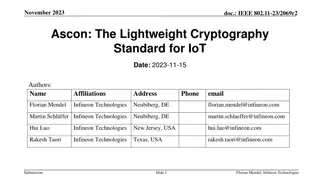
Ascon: The Lightweight Cryptography Standard for IoT
The November 2023 document IEEE 802.11-23/2069r2 discusses the importance of secure data storage and communication in IoT devices due to the increasing number of connected devices and potential security threats. It introduces Ascon as a lightweight cryptography standard selected by NIST for protecti
0 views • 26 slides
Safeguarding Canada's Research: Policy on Sensitive Technology Research and Affiliations of Concern (STRAC)
Canada's new Policy on Sensitive Technology Research and Affiliations of Concern (STRAC) aims to protect the country's research ecosystem from foreign entities posing security risks. The policy restricts funding for projects involving sensitive technology research if affiliated with military or stat
1 views • 10 slides
Lightweight Cryptography Standard for IoT - November 2023 IEEE Presentation
IEEE 802.11-23/2069r1 presents Ascon as a lightweight cryptography standard for IoT devices. With the increasing number of connected devices, protecting data on IoT devices becomes crucial. NIST selects Ascon to safeguard small devices, offering authenticated encryption and hashing efficiently. Asco
3 views • 26 slides
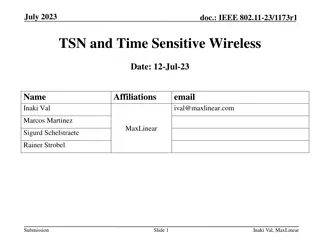
TSN and Time Sensitive Wireless
This document explores the relationship between IEEE 802.11 and Time Sensitive Networking (TSN), defining TSN in the context of 802.11 and highlighting the importance of TSN for improving packet delivery, reducing latency, and enhancing network reliability. Various features like Multi-AP, preemption
6 views • 18 slides
Mistakes to Avoid When Parenting as a Sensitive Father_
Are you a sensitive father raising a strong-willed child? While it's natural to make mistakes along the way, being aware of common pitfalls can help you navigate parenthood more effectively. Below, we are going to outline some common mistakes to steer clear of when parenting as a sensitive father, d
7 views • 6 slides
Static Optimizations
Explore the fundamental concepts of static optimizations in hardware architecture, focusing on compiler-driven techniques to improve performance and efficiency. Learn how compilers can enhance data locality, reduce unnecessary instructions, and minimize branches executed. Discover strategies such as
0 views • 42 slides
Understanding SHA-256 Algorithm and History
SHA-256 is a secure hashing algorithm that produces 256-bit hash values and is more secure than MD5, SHA-0, and SHA-1 due to fewer collisions. Created in 2001 by the NSA, it is widely used in various applications like cryptocurrency, SSL certificates, and blockchain. This summary provides insights i
0 views • 17 slides
Secure Keyed Hashing on Programmable Switches
Explore the implementation challenges and opportunities for improved security, privacy, performance, and reliability in data plane applications using (Half)SipHash and CRC32 hashing techniques. Discover the vulnerabilities associated with CRC32 and the need for secure hashing solutions like SipID. L
0 views • 17 slides
Understanding Scrypt: Maximally Memory-Hard Functions
Scrypt is a memory-hard function designed for password hashing and key derivation, aiming to thwart brute-force attacks by making evaluation moderately hard. It emphasizes the need for memory intensity over computation, hindering the advantages of special-purpose hardware, parallelism, and amortizat
0 views • 59 slides
Entity Resolution Problem in Customer Data Matching
The challenge of entity resolution, especially in the context of matching customer data between companies, is addressed in this content. The scenario involves accurately identifying which records correspond to the same individuals despite potential variations or errors in the data. Strategies such a
1 views • 56 slides
Comprehensive Overview of Binary Heaps, Heapsort, and Hashing
In this detailed review, you will gain a thorough understanding of binary heaps, including insertion and removal operations, heap utility functions, heapsort, and the efficient Horner's Rule for polynomial evaluation. The content also covers the representation of binary heaps, building initial heaps
0 views • 24 slides
CSE 373 - Hashing Concepts and Exam Preparation
Introduction to hashing in CSE 373, covering basic concepts, hash functions, collision resolution, and runtimes. Exam details for Friday's practice exam include topics on Stacks, Queues, BigO Notation, Heaps, Trees, Design Tradeoffs, and exam format with emphasis on theoretical understanding. Lectur
0 views • 38 slides
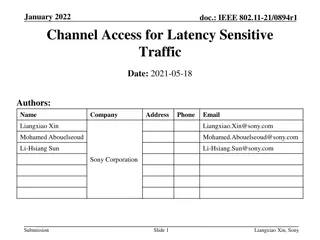
Enhancing Channel Access for Latency-Sensitive Traffic in January 2022
In the documentation IEEE 802.11-21/0894r1, the focus is on improving channel access for latency-sensitive traffic through concepts like Restricted TWT (Target Wake Time). The proposal suggests methods to protect TWT Service Periods from non-TWT scheduled STAs, ensuring prioritized transmission of l
0 views • 11 slides
Exploring Locality Models for High-Quality Education Systems
