Unveiling Incompressible Cryptography Techniques
Explore the fascinating world of incompressible cryptography techniques, including forward secrecy, deniable encryption, multi-round protocols, and more. Dive into the concepts of disappearing cryptography, memory-bound encryption, and bounded storage models to secure data effectively in various scenarios.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
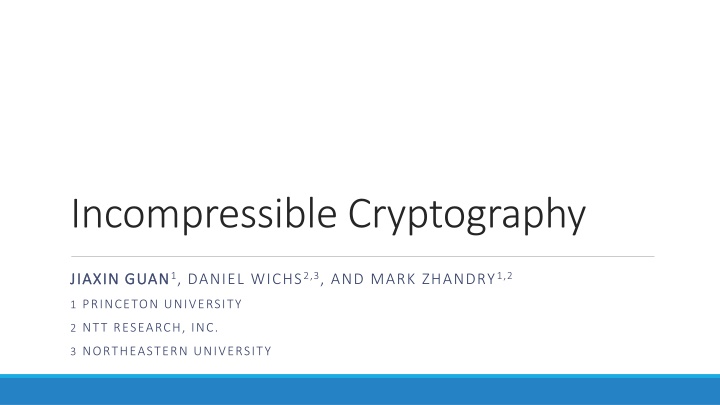
Incompressible Cryptography JIAXIN GUAN JIAXIN GUAN1, DANIEL WICHS2,3, AND MARK ZHANDRY1,2 1 PRINCETON UNIVERSITY 2 NTT RESEARCH, INC. 3 NORTHEASTERN UNIVERSITY
Forward Secrecy Hi, Bob! Here is a super secret QR code. For your eyes only!!! Multi-Round Protocols Key Updates
Receiver-Deniable Encryption [CDNO97] funny cat image Impossible in the standard model! [BNNO11]
Replay Attack Party Tonight Multi-Round Protocols Party Tonight Synchronized Clocks Stateful Verifier
What if the adversary cannot store the ciphertext / signature?
Party Tonight Party Tonight
Key Idea: Manually blow up the ciphertext / signature size
Disappearing Cryptography in the Bounded Storage Model [G GZ21]
Traditionally Bounded Storage Model [Mau92] = poly(?) = ?(?) fixed poly. ?
Disappearing PKE [G GZ21] ? ??,?? ,? ?? ?0,?1 Enc(??,??) ? ??
Memory Bound for Adv. Adv. 1 Adv. 2 Storage Storage ? Time Time
Incompressible PKE Security ? ??,?? ,? ?? ,aux ?0,?1 Enc(??,??) st ?.?. st ? ?? ? ,??,aux,st Implies Disappearing PKE Security!
Feature: Low Space Streaming BSM requires honest parties run protocol with lower storage bound Enc, Dec, Sig, Ver runs in low space Incompressible PKE + Low Space Streaming -> Disappearing PKE
Feature: Rate 1 Low Rate PKE: Rate-1 PKE: ? ? ct ct
Key Idea: Manually blow up the ciphertext / signature size Entropy
This Work: Incompressible Cryptography Incompressible Signatures (low rate) Incompressible Signatures (rate 1) Incompressible PKE (low rate) Incompressible PKE (rate 1) >> >> Incompressible Encodings [MW20] Standard Model PKE One Way Functions Indistinguishability Obfuscation (iO)
Thank you! eprint.iacr.org/2021/1679 jiaxin@guan.io