Cryptography,.Quantum-safe Cryptography& Quantum Cryptography
Dive into the world of cryptography, quantum-safe cryptography, and quantum technology as discussed in Maurizio D. Cina's presentation at CYBERDAYS in Prato. Topics include current cryptosystems, post-quantum cryptography, quantum key distribution, and future cryptosystems based on quantum algorithm
4 views • 17 slides
Introduction to Cryptography: Basics, Terminology, and Significance
Cryptography is the study of techniques used for secure communication, involving creating programs to protect private messages. This overview covers the history, terminology, and significance of cryptography. Explore the basics, cyphers, and the importance of encryption in safeguarding sensitive dat
3 views • 15 slides
Understanding Road Safety Audit and Inspection Concepts
Road Safety Audit (RSA) and Road Safety Inspection (RSI) play important roles in evaluating and improving road safety infrastructure. While RSA focuses on new road design and construction, RSI assesses existing roads periodically. This article discusses the differences between RSA and RSI, their pro
0 views • 32 slides
The Fascinating World of Cryptography
Cryptography is the art of concealing messages to ensure information security, involving processes like encryption and cryptanalysis. Explore the history of cryptography from ancient civilizations to modern-day techniques like steganography. Witness the evolution of coding methods and machines that
0 views • 14 slides
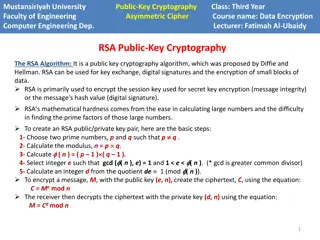
Introduction to RSA Cryptography and Public Key Encryption
Explore the fundamentals of RSA cryptography and public key encryption, including shift ciphers and affine ciphers. Learn how public key encryption solves the challenges of implementing secure communication on a large scale. Discover the key components of RSA, its development history, and the mathem
2 views • 37 slides
Formal Verification of Quantum Cryptography by Dominique Unruh
Explore the significance of formal verification in quantum cryptography as discussed by Dominique Unruh from the University of Tartu. Understand the challenges, motivations, and current work in verifying quantum crypto protocols, and the potential impact of quantum computers on common encryption met
0 views • 25 slides
Introduction to Public Key Cryptography
Public key cryptography, exemplified by algorithms like Diffie-Hellman and RSA, revolutionizes secure communication by allowing users to encrypt messages with public keys known to all and decrypt them with private keys known only to the intended recipient. This advanced encryption method ensures sec
1 views • 44 slides
Evolution of Cryptography: From Ancient Techniques to Modern Security Mechanisms
Explore the evolution of cryptography from ancient techniques like the Caesar Cipher to modern security mechanisms like SSL, SSH, and IPSec. Learn how cryptography plays a crucial role in ensuring confidentiality, integrity, authentication, non-repudiation, and availability in network security. Disc
1 views • 62 slides
Introduction to Cryptography, Cryptanalysis, and Cryptology
Cryptography involves protecting information by encrypting and decrypting data, while cryptanalysis focuses on breaking encryption methods to access hidden messages. Cryptology encompasses both cryptography and cryptanalysis. Encryption encodes messages to prevent unauthorized access, while decrypti
0 views • 12 slides
Exploring Cloud Cryptography for Secure Data Processing
Cloud cryptography is a vital aspect of data security in cloud computing, allowing data to be encrypted and processed securely. This presentation delves into the concepts of cloud cryptography, homomorphic encryption, and the two types of homomorphic encryption - hybrid and partial. It discusses the
8 views • 17 slides
Understanding Cryptography in the Digital World
Uncover the world of cryptography with a focus on digital advancements, emphasizing the importance of rules in society. Delve into the history of secret communication, code design, and breaking. Explore the rise of cryptocurrencies, digital banking, and blockchain technologies, such as Bitcoin and E
0 views • 12 slides
RSA Algorithm in Public-Key Cryptography
The RSA algorithm is a crucial public key cryptography method used for key exchange, digital signatures, and data encryption. It involves generating public-private key pairs using prime numbers, encryption with the public key, and decryption with the private key. The algorithm's strength lies in the
0 views • 5 slides
Exploring the World of Quantum Money and Cryptography
Delve into the realm of quantum money, computation, and cryptography, understanding the intricacies of semi-quantum money, consensus problems, post-quantum cryptography, and unique concepts like certifiable randomness and tokenized digital signatures.
