Public key encryption, Digital signature and authentication
Understand the concept of public key encryption, asymmetric encryption, and the widely used RSA algorithm. Explore how public key cryptography revolutionized the field of encryption and its applications in confidentiality, authentication, and key distribution.
4 views • 12 slides
Algorithm Analysis
Algorithm analysis involves evaluating the efficiency of algorithms through measures such as time and memory complexity. This analysis helps in comparing different algorithms, understanding how time scales with input size, and predicting performance as input size approaches infinity. Scaling analysi
1 views • 30 slides
Clinical Algorithm for Rash Evaluation
The clinical algorithm outlines the evaluation process for a patient presenting with a rash, focusing on the assessment for measles transmission. It covers key criteria, testing recommendations, and guidelines for suspected measles cases. Healthcare providers can utilize this algorithm to determine
0 views • 5 slides
Batching Techniques for Accumulators: Applications to IOPs and Blockchains
This presentation discusses batching techniques for accumulators in the context of IOPs and blockchains. It covers challenges with UTXO sets, Merkle trees, and RSA accumulators, proposing solutions and improvements. The content explores problems with Merkle trees, benefits of RSA accumulators, and e
0 views • 27 slides
Advanced Cardiovascular Life Support Algorithm
This advanced cardiovascular life support algorithm provides step-by-step guidance in managing cardiac emergencies such as cardiac arrest, arrhythmias, and other life-threatening conditions. The algorithm includes a series of slides detailing important procedures and interventions to improve patient
5 views • 9 slides
Understanding Booth's Algorithm for Binary Integer Division
Learn about Booth's Algorithm and how it facilitates binary integer division. Discover key points to remember when using the algorithm, steps to initiate the process, and a detailed example to illustrate the multiplication of two operands using Booth's Algorithm.
1 views • 42 slides
Understanding Road Safety Audit and Inspection Concepts
Road Safety Audit (RSA) and Road Safety Inspection (RSI) play important roles in evaluating and improving road safety infrastructure. While RSA focuses on new road design and construction, RSI assesses existing roads periodically. This article discusses the differences between RSA and RSI, their pro
0 views • 32 slides
Introduction to RSA Cryptography and Public Key Encryption
Explore the fundamentals of RSA cryptography and public key encryption, including shift ciphers and affine ciphers. Learn how public key encryption solves the challenges of implementing secure communication on a large scale. Discover the key components of RSA, its development history, and the mathem
2 views • 37 slides
Understanding Stable Matchings and the Gale-Shapley Algorithm
The concept of stable matchings is explored, along with the Gale-Shapley algorithm for finding them efficiently. Key ideas and steps of the algorithm are explained, supported by visuals. The process, examples, and observations related to the algorithm's effectiveness are discussed, highlighting the
1 views • 29 slides
Ricart and Agrawala's Algorithm for Mutual Exclusion
The Ricart-Agrawala Algorithm is a distributed system algorithm for achieving mutual exclusion without the need for release messages, developed by Glenn Ricart and Ashok Agrawala. The algorithm involves processes sending timestamped requests to enter a critical section, with careful handling of repl
1 views • 16 slides
Understanding Algorithm Efficiency Analysis
In this chapter, Dr. Maram Bani Younes delves into the analysis of algorithm efficiency, focusing on aspects such as order of growth, best case scenarios, and empirical analysis of time efficiency. The dimensions of generality, simplicity, time efficiency, and space efficiency are explored, with a d
1 views • 28 slides
Introduction to Public Key Cryptography
Public key cryptography, exemplified by algorithms like Diffie-Hellman and RSA, revolutionizes secure communication by allowing users to encrypt messages with public keys known to all and decrypt them with private keys known only to the intended recipient. This advanced encryption method ensures sec
1 views • 44 slides
Understanding Lamport Algorithm for Mutual Exclusion
Lamport Algorithm, presented by Prafulla Santosh Patil, is a permission-based algorithm utilizing timestamps to order critical section requests and resolve conflicts. It employs three types of messages: REQUEST, REPLY, and RELEASE, where each site manages a queue to store requests. By ensuring commu
0 views • 15 slides
Digital Differential Analyzer (DDA) Algorithm in Computer Graphics
In computer graphics, the Digital Differential Analyzer (DDA) Algorithm is utilized as the basic line drawing algorithm. This method involves interpolation of variables between two endpoints to rasterize lines, triangles, and polygons efficiently. The algorithm requires inputting coordinates of two
0 views • 9 slides
Republic of South Africa (RSA): COSO Components 2 & 3 with 3 Lines of Defence Approach
The presentation delves into RSA's approach to the COSO components, focusing on Risk Assessment and Internal Controls. It discusses the legislative mandate, Treasury regulations, and the COSO Internal Control Integrated Framework. The Risk Assessment section covers levels, matrices, and key instrume
0 views • 13 slides
RSA Algorithm in Public-Key Cryptography
