Comparative Analysis of Privacy and Cybersecurity Laws in India and the United States
Explore the distinct frameworks governing information privacy and cybersecurity in India and the United States through the lens of legal expert Professor Peter Swire. Covering constitutional, statutory, and self-regulatory laws, the discussion delves into key themes like encryption, the Google Buzz settlement, and the evolving landscape of cyber risks. Gain insights into the historical contexts and legal developments shaping these crucial aspects of digital governance.
Uploaded on Sep 08, 2024 | 2 Views
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
Privacy and Cybersecurity Law in India and the U.S. Professor Peter Swire Ohio State University Delhi University Law Centre March 31, 2011
Overview Theme the rules about information are important in the information age Information privacy Constitutional law Statutory and self-regulatory law, with Indian proposal under development Google Buzz settlement this week Cybersecurity Risk-adjusted efforts for security, Indian proposal under development Encryption Current controversy on RIM/Blackberry, Skype, etc. Reasons why the US decided to support strong crypto after intense debate in the 1990s Disclaimer I am not an expert on Indian law, but have been working on specific issues related to encryption and will have research paper this year on that
Swire Background Law professor since 1990 First Internet law writing 1992 Chief Counselor for Privacy to President Clinton, 1999-2001 Big growth of Internet, and first U.S. national laws on medical privacy, financial privacy, Internet privacy Wiretaps and other surveillance law for Internet (not just phones) Encryption, big U.S. legal shift in 1999 Special Assistant to President Obama, 2009-2010 Issues included broadband, spectrum, privacy, cybersecurity Theme: blend law, technology, business, government
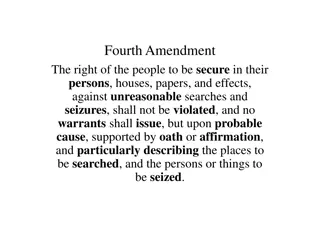
U.S. Constitution 4thAmendment to Constitution (in effect 1789) Protects a reasonable expectation of privacy against government search Usually require warrant signed by judge to do search or seizure , such as entry to a home or business Wiretaps for law enforcement generally require a warrant Very complex case law
U.S. Constitution 1stAmendment to Constitution (in effect 1789) Strong rules against state limits on free speech or free press Important in case law about personal privacy Common law protections for individual privacy Public revelation of private facts, or false light about a person Intrusion on seclusion Protect a celebrity or other person s right of publicity rule is that other person can t make money off of the celebrity s name (no advertisement suggesting Tandulkar supports your product without his permission) But 1stAmendment guarantees free speech Newspaper can make money with Tandulkar s name in headline Many revelations of your personal life are protected speech
Statutes for Private Sector Data In U.S. (and, I understand, India) no similar constitutional/human right to limit processing of personal information by private sector European Convention on Human Rights, implemented in E.U. Data Protection Directive, does treat this as a human right U.S. Congress has passed statutes for some sensitive types of information HIPAA for medical privacy Gramm-Leach-Bliley for financial services Telecom Act of 1996 for data held by phone companies Children s Online Privacy Protection Act for information collected from under-13s Video Privacy Protection Act for movie rentals (Judge Bork)
Statutory Protections & Fair Information Practices For HIPAA, European laws, and other possible private-sector laws, have FIPS On Internet, often done by self-regulation promises like statutes Notice how the personal data will be used Choice We have business partners who may have offers. Do you want your data shared? Opt in: don t use data unless affirmative consent; aps for FB Opt out: use data unless customer says no (tick box already checked but you can uncheck it) Access see your medical or other records Data security -- doesn t help to have privacy rules if the 12 year old can hack in Accountability consequences if don t follow the rules
Accountability HIPAA enforced by U.S. Department of Health and Human Services Patient complaints Opportunity for hospital, etc., to fix problem Consent decrees & penalties $1 million penalty last month for hospital Federal Trade Commission enforces against unfair and deceptive trade practices , notably including broken privacy promises This week, consent decree for Google Buzz New service, log in, Sweet, send me to Buzz! G signed Gmail users up for this new social network, saying unless you ticked Nah, send me to my inbox Claim Google broke its privacy policy and violated the U.S.-E.U. Safe Harbor Google promises now comprehensive privacy program, with 20 years of outside privacy audits
Hi Kenesa: I ll be talking about encryption on April 11. Also, Beyond FIPS: Legal Conflicts Often have intersection of a privacy rule (don t share data) and some other public policy purpose (need to share data) An example from HIPAA: doctor or hospital, and someone arrives who did/might have broken the law. Should the doctor report to the police? Perspective of the doctor? Hippocratic Oath? Why have that? Perspective of the police? Knife wound? IV drug user? History of this in HIPAA This question raised to me this week in India by a national security official When is disclosure required/permitted/forbidden?
