Using Analytics for Student Success: A Case Study of UNISA
The implementation and application of analytics for student success at UNISA, focusing on the complexities and modalities involved. It explores the use of analytics to enhance teaching and learning processes, improve academic performance, and provide personalized support to individual learners.
1 views • 24 slides
A Data Analytics Company Could Be Your Most Valuable Partner_ Here's Why
Discover why partnering with a data analytics company could revolutionize your business strategy, improve operational efficiency, and drive growth. Learn from real success stories how a business analytics dashboard turns data into actionable insights.\n
1 views • 5 slides
Efficient Fraud Management with Data Analytics
Learn the importance of data analytics in fraud management and how it can streamline risk assessment, prevention, detection, audit planning, and investigation processes. Discover key areas where data analytics can make a difference and avoid common mistakes in your fraud analytics plan. Embrace data
2 views • 33 slides
Demystifying Data Analytics: Your Guide to Effective
\"Fixity EDX offers top-notch upskilling opportunities for students and professionals with data analyst, skill development, and corporate training programs. Gain high-quality skills and industry-recognized certification for enhanced career prospects.\" \n\nAre you intrigued by the vast potential of
1 views • 2 slides
Airport Security Market to be Worth $25.27 Billion by 2031
\u00ae, the airport security market is projected to reach $25.27 billion by 2031, at a CAGR of 8.6% from 2024 to 2031. Some of the major factors driving the growth of this market are stringent government regulations for airport security and the growing number of air passengers. In addition, increasi
6 views • 5 slides
D-DS-FN-23 Dell Technologies Data Scientist and Big Data Analytics Foundations 2023 Exam
Prepare for the D-DS-FN-23 exam with confidence. Master the Dell Technologies Data Scientist and Big Data Analytics Foundations 2023 certification with comprehensive study materials, practice tests, and expert guidance. Gain the skills and knowledge needed to excel in big data analytics. Our resourc
1 views • 6 slides
KEERTHI SECURITY - Best Security Agencies In Bangalore
Keerthi Security is a security and facility management services provider in Bangalore. We are committed to offering top-notch security services for commercial and residential places. We aim to offer very secure and reliable security services to everyone. Our best-trained security guards are very sha
9 views • 11 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
0 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
Sens Security Your Premier Personal Security Firm
In a world where personal safety cannot be taken for granted, Sens Security stands out as Melbourne's leading personal security firm. Our services are designed for those who demand the utmost in protection, whether you're a high-profile personality, a top executive, or an individual with unique secu
1 views • 6 slides
To the Teams Who Think They're Too Small for Data_ How Analytics Tools Level the Playing Field
Explores the transformative impact of business analytics tools on small teams, showing how data can drive informed decision-making, enhance operational efficiency, and provide a competitive edge. Learn about user-friendly, scalable, and cost-effective business analytics software solutions that empow
1 views • 4 slides
Understanding the Role of Security Champions in Organizations
Security Champions play a vital role in decision-making concerning security engagement, acting as a core element in security assurance processes within a team. They foster a security culture, reduce dependency on the CISO, and promote responsible autonomy and continuous security education in the org
3 views • 13 slides
Exploring Data Analytics: Introduction, Terminology, Challenges, Platforms, Tools, Applications
Delve into the world of data analytics through this comprehensive guide covering topics such as the definition of data, big data, analytics vs analysis, the importance of data analytics, real-world applications, and more. Explore the classification of data, the 3Vs of big data, and how data analytic
4 views • 39 slides
Harnessing Climate Data Analytics for Sustainable Supply Chain
In the end Vinz Global's dedication to using climate data analytics to build sustainable supply chains illustrates its ability to lead positive change and generating benefits for society and the environment. Through integrating climate data analytics into its business operations, Vinz Global gains i
10 views • 4 slides
Meticulous Research® Releases In-Depth Report on Global Cloud Analytics Market Forecast