6 views • 30 slides
Overview of Basic Security Properties and Cryptography Fundamentals
This content provides an introduction to basic security properties such as confidentiality, authenticity, integrity, availability, non-repudiation, and access control. It also covers the fundamentals of cryptography, including symmetric and asymmetric encryption, public-key cryptography, and the imp
0 views • 41 slides
Introduction to Cryptography: The Science of Secure Communication
Cryptography is the study of methods for sending and receiving secret messages securely. This lecture explores the application of number theory in computer science, focusing on the design of cryptosystems like public key cryptography and the RSA cryptosystem. The goal of cryptography is to ensure th
0 views • 53 slides
Introduction to Cryptography and Its Applications in Computer Science
Cryptography is the study of methods for sending and receiving secret messages. In this lecture, we explore the design and application of cryptosystems, such as the RSA cryptosystem and Turing's Code. The goal is to securely encrypt and decrypt messages using number theory to protect communication f
0 views • 53 slides
Post-Quantum Cryptography Security Proofs and Models Overview
Explore the various aspects of post-quantum cryptography security, including evaluation criteria, building public key cryptography (PKC) systems, security proofs, digital signatures, and reduction problems. Dive into topics such as performance, cryptanalysis, provable security, standard models, exis
0 views • 42 slides
Understanding Public-Key Cryptography and Its Applications
Public-Key Cryptography revolutionized secure communication by introducing the concept of using separate keys for encryption and decryption. Initially explored by researchers like Diffie, Hellman, and Merkle in the 70s, it addressed key distribution challenges faced by symmetric cryptography. This m
0 views • 34 slides
Foundations of Cryptography: MIT Course Overview and Key Concepts
Explore the MIT course "Foundations of Cryptography" offering insights on cryptography, key themes like adversarial thinking and computational hardness, historical context, and the significance of security proofs via reductions. Learn about the course staff, topics covered, and intellectual origins
1 views • 33 slides
Cryptography Concepts and Encryption Methods Overview
Exploring elementary cryptography concepts such as encryption, cryptanalysis, symmetric and asymmetric encryption algorithms like DES, AES, and RSA. Delve into key exchange protocols, digital signatures, cryptographic hash functions, and the process of encryption and decryption in a cryptosystem.
0 views • 23 slides
Exploring Post-Quantum Cryptography and Constructive Reductions
Delve into the realm of post-quantum cryptography through an insightful journey of constructive reductions, rethinking cryptography assumptions, and the relationship between classical and post-quantum regimes. Discover the challenges, advancements, and goals in the quest for durable cryptographic al
1 views • 21 slides
Understanding Cryptography: Basic Concepts in Number Theory and Divisibility
This text delves into the fundamental concepts of number theory, divisibility, and finite fields essential for understanding cryptography. It covers topics such as divisibility, properties of divisibility, the division algorithm, the Euclidean algorithm for determining the greatest common divisor, a
0 views • 35 slides
Understanding Public Key Cryptosystems in RSA Encryption
Public key cryptosystems, like RSA, use two keys for encryption and decryption, with one key made public and the other kept secret. This asymmetric system allows secure communication, where the encryption key (E) is used to encrypt messages into ciphertext (C), which can only be decrypted back to th
0 views • 11 slides
Key Distribution and Management in Cryptography
This presentation discusses key distribution and management in cryptography, covering symmetric and asymmetric key cryptography, methods for sharing symmetric and public keys, as well as key distribution techniques such as manual delivery, initial key distributions, and the use of trusted third part
0 views • 30 slides
Exploring Public-Key Cryptography and Ancient Mathematical Techniques
Delve into the fascinating world of public-key cryptography, where the convergence of prime numbers and inverse functions plays a pivotal role in ensuring secure communication. From the history of math to contemporary applications, discover how encryption and decryption transform messages to keep th
1 views • 21 slides
Understanding Public Key Cryptography in Network Security
Explore the concepts of public key cryptography, key distribution challenges, solutions to secret key schemes, and the importance of secure communication in network security. Learn about cryptology, cryptography, cryptanalysis, block ciphers, stream ciphers, and more in this informative content.
0 views • 21 slides
Overview of Public-Key Cryptography and Knapsack Problem in Cryptology
This lecture delves into the realm of public-key cryptography, including the Knapsack one-way function and the Merkle-Hellman Crypto System. It explores historical perspectives, the concepts of OWFs, Elliptic Curve Cryptography, and introduces new algebra using additive groups over Elliptic Curves.
