BCA 601(N): Computer Network Security
Explore various aspects of computer network security including cryptography, IP security, web security, and system security. Learn about authentication, encryption, key management, and network management security. Real-world examples and best practices covered.
0 views • 23 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Enhancing Security Definitions for Functional Encryption
This study delves into the realm of functional encryption (FE) against probabilistic queries, highlighting the necessity for improved security definitions to address existing limitations such as counter-intuitive examples and impossibility results. The exploration leads to proposing a new security n
4 views • 20 slides
Shielding Your Organization: Chief Security Officer Recruitment Insights
\"Shielding Your Organization: Chief Security Officer Recruitment Insights\" offers invaluable guidance for businesses seeking to fortify their security posture by recruiting the right Chief Security Officer (CSO). This comprehensive resource delves into the intricacies of chief security officer rec
0 views • 7 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
0 views • 1 slides
security service solutions
With skilled workers and cutting-edge technology, Ingenuity Security Solutions offers full tower security services in Maryland to keep your property safe. Our personalized security options for businesses include video, limiting who can enter, and assessing the risk. Keeping the highest standards of
1 views • 1 slides
The Importance of Cultural Fit in Chief Security Officer Recruitment
Ensuring cultural fit in Chief Security Officer recruitment is crucial for aligning security leadership with company values, enhancing collaboration, and improving retention. A CSO who meshes well with the organizational culture can effectively drive strategic security initiatives and foster a cohes
0 views • 8 slides
International Approaches to Enhance Nuclear Safety and Security
Understanding the concepts of nuclear safety and security, their differences, and the importance of establishing a robust nuclear security culture are essential for safeguarding nuclear facilities. The International Atomic Energy Agency (IAEA) plays a significant role in promoting nuclear safety and
1 views • 10 slides
TSA Updates on Security Training Rule for OTRB Companies
In the recent updates by TSA, the Security Training Rule for over-the-road bus (OTRB) companies has been highlighted. The rule mandates TSA-approved security training for employees in security-sensitive roles, emphasizing key requirements and elements of security training. Urban areas covered by the
1 views • 18 slides
Comprehensive Guide to Ultrasonic Testing (UT) in Non-Destructive Testing
Ultrasonic Testing (UT) is a crucial non-destructive testing method utilizing high-frequency acoustic waves for flaw detection, dimensional measurements, material characterization, and more. This guide covers the basic principles, types of sound waves, ultrasonic transducers, test techniques, applic
2 views • 35 slides
AEP Enterprise Security Program Overview - June 2021 Update
In the June 2021 update for the Kentucky Interim Committee on Natural Resources and Energy, American Electric Power (AEP) addresses recent ransomware events, their security program updates, and details about their enterprise security measures. AEP, one of the largest electric utilities in the U.S.,
0 views • 12 slides
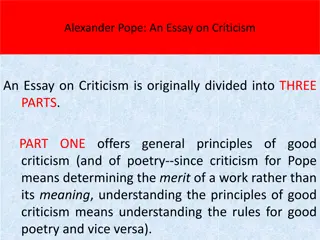
Overview of Alexander Pope's "An Essay on Criticism
Alexander Pope's "An Essay on Criticism" is divided into three parts discussing the principles of good criticism, offering solutions to critical problems, and identifying obstacles to good criticism. Part One delves into the challenges critics face due to partial judgments, false learning, and envy.