This research aims to develop partnership models at the locality level to ensure high-quality education for all students. It includes a conceptual approach analyzing key governance functions and draws insights from leading international systems like Ontario, Estonia, Finland, and Singapore. The stud
0 views • 28 slides
Understanding Locality Sensitive Hashing (LSH) for Nearest Neighbor Queries
Locality Sensitive Hashing (LSH) is a technique used to efficiently find nearest neighbors in high-dimensional spaces. By grouping similar points into the same hash bucket, LSH enables fast search for nearest neighbors, overcoming the curse of dimensionality. Variants include k-nearest neighbors and
0 views • 41 slides
Gentle Cleanser for Maintaining Healthy and Refreshed Sensitive Skin
Atomy Aidam offers a gentle cleanser that maintains the health and freshness of sensitive skin, leaving you with a revitalizing feeling. The Oriental Herb Complex, developed with natural herbs like chamomile and rosemary, enhances skin immunity and provides a natural aroma that keeps your private ar
0 views • 4 slides
Scaling Services and Key-Value Storage Techniques
This content delves into various aspects of scaling services, including partitioning, hashing, and key-value storage. It discusses vertical and horizontal scalability, the chaotic nature of horizontal scaling, techniques for partitioning data, and case studies like Amazon Dynamo. The importance of p
0 views • 48 slides
Stream Management and Online Learning in Data Mining
Stream management is crucial in scenarios where data is infinite and non-stationary, requiring algorithms like Stochastic Gradient Descent for online learning. Techniques like Locality Sensitive Hashing, PageRank, and SVM are used for critical calculations on streaming data in fields such as machine
0 views • 46 slides
Understanding Consistent Hashing and Distributed Hash Table
Explore the concept of consistent hashing and distributed hash tables to efficiently store and retrieve web pages across multiple servers. Learn how hashing functions and algorithms can distribute data evenly, handle server additions smoothly, and minimize object relocations. Discover the benefits o
1 views • 36 slides
Overlay Networks and Consistent Hashing in Distributed Systems
Understanding the concept of overlay networks and consistent hashing in distributed systems is crucial for scalability and efficient data storage. Overlay networks like P2P DHT via KBR offer a decentralized approach for managing data while consistent hashing provides a balanced and deterministic way
0 views • 36 slides
Adapting Linear Hashing for Flash Memory Constrained Embedded Devices
This research explores the adaptation of linear hashing for improved data handling on flash memory-constrained embedded devices. Motivated by the increasing data collection by IoT devices, the study focuses on implementing database structures like a linear hash table for efficient data processing. T
0 views • 67 slides
Understanding Hash Functions in Data Structures
Hash functions are crucial in storing data efficiently by converting a sized amount of data into a single integer. They are used to generate hash values, hash codes, or hash sums, which serve as indexes in arrays. The hash function should be quick to compute and distribute hash addresses uniformly t
0 views • 200 slides
Enhancing MemC3: Compact and Concurrent MemCache for Improved Performance
MemC3 introduces a novel approach to compact and concurrent caching through dumber caching and smarter hashing techniques, addressing key issues faced by traditional memory caching systems. By implementing CLOCK-based LRU, approximate LRU, and utilizing Cuckoo Hashing, MemC3 achieves significant imp
0 views • 20 slides
Enhancing Key-Value Storage with MemC3 and Cuckoo Hashing
MemC3 is a specialized key-value store that combines CLOCK and Concurrent Cuckoo Hashing to improve performance and efficiency. Memcached, an established DRAM-based key-value store, is also discussed along with its LRU eviction strategy. The use of internal chaining hashtable and LRU caching in Memc
1 views • 23 slides
Understanding Trauma-Sensitive Discipline Policies in Schools
Explore the concept of trauma-sensitive discipline policies in schools within the framework of VTSS TFI 1.6. Gain insights into changes in the Model Code of Conduct, identify vulnerable decision points, and incorporate trauma-sensitive approaches to respond to challenging behaviors. Embrace proactiv
0 views • 34 slides
Best Practices for Protecting Sensitive Data
Learn about password and credit card data security, storing passwords securely, data in transit vs. data at rest, and the importance of using salts to protect password hashes from offline attacks. Discover how to securely store passwords using encryption, hashing, and more to minimize exposure of se
0 views • 30 slides
Understanding the Risks of Sensitive Sectors in Free Trade Agreements
Explore the intricacies of sensitive sectors in Free Trade Agreements (FTAs) through an in-depth analysis of the potential dangers and benefits. Delve into the complexities of preferential tariff cuts, trade creation versus diversion, rules of origin, and the exemption of sensitive sectors. Learn ho
