Revisiting the Spymasters: The Double Agent Problem
Delve into the intriguing world of spymaster tactics with a focus on the double agent problem and the feasibility of secure multiparty computation protocols. Explore motivations, related works, and groundbreaking results in this complex domain.
4 views • 20 slides
Enhanced Security in Multiparty Computation
Explore the improved black-box constructions of composable secure computation, focusing on definitions, objectives, and the formalization basics of multiparty computation (MPC). Learn about the motivating security aspects in MPC and the real/ideal paradigm. Discover how MPC security involves compari
1 views • 68 slides
Secure Computation Techniques in RAM Models with Efficient Automation
Explore the automation of efficient RAM-model secure computation techniques, including examples such as secure binary search. Discover how traditional solutions using circuit abstractions can be improved for sub-linear time computation through methods like Oblivious RAM. Learn about techniques such
0 views • 37 slides
Secure Multiparty Computation for Department of Education Data Sharing
This report discusses the use of Secure Multiparty Computation (SMC) to enable sharing of sensitive Department of Education data across organizational boundaries. The application of SMC allows for joint computation while keeping individual data encrypted, ensuring privacy and security within the Nat
0 views • 15 slides
Advancements in Active Secure Multiparty Computation (MPC)
Delve into the realm of secure multiparty computation under 1-bit leakage, exploring the intersection of DP algorithms, MPC, and the utilization of leakage for enhanced performance. Discover the overhead implications of achieving active security, as well as the evolution of secure computation protoc
1 views • 43 slides
Secure Multiparty Computation: Enhancing Privacy in Data Sharing
Secure multiparty computation (SMC) enables parties with private inputs to compute joint functions without revealing individual data, ensuring privacy and correctness. This involves computations on encrypted data using techniques like homomorphic encryption for scenarios like e-voting. SMC serves as
2 views • 27 slides
Actively Secure Arithmetic Computation and VOLE Study
Exploring actively secure arithmetic computation and VOLE with constant computational overhead at Tel Aviv University. Understanding how functions are represented in secure computation using arithmetic circuits over boolean circuits. Efficiently evaluating arithmetic circuits over large finite field
0 views • 36 slides
Enhancing Multi-Party Computation Efficiency Through ORAM Techniques
Explore the realm of efficient random access in multi-party computation through the reevaluation of classic schemes and the introduction of new approaches. Discover the potential of ORAM in improving performance and reducing costs in various computational tasks, such as secure multi-party computatio
0 views • 22 slides
Advancements in Multi-Key Homomorphic Encryption Using TFHE
Revolutionary research has led to the development of Multi-Key Homomorphic Encryption (MKHE) from TFHE, enabling secure and efficient computations on encrypted data. This technology offers advantages such as dynamic operability, stronger security, and minimized interaction, making it an ideal soluti
0 views • 20 slides
Secure Computation in the Age of Information
Welcome to Secure Computation Lecture 1 by Arpita Patra. The course covers evaluation policies, projects, and references in the realm of secure computation. The content delves into the significance of information security across various sectors, emphasizing the importance of safeguarding sensitive d
0 views • 36 slides
Secure Two-Party Computation and Basic Secret-Sharing Concepts
In today's lecture of "Foundations of Cryptography," the focus is on secure two-party and multi-party computation, emphasizing semi-honest security where Alice and Bob must compute without revealing more than necessary. Concepts such as real-world vs. ideal-world scenarios, the existence of PPT simu
0 views • 27 slides
Linear Communication in Secure Multiparty Computation for Efficient and Fast Processing
The research focuses on achieving perfectly secure multiparty computation (MPC) with linear communication and constant expected time. It explores efficient approaches using a broadcast-hybrid model and P2P communication, aiming to balance speed and efficiency in MPC. The study highlights the importa
1 views • 23 slides
Secure Computation Challenges and Solutions in Data Mining
Exploring the intersection of secure computation and data mining, this content uncovers key challenges such as improving algorithms, converting programs for secure computation, and addressing parallelizability issues. It highlights the importance of cryptography in ensuring data privacy and presents
0 views • 30 slides
Covert Computation: Ensuring Undetectable Engagement
