Principles of Cyber Security
Threat actors prioritize targeting networks to exploit vulnerabilities, leading to various attacks such as interception, DNS attacks, and MITM attacks. MITM attacks involve eavesdropping on communications or impersonating parties, with techniques like session replay to steal credentials. Implementin
0 views • 7 slides
Web App Security: Common Attacks and Preventive Measures
Explore common web application attacks like eavesdropping, SQL injection, and packet sniffing, along with their countermeasures like encryption with SSL. Learn how to prevent data breaches and secure your online platforms effectively.
2 views • 29 slides
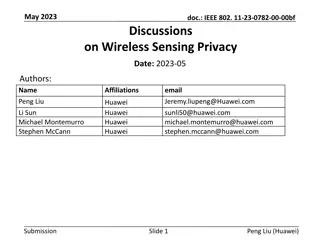
Wireless Sensing Privacy Discussions in May 2023 Document
May 2023 document (.IEEE 802..11-23-0782-00-00bf) discusses privacy issues related to wireless sensing, including unauthorized access to sensing reports, tracking of sensing devices, and potential eavesdropping on sensing signals. It proposes solutions to protect sensitive information and addresses
4 views • 12 slides
Understanding Network Security: Hijacking, Denial of Service, and IDS
This content delves into the concepts of spying and hijacking in network security, covering topics such as eavesdropping on packets, injecting packets into streams, denial of service attacks, and defense mechanisms like firewalls and IDS. It explores low-level attacks and defenses, including ARP cac
1 views • 81 slides
Enhancing Crowd Anonymity with Dummy Jondos
Explore the concept of using dummy jondos to increase anonymity in crowds and mitigate common attacks like eavesdropping and collusion. Learn how the introduction of dummy jondos can impact crowd size and resistance against potential threats, along with considerations for implementation and ensuring
2 views • 30 slides
Understanding Network Security Threats and Goals in Computer Systems
Explore the concept of threats in communication networks, including examples of attacks such as hacking and data disclosure. Learn about key security goals like confidentiality, data integrity, accountability, availability, and controlled access. Discover technically defined threats like masquerade,
0 views • 32 slides
Mobile App Security: Vulnerabilities in User and Session Authentication
Mobile apps face widespread vulnerabilities in user and session authentication, posing threats like eavesdropping and man-in-the-middle attacks. End-to-end security is crucial to protect apps from untrusted networks. App developers must prioritize security measures to prevent unauthorized access to
0 views • 30 slides
Understanding Kerberos Authentication in Network Security
Kerberos is a trusted authentication service for establishing secure communication between clients and servers in a distributed environment. Developed at MIT, it addresses threats like user impersonation and eavesdropping by providing centralized authentication. Kerberos relies on symmetric encrypti
0 views • 13 slides
Proactive Security Measures in Wireless Network Design
Exploring the benefits of proactive security measures in wireless networks, this study delves into protecting network flow information from inference attacks and implementing security designs to prevent eavesdropping. Case studies, strategies to safeguard connectivity information, and methods for un
0 views • 53 slides
Understanding Network Security Fundamentals in Computer Networks
Explore the importance of network security in Computer Networks, focusing on key aspects like confidentiality, integrity, authentication, and non-repudiation. Learn about common threats, such as eavesdropping, impersonation, hijacking, and denial of service attacks, and the role of cryptography in e
0 views • 28 slides
Understanding Network Security Fundamentals
Network security is crucial in today's digital age as the Internet is used for various activities like banking, shopping, and social interactions. This article covers key aspects of network security such as confidentiality, integrity, authentication, non-repudiation, and availability. It also explor
0 views • 45 slides
CPA-Security and Multiple Message Security in Cryptography
Today's goal is to build a CPA-secure encryption scheme focusing on multiple message security. The concept of indistinguishable multiple encryptions against eavesdropping attackers is explored, highlighting the importance of secure encryption schemes in the presence of an eavesdropper. The experimen
0 views • 22 slides
Understanding Network Security Part 2: Link Layer and ARP
Exploring the vulnerabilities in simple network topologies with hubs and the need for examining the link layer to prevent eavesdropping. Dive into MAC addresses, ARP (Address Resolution Protocol), and how machines translate IP addresses to physical Ethernet addresses. Learn about ARP tables, the tra
0 views • 61 slides
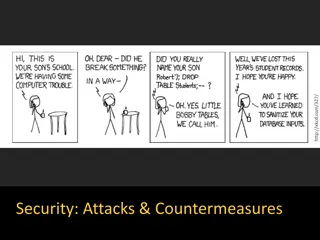
Web Application Security: Uncovering Common Attacks and Countermeasures
Explore common web application attacks such as eavesdropping and injection, along with effective countermeasures like encryption through SSL. Learn how to prevent attacks and secure your web apps.
0 views • 29 slides