BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Functional Safety and Cyber Security International Standards Update
This update covers various international standards related to functional safety and cyber security, including protocols like CSMA/CD, CSMA/CA, TSN, as well as standards for safety engineering tools and safety modules. It also highlights the collaboration with BSI standards for developing industry st
2 views • 16 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Overview of Internal Audit Standards and Accounting Standards
This content provides an overview of internal audit standards and accounting standards, emphasizing the importance of continuous professional development and updating in the field. It covers various accounting standards, including disclosures, valuation, revenue recognition, and more. Additionally,
5 views • 43 slides
Overview of Human Factors and Automotive Standards YouTube Series
This YouTube series, led by Paul Green from the University of Michigan, covers human factors and automotive standards. It includes topics like introduction to standards, core human factors standards, automotive human factors standards, human-computer interaction standards, and SAE vehicle standards.
7 views • 9 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
0 views • 1 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
1 views • 1 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
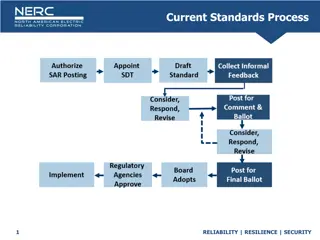
Current Standards Process for Reliability, Resilience, and Security
The current standards process focuses on ensuring reliability, resilience, and security in regulatory directives. It involves remanding standards to committees, convening technical conferences, re-ballingoting within 45 days, and considering input for further work. The process also covers the initia
1 views • 8 slides
Milk and Milk Products: Regulations and Standards in India
The regulations and standards for milk and milk products in India are governed by national bodies such as PFA, AGMARK, BIS, and FSSAI. Legal standards set by the government ensure minimum requirements for quality, composition, hygiene, labeling, and packaging. Quality standards, like BIS and Agmark,
2 views • 36 slides
Understanding LXI Network Security in Industrial Environments
LXI Security Overview provides insights into the critical attribute of security in industrial networks, focusing on LXI instruments connected to company networks. The presentation covers security standards, communication channels, encryption, PKI, certificates, and proposals for secure communication
1 views • 41 slides
Tanzania Bureau of Standards: Managing E-Waste with Standards
Tanzania Bureau of Standards (TBS), established in 1975, plays a vital role in formulating and implementing national standards, including those for managing e-waste. Standards ensure quality, safety, and sustainability in materials, products, and services. TBS follows international best practices in
0 views • 22 slides
IEEE Vehicular Technology Society Standards Update
The Vehicular Technology Society (VTS) and its standards committees, in collaboration with ITU-T, are focused on communication standards for automated vehicles. This update covers approved scopes and new project authorization requests related to extending functionality and ensuring security in vehic
8 views • 12 slides
Optimized Standards for Medical Device Safety and Performance in the EU
This report discusses the importance of harmonized standards in supporting the safety and performance of medical devices in the EU. It highlights the impact of drafting international medical device standards on EU legislation harmonization and emphasizes the role of harmonized standards under the EU
0 views • 8 slides
Understanding IoT Security Standards and Protocols
Explore the world of IoT security through the eyes of Bhuvana Ramkumar, a Staff Software Engineer at GE Digital. Gain insights into web security standards, compare IoT security concerns, and dive into Layer 7 protocols. Learn about authentication mechanisms like SASL, MQTT, AMQP, and the benefits th
5 views • 21 slides
ANSI C12.1 Overview and Current Events
ANSI C12.1 standards are integral to the electric metering industry. The standards, managed by the American National Standards Institute (ANSI) and NEMA, promote voluntary compliance. NEMA plays a crucial role as the secretariat, overseeing committees that propose and review standards every five yea
0 views • 32 slides
Hardware Security and Trusted Platform Module Overview
This content discusses the importance of hardware security, distinguishing it from software security, and introduces the concept of Trusted Platform Module (TPM) as a trusted co-processor integrated into the platform to enhance security. It also highlights the role of the Trusted Computing Group (TC
0 views • 19 slides
NUSSC 57th Meeting - End of Term Report & Safety Standards Update
The 57th Meeting of the Nuclear Safety Standards Committee (NUSSC) concluded its 9th term with significant achievements including the approval and publication of multiple safety standards. Key highlights include the development of new standards such as SSG-3, SSG-88, SSG-89, and SSG-90 focusing on v
0 views • 8 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Role of Statistical Standards in Building National Data Backbones
The role of statistical standards in constructing national data backbones is crucial for efficient data dissemination and reporting, especially in the context of Sustainable Development Goals (SDGs). Statistical standards guide the orchestration of information flows within a national statistical net
0 views • 22 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Development of Harmonized North American Life Jacket Standards
The development of harmonized North American life jacket standards led by Brandi Baldwin in the Lifesaving & Fire Safety Division at the Office of Design & Engineering Standards is a crucial regulatory process. It involves regulatory progress, standards development, consensus processes, and ongoing
0 views • 16 slides
Enhancing NASA's Cybersecurity for Mission Assurance
NASA's IV&V Program Safety and Mission Assurance Office prioritizes cybersecurity to protect mission assets. The evolving threat landscape necessitates a robust security posture, focusing on network security, software vulnerabilities, and secure development practices. Measures include leveraging sec
0 views • 15 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Health Data Interchange Standards Overview
Explore the importance of data standards in healthcare, including HL7 standards, core requirements for data exchange, and choices for data interchange. Learn about HL7 v2 and v3 messaging standards, document standards, and the benefits of using HL7 v2 messaging standard. Understand why data intercha
0 views • 28 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
New Generation Network Security System Evolution and Implementation
The presentation outlines the evolution of network security systems, focusing on the transition from traditional firewalls to next-generation systems like intrusion detection systems. It highlights the limitations of current systems in detecting internal threats and the need for advanced solutions t
0 views • 9 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
Essential Guidelines for Statewide Assessment Security Training
This resource outlines key objectives for successful test administration, test security standards, accommodation resources, and responsibilities for building coordinators and test administrators. It emphasizes the importance of adhering to test security measures to ensure the accuracy and integrity
0 views • 20 slides
Understanding Nebraska's Road Design Standards
Explore the Nebraska Administrative Code Title 428, which outlines the standards and regulations for public roads in Nebraska, including county roads and municipal streets. Learn about terminology, acronyms, and design tables to find the appropriate standards for road and street work. Discover the p
0 views • 51 slides
EHFA Standards in the Fitness Industry
The EHFA Standards Council has developed a series of standards for fitness occupations, focusing on job purpose as the foundation for qualifications. EHFA provides guidance on standards for people, programs, and places in the health and fitness sector. Since 2003, EHFA has been setting standards for
0 views • 19 slides