples like KL divergence, Reverse KL divergence, and Chi-Square. Additionally, the Fenchel Conjugate method plays a crucial
0 views • 14 slides
Adversarial Machine Learning in Cybersecurity
Explore the realm of adversarial machine learning in cybersecurity focusing on malware detection and classification. Understand the evolving nature of malware and the threat it poses to computer systems. Discover automated detection versus classification systems and the role of machine learning in c
0 views • 49 slides
Adversarial Examples in Neural Networks
Adversarial examples in neural networks refer to inputs intentionally modified to cause misclassification. This phenomenon occurs due to the sensitivity of deep neural networks to perturbations, making them vulnerable to attacks. By understanding the generation and impact of adversarial examples, re
0 views • 14 slides
Algorithms and Game Theory Overview
An overview of algorithms, uninformed and informed searches, heuristics, adversarial searches, and game theory. Explore the concepts with examples like the Prisoner's Dilemma and deterministic games in multiagent environments. Learn about the application of game theory in AI and how games are well-s
0 views • 49 slides
Workshop on Adversarial Machine Learning and Voice Assistant Vulnerabilities
Explore the innovative discussions at the AIMCOM2 Workshop on Adversarial Machine Learning and Voice Assistant Vulnerabilities, featuring insights from Ananthram Swami and Yingying Chen on critical topics in network protocols and edge computing. Discover the latest advancements in detecting and defe
0 views • 4 slides
Practical Byzantine Agreement in Distributed Systems: Exploring Protocols and Adversarial Scenarios
Delve into the dynamics of achieving Byzantine agreement in distributed systems through protocol design, adversarial scenarios, and the use of randomized algorithms. Understand the challenges posed by untrusted players and the importance of public ledgers and digital currencies.
0 views • 34 slides
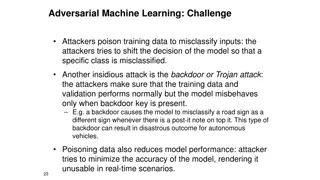
Understanding Adversarial Machine Learning Attacks and Defenses
Learn about the challenges posed by adversarial machine learning attacks such as poisoning and evasion, and explore offensive and defensive strategies to protect machine learning models. Discover how attackers manipulate training data to misclassify inputs and how defenders can counter such attacks
1 views • 9 slides
Adversarial Search in Competitive Environments: A Deep Dive
Delve into the world of adversarial search in competitive environments where agents strategize against each other, focusing on zero-sum games like chess. Explore game setup, minimax strategy, and the challenges of decision-making in adversarial settings.
0 views • 21 slides
Powerful Generative Adversarial Networks in Medical Imaging
Discover the power of Generative Adversarial Networks (GANs) in medical imaging, where two neural networks collaborate to generate realistic images and handle domain shifts. Explore challenges, popular GAN models like CycleGAN and ProGAN, and potential solutions for diverse image synthesis across do
0 views • 8 slides
Understanding Neural Network Robustness from a Probabilistic Perspective
Explore the intriguing behavior of neural networks, the discovery of adversarial examples, challenges in training robust networks, and the shift towards non-adversarial robustness considerations. Learn about local and global robustness specifications and the probabilistic view on maintaining neural
1 views • 12 slides
Julia Machine Learning: Adversarial Algorithms & Practical Applications
Discover the world of adversarial machine learning in Julia, including the intricacies of adversarial algorithms, distance metrics, and practical applications such as malware detection. Learn why Julia is a preferred language for machine learning tasks and how it excels in optimization challenges. U
0 views • 9 slides
Understanding Adversarial Learning in ML: Internet Abuse & Spam
Explore the complexities of adversarial learning in machine learning, focusing on combating internet abuse and spam. Discover the motivations behind online abuse, the closed-loop approach to filter spam, risks of training on test data, and tactics used by spammers. Gain insights into the challenges
0 views • 13 slides
Adversarial Search and Minimax Algorithm Overview
Explore supplemental slides covering adversarial search in CSE 327 with Prof. Jeff Heflin, including Tic-Tac-Toe transition models, the Minimax Algorithm, utility-based agents, and Minimax with cutoff limits. Understand how these concepts are used in decision-making processes for game-playing agents
0 views • 5 slides