Cloud Analytics Market Size, Share, Forecast, & Trends Analysis by Offering (Solutions, Services), Type (Predictive Analytics, Diagnostic Analytics, Prescriptive Analytics), Deployment Mode, Sector (BFSI, Retail & E-commerce, Healthcare & Life Sciences), and Geography - Global Forecast to 2031\n
0 views • 4 slides
Your Current Business Analytics Tool Is No Longer Enough_ What’s Next for Data-Driven Decisions_
Discover why your current business analytics tool may no longer meet the demands of today's data-driven landscape. This blog explores the limitations of outdated analytics platforms and guides you through the essential features of next-generation tools that can enhance your decision-making capabilit
2 views • 7 slides
Understanding the Roles of a Security Partner
Learn about the roles and responsibilities of a Security Partner, including requesting changes to security roles, approving security requests, and initiating access requests. Explore the overview of Workday Security, the security access request process, and the pre-request process flow. Discover how
1 views • 17 slides
Cyber Threat Detection and Network Security Strategies
Threat detection is crucial in analyzing security ecosystems to identify and neutralize malicious activities. Methods like leveraging threat intelligence, behavior analytics, setting intruder traps, and conducting threat hunts are essential for proactive security. Implementing security through obscu
0 views • 51 slides
Developing a Teaching Portfolio for Online Doctoral Workshop on Supply Chain Analytics
In this workshop, distinguished panelists including Ananth Iyer, Apurva Jain, Subodha Kumar, and Yao Zhao share insights and expertise on supply chain analytics. Topics include program introductions, audience engagement, format, content criteria, and analytics applications. Participants will gain va
1 views • 7 slides
Impact of Data Analytics and Consulting Activities on Internal Audit Quality
This research examines how the use of data analytics and consulting activities affect perceived internal audit quality. The study investigates the relationship between these factors and top management's perception of internal audit quality. Through online scenario-based experiments with middle and t
2 views • 11 slides
Is Your Analytics Software Lying to You_ How to Spot and Correct Data Bias
Data bias can distort your analytics and lead to misguided decisions. In this blog, learn how to identify common signs of data bias, understand its impacts, and explore effective strategies to correct it. Enhance the accuracy and reliability of your insights with practical tips and advanced tools, e
3 views • 8 slides
Unleashing the Power of Business Analytics for Enhanced Decision-Making
Businesses are leveraging data and analytics capabilities to transform decision-making processes. This shift has been driven by the availability of vast amounts of data, improved computational power, and sophisticated algorithms. The incorporation of business analytics in various sectors like market
0 views • 9 slides
Leveraging Predictive Analytics in Mobile App Development_ Enhancing User Experience and Retention
Discover how predictive analytics is transforming the mobile app development landscape in our latest blog, How Predictive Analytics is Shaping the Future of Mobile App Development. By leveraging data and machine learning models, predictive analytics
0 views • 4 slides
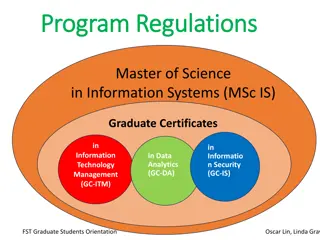
Graduate Programs in Information Systems and Data Analytics
Explore a range of graduate programs in Information Systems and Data Analytics, including the Master of Science in Information Systems (MSc.IS) and various Graduate Certificates. Dive into core and elective courses covering topics such as data analytics, information security, technology management,
0 views • 13 slides
Understanding Security in World Politics
Security studies delve into the intricate processes of defining and addressing security threats in global politics. It explores the contested nature of security definitions, emphasizes the political significance of security, and challenges the conventional boundaries of International Relations. The
0 views • 8 slides
Stream Processing for Incremental Sliding Window Analytics
This content explores the design requirements, state-of-the-art technologies, trade-offs, goals, and approach for achieving efficient incremental processing in stream analytics. It emphasizes the need to balance advantages of batch-based systems with the efficiency of incremental updates for sliding
0 views • 37 slides
Comprehensive Course Review: Security Research Cornerstones at Carnegie Mellon University
Dive into the essential topics of software security, network security, OS security, and cryptography in the course offered by Vyas Sekar at Carnegie Mellon University. Explore control flow hijacks, cryptography terminology, and the importance of network security in protecting data transmissions. Lea