0 views • 27 slides
Locality of Java 8 Streams in Real-Time Big Data Applications
The study explores the impact of ccNUMA and locality on Java 8 Streams, focusing on their complexity and implementation in real-time Big Data applications. It discusses the Java support for server computers in clusters, the use of streams for programming models, and considerations for extending stre
0 views • 22 slides
Understanding Database Index Hashing Techniques
Hashing-based indexing in database systems is efficient for equality selections but not suitable for range searches. Both static and dynamic hashing methods exist, with static hashing involving fixed primary pages that are allocated sequentially. The process involves determining the bucket to which
0 views • 41 slides
Understanding Data Structures and Hashing in Java
Data structures play a crucial role in organizing, iterating, adding, deleting, and searching data efficiently. Hash tables, linked lists, trees, and more are explored in this overview, highlighting their strengths and trade-offs. Hashing, collision resolution strategies, and the importance of a wel
0 views • 19 slides
Understanding Hashing: Efficient Data Storage and Retrieval
Hashing is a powerful technique for achieving constant time complexity in finding and inserting data. It allows for quick access without the need for ordered elements. Direct addressing, limited hash operations, and efficient storage methods are discussed in this content to optimize data retrieval s
0 views • 100 slides
Impact of Data Locality on Garbage Collection in SSDs: A General Analytical Study
SSDs, widely deployed in desktops and data centers, offer high throughput but face limitations due to garbage collection overhead. This study explores the impact of data locality on garbage collection performance in SSDs, highlighting challenges, motivation, and contributions of the research. The wo
0 views • 26 slides
Inclusion Programme & SEND Reforms in Sheffield Update for School Governors (June 2016)
Sheffield is undergoing significant reforms in its inclusion programme and SEND services, aiming to provide better support for vulnerable young people and their families. The vision includes a shift towards a locality model, ensuring high-quality inclusive provision, robust mental health support, an
0 views • 13 slides
Understanding Sketching and Locality Sensitive Hashing in Data Mining
Explore the concepts of Jaccard Similarity and Cosine Similarity in data mining, along with their applications in recommendation systems and finding near-duplicates. Discover how Sketching and Locality Sensitive Hashing techniques help in efficiently identifying similar items and solving the Nearest
0 views • 63 slides
Understanding Hash Tables and Hashing Concepts in Computer Algorithms
This content delves into the concept of Hash Tables, covering topics such as the support for dictionary operations, achieving constant time through direct address tables, case studies in web server maintenance, and an exploration of hashing functions and collision avoidance. It also touches upon key
0 views • 40 slides
The Water Sensitive City Theory: Climate Change Adaptation Approach
The Water Sensitive City Theory explores how cities can evolve into integrated, adaptive, and climate-resilient water systems. It emphasizes restoring natural water balance, providing ecosystem services, and fostering water-sensitive communities. This approach is crucial for climate change adaptatio
0 views • 16 slides
Understanding Network Security Principles and Techniques
Explore the fundamental concepts of network security, including issues of confidentiality, integrity, and non-repudiability. Learn about the challenges of securing networks and the types of attacks that computer systems face. Dive into basic security techniques like hashing and symmetric key cryptog
0 views • 36 slides
Locality-Aware Caching Policies for Hybrid Memories
Different memory technologies present unique strengths, and a hybrid memory system combining DRAM and PCM aims to leverage the best of both worlds. This research explores the challenge of data placement between these diverse memory devices, highlighting the use of row buffer locality as a key criter
0 views • 34 slides
Managing Sensitive Data in Cloud Infrastructures: Best Practices and Considerations
Explore the orchestration of cloud infrastructures for handling sensitive data, including the importance of context, legal considerations, and utilizing self-assessment tools like CAIQ. Learn about QDR's current infrastructure at Syracuse University and the challenges of storing sensitive data in th
0 views • 10 slides
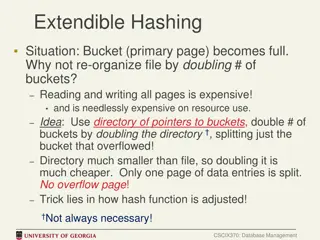
Efficient Bucket Management in Extendible Hashing
In cases where a bucket (primary page) becomes full in extendible hashing, re-organizing the file by doubling the number of buckets can be costly in terms of resource utilization. An alternative approach involves using a directory of pointers to buckets and doubling the directory instead of all buck
0 views • 9 slides