Public key encryption, Digital signature and authentication
Understand the concept of public key encryption, asymmetric encryption, and the widely used RSA algorithm. Explore how public key cryptography revolutionized the field of encryption and its applications in confidentiality, authentication, and key distribution.
4 views • 12 slides
Go Green and Stylish with Eco-Friendly Wooden USBs
Put a natural twist on your branding with a wooden USB from Wholesale USB.Ditch the ordinary and embrace a unique, eco-friendly option that speaks volumes about your commitment to sustainability. Imagine the warm feel of real wood in your hand, engraved with your logo for a lasting impression. Not j
1 views • 4 slides
Go Green and Stylish with Eco-Friendly Wooden USBs
Put a natural twist on your branding with a wooden USB from Wholesale USB.Ditch the ordinary and embrace a unique, eco-friendly option that speaks volumes about your commitment to sustainability. Imagine the warm feel of real wood in your hand, engraved with your logo for a lasting impression. Not j
0 views • 4 slides
Go Green and Stylish with Eco-Friendly Wooden USBs
Put a natural twist on your branding with a wooden USB from Wholesale USB.Ditch the ordinary and embrace a unique, eco-friendly option that speaks volumes about your commitment to sustainability. Imagine the warm feel of real wood in your hand, engraved with your logo for a lasting impression. Not j
0 views • 4 slides
Purchase 1GB USB in Bulk for Efficient Data Management
While the digital world keeps growing, your storage solutions shouldn't shrink. Gone are the days of scrambling for bulky hard drives or relying on unreliable cloud storage. At Wholesale USB, we've got you covered with our straightforward and effective 1GB USB bulk option. Yes, we supply top-notch 1
7 views • 7 slides
Get Your Hands on Bulk USBs for All Your Needs
You get one USB drive and that is... history. In today's data-hungry world, a single flash drive just doesn't cut it anymore. You need a reliable supplier for bulk USB drives that can handle all your storage and distribution needs, and Wholesale USB helps you with just that.\nWe're your one-stop sho
7 views • 5 slides
Get a Customised USB to Make Your Brand Look Stylish
At Wholesale USB, we understand the importance of data security and personalised solutions in today\u2019s fast-paced world. \n\nThat\u2019s why our customised USB flash drives, including the cutting-edge USB card with built-in 128-bit encryption software, are designed to ensure your important data
3 views • 5 slides
Get High-Quality Custom USB Flash Drives at Wholesale USB
Custom USB flash drives are an excellent solution for businesses combining functionality with effective branding. Here\u2019s why you should consider them:\nConvenient and Portable- Easy to store in your wallet, always on hand when needed.\nEffective Branding- Large surface area ideal for printing y
2 views • 5 slides
Buy Custom USB Business Cards to Empower Your Brand
Are you looking for fantastic giveaways for corporate events? The custom USB business cards are the perfect solution. \n\nThey are designed to fit easily in a wallet and are always handy when needed. The large surface area allows for prominent branding, making your logo and message more impactful.\n
2 views • 5 slides
Introducing the RECOVIB Feel – the easiest-to-use USB accelerometer designed for immediate vibratory analysis
\n\nIntroducing the RECOVIB Feel \u2013 the easiest-to-use USB accelerometer designed for immediate vibratory analysis! This compact device seamlessly connects to Android devices (smartphones and tablets) or PCs via a USB connection, providing real-time insights effortlessly. Perfect for engineers,
1 views • 3 slides
Get an Affordable 32 GB Promotional USB for Your Data Storage
At Wholesale USB, we provide a wide range of USB products in various storage sizes, designs and materials.\n\nThe 32GB promotional USB serves as one of the highly sought-after options for its balance of ample storage capacity and versatility.\nHere\u
3 views • 4 slides
Understanding Security Threats and Public-Key Cryptosystems
Explore the world of security threats, passive and active attacks, and the importance of asymmetric encryption through the terminology related to asymmetric encryption, public-key cryptosystems, and public-key cryptography. Learn about the key components of public-key encryption schemes and the proc
0 views • 46 slides
Understanding AES Encryption Algorithm and Its Implementation
Learn about the Advanced Encryption Standard (AES) algorithm - a NSA-approved NIST standard encryption method. Explore how AES works, its key rounds, SubBytes, ShiftRows, MixColumns operations, and its optimization for embedded systems and small memory devices. Discover the importance of secure cryp
0 views • 14 slides
Introduction to SFTP & PGP Encryption for Secure Data Transfer