0 views • 17 slides
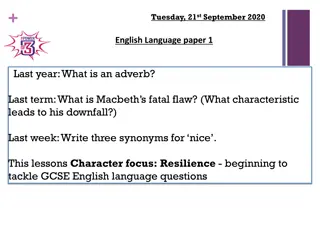
Exploring Resilience in GCSE English Language Preparation
In this lesson, students delve into GCSE English language questions focusing on character analysis, literary elements, and critical thinking skills. The lesson covers topics such as identifying adverbs, analyzing Macbeth's fatal flaw, exploring synonyms, and engaging with a novel excerpt by Jack Lon
1 views • 16 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Evolving Security Practices in DevOps: A Holistic Approach
Explore the evolution of security practices within the DevOps landscape, from debunking the myth of DevSecOps non-existence to embracing a shift-left mentality. Discover the challenges of traditional security views, the importance of continuous security integration, and the impact of delivery exposu
1 views • 25 slides
Certification and Training in Information Security
This content covers various aspects of certification and training in the field of information security, including organizational information security outlines, positions in information security personnel, and professional certifications from renowned organizations. It also provides insights into dif
0 views • 18 slides
Understanding Security Onion: Network Security Monitoring Tools
Security Onion is a Linux distribution designed for network security monitoring using various tools like Full Packet Capture, Network IDS, Host IDS, and Analysis Tools. It offers capabilities for detecting and responding to security incidents effectively, making it a valuable asset for defensive net
0 views • 17 slides
Overview of Social Security and Health Care System in Turkey
The social security system in Turkey comprises three main organizations: Social Insurance Institution (SGK/SSK), Social Security Institution for the Self-employed (Bag-Kur/SISE), and Pension Fund for Civil Servants (Emekli Sandigi). Hospitals in Turkey are dispersed among various social security and
7 views • 42 slides
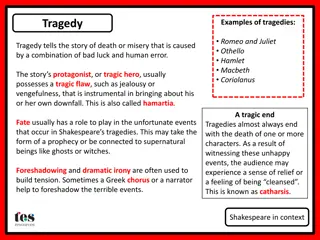
Shakespearean Drama Overview
Tragedies in Shakespeare's works often depict the protagonist's downfall due to a tragic flaw, intertwined with fate and supernatural elements leading to death or misery. Comedies, on the other hand, explore themes of love and humor, usually culminating in marriage and a sense of hope. Tragicomedies
1 views • 5 slides
Exploring the Notions of Heroism and Hubris in Greek Literature
Delve into the essence of heroism and hubris in Greek literature through an exploration of the qualities, virtues, and dangers associated with these concepts. Understand how hubris, defined as excessive pride, often serves as a tragic flaw that hinders heroes from achieving their goals. Unravel the
0 views • 12 slides
Macbeth Comprehension Questions and Tragedy Context Analysis
Explore the themes and context of Shakespeare's Macbeth through comprehension questions and in-depth analysis, including discussions on James I's rule, the divine right to rule, the character of Banquo, Macbeth's tragic flaw, and more.
0 views • 38 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Creating a Beowulf-Inspired Superhero for Marvel Comics
Hired by Marvel Comics, you are tasked with developing a new superhero embodying the qualities of Beowulf. This project involves designing a brave, kind, protective, and honest character with superhuman abilities and a flaw, set in an Anglo-Saxon inspired society that values bravery, honesty, and co
0 views • 12 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
Understanding the Elements of Greek Tragedy
Delve into the key components of Greek tragedy, exploring the characteristics of a tragic hero, the concept of tragic flaw (Hamartia), classic moments in the tragic plot, Aristotle's definition of tragedy, and the dramatic unities in a play. Discover the structure of a tragedy, from the prologue to
0 views • 19 slides
Understanding Ultrasonic Inspection (UT) in NDT
Ultrasonic Inspection (UT) is a nondestructive test method using high-frequency sound energy for flaw detection, dimensional measurements, and material characterization. It involves components like pulser/receiver, transducer, display screen, and piezoelectric element. UT equipment includes thicknes
0 views • 39 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Analysis of Ikemefuna's Role in Things Fall Apart
Introduced as an ill-fated lad who had to leave his homeland, Ikemefuna becomes part of Okonkwo's family but meets a tragic end after three years. His presence influences Nwoye's development and highlights the brutality and adherence to rituals in Ibo society. Ikemefuna's murder triggers Okonkwo's t
0 views • 9 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
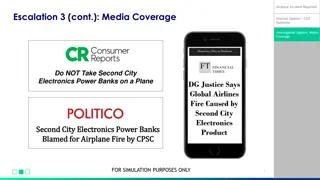
Key Updates on Airplane Incident and Potential Security Issue
Media coverage and internal updates reveal a concerning airplane incident attributed to Second City Electronics power banks, prompting investigations by CPSC and DG Justice. Additionally, a potential security flaw in the Mr. Robot 3000 toy, manufactured by the same company, has raised alarms among s
0 views • 6 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides