Secure Keyed Hashing on Programmable Switches
Explore the implementation challenges and opportunities for improved security, privacy, performance, and reliability in data plane applications using (Half)SipHash and CRC32 hashing techniques. Discover the vulnerabilities associated with CRC32 and the need for secure hashing solutions like SipID. L
0 views • 17 slides
CSE 373 - Hashing Concepts and Exam Preparation
Introduction to hashing in CSE 373, covering basic concepts, hash functions, collision resolution, and runtimes. Exam details for Friday's practice exam include topics on Stacks, Queues, BigO Notation, Heaps, Trees, Design Tradeoffs, and exam format with emphasis on theoretical understanding. Lectur
1 views • 38 slides
Scaling Services and Key-Value Storage Techniques
This content delves into various aspects of scaling services, including partitioning, hashing, and key-value storage. It discusses vertical and horizontal scalability, the chaotic nature of horizontal scaling, techniques for partitioning data, and case studies like Amazon Dynamo. The importance of p
1 views • 48 slides
Consistent Hashing and Distributed Hash Table
Explore the concept of consistent hashing and distributed hash tables to efficiently store and retrieve web pages across multiple servers. Learn how hashing functions and algorithms can distribute data evenly, handle server additions smoothly, and minimize object relocations. Discover the benefits o
1 views • 36 slides
Overlay Networks and Consistent Hashing in Distributed Systems
Understanding the concept of overlay networks and consistent hashing in distributed systems is crucial for scalability and efficient data storage. Overlay networks like P2P DHT via KBR offer a decentralized approach for managing data while consistent hashing provides a balanced and deterministic way
1 views • 36 slides
Adapting Linear Hashing for Flash Memory Constrained Embedded Devices
This research explores the adaptation of linear hashing for improved data handling on flash memory-constrained embedded devices. Motivated by the increasing data collection by IoT devices, the study focuses on implementing database structures like a linear hash table for efficient data processing. T
0 views • 67 slides
Enhancing Key-Value Storage with MemC3 and Cuckoo Hashing
MemC3 is a specialized key-value store that combines CLOCK and Concurrent Cuckoo Hashing to improve performance and efficiency. Memcached, an established DRAM-based key-value store, is also discussed along with its LRU eviction strategy. The use of internal chaining hashtable and LRU caching in Memc
2 views • 23 slides
Database Index Hashing Techniques
Hashing-based indexing in database systems is efficient for equality selections but not suitable for range searches. Both static and dynamic hashing methods exist, with static hashing involving fixed primary pages that are allocated sequentially. The process involves determining the bucket to which
1 views • 41 slides
Data Structures and Hashing in Java
Data structures play a crucial role in organizing, iterating, adding, deleting, and searching data efficiently. Hash tables, linked lists, trees, and more are explored in this overview, highlighting their strengths and trade-offs. Hashing, collision resolution strategies, and the importance of a wel
1 views • 19 slides
Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
1 views • 40 slides
Network Security Principles and Techniques
Explore the fundamental concepts of network security, including issues of confidentiality, integrity, and non-repudiability. Learn about the challenges of securing networks and the types of attacks that computer systems face. Dive into basic security techniques like hashing and symmetric key cryptog
0 views • 36 slides
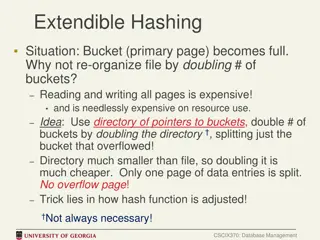
Efficient Bucket Management in Extendible Hashing
In cases where a bucket (primary page) becomes full in extendible hashing, re-organizing the file by doubling the number of buckets can be costly in terms of resource utilization. An alternative approach involves using a directory of pointers to buckets and doubling the directory instead of all buck
0 views • 9 slides
Cryptographic Hashing and its Importance
Cryptographic hashing involves converting data into fixed-size values for secure storage and verification purposes. It plays a vital role in data security, ensuring integrity and confidentiality. This article explores hashing algorithms, applications, collisions, and the best practices for storing s
0 views • 24 slides
Hashing Data Structures
Hashing is a fundamental concept in computer science that involves mapping data from a large space to a target space efficiently using hash functions. In this context, we explore the principles of hashing, ideal data structures, memory considerations, and the role of hash functions in achieving effi
1 views • 93 slides
Community ID Standardized Flow Hashing for NSM Tools
In the realm of NSM tools, standardized flow hashing through Community ID offers a robust solution for efficient data processing and analysis. Christian Kreibich's expertise shines in this comprehensive approach to flow hashing, enhancing the capabilities of your security infrastructure significantl
0 views • 17 slides
Hash-Based Indexes
In this lecture, you will delve into hash-based indexes, exploring their application in database management. Topics covered include static and dynamic hashing techniques, review of hashing structures, adjustments against inserts and deletes, extendible hashing, linear hashing, and the relative stren
0 views • 8 slides
External Memory Hashing
Memory Hashing involves utilizing hash-based indices for efficient data retrieval on disk storage systems. It discusses the concepts of B+-trees, hashing techniques, indexing strategies, and design decisions for optimal performance. Explore the complexities, query types, and dynamic hashing schemes
0 views • 23 slides
Linear Hashing for Flash Memory on Resource-Constrained Microprocessors
This research focuses on evaluating the performance of linear hashing on the Arduino platform for efficient utilization of flash memory in resource-constrained microprocessors. Linear hashing is explored as a near-optimal data structure that maintains performance while conserving main memory, aiming
0 views • 25 slides
DBMS Internals: Hashing and External Sorting
Today's DBMS session covered hash-based indexes and external sorting, exploring topics such as linear hashing, sorting algorithms, and database layers. Linear Hashing provides a flexible approach to dealing with insertions and deletions, offering an alternative to Extendible Hashing. The session del
0 views • 44 slides
Lock-free Cuckoo Hashing
Implementing a lock-free cuckoo hashing scheme for concurrent multicore systems, this research presents a high-performance hash table supporting multiple read/write operations simultaneously. The system guarantees progress without locking, achieving exceptional scalability in multicores and outperfo
0 views • 28 slides
Introduction to Min-Hashing and Locality Sensitive Hashing
Discover the concepts of Min-Hashing and Locality Sensitive Hashing as detailed in Rajaraman and Ullman's "Mining Massive Datasets" and Evimaria Terzi's Data Mining Course slides. Uncover the motivation behind finding duplicate and near-duplicate documents in large datasets, the challenges of docume
0 views • 52 slides
Min-Hashing and Locality-Sensitive Hashing
Min-Hashing and Locality-Sensitive Hashing are techniques used to identify duplicate and near-duplicate documents efficiently, especially when dealing with massive datasets. These methods involve representing documents in a compact manner, enabling pairwise comparisons for similarity assessment. Shi
0 views • 47 slides
Cryptographic Hashing
Cryptographic hashing is a key concept in data security, ensuring data integrity and authenticity. Learn about the properties of good cryptographic hashes, the difference between encryption and hashing, and delve into the specifics of SHA-1, its collisions, and processing of original messages. Under
0 views • 39 slides
Finding Similar Documents Using Locality-Sensitive Hashing in Big Data Mining
In this task, we explore the application of Locality-Sensitive Hashing (LSH) to find similar documents in a large text dataset. The process involves steps such as shingling, min-hashing, and implementing LSH algorithm to identify candidate pairs of similar documents. The dataset used is the Reuters-
0 views • 18 slides
Exploring Overlay Networks and Consistent Hashing in Distributed Systems
Delve into the realm of overlay networks and consistent hashing in the context of distributed systems. Learn about key concepts such as mapping keys to servers, scaling key/value storage services, and the benefits of consistent hashing algorithms. Discover how these techniques enable efficient data
0 views • 36 slides
Overlay Networks and Consistent Hashing in Distributed Systems
Explore the concepts of Overlay Networks, Consistent Hashing, and Distributed Key/Value Storage Services in Networks and Distributed Systems. Learn how to scale services, map keys to servers, and implement effective hashing algorithms for efficient data distribution.
0 views • 36 slides
Universal Hashing and Pseudorandom Numbers Overview
Explore the concepts of pseudorandom number generation, universal hashing, chaining, and linear probing. Learn about different methods for generating random numbers, such as natural experiments and seed-based generators like the Middle-Square method. Dive into the importance of hashing in data struc
0 views • 25 slides
Universal Hashing Techniques for Pseudorandom Number Generation
Learn about the concept of universal hashing and its application in generating pseudorandom numbers. Explore methods like the Middle-Square technique and Weyl's Sequence Idea, along with discussions on perfect hash functions and 2-Universal Hashing Family. Discover how to remove duplicates from an a
0 views • 24 slides
Linear Hashing: An Extension to Extendible Hashing
Linear Hashing (LH) is an innovative technique that enhances Extendible Hashing by eliminating the need for a directory through the usage of a family of hash functions. By employing hash functions hi and looking at the last di bits, LH expands the range of directories to improve performance. The pro
2 views • 11 slides
Understanding Hashing and Avoiding Collisions in Computer Science
Dive into the world of hashing, learn about hash functions, chaining, collisions, and the importance of using a universal hash family. Explore the concepts with examples and understand the significance of randomness in hashing.
1 views • 34 slides
Understanding Hashing: Techniques and Functions in Computer Science
Explore the concept of hashing, including hash functions, hash tables, collisions, and the importance of good hash function design. Learn how hashing optimizes table operations and delves into the realm of computer science structures seamlessly.
1 views • 49 slides
Linear Hashing: A Directory-Less Hashing Extension Strategy
Linear Hashing is an approach that extends Extendible Hashing by avoiding the need for a directory. It utilizes a family of hash functions to allocate data to buckets dynamically, thereby increasing efficiency and minimizing directory maintenance. This technique eliminates the traditional directory
0 views • 11 slides
Fuzzy Hashing and Locality-Sensitive Hashing for File Analysis
Learn about bro-fuzzy-hashing and its applications in file analysis, including fuzzy hashing and locality-sensitive hashing. Explore examples, use cases, and open questions related to these advanced hashing techniques.
0 views • 4 slides
Understanding Hash-Based Indexes in Database Management
Explore the concept of hash-based indexes in database management, covering topics like static hashing, dynamic hash structure adjustment, extendible hashing, linear hashing, and when to choose B+trees vs. Hashing. Gain insights into the strengths and applications of different hashing techniques.
0 views • 12 slides
Hashing in Randomized Algorithms - Overview and Applications
Explore the concept of hashing in randomized algorithms, understand its problem definition, solutions, collision handling, and why hashing works effectively in practice. Learn about the efficiency, guarantees, and complexities associated with hashing in maintaining data structures.
0 views • 24 slides
Understanding Hashing Strings in Computer Science
Explore the concept of hashing with string keys in computer science, focusing on creating effective hash functions and addressing issues with summing hash functions. Delve into examples, ASCII tables, and discussions to grasp the complexities of hashing strings effectively. Learn how to optimize has
0 views • 14 slides
Database Systems with Linear Hashing Structures and Algorithms
Explore the concepts of linear hashing and dynamic hashing schemes in database systems. Learn about extensible hashing, hash tables, search operations, and insertion techniques using hash functions and bucket addresses. Discover how linear hashing handles search and insertion processes efficiently i
0 views • 78 slides
Efficient Hashing Techniques for Data Storage
Explore the concepts of hashing and collision resolution techniques for efficient data storage. Learn about hashing functions, hash tables, collision resolution algorithms, and their impact on add, search, and remove operations. Discover ways to optimize data storage and retrieval using hashing in p
0 views • 17 slides
Understanding Min-Hashing and Locality Sensitive Hashing for Document Clustering
Dive into the world of data mining with Min-Hashing and Locality Sensitive Hashing techniques used for clustering duplicate and near-duplicate documents from large datasets. Learn about shingling, document similarity, and the importance of signatures in preserving similarity while managing memory ef
0 views • 87 slides
Novel Contextual Locality Sensitive Hashing Algorithm for SMRT Reads Mapping
Explore a novel contextual Locality Sensitive Hashing algorithm designed to align noisy SMRT reads effectively with the reference genome. This algorithm, conLSH, surpasses rHAT in speed and memory requirements, offering significant improvements for aligning SMRT reads in genomics research.
0 views • 14 slides