Covert computation aims to conceal the fact that computation is occurring and hide engagement in certain tasks like secure computation, authenticated key exchange, and more. By making messages indistinguishable and utilizing steganographic channels, it becomes possible to keep the activities covert
1 views • 16 slides
Fides: A System for Verifiable Computation Using Smart Contracts
Fides presents a system for verifiable computation using smart contracts, focusing on blockchain basics, Ethereum, smart contracts, and outsourcing computation. It explores key components of blockchain, Ethereum's decentralized computing platform, properties of smart contracts, and the concept of ve
2 views • 25 slides
Insights into Secure Computation with Minimal Interaction
This paper revisits the concept of secure computation with minimal interaction, focusing on the challenges and possibilities of achieving secure multiparty computation in 2 rounds. Specifically exploring scenarios with 3 and 4 parties, the study delves into the reasons for choosing n=3, n=4, and t=1
0 views • 23 slides
Foundations of Cryptography: Secure Multiparty Computation
Explore the foundations of cryptography with insights into secure multiparty computation, including the Secure 2PC from OT Theorem and the Two-Party Impossibility Theorem. Delve into the impossibility of 2-Party Secure MPC, claims, and exercises on extending to statistical security. Learn about redu
0 views • 39 slides
Catalytic computation
Catalytic computation, space hierarchy theorem, and reversible computation are explored in collaboration with researchers from Charles University. The interplay between work space, auxiliary tapes, and catalyst space is investigated to understand the power and limitations of different computational
1 views • 30 slides
Secure Multiparty Computation with Sublinear Preprocessing
Secure Multiparty Computation with sublinear preprocessing allows parties to jointly compute arithmetic circuits over private inputs with malicious security in a dishonest majority setting. The online execution involves the dealer generating correlated randomness, preprocessing, and cryptographic ou
0 views • 30 slides
Practical and Deployable Secure Multi-Party Computation
This content delves into the realm of Secure Multi-Party Computation (SMPC), exploring its practical applications, challenges, and the evolving landscape of modern cryptography. It discusses the apparent paradox of encrypted data safety and usability and touches on topics like Privacy-Preserving Pro
0 views • 35 slides
Secure Computation Lecture 6 - Secrets Sharing and Circuit Evaluation
This content discusses secure computation techniques such as secret sharing and circuit evaluation. It covers linear and non-linear aspects of Shamir Secret Sharing, multiplication of shared secrets, and secure circuit evaluation with examples.
0 views • 16 slides
Multi-party Computation Fundamentals
Covering concepts of secure computation, from Shamir secret-sharing to advanced protocols like BGW and Yao, exploring MPC with both honest and dishonest majorities, discussing techniques for secure computation with malicious adversaries, and delving into secret sharing and VSS.
0 views • 24 slides
Fast Secure Computation for Small Population over the Internet
Efficient 3-Party and 4-Party protocols with honest majority, achieving strong security notions. Secure MultiParty Computation (MPC), joint function f(x1, x2, .., xn) with goals of correctness and privacy. Real-world applications in Secure ML, auctions, and more. Explore why small populations with h
1 views • 13 slides
iThreads: A Threading Library for Parallel Incremental Computation
This content explores iThreads, a threading library designed for efficient execution of applications in successive runs with small input changes. They aim for transparency, practicality, and efficiency in parallel incremental computation, targeting unmodified pthreads-based programs while supporting
0 views • 28 slides
Efficient Multiparty Protocols via Log-Depth Threshold Formulae
Secure Multiparty Computation (MPC) allows multiple players to jointly perform computational tasks securely. Feasibility results show perfect security in specific scenarios. This work proposes a novel approach using player emulation to design efficient MPC protocols, simplifying existing complex pro
0 views • 35 slides
PeerTalk: A Peer-to-Peer Multiparty Voice-over-IP System
This paper discusses "PeerTalk," a peer-to-peer multiparty voice-over-IP system proposed by Gu, Wen, Yu, and Shae. The system aims to facilitate voice communication among multiple parties in a decentralized manner. The study, published in IEEE Transactions on Parallel and Distributed Systems in Apri
0 views • 17 slides
Two Round MPC via Multi -Key FHE
Explore the innovative approach of Two-Round MPC via Multi-Key FHE proposed by Daniel Wichs from Northeastern University in collaboration with Pratyay Mukherjee. This joint work introduces a novel protocol for secure multiparty computation, enhancing privacy and efficiency in data sharing scenarios.