Cybersecurity Protections Already saw that security is an element of privacy FIPS Don t steal from my bank account Don t reveal my medical or surfing records Government agencies and don t reveal secret government information Basic idea of many cybersecurity laws: Must have risk-adjusted security provisions HIPAA, GLB, U.S. government (FISMA) Online policies promise reasonable security , so FTC enforcement Some common elements Responsible officials Policies, training Identify areas of greatest risk, e.g., bank accounts vs. marketing materials Good idea to specify technology? 40-bit? Have a firewall? No.
Hi Kenesa: I ll be talking about encryption on April 11. Also, Also, Hi Kenesa: I ll be talking about encryption on April 11. Summary Thus Far Constitutional provisions, especially about government intrusion into personal space Statutes privacy FIPs, risk-weighted cybersecurity Beyond statutes to self regulation , but have enforcement Interesting legal issues where conflicts between reasons to share data and to limit data flows Goal of an overall regime where important things are protected and important data uses also succeed Next current controversy about encryption Idea of encryption: Alice sends to Bob; she wraps her text in code, and only he can decode it Current statute in India from 1998 encryption bit length maximum 40 bits Current banking regulators encryption bit length minimum 128 bits RIM/Blackberry and should messages be available to a government in the clear, in real time?
Phone call Alice Local switch Telecom Company Local switch Phone call Bob
Phone call Alice Local switch Telecom Company Local switch Phone call Bob
Hi Bob! Alice Alice ISP %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% Internet : Many Nodes betwee n ISPs %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% %!#&*YJ#$ &#^@% Bob ISP Hi Bob! Bob
Problems with Weak Encryption Nodes between A and B can see and copy whatever passes through Brute force attacks became more effective due to Moore s Law ; today, 40 bits very easy to break by many From a few telcos to many millions of nodes on the Internet Hackers Criminals Foreign governments Amateurs Strong encryption as feasible and correct answer Scaled well as Internet users went over one billion
U.S. Experience 1990s Initial inter-agency victory for law enforcement (FBI) and national security (NSA), early-mid 90 s Fear of loss of ability to wiretap Strong crypto within US Exports were controlled, on idea that crypto = munition Political system supports law enforcement and national security Sept. 1999, shift in U.S. policy to allow strong crypto for export I chaired WH working group on encryption 1999 Part of WH announcement 1999 of shift to strong crypto exports Why the change to position contrary to view of law enforcement and security agencies?
Crumbling of Weak Crypto Position Futility of weak crypto rules Meeting with Senator or Congressman Start the clock, how long to search for encryption download ? Get PGP or other strong crypto in less than one minute In world of weak crypto rules, effect on good guys and bad guys Bad guys download PGP, stop the wiretap Good guys follow the rules, legitimate actors get their secrets revealed Banking, medical records, retail sales The military s communications on the Internet, government agencies, critical infrastructure
Objection We Want the Keys The failure of the Clipper Chip Idea was that all users of strong crypto would escrow their keys with law enforcement Advocates for it had various safeguards, e.g., two people in the government had to agree for the key to be revealed Very strong technical arguments against this Some people didn t trust the government If do this for 200 nations worldwide, more people don t trust all the governments Single point of failure if the databank of keys is ever revealed, most/all communications can be read Personal communications Corporate secrets Government communications over the Internet
Objection We Want the Keys Even apart from key escrow, is useful to walk briefly through how public key encryption works, to show limits of requests for we want the keys Basic approach of public key encryption RSA a well-known instance of this approach Alice and Bob each have a public key that anyone can wrap plaintext with They each have a private key that is the only way to unwrap the encrypted text (unless someone tries brute force or other attack) Wrapping like multiplication (multiply two huge prime numbers); unwrap is like division (find the two primes); cryptosystem is one-way function
1 Hi Bob! Encrypt Bob's public key Alice Encrypted message %!#&YJ@$ Alice's local ISP %!#&YJ@$ Backbone provider %!#&YJ@$ Bob's local ISP %!#&YJ@$ Hi Bob! Decrypt Bob's private key Bob
2 Encrypt Hi Fred! Jill at Corporation A, Tata Public key of Corporation B Reliance Encrypted message %!#&YJ@$ Corporation A's ISP Lawful process: (1) Ask Tata before encryption (2) Ask Reliance after decryption %!#&YJ@$ Backbone provider %!#&YJ@$ Corporation B's ISP %!#&YJ@$ Decrypt Hi Fred! Private key of Corporation B, Reliance Fred at Corporation B Reliance.