Discover how to ensure reliable data transfer, make informed decisions, and gain a strategic advantage through the use of Secure File Transfer Protocol (SFTP) and Pretty Good Privacy (PGP) encryption. The session includes demonstrations on PGP encryption and SFTP access, along with insights on setti
1 views • 22 slides
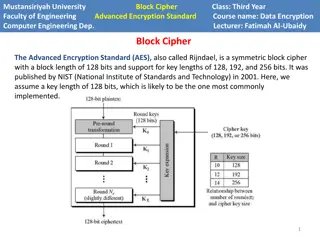
Understanding AES Encryption in Computer Engineering
Advanced Encryption Standard (AES) is a powerful symmetric block cipher used in computer engineering for data encryption. Developed by NIST, AES supports key lengths of 128, 192, and 256 bits. The algorithm operates on a state array and consists of encryption phases like initial round, main rounds,
2 views • 8 slides
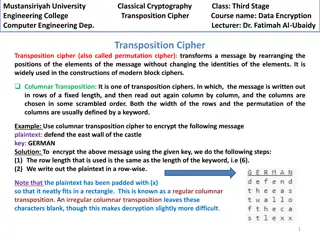
Columnar Transposition Cipher: Data Encryption Techniques at Mustansiriyah University Engineering College
Transposition ciphers, particularly the columnar transposition technique, are explored in the course "Data Encryption" at Mustansiriyah University Engineering College. The cipher involves rearranging message elements without changing their identities, making it crucial in modern block cipher designs
0 views • 4 slides
USB-TypeC Charging Operation Confirmation Results
This document provides detailed information regarding USB-TypeC charging operation confirmation results, including measurement conditions, target boards, charging current specifications, and confirmation details. It covers topics such as detecting Type-C and BC1.2, power feeding ports, measurement c
1 views • 14 slides
Get Customised Wooden USB for Your Powerful Branding
At Wholesale USB, we provide wooden usb drives as part of our extensive range of customised USB options. \n\nThese eco-friendly and stylish drives are a popular choice for businesses looking to improve their brand image. \n\nMade from sustainable mat
0 views • 5 slides
Purchase High-Quality Custom USB Flash Drives at Wholesale USB
If you are searching to impress your clients in the first go of the events, there's nothing better than customised USB flash drives. \n\nAt Wholesale USB, we specialise in providing top-tier custom USB flash drives designed for functionality and bran
1 views • 4 slides
Security with Functional Re-Encryption in Cryptography
Exploring the concept of functional re-encryption from the perspective of security in encryption schemes lies between CPA and CCA security levels. The work done by Yevgeniy Dodis, Shai Halevi, and Daniel Wichs delves into how functional re-encryption can enhance the security and privacy of encrypted
0 views • 12 slides
Probabilistic Public Key Encryption with Equality Test Overview
An exploration of Probabilistic Public Key Encryption with Equality Test (PKE-ET), discussing its concept, applications, security levels, and comparisons with other encryption schemes such as PKE with Keyword Search and Deterministic PKE. The PKE-ET allows for perfect consistency and soundness in en
3 views • 17 slides
Overview of SMX Algorithm and AES Encryption Standard
The SMX Algorithm presents a fresh approach to the avalanche effect in the Advanced Encryption Standard (AES). Initially developed to overcome the limitations of the Data Encryption Standard (DES), AES boasts improved security and efficiency, supporting key lengths of 128, 192, and 256 bits. The AES
3 views • 19 slides
The Vital Role of Encryption in Safeguarding the Digital Economy
Encryption plays a crucial role in protecting the digital economy by providing secure communication channels. Professor Peter Swire from Ohio State University emphasizes the need for strong encryption over weak cybersecurity measures. He discusses the history of wiretaps, the shift to strong cryptog
0 views • 15 slides
Maximise Your Marketing Strategies with Customised USB
Make your tasks more efficient with USB drives designed for effortless data accessibility. Wholesale USB provides perfect storage solutions by offering various Usb products. \n\nPerfect for small businesses, corporate clients, and event organisers, c
0 views • 5 slides
Buy USB Pen Drives for Your Effective Branding
USB pen drives serve as powerful branding tools. At Wholesale USB, we offer customised pen drives with sleek designs and options for printing or engraving your logo. \n\nHere\u2019s how our USB pen drives stand out as a premium choice for your brandi
1 views • 5 slides
Understanding Encryption: Keys, Algorithms, and Applications
Encryption plays a crucial role in securing data transmission and storage. It involves using keys and algorithms to convert plaintext information into a cipher that can only be deciphered with the correct key. This article explores different encryption methods, such as private and public key encrypt
0 views • 62 slides
Homomorphic Encryption Overview
Homomorphic encryption allows computation on encrypted data without revealing the underlying information. It enables secure delegation of data processing to a server while maintaining privacy. The process involves key generation, encryption, decryption, and evaluation of functions on encrypted data.