0 views • 17 slides
Privacy-Preserving Measurement of the Tor Network Study Summary
This study conducted by Aaron Johnson on May 30th, 2017 at the Center for Disclosure Avoidance Research delves into the intricacies of the Tor network. It focuses on the anonymous and censorship-resistant communication system, exploring the number of users, connections, and traffic volume. The use o
0 views • 39 slides
Secure Multiparty Computation and Communication Models for Asynchronous Security
Explore the world of secure multiparty computation and communication models tailored for asynchronous security scenarios, where intelligence agencies must collaborate to stop a terrorist threat. Learn about the essential security requirements, simulation-based security, communication models like poi
0 views • 21 slides
Practical Deployment of Secure Multi-Party Computation and Cryptography Paradox
Explore the practical aspects of Secure Multi-Party Computation (SMPC) and the paradox of modern cryptography. Discover how SMPC allows joint computation while keeping inputs private. Learn about the challenges and advancements in deploying SMPC for privacy-preserving proximity calculations.
0 views • 35 slides
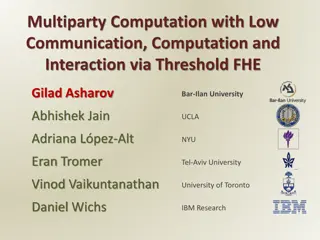
Multiparty Computation Using Threshold Fully Homomorphic Encryption
Explore the concept of multiparty computation with low communication and computation complexity through threshold fully homomorphic encryption. Advantages include reduced round complexity, low communication requirements, and independence of specific functions and inputs. Discover how this approach c
0 views • 35 slides
Efficient Fully Malicious Multiparty Computation Protocol
Explore the construction of a fully malicious Multiparty Computation protocol in the dishonest majority setting, aiming for constant rounds and linear communication complexity. Delve into known literature results and communication-efficient protocols for secure computation scenarios.
0 views • 41 slides
Secure Multiparty Computation for Highly Repetitive Circuits
Explore the advancement in secure multiparty computation for highly repetitive circuits, presenting efficient protocols, comparisons with existing methods, focusing on Single Instruction Multiple Data (SIMD) circuits, and proposing protocols for a broader range of circuits. Discover implementations
0 views • 11 slides
Secure Two-Party Computation Techniques Explained
Delve into the world of secure two-party computation techniques such as Yao's Garbled Circuit (GC) and the innovative Free-XOR technique. Explore the research, challenges, and advancements in achieving practicality in secure computation protocols.
1 views • 32 slides
Secure Computation Protocols and Challenges in the Internet World
Explore the world of secure computation protocols such as cross-domain secure computation, GMW protocols, and black-box simulators, along with the challenges faced in ensuring security in the internet world. Learn about concurrent security issues and the complexities involved in constructing secure
0 views • 28 slides
Efficient Multiparty Computation for Matrix Rings against Malicious Adversaries
Explore the development of efficient multiparty computation protocols for non-commutative rings, specifically focusing on matrix rings, in the dishonest majority setting to combat malicious adversaries. This study, presented at ASIACRYPT 2024, delves into the significance of utilizing matrix rings i
0 views • 19 slides
Secure Messaging and Multiparty Computation Techniques
Explore Sabre anonymous messaging and secure multiparty computation protocols for enhanced data privacy and security. Learn about additive secret sharing techniques for secure data transfer and computation.
1 views • 53 slides
Exploring Garbled RAM Techniques for Secure Computation
Dive into the world of Garbled RAM, a secure computation technique pioneered by Daniel Wichs and his team at Northeastern University. Discover how Garbled RAM offers efficient and secure ways to process data while protecting sensitive information from unauthorized access. Learn about the goals, defi
0 views • 29 slides
Efficient Algorithm for Quantum Circuit Synthesis and Optimization
Explore the efficient algorithm for synthesizing quantum circuits and optimizing quantum computation. Delve into essential functions, sorting, and experimental results in quantum computation. Discover the advancements in quantum computation led by IBM, Google, and Lockheed Martin. Learn about the fu
0 views • 27 slides
Multiparty Computation with Threshold Fully Homomorphic Encryption
Explore the concept of Multiparty Computation with low communication complexity and independent computation, featuring Threshold Fully Homomorphic Encryption. Learn about advantages such as low round complexity and communication complexity, as well as the implementation of Threshold Key Generation,
0 views • 35 slides