0 views • 41 slides
UIC Security Division Overview and International Activities
The UIC Security Division plays a crucial role in supporting the security platform of the International Union of Railways (UIC). Headed by Jacques Colliard, the division is based in Paris and consists of key personnel like Marie-Hélène Bonneau, Jos Pires, and Laetitia Granger. The division's activ
0 views • 12 slides
Understanding Analytics for Target (A4T) Integration
Analytics for Target (A4T) is a powerful cross-solution integration that enables you to create target activities based on Analytics conversion metrics and audience segments. This integration utilizes Analytics reports for result examination and drives optimization program analysis. A4T provides valu
0 views • 33 slides
Business Analytics Program at Wake Tech Community College
Wake Tech Community College offers an Associate in Applied Science degree program in Business Analytics. The program aims to prepare students for careers in analytics fields such as Business Intelligence, Marketing Analytics, Finance Analytics, and Logistics Analytics. With a focus on employability,
0 views • 13 slides
Automating Security Operations Using Phantom
Isabella Minca, an intern for 4 months in the Security Team at Adobe, presents an overview of automating security operations using Phantom. The presentation covers goals, security alerts, Phantom playbooks, handling security data, and the capabilities of Phantom in orchestrating security responses.
0 views • 28 slides
Implementing Library Analytics at Lancaster University
Lancaster University Library, through the leadership of John Krug, Systems and Analytics Manager, has embraced analytics to enhance operations and decision-making. With the implementation of Alma and the development of analytics dashboards, the library is utilizing data from various sources such as
0 views • 17 slides
Understanding HTTP Security Headers for Web Apps
Explore the importance of HTTP security headers on web applications through a detailed breakdown of headers like HSTS, XFO, XSS, CSP, CTO, RH, and FP. Learn how these headers enhance security by instructing browsers on handling website content, preventing various attacks. Gain insights on configurin
0 views • 68 slides
Evolution of Scala-Based Open Source Big Data Analytics Frameworks
The evolution of big data analytics frameworks written in Scala, such as Spark, Kafka, and Samza, has led to significant improvements in parallel execution and support for NoSQL databases. Scala's functional and object-oriented programming capabilities have enabled the development of powerful analyt
0 views • 16 slides
Modular Security Analysis for Key Exchange and Authentication Protocols
Explore the modular security analysis approach used to examine the security of key exchange and authentication protocols, focusing on the universally composable authentication with a global Public Key Infrastructure. The analysis involves splitting the system into smaller components, separately anal
0 views • 15 slides
Revolutionizing Security Testing with BDD-Security
Explore the innovative approach of Continuous and Visible Security Testing with BDD-Security by Stephen de Vries. Gain insights into how security testing can be integrated seamlessly into modern development practices, shifting the focus from reactive to proactive measures. Learn about the importance
0 views • 33 slides
Comprehensive DevOps Security Training Overview
This Certified DevOps Security Practitioner course provides a deep dive into implementing DevSecOps, integrating security into the DevOps processes. Covering topics like security testing, Docker security, automation, and more, the training aims to equip participants with the necessary skills to embe
0 views • 5 slides
The Importance of Web & Mobile App Analytics in Modern Business.
The Importance of Web & Mobile App Analytics in Modern Business emphasizes how analytics helps businesses understand user behavior, improve engagement, and make data-driven decisions. It covers key tools like Google Analytics, Mixpanel, and practical
0 views • 13 slides
Understanding Security Testing and Architecture
Explore the fundamentals of security testing, computer security goals, software security approach, and security architecture. Learn about securing computer assets, verifying trustworthiness of security mechanisms, and validating security architecture through threat modeling. Enhance your knowledge o
0 views • 57 slides
What is Data Analytics and How It’s Useful for Business
Data analytics involves collecting, processing, and analyzing data to extract actionable insights. It includes descriptive, diagnostic, predictive, and prescriptive analytics. For businesses, data analytics helps improve decision-making, reduce costs
0 views • 1 slides