Modern Threat Modeling & Cloud Systems in OWASP Sacramento
Explore modern threat modeling techniques for cloud systems at OWASP Sacramento's June 2023 event. Agenda includes community topics and more. Membership at Granite City offers workspace perks and access to exclusive events. Learn about threat modeling history and methodologies like STRIDE and PASTA.
1 views • 14 slides
Business Modelling and Innovation for Holistic Understanding and Growth
Explore the CGC Aarhus University International Summer Internship Program in Denmark focusing on business modelling and innovation. The program offers a comprehensive learning experience for graduate and postgraduate students, including online sessions and weeks in Denmark. Discover the significance
4 views • 14 slides
Tradeoffs Between Water Savings and GHG Emissions in Irrigated Agriculture
This study examines the tradeoffs between water savings, economic impact, and greenhouse gas emissions resulting from technological changes in the irrigation industry. Key objectives include estimating water savings for different crops, quantifying GHG emissions from new irrigation technologies, and
0 views • 24 slides
Modelling Estuarine Habitats in the Upper Sea Scheldt: Human-Induced Adaptations
Explore a research study on modelling estuarine habitats in the Upper Sea Scheldt under various human-induced channel and floodplain adaptations. The study examines the impact of interventions on habitat size, water quality, ecosystem, and more, providing insights into the future of the estuarine en
3 views • 13 slides
Software Development Life Cycle - Threat Modelling Initiation
Threat modelling should commence at the early stage of the software development life cycle to identify potential security risks and vulnerabilities effectively. It should ideally begin during the requirement analysis and continue throughout development, testing, and maintenance phases to ensure robu
3 views • 27 slides
Modelling and Exploration of Coarse-Grained Reconfigurable Arrays Using CGRA-ME Framework
This content discusses the CGRA-ME framework for modelling and exploration of Coarse-Grained Reconfigurable Arrays (CGRA). It covers the objectives, architecture description, inputs required, and tools included in the framework. CGRA-ME allows architects to model different CGRA architectures, map ap
2 views • 33 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
1 views • 51 slides
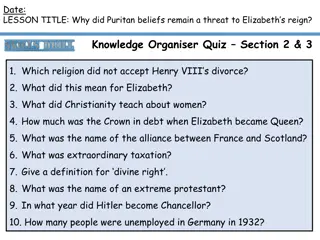
The Persistent Threat of Puritan Beliefs to Elizabeth's Reign
The Puritan belief system posed a significant threat to Queen Elizabeth I's reign, challenging the religious settlement she had put in place. Puritans disagreed with key aspects of the Church of England, such as the use of crucifixes and clergy vestments, leading to conflicts and resistance. Elizabe
0 views • 10 slides
Understanding Stereotype Threat and Teacher Response in Education
Stereotype Threat Theory explores the fear of confirming negative stereotypes and its impact on academic performance. Reduction of this threat can lead to improved learning outcomes. Teacher response plays a crucial role in shaping student writing, with various studies highlighting the importance of
0 views • 9 slides
EUROfusion WPSA Code Management and Modelling Activities 2021-2022
EUROfusion's WPSA Code Management and Modelling activities for 2021-2022 focus on developing operation-oriented tools and synthetic diagnostics for JT-60SA scientific exploitation. The tasks include discharge simulator development, breakdown simulator optimization, Energetic Particle stability analy
0 views • 12 slides
Understanding Conceptual and Requirement Modelling Using UML
Enterprise and system models play a crucial role in the business world. This collection of images showcases various aspects of conceptual and requirement modelling using Unified Modelling Language (UML). From business process models to human interactions with software systems, these visual represent
1 views • 92 slides
Behavioral Threat Assessment Tabletop Exercise - College First Year Analysis
Explore a comprehensive behavioral threat assessment tabletop exercise focused on analyzing a college first-year scenario. The exercise includes roles and responsibilities for players, facilitators, evaluators, and observers, guiding participants through phases to familiarize themselves with a stude
0 views • 19 slides
Understanding Cyber Threat Assessment and DBT Methodologies
Comprehensive information on methodologies and approaches useful for cyber threat assessment and Cyber DBT alongside classical DBT methodology as outlined in the NSS-10 document by S.K. Parulkar. The content discusses the importance of threat assessment, differences between physical and cyber threat
4 views • 17 slides
Challenges in Computer Systems Security
Understanding security in computer systems involves achieving goals in the presence of adversaries. However, this task is challenging due to the need to guarantee policies in the face of realistic and open-ended threat models. Issues can arise from problems with policy formulation, assumptions in th
0 views • 16 slides
Enhancing Incident Response Through Threat Intelligence
Explore the importance of threat intelligence in incident response, covering aspects such as understanding adversaries, assessing risks, evaluating threats, and leveraging strategic intelligence. Learn how organizations can benefit from a proactive approach to cybersecurity by utilizing threat intel
1 views • 18 slides
Stochastic Coastal Regional Uncertainty Modelling II (SCRUM2) Overview
SCRUM2 project aims to enhance CMEMS through regional/coastal ocean-biogeochemical uncertainty modelling, ensemble consistency verification, probabilistic forecasting, and data assimilation. The research team plans to contribute significant advancements in ensemble techniques and reliability assessm
0 views • 28 slides
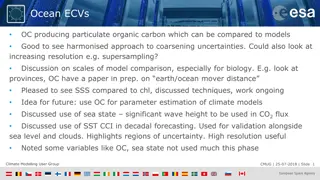
Insights from Climate Modelling User Group Meeting - July 2018
Discussion at the Climate Modelling User Group meeting highlighted the use of Ocean ECVs, with a focus on organic carbon production and model comparisons. Key topics included increasing resolution, biogeochemistry predictions, and validation using OC CCI data. Various WP projects were also discussed
1 views • 4 slides
Understanding N-Gram Models in Language Modelling
N-gram models play a crucial role in language modelling by predicting the next word in a sequence based on the probability of previous words. This technology is used in various applications such as word prediction, speech recognition, and spelling correction. By analyzing history and probabilities,
0 views • 101 slides
Expert Training on The 7 Habits of Highly Effective Cost Modelling
In this workshop session by David Rogerson, an ITU expert, participants learn the key habits of successful cost modelling in the telecom industry. The session covers identifying, illustrating, remembering, and implementing these habits for effective regulatory cost-modelling practices, with a focus
0 views • 23 slides
Understanding CBA Results Files and Modelling Outputs
The content provides a detailed guide on accessing and utilizing CBA Results Files, including tips on reading the CBA Methodology and understanding various indicators and economic templates. It also highlights the importance of analyzing disrupted rates, quantities, flexibility, and other key compon
0 views • 15 slides
Climate Modelling User Group Discussion Session Overview
The Climate Modelling User Group (CMUG) discussion session aims to foster collaboration among members, welcome new participants, identify common research questions and challenges, and establish long-term interaction mechanisms. The session includes presentations on ECV consistency and planetary visi
0 views • 15 slides
Exploring RNNs and CNNs for Sequence Modelling: A Dive into Recent Trends and TCN Models
Today's presentation will delve into the comparison between RNNs and CNNs for various tasks, discuss a state-of-the-art approach for Sequence Modelling, and explore augmented RNN models. The discussion will include empirical evaluations, baseline model choices for tasks like text classification and
0 views • 20 slides
Comprehensive Training on Campus Threat Assessment Teams
Explore the advanced training curriculum developed by experts Marisa Randazzo, Ph.D., and Gene Deisinger, Ph.D., for Virginia Campus Threat Assessment Teams. The training covers areas like threat assessment processes, case management, legal updates, and challenges in team implementation. Participant
0 views • 92 slides
Mobile App Security Threat Modeling and Mitigation
Explore mobile app security threats, learn how to conduct threat modeling exercises, and implement mitigation strategies. Discover built-in security features, threat modeling technologies, and common threats like malware and code injection. Enhance your understanding of app security constraints and
0 views • 63 slides
Pennsylvania School Threat Assessment: Keeping Schools Safe
Pennsylvania schools have implemented a Threat Assessment Team to ensure the safety and security of students, staff, and community members. The team follows specific guidelines and procedures to assess and address threats, involving key stakeholders and promoting collaboration among multidisciplinar
0 views • 37 slides
Understanding Modelling Knowledge and Knowledge Representation
Explore the significance of modelling knowledge through knowledge representation, making it explicit, independent, and reusable. Learn why knowledge representation is essential and how it facilitates exchange, query, inference, and visualization. Delve into examples of knowledge application in vario
0 views • 30 slides
Sustainable Development Modelling Tools at ICTP Trieste
In June 2017, a Summer School on Modelling Tools for Sustainable Development was organized at ICTP, Trieste. The sessions covered topics like representation of water supply and demand, incorporation of land use in modelling, energy system diagrams, and structures of energy and water systems models.
0 views • 30 slides
Understanding Stereotype Threat in Education
Stereotype threat is a phenomenon where individuals from marginalized groups experience anxiety due to negative stereotypes about their abilities. This can impact their performance and self-perception. Various groups, such as African-Americans, Latinos, females in STEM, elderly individuals, Roma, an
1 views • 42 slides
Threat Assessment Tabletop Exercise Overview
Conducting a tabletop exercise focused on threat assessment in a school setting. The exercise agenda includes welcome, introductions, exercise goals, objectives, participants' roles, exercise structure, and rules. The goals are to test preparedness for potential threats, coordinate plans effectively
0 views • 33 slides
Understanding Threat Modeling and Offensive Security
Threat modeling in offensive security involves determining potential threat scenarios that could compromise a system, understanding the system from an attacker's perspective, and devising defensive strategies. It helps confirm security implementations, identify gaps, monitor shortcomings, vulnerabil
0 views • 31 slides
Understanding Threat Assessment in Conservation: Direct, Stress, and Indirect Threats
Within threat assessment for conservation, different types of threats are identified and categorized, including direct threats which are human-induced actions directly affecting conservation targets, stressors which result from biophysical impacts of actions on targets, and indirect threats contribu
0 views • 24 slides
Pennsylvania School Threat Assessment Procedures and Guidance
Ongoing concerns about school safety led to legislation in 2019, requiring schools in Pennsylvania to establish threat assessment teams. This presentation provides an overview of the statute, threat levels, team responsibilities, procedures, and resources for school staff, parents, and guardians to
0 views • 25 slides
Conducting Threat Assessments Through the Atrocity Prevention Lens
This module from the GLOBAL CENTRE FOR THE RESPONSIBILITY TO PROTECT focuses on conducting threat assessments through an atrocity prevention lens. It covers risk identification, situational awareness in field settings, information collection methods, addressing vulnerabilities of women and children,
0 views • 20 slides
Bomb Threat Preparedness Guidelines for Shifa International Hospital
The Shifa International Hospital emphasizes the importance of maintaining a secure environment for employees, patients, and visitors in the event of a bomb threat. This presentation covers the types of bomb threats, steps to follow in case of a bomb threat, and provides guidance on handling telephon
0 views • 14 slides
High School Students Behavioral Threat Assessment Tabletop Exercise Analysis
Conduct a tabletop exercise analyzing the behavioral threat assessment of two high school students. Explore roles and responsibilities, exercise itinerary, goal, and purpose to enhance threat assessment team preparedness and response. Utilize simulated scenarios to simulate real-world events for opt
0 views • 23 slides
Examining Stereotype Threat in Engineering Education
Exploring the experiences of female engineering students facing stereotype threat, this critical theoretical framework study sheds light on the challenges that impact their academic journey. Through narrative inquiry methodology, the research focuses on white female students to understand how stereo
0 views • 37 slides
Insights into Modelling Intermediate Stops and Tour-Based Models in Transportation Planning
Explore the concept of intermediate stops in transportation modelling, including the development of a new tour-based model in Charlotte. Learn about the challenges faced in modelling stops and the estimation process using the Logit model. Discover how tour frequency, main destination choice, number
0 views • 19 slides
Opportunities at Modelling Weeks: Join for Real-Life Problem Solving
Explore the world of Modelling Weeks where small teams of students work on real-life problems under experienced instructors. Benefits include networking, teamwork, presenting results, and preparing scientific documents. Organize your own Modelling Week with support from MI-NET, focusing on PhD stude
0 views • 11 slides
School Safety and Threat Assessment Program Overview
Fact-based Threat Assessment for Safe and Supportive School Programs involves identifying, inquiring, assessing, and managing potentially dangerous situations. It aims to distinguish between those making threats and those posing real risks, without profiling or labeling individuals. Understanding th
0 views • 20 slides
Impact of Stereotypes on Perceived Facial Threat in Women Offenders
Facial expressions play a significant role in understanding emotions, but stereotypes can influence how people perceive facial affect. This study examines how reading tabloid articles about crimes committed by dark and light-skinned women offenders affects the perceived facial threat. Using a 2x2 fa
0 views • 9 slides