0 views • 16 slides
Efficient Verified Cryptography in F* by Jean-Karim Zinzindohou
Explore the importance of cryptography verification in F* through Jean-Karim Zinzindohou's joint work with Karthik Bhargavan. Discover the significance of verifying crypto, static guarantees provided, and examples like elliptic curve cryptography. Delve into F* as a rich ML-like language for secure
0 views • 38 slides
Cache Attack on BLISS Lattice-Based Signature Scheme
Public-key cryptography, including the BLISS lattice-based signature scheme, is pervasive in digital security, from code signing to online communication. The looming threat of scalable quantum computers has led to the development of post-quantum cryptography, such as lattice-based cryptography, whic
0 views • 13 slides
Understanding Quantum Computing and Its Impact on Cryptography
Quantum computing utilizes the principles of quantum mechanics to process information exponentially faster than classical computers. This advancement poses a significant threat to current cryptographic systems, especially those reliant on factors like RSA and Diffie-Hellman key exchange. If large-sc
0 views • 25 slides
Understanding Prime Numbers and RSA Algorithm in Cryptography
Delve into the world of prime numbers and the RSA algorithm in cryptography. Learn about key generation, Bertrand's Postulate, the Miller-Rabin test for primality, and the Almost Miller-Rabin test. Discover how these concepts are crucial in ensuring secure communication and data encryption.
0 views • 20 slides
Lightweight Cryptography: Key-Reduced Variants and Beyond-Birthday-Bound Security
Lightweight cryptography has emerged as a hot research topic in the past two decades, with over 60 ciphers proposed. This includes examples like PRESENT, GIFT, SIMON/SPECK, and more. Authenticated encryption through CAESAR and NIST LWC plays a vital role, with ASCON and ACORN leading the lightweight
0 views • 25 slides
Cryptographic Center in Novosibirsk: Advancements in Cryptography and Research
The Cryptographic Center in Novosibirsk, established in 2011, focuses on advancing cryptography through research, education, and international collaborations. With a team of researchers and students, the center explores various aspects of cryptography, including cryptographic Boolean functions, ciph
0 views • 33 slides
Key Exchange and Public-Key Cryptography Overview
Explore the challenges of key management, the use of trusted third parties in generating shared keys, the limitations of toy protocols in secure key exchange, and the evolution of public-key cryptography techniques like Merkle Puzzles, Diffie-Hellman, and RSA. Learn how to achieve secure key exchang
0 views • 36 slides
Understanding the RSA Algorithm - An Overview
Cryptography is the science of writing in secret code to protect information. The RSA algorithm, introduced by Rivest, Shamir, and Adleman in 1978, is a popular public key system. It involves the exchange of secure messages between senders and receivers to avoid code breaking. This algorithm uses bo
1 views • 31 slides
Understanding RSA Public-key Cryptography in Data Encryption
Exploring the foundational concepts of RSA public-key cryptography and its applications in data encryption. Learn how messages can be encoded, transmitted securely, and decoded using encryption and decryption functions. Discover the significance of picking large primes and understanding the bijectio
1 views • 12 slides
Understanding RSA Encryption for Secure Communication
Encryption plays a vital role in securing information, and RSA encryption, developed by Rivest, Shamir, and Adleman in 1977, uses public and private keys to safeguard data. Learn about the process, challenges with other encryption methods, prime numbers, and how RSA encryption works step by step.
0 views • 24 slides
Evaluation of Ed25519 Cryptography Performance in DNSSEC Validation
Edwards Curve Cryptography, specifically the Ed25519 algorithm, offers faster performance and high crypto density compared to other algorithms. This evaluation study compares key sizes, processing times, and validation support for Ed25519, ECDSA P-256, RSA-2048, and RSA-4096 in DNSSEC validation sce
0 views • 19 slides
Weak Keys Detection in Network Devices
TLS and SSH rely on RSA and DSA for security, but weaknesses in random number generation can lead to widespread weak keys among hosts on the Internet. This paper uncovers the prevalence of repeated keys and easily inferred private keys, emphasizing the importance of entropy pools in key generation.
0 views • 28 slides
New Directions in Cryptography: Harta Dwijaksara, Yi Jae Park
Explore the world of cryptography through this comprehensive guide covering topics such as conventional cryptography, public key cryptography, one-way authentication, trap doors, computational complexity, and more. Learn about the importance of privacy in communications and the key principles behind
0 views • 20 slides