The RSA algorithm is a crucial public key cryptography method used for key exchange, digital signatures, and data encryption. It involves generating public-private key pairs using prime numbers, encryption with the public key, and decryption with the private key. The algorithm's strength lies in the
0 views • 5 slides
Grey Wolf Optimizer: A Nature-Inspired Optimization Algorithm
The Grey Wolf Optimizer algorithm is based on the social hierarchy of grey wolves in the wild. Inspired by the pack behavior of grey wolves, this algorithm utilizes alpha, beta, and delta solutions to guide the optimization process. The hunting phases of tracking, pursuing, and attacking prey mimic
3 views • 16 slides
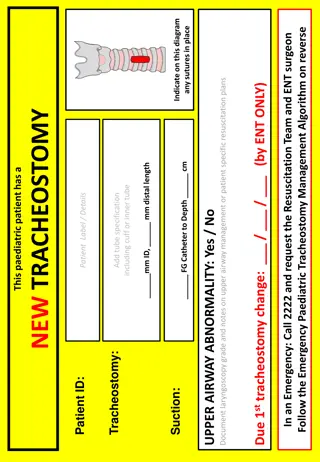
Emergency Paediatric Tracheostomy Management Algorithm
Emergency Paediatric Tracheostomy Management Algorithm provides a structured approach for managing pediatric patients requiring tracheostomy in emergency situations. The algorithm outlines steps for assessing airway patency, performing suction, and changing the tracheostomy tube if necessary. It emp
0 views • 4 slides
Development of Satellite Passive Microwave Snowfall Detection Algorithm
This study focuses on the development of a satellite passive microwave snowfall detection algorithm, highlighting the challenges in accurately determining snowfall using satellite instruments. The algorithm uses data from AMSU/MHS, ATMS, and SSMIS sensors to generate snowfall rate estimates, overcom
0 views • 20 slides
Understanding Euclid's Algorithm: An Ancient Approach to Finding Greatest Common Divisors
Euclid's Algorithm, dating back 2500 years, offers a simpler method to find the greatest common divisor (gcd) of two non-negative integers compared to traditional factorization. By iteratively applying a rule based on the gcd of remainders, it efficiently computes gcd values. The basis of the algori
0 views • 15 slides
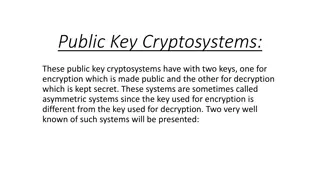
Understanding Public Key Cryptosystems in RSA Encryption
Public key cryptosystems, like RSA, use two keys for encryption and decryption, with one key made public and the other kept secret. This asymmetric system allows secure communication, where the encryption key (E) is used to encrypt messages into ciphertext (C), which can only be decrypted back to th
0 views • 11 slides
GPU Accelerated Algorithm for 3D Delaunay Triangulation
Thanh-Tung Cao, Todd Mingcen Gao, Tiow-Seng Tan, and Ashwin Nanjappa from the National University of Singapore's Bioinformatics Institute present a GPU-accelerated algorithm for 3D Delaunay triangulation. Their work explores the background, related works, algorithm implementation, and results of thi
0 views • 24 slides
Cuckoo Search: A Nature-Inspired Optimization Algorithm
Cuckoo Search (CS) algorithm, developed in 2009, mimics the brood parasitism of cuckoo species and utilizes Lévy flights for efficient optimization. This algorithm has shown promise in outperforming other traditional methods like PSO and genetic algorithms. The behavior of cuckoos in laying eggs an
0 views • 25 slides
Ford-Fulkerson Algorithm for Maximum Flow in Networks
The Ford-Fulkerson algorithm is used to find the maximum flow in a network by iteratively pushing flow along paths and updating residual capacities until no more augmenting paths are found. This algorithm is crucial for solving flow network problems, such as finding min-cuts and max-flow. By modelin
0 views • 26 slides
3GPP Voting Rights Algorithm: Contiguous-3 Solution Evaluation
This evaluation delves into the advantages and disadvantages of the 3 Contiguous-3 solution within the 3GPP voting rights algorithm. It explores scenarios to test the algorithm's effectiveness in granting and revoking voting rights based on meeting attendance types. The evaluation includes diverse h
0 views • 10 slides
Introduction to Algorithm Analysis and Complexity in Computer Science
Algorithm analysis is crucial in determining the efficiency of programs by analyzing resource usage such as time and space. This involves comparing programs, understanding data structures, and evaluating algorithm performance. Efficiency is key as program execution time depends on various factors be
0 views • 66 slides
Bresenham Line Drawing Algorithm Explained with Examples
Bresenham Line Drawing Algorithm is a method used to generate points between starting and ending coordinates to draw lines efficiently. This algorithm involves calculating parameters, decision parameters, and iteratively finding points along the line. Two example problems are provided with step-by-s
0 views • 8 slides
Algorithm Strategies: Greedy Algorithms and the Coin-changing Problem
This topic delves into general algorithm strategies, focusing on the concept of greedy algorithms where locally optimal choices are made with the hope of finding a globally optimal solution. The discussion includes the nature of greedy algorithms, examples such as Dijkstra's algorithm and Prim's alg
0 views • 91 slides
Stable Matching Problem and Gale-Shapley Algorithm Overview
The content provides information on the stable matching problem and the Gale-Shapley algorithm. It covers the definition of stable matching, the workings of the Gale-Shapley algorithm, tips for algorithm implementation, and common questions related to the topic. The content also includes a summary o
0 views • 16 slides
Understanding Prime Numbers and RSA Algorithm in Cryptography
Delve into the world of prime numbers and the RSA algorithm in cryptography. Learn about key generation, Bertrand's Postulate, the Miller-Rabin test for primality, and the Almost Miller-Rabin test. Discover how these concepts are crucial in ensuring secure communication and data encryption.