Limits to Getting the Keys In many instances, the keys are held by Alice and Bob No one else has the keys That can include the software maker or service provider Can be encryption at rest your laptop Keep a backup, or else computer brickifies Can be encryption in communication You may be only one with access to the private key, in some systems select it yourself or it is created by a one- way function where the originator has no access Technical experts prefer/insist on this
Objection Isnt There a Back Door? As with Clipper Chip, law enforcement would love to have a back door Back door = designed security flaw in the system May be that law enforcement only can read (Clipper Chip) May be that software/service provider can read (they promise security but keep a secret way in) Goal of back door: All the good guys can get in (and know they can ask for it) No one else, including bad guys, get in: Criminals and their hackers Foreign governments and spy services Ph.D. computer experts White hat hackers people who detect flaws and tell CERTs and others about them
The Likelihood of Back Doors? Let s think through the likelihood that widely-used strong encryption actually has back doors for some law enforcement/national security agencies My view much less likely than many people think Swire writings on when secrecy helps/hurts security Key point is that secrecy not likely to be successful when there are many attackers, who can attack repeatedly, and can report successful attacks A simpler way to say this: Wikileaks What likelihood that the FBI has been pervasively using a backdoor, with knowledge of software/services companies, and it hasn t leaked since 1999 approval of strong crypto? What likelihood that none of the smart Ph.Ds and white hat hackers have ever found an example of this? What brand effect on Microsoft (Bit Locker) and other global brands if they promised security and secretly broke it? What penalties for fraud?
Why We Dont Want Weak Cybersecurity Key point so far on encryption weak crypto is weak cybersecurity A world full of attackers can and will read data sent over the Internet unless there is strong crypto Indian and all other governments have spoken strongly about the need for strong cybersecurity Numerous quotes about the need for strong cybersecurity Cyber warfare and threats to cyber security are fast becoming the next generation of threats. We need to make our cyber systems as secure and as non-porous as possible. Indian Defense Minister, Shri A.K. Antony, May 2010 Critical infrastructure open to attack Financial system Medical records and other sensitive personal information Including records used in cross-border provision of services
Lack of Strong Crypto as Legal Violation Strong crypto increasingly becoming legal requirement State of Massachusetts computer security law now in effect Strict penalties for loss of laptop or other loss of data unless strong encryption in place U.S. funding of $19 billion for electronic health records Rules for reimbursement Strong encryption is expected to qualify for funding More generally, numerous laws worldwide require cost-effective security measures, on pain of penalties What is adequate protection under E.U. law? For instance, Gramm-Leach-Bliley safeguards rule for U.S. financial services With strong crypto low-cost and pervasive, its absence violates many laws
Conclusion Privacy and cybersecurity are key information law issues for the information age New generation of lawyers will become expert on these topics International Association of Privacy Professionals, from 140 people in 2001 to over 2000 people at the conference this year, over 7000 members (CIPP certification) Intellectually interesting law to match cutting-edge technology, trying to govern global data flows For lawyers who understand the needs of technology, business, and government, the chance to build a better Information Society Come aboard for this interesting ride