0 views • 40 slides
Bootstrapping in Fully Homomorphic Encryption
Fully Homomorphic Encryption (FHE) allows evaluation of unbounded-depth circuits without being limited by specific parameters. Bootstrapping is a critical technique to achieve full homomorphism by refreshing ciphertexts, enabling decryption functionalities within the encryption scheme. This process
0 views • 38 slides
Homomorphic Encryption and RLWE Schemes Overview
Homomorphic encryption allows computation on encrypted data, enabling privacy in outsourced computing services and applications like spam filters for encrypted mail. The Ring Learning With Errors (RLWE) scheme and its properties are discussed, along with symmetric encryption from RLWE and fully homo
0 views • 16 slides
Understanding Unidirectional Updatable Encryption and Proxy Re-Encryption
Unidirectional updatable encryption and proxy re-encryption are key concepts in secure cryptography deployments. Key management and rotation are essential for secure encryption schemes such as Proxy Re-Encryption (PRE) and Updatable Encryption (UE). PRE allows delegation of decryption abilities, whi
0 views • 16 slides
Understanding RSA Public-key Cryptography in Data Encryption
Exploring the foundational concepts of RSA public-key cryptography and its applications in data encryption. Learn how messages can be encoded, transmitted securely, and decoded using encryption and decryption functions. Discover the significance of picking large primes and understanding the bijectio
1 views • 12 slides
Understanding RSA Encryption for Secure Communication
Encryption plays a vital role in securing information, and RSA encryption, developed by Rivest, Shamir, and Adleman in 1977, uses public and private keys to safeguard data. Learn about the process, challenges with other encryption methods, prime numbers, and how RSA encryption works step by step.
0 views • 24 slides
Purchase USB for Data Storage Available for Sale at Wholesale USB
Get the ultimate solution for all your data storage necessities at Wholesale USB, where we provide high-quality USB for sale. \n\nOur range covers sleek and functional USB options designed to cater to the diverse demands of modern-day users. \n\nWhet
0 views • 5 slides
Ensuring Orthogonal Security in Data Encryption Processes
Addressing the challenge of data confidentiality in untrusted server environments through the use of encryption techniques such as deterministic and non-deterministic encryption. The goal is to achieve full functionality independently of data encryption, allowing for secure processing of data querie
0 views • 21 slides
Advances in Functional Encryption for Secure Data Handling
Explore the evolution from Cryptomania to Obfustopia through Secret-Key Functional Encryption, Public-Key Encryption, and the power of Secret-Key Functional Encryption. Discover the significance of different encryption schemes such as Public-Key Functional Encryption, Secret-Key Functional Encryptio
0 views • 36 slides
Understanding Secure Messaging and Encryption Techniques
Explore the possibilities of sending secure messages through encryption without the need for advanced degrees in Computer Science or Math. Learn about symmetric and asymmetric key encryption methods, the use of PGP for secure messaging, and the concept of shared-key encryption. Discover the intricac
0 views • 16 slides
Shop a Black USB Drive at Wholesale Rate to Secure the Best Deals
Discover the exceptional value of a black USB drive at wholesale rates from Wholesale USB, your trusted source for premium storage solutions in Australia. \n\nOur black USB drives combine sleek aesthetics with practical functionality, making them the
1 views • 5 slides
Ambitious Plan to Download and Organize English Fiction on a USB Stick
One ambitious individual aims to download all English fiction onto a single USB stick, facing challenges of finding, compressing, and indexing the text files. The plan involves downloading free books from platforms like Project Gutenberg, compressing them, and creating an index with unique categorie
0 views • 19 slides
Comprehensive Overview of Encryption Techniques and Algorithms
Explore the world of encryption with insights into symmetric and public key encryption, certificate authorities, secure sockets layer, substitution ciphers, block ciphers, AES, and public key cryptography. Delve into the intricacies of encryption keys and algorithms, including the AES process, Diffi
0 views • 31 slides
8 GB USB For Promotional Needs Are a Smart Choice for Professionals
Experience seamless, high-speed file storage with our 8GB USB drives for promotional needs. These USB drives are available for bulk orders and are designed for efficiency and reliability. They are perfect for businesses, educators, and event organise
1 views • 4 slides