0 views • 20 slides
Understanding the RSA Algorithm - An Overview
Cryptography is the science of writing in secret code to protect information. The RSA algorithm, introduced by Rivest, Shamir, and Adleman in 1978, is a popular public key system. It involves the exchange of secure messages between senders and receivers to avoid code breaking. This algorithm uses bo
1 views • 31 slides
Understanding RSA Public-key Cryptography in Data Encryption
Exploring the foundational concepts of RSA public-key cryptography and its applications in data encryption. Learn how messages can be encoded, transmitted securely, and decoded using encryption and decryption functions. Discover the significance of picking large primes and understanding the bijectio
1 views • 12 slides
Understanding RSA Encryption for Secure Communication
Encryption plays a vital role in securing information, and RSA encryption, developed by Rivest, Shamir, and Adleman in 1977, uses public and private keys to safeguard data. Learn about the process, challenges with other encryption methods, prime numbers, and how RSA encryption works step by step.
0 views • 24 slides
Evaluation of Ed25519 Cryptography Performance in DNSSEC Validation
Edwards Curve Cryptography, specifically the Ed25519 algorithm, offers faster performance and high crypto density compared to other algorithms. This evaluation study compares key sizes, processing times, and validation support for Ed25519, ECDSA P-256, RSA-2048, and RSA-4096 in DNSSEC validation sce
0 views • 19 slides
Understanding Deutsch's Algorithm in Quantum Computing
Deutsch's Algorithm is a fundamental quantum algorithm designed to solve the problem of determining if a given function is constant or balanced. This algorithm leverages quantum principles such as superposition and entanglement to provide a more efficient solution compared to classical methods. By e
0 views • 17 slides
Research Assessment Trends in RSA and Lesotho: Issues, Challenges, and Forward Strategies
Research assessment in RSA and Lesotho involves evaluating research quality, measuring inputs, outputs, and impacts using both qualitative and quantitative methodologies. The prevailing practices include assessing research productivity for progression and utilizing various assessment mechanisms to e
0 views • 7 slides
Algorithm for Determining Endpoints in Speech Recognition
This article discusses an algorithm proposed by L.R. Rabiner and M.R. Sambur in 1975 for determining endpoints in isolated utterances. The algorithm focuses on detecting word boundaries in speech through the recognition of silence, which can lead to reduced processing load and increased convenience,
0 views • 22 slides
Weak Keys Detection in Network Devices
TLS and SSH rely on RSA and DSA for security, but weaknesses in random number generation can lead to widespread weak keys among hosts on the Internet. This paper uncovers the prevalence of repeated keys and easily inferred private keys, emphasizing the importance of entropy pools in key generation.
0 views • 28 slides
Time-space Tradeoffs and Optimizations in BKW Algorithm
Time-space tradeoffs and optimizations play a crucial role in the BKW algorithm, particularly in scenarios like learning parity with noise (LPN) and BKW algorithm iterations. The non-heuristic approach in addressing these tradeoffs is discussed in relation to the hardness of the LPN problem and the
0 views • 14 slides
Cryptology System Design Fundamentals - RSA Public Key System Analysis
The RSA public key system analysis involves determining suitable public and secret keys for users A and B, calculating distinct possible public keys, decrypting cryptograms, generating digital signatures, and discussing data ranges for secure communication. The solution covers the key generation pro
0 